The OSI Reference Model and the TCP/IP Reference Model
The OSI Reference Model and the TCP IP Reference Model
Before two computers or network devices can exchange information, they must establish communication, and this is where protocols come in. A network protocol enables two devices to communicate by using one set of rules. The OSI model and protocol standards help to ensure that networking devices are capable of working together over a network.
Protocols are the hardware or software components that carry out the OSI model guidelines for transferring information on a network. A protocol may be one component or a collection of components that carry out a task. A protocol stack, or protocol suite, is made up of multiple protocols used to exchange information between computers. One protocol in the stack might specify how network interface cards (NICs) communicate, and another might specify how a computer reads information from the NIC.
For More Protocol InformationThe Web site www.protocols.com provides easy-to-understand information about protocols. |
A layer is a section of a protocol stack that is responsible for performing one particular aspect of information transfer. Because some protocols are capable of performing more than one function, one layer in a protocol stack may not necessarily correspond to one layer in the OSI model. Tunneling describes the process of using a protocol to transfer information through a network, using a different type of protocol.
The OSI Seven-Layer Reference Model
In the early 1970s, a problem was brewing. There were many different computer manufacturers, and there were many incompatibilities among them. Furthermore, each manufacturer created different product lines, and even within one company, there were often incompatibilities between product lines. So the International Organization for Standardization (ISO; www.iso.org) got involved and created the Open Systems Interconnection (OSI) reference model, which is a blueprint for device manufacturers and software developers to use when creating products.
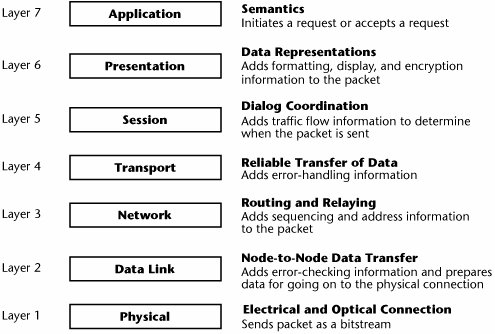
The OSI model, shown in Figure 5.8, has seven layers that describe the tasks that must be performed to transfer information on a network. When data is being transferred over a network, it must pass through each layer of the OSI model. As the data passes through each layer, information is added to that data. At the destination, the additional information is removed. Layers 4 through 7 occur at the end node, and Layers 1 through 3 are the most important to telecommunications networks.
Figure 5.8. The OSI reference model
It is important to understand that the OSI model is exactly thata model. It is a conceptual framework useful for describing the necessary functions required of a network device or member. No actual networking product implements the model precisely as described.
Layer 7, the application layer, is responsible for exchanging information between the programs running on a computer and other services on a network. This layer supports application and end-user processes. It acts as a window for applications to access network services. It handles general network access, flow control, error recovery, and file transfer. Examples of application layer protocols include File Transfer Protocol (FTP), Telnet, Simple Mail Transfer Protocol (SMTP), and Hypertext Transfer Protocol (HTTP).
Layer 6, the presentation layer, formats information so that a software application can read it. It performs transformations on the data to provide a standardized application interface and common communication services. It offers services such as encryption, compression, and reformatting. The presentation layer adds a field in each packet that tells how the information within the packet is encoded. It indicates whether any compression has been performed and, if so, indicates what type of compression so that the receiver can decompress it properly. It also indicates whether there has been any encryption, and if there has, it indicates what type so that the receiver can properly decrypt it. The presentation layer ensures that the transmitter and receiver see the information in the same format. Typically, Layer 6 processing is handled by an application rather than by a separate process running on a computer. In some cases, Layer 6 processing is handled by a process running at Layer 5.
Layer 5, the session layer, supports connections between sessions and handles administrative tasks and security. It establishes and monitors connections between computers, and it provides the control structure for communication between applications. Examples of session layer protocols include Network Basic Input/Output System (NetBIOS) and Lightweight Directory Access Protocol (LDAP).
Layer 4, the transport layer, corrects transmission errors and ensures that the information is delivered reliably. It provides an end-to-end error recovery and flow control capability. It deals with packet handling, repackaging of messages, division of messages into smaller packets, and error handling. Examples of transport layer protocols include Transmission Control Protocol (TCP), User Datagram Protocol (UDP), and Sequenced Packet Exchange (SPX).
Layer 3, the network layer, identifies computers on a network and determines how to direct information transfer over that network. In other words, it is a routing and relaying layer. It defines how to move information between networks, providing the functional and procedural means of transferring variable-length data sequences from a source to a destination via one or more networks while maintaining the QoS requested by the transport layer. The key responsibility of this layer is to perform network routing, flow control, segmentation/desegmentation, and error control functions. Examples of network layer protocols are X.25, Internet Protocol (IP), Internetwork Packet Exchange (IPX), and Message Transfer Part (MTP; part of the PSTN).
