Internet Addressing and Address Resolution
To make the Internet an open communications system, a globally accepted method of identifying computers was needed, and IP acts as the formal addressing mechanism for all Internet messaging. Each host on the Internet is assigned a unique 32-bit Internet address, called the IP address, which is placed in the IP header and used to route packets to their destinations. IP addresses are assigned on a per-interface basis, so a host can have several IP addresses if it has several interfaces. (Note that a single interface can have multiple addresses, too.) Therefore, an IP address refers to an interface, not to the host. A basic concept of IP addressing is that some of the bits of the IP address can be used for generalized routing decisions because those bits indicate which network (and possibly which subnet) the interface is a member of. Addressing is performed on the basis of network/subnet and host; routing is performed based on the network/subnet portion of the address only. When a packet reaches its target network, the host portion of the address is examined for final delivery.
Because humans have a difficult time remembering strings of numbers and because many IP addresses are assigned dynamically, we use DNS to translate between easy-for-humans-to-remember host names and numeric IP addresses.
The following sections discuss addressing and routing schemes, two generations of IP addressing (IPv4 and IPv6), and DNS.
Addressing and Routing Schemes
To start our discussion on Internet and IP addressing, it is necessary to define the various ways in which information can flow between two or more points on a computer network. In the IP world, there are three main approaches: unicast, multicast, and anycast.
Unicast
With unicast, sometimes referred to as single-cast, information is sent from one transmitter to one receiver. In other words, information goes to only one location. A unicast server sends a stream to a single user at a time, and each destination address uniquely identifies a single receiver.
Multicast
Multicast involves sending information from one transmitter to multiple receivers. From this standpoint, it is rather like broadcasting in the television world, where one stream goes to multiple users simultaneously. Say, for instance, that you are in San Francisco, and you want to do a videoconferencing session that involves three offices located in London. In unicast mode, you need three separate IP connections to London from the conferencing point in San Francisco. With multicast, however, you need only one IP connection. A multicast router (mrouter) enfolds your IP packets in special multicast packets and forwards those packets to an mrouter in London; in London, that mrouter removes the IP packets, replicates them, and then distributes them to the three locations in London. In IP networks, the IP multicast protocol involves the use of a special group of addresses known as multicast addresses (as discussed later in this chapter). Each destination address identifies a group of receivers to which all information is replicated.
Anycast
A new development in IP routing is the introduction of anycast, which refers to the point-to-point flow of packets between a single client and the nearest destination server identified by an anycast address. As shown in Figure 8.11, in anycast, clients send packets addressed to A. Routers forward packets to the closest server with the address A. As with multicast, anycast involves a one-to-many association in which each destination address identifies a group of receivers. However, at any given time, only one of them is chosen to receive information from any given sender.
Figure 8.11. Anycast
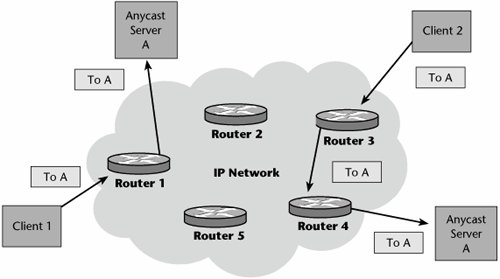
The type of anycast is determined by the criteria for selecting the nearest server. In IP anycast, the network topology is the key criterion. In Application anycast, applications or server metricssuch as number of connections or available capacityare the key criteria.
Anycast has several advantages. First, it offers a reduction in router and link resources because IP routing delivers packets over the shortest path to the closest available host. Another advantage is simplified configuration: The client needs to be configured with only a single IP anycast address of the server. Resiliency is another advantage: If one anycast server goes away, routing forwards the message to the next closest one with the same IP anycast address. Finally, anycast provides for load balancing, in which servers distributed over the network topology have the effect of balancing the traffic load for many clients.
There are three broad uses for IP anycast. The first use is service discovery, in which IP anycast routes the client's packets to a nearby server, which then redirects the client to a server (possibly itself), which is subsequently accessed using IP unicast. The second is query/reply services, in which the entire exchange is done using IP anycast; DNS is a popular recent example. The third use is routing services: IP anycast routes a client's packets to a routing infrastructure (e.g., IP multicast), which then continues to forward the packet by using whatever technology is appropriate.
IPv4 Addressing
The current generation of IP is called IP version 4 (IPv4). IPv4 addresses have two parts: the network ID and the host ID. Under IPv4, which was the only scheme in use until CIDR was introduced around 1995, there are five classes, which support different numbers of networks and hosts (see Figure 8.12):
- Class A With Class A, there can be a total of 126 networks, and on each of those networks there can be 16,777,214 hosts. Class A address space is largely exhausted, although ICANN has reserved some Class A address space.
- Class B Class B addresses provide for 16,384 networks, each of which can have 65,534 hosts. Class B space is also largely exhausted; some Class B addresses are still available at a very high cost.
- Class C Class C allows for 2,097,152 networks, each of which can have 254 hosts.
- Class D Class D belongs to a special aspect of the Internet called the multicast backbone (mbone). The mbone system conserves bandwidth over a distance, relieves congestion on transit links, and makes it possible to address a large population in a single multicast.
- Class E Class E is address space reserved for experimental purposes.
Figure 8.12. IPv4 32-bit addressing
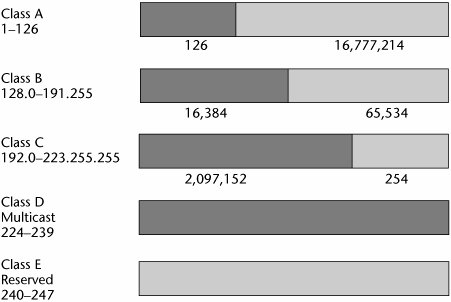
The digits in an IP address tell a number of things about the address. For example, consider the IP address 124.29.88.7. We know this is a Class A network because the first octet, 124, falls in the range of numbers for Class A addresses. Thus, 124 indicates the network ID. The remaining three octets, 29.88.7, indicate the host ID. In the address 130.29.88.7, the first two octets, 130.29, comprise the network ID and indicate that this is a Class B address; the second two octets, 88.7, comprise the host ID. Figure 8.13 shows an example of IP addressing on a network.
Figure 8.13. An example of IP network addressing
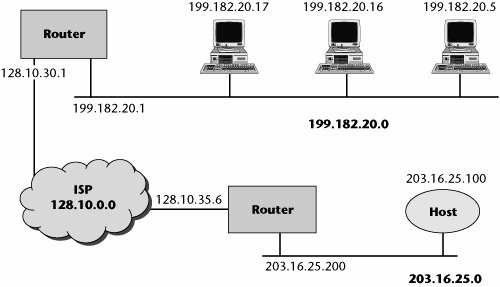
Network IDs are managed and assigned by the RIRs (ARIN, APNIC, RIPE NCC, LACNIC, and AfriNIC). Host IDs are assigned locally by the network administrator. Given a 32-bit address field, IPv4 makes available approximately 4.3 billion different addresses. That seems like a lot, but as we began to experience growth in the Internet, we began to worry about the number of addresses left.
CIDR
In the early 1990s, the IETF began to consider the possibility of running out of IP address space. The result was the implementation of CIDR, which eliminated the old class-based style of addressing. A CIDR address is still a 32-bit IP address, but it is hierarchical rather than class based. Large national and regional service providers are allocated large blocks of contiguous Internet addresses, which they then allocate to other smaller ISPs or directly to organizations. Networks can be broken down into subnetworks, and networks can be combined into supernetworks, as long as they share a common network prefix. Basically, with CIDR, a route is no longer an IP address broken down into network and host bits according to its class; instead, the route becomes a combination of an address and a mask. The mask indicates how many bits in the address represent the network prefix. For example, the address 200.200.14.20/23 means that the first 23 bits of the binary form of this address represent the network. The bits remaining represent the host. In decimal form, the prefix 23 would look like this: 255.255.254.0.