Layer 2, the data link layer, groups data into containers to prepare that data for transfer over a network. It puts the ones and zeros into a container that allows the movement of information between two devices on this same network. The protocols at this layer specify the rules that must be followed in transmitting a single frame between one device and another over a single data link. Bits are packaged into frames of data, and they include the necessary synchronization, error control, and flow control information. Examples of data link layer protocols in a LAN environment include Ethernet, Token Ring, and Fiber Distributed Data Interface (FDDI). Examples of data link layer protocols in a WAN environment include Frame Relay and Asynchronous Transfer Mode (ATM). Examples of data link layer protocols within the PSTN are Signaling System 7 (SS7) and MTP2.
Layer 1, the physical layer, defines how a transmission medium connects to a computer as well as how electrical or optical information is transferred on the transmission medium. The physical layer defines the types of cables or wireless interfaces that are allowed, the voltage levels used to represent the bits or the optical levels, the types of connectors that are allowed, and the types of transmission rates that can be supported. Every network service and every network device has definitions at the physical layer in terms of what it can physically interface with. For example, the physical layer deals with unshielded twisted-pair (UTP) and shielded twisted-pair (STP), coax, 10BASE-T (an Ethernet standard that allows the use of twisted-pair to support 10Mbps to the desktop, largely for legacy systems), 100BASE-T (the standard enterprises currently favor), multimode fiber and single-mode fiber, xDSL, ISDN, and the various capacities in PDH (e.g., DS-1/DS-3, E-1/E-3) and SDH/SONET (e.g., OC-1 through OC-192) networks.
The TCP/IP Four-Layer Reference Model
TCP/IP, which is an entire set of internetworking protocols, is described by its own layered modelsomewhat like the OSI model but also unique. Whereas OSI defines seven layers, the TCP/IP model is a four-layer network architecture (see Figure 5.9).
Figure 5.9. The TCP/IP four-layer reference model
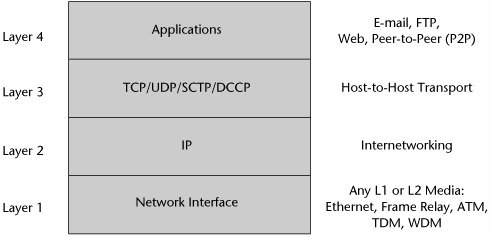
TCP/IP Layer 1, the network access protocols, relates to OSI Layers 1 and 2. It defines the range of networks that can be interconnected with IP and through which an IP datagram can be forwarded on the way to its destination. The many options include the following:
- Ethernet LANs (10Mbps, 100Mbps, 1Gbps, and 10Gbps)
- Token-ring LANs (4Mbps and 16Mbps)
- Wireless LANs (802.11x, better known as Wi-Fi)
- 2.5G and 3G wireless WANs
- Private line or dialup links (using Point-to-Point Protocol [PPP])
- Frame Relay networks (Frame Relay interface)
- ATM-user network interface
TCP/IP Layer 2 deals with internetworking protocols and is analogous to OSI Layer 3. This layer is the key to the architecture: It realizes the interconnection of remote (heterogeneous) networks without establishing an end-to-end connection. Its role is to inject packets into any network and deliver them to the destination independent of one another. Because no connection is established first, packets may not be received in order; the delivery order control process is the responsibility of the upper layers. Because of the major role of this layer in the packet delivery process, the critical point of this layer is routing. That is why this layer compares to the network layer of the OSI model. IP is the official implementation of this layer, and all transmissions are sent in IP messages, referred to as datagrams. The datagrams are forwarded to their destinations by routers. IP defines an unreliable, best-effort packet-forwarding service. It does not provide error checking, sequencing, or guaranteed delivery.
TCP/IP Layer 3 handles the host-to-host protocols and has the same role as the transport layer of the OSI model (Layer 4). It is used to enable peer entities to talk with one another. These are terminal-to-terminal protocols that run in the end devices, such as the user's PC and the server. There are four possible implementations: TCP, UDP, and two newer transport protocols, Stream Control Transmission Protocol (SCTP) and Datagram Congestion Control Protocol (DCCP) (which are discussed in Chapter 8, "The Internet and IP Infrastructures"). TCP is a connection-oriented protocol that provides reliable, error-free delivery; mind you, sometimes conditions in the network can cause it to fail, and the network connection can be lost. Its role is to split up the message to be transmitted into a form the IP layer can handle. On the receiving side, TCP places packets in order to reconstruct the initial message. TCP is also in charge of the flow control of the connection. In comparison, UDP is a very simple protocol; it is connectionless and not guaranteed to be reliable, although in practice it works quite well. UDP assumes that there is no need for control of flow of the packets; instead, it relies on some other mechanism to assure quality control. It is used, for example, in support of Voice over IP (VoIP), where the delay associated with retransmissions is not tolerable and instead the end user must ask a person to repeat himself or herself when there is a problem with the delivery of the voice packets.
TCP/IP Layer 4 is the realm of applications protocols and relates to OSI Layers 5, 6, and 7. These are utilities that allow applications to access particular network services:
- Telnet for remote terminal access
- File Transfer Protocol (FTP) for batch transmission
- Simple Mail Transfer Protocol (SMTP) for sending e-mail
- Post Office Protocol (POP) for receiving e-mail
- Hypertext Transfer Protocol (HTTP) for accessing and downloading Web-based (HTML-formatted) information
- Simple Network Management Protocol (SNMP) for network management
- Real-Time Transport Protocol (RTP) for transport of real-time audio and video
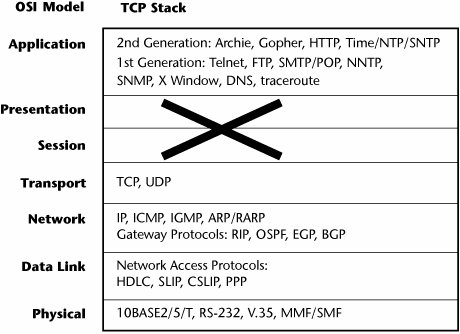
The TCP Stack Versus the OSI Model
Figure 5.10 shows the TCP stack and how it relates to the OSI model.
Figure 5.10. The TCP/IPOSI hybrid model (five layers)
Part I: Communications Fundamentals
Telecommunications Technology Fundamentals
- Telecommunications Technology Fundamentals
- Transmission Lines
- Types of Network Connections
- The Electromagnetic Spectrum and Bandwidth
- Analog and Digital Transmission
- Multiplexing
- Political and Regulatory Forces in Telecommunications
Traditional Transmission Media
Establishing Communications Channels
- Establishing Communications Channels
- Establishing Connections: Networking Modes and Switching Modes
- The PSTN Versus the Internet
The PSTN
- The PSTN
- The PSTN Infrastructure
- The Transport Network Infrastructure
- Signaling Systems
- Intelligent Networks
- SS7 and Next-Generation Networks
Part II: Data Networking and the Internet
Data Communications Basics
- Data Communications Basics
- The Evolution of Data Communications
- Data Flow
- The OSI Reference Model and the TCP/IP Reference Model
Local Area Networking
Wide Area Networking
The Internet and IP Infrastructures
- The Internet and IP Infrastructures
- Internet Basics
- Internet Addressing and Address Resolution
- The Organization of the Internet
- IP QoS
- Whats Next on the Internet
Part III: The New Generation of Networks
IP Services
Next-Generation Networks
- Next-Generation Networks
- The Broadband Evolution
- Multimedia Networking Requirements
- The Broadband Infrastructure
- Next-Generation Networks and Convergence
- The Next-Generation Network Infrastructure
Optical Networking
- Optical Networking
- Optical Networking Today and Tomorrow
- End-to-End Optical Networking
- The Optical Edge
- The Optical Core: Overlay Versus Peer-to-Peer Networking Models
- The IP+Optical Control Plane
- The Migration to Optical Networking
Broadband Access Alternatives
- Broadband Access Alternatives
- Drivers of Broadband Access
- DSL Technology
- Cable TV Networks
- Fiber Solutions
- Wireless Broadband
- Broadband PLT
- HANs
Part IV: Wireless Communications
Wireless Communications Basics
- Wireless Communications Basics
- A Brief History of Wireless Telecommunications
- Wireless Communications Regulations Issues
- Wireless Impairments
- Antennas
- Wireless Bandwidth
- Wireless Signal Modulation
- Spectrum Utilization
Wireless WANs
- Wireless WANs
- 1G: Analog Transmission
- 2G: Digital Cellular Radio
- 5G: Enhanced Data Services
- 3G: Moving Toward Broadband Wireless
- Beyond 3G
- 4G: Wireless Broadband
- 5G: Intelligent Technologies
WMANs, WLANs, and WPANs
Emerging Wireless Applications
- Emerging Wireless Applications
- The Handset Revolution
- Mobile IP
- The IP Multimedia Subsystem
- Mobile Gaming
- Mobile Video
- Mobile TV
- Mobile Content
Glossary
EAN: 2147483647
Pages: 160