Table 8.1 lists the most commonly used masks, giving their dotted-decimal and prefix values and the number of available host addresses of each type. CIDR defines address assignment and aggregation strategies designed to minimize the size of top-level Internet routing tables, which was another goal of CIDR. The national or regional ISP needs only to advertise its single supernet address, which represents an aggregation of all the subnets within that supernet. Routers in the Internet no longer give any credence to class; routing is entirely based on the CIDR prefix. CIDR does require the use of supporting routing protocols, such as RIPv2, OSPF version 2, Enhanced Interior Gateway Routing Protocol (EIGRP), and BGP4.
|
Mask as Dotted-Decimal Value |
Mask as Prefix Value |
Number of Hosts |
|---|---|---|
|
255.255.255.224 |
/27 |
32 |
|
255.255.255.192 |
/26 |
64 |
|
255.255.255.128 |
/25 |
128 |
|
255.255.255.0 (Class C) |
/24 |
256 |
|
255.255.254.0 |
/23 |
512 |
|
255.255.252.0 |
/22 |
1,024 |
|
255.255.248.0 |
/21 |
2,048 |
|
255.255.242.0 |
/20 |
4,096 |
|
255.255.240.0 |
/19 |
8,192 |
|
255.255.224.0 |
/18 |
16,384 |
|
255.255.192.0 |
/17 |
32,768 |
|
255.255.0.0 (Class B) |
/16 |
65,536 |
|
255.254.0.0 |
/15 |
131,072 |
|
255.252.0.0 |
/14 |
262,144 |
|
255.248.0.0 |
/13 |
524,288 |
Subnetting is a term you may have heard in relationship to addressing. It once referred to the subdivision of a class-based network into subnetworks. Today, it generally refers to the subdivision of a CIDR block into smaller CIDR blocks. Subnetting allows single routing entries to refer either to the larger block or to their individual constituents, which permits a single general routing entry to be used through most of the Internet, with more specific routes required only for routers in the subnetted block.
NAT
Network Address Translation (NAT) is another technique used to deal with the shortage of IPv4 addresses. NAT was developed specifically to address this problem when the cost of extra IP addresses is an issue. NAT is therefore of particular interest in countries other than the United States where historically there have been fewer addresses allocated per capita, and also in small businesses and home offices. NAT enables a LAN to use one set of IP addresses for internal traffic and a second set of addresses for external traffic. The necessary IP address translations are performed at the NAT router, which is located where the LAN meets the Internet.
NAT allows an enterprise to use internal IP addresses, which, because they are internal, present no conflict with IP addresses employed by other enterprises. In a typical configuration, the LAN uses one of the designated "private" IP address subnets (10.0.0.0/8, 172.16.0.0/12, or 192.168.0.0/16). The router connecting this LAN to the Internet will have an address from the private subnet and a public address assigned by the ISP. The NAT function in the router translates between the public and private addresses. As far as the Internet is concerned, the router is the source and destination for any traffic. Because NAT-enabled routers do not have end-to-end connectivity, they cannot take part in some of the Internet protocols; for example, security protocols such as IPsec are complicated by the use of NATalthough the IETF has approved an extension to IPsec that encapsulates IPsec inside UDP, thus enabling it to traverse NAT devices. On the other hand, because the NAT server resides on the local network and must be used to initiate any connections to hosts on the other side of the router, the NAT server prevents some potential malicious activity coming from outside hosts. This improves the reliability of the local network, enhancing privacy by making it difficult for someone from outside the network to monitor individual usage patterns. Of course, this is less a function of NAT than a function of the rules that can be present in any router or firewallblocking all inbound traffic unless that traffic is a reply to some previous outbound request.
There are two main types of NAT: dynamic and static. In static NAT, the public IP address is always the same, allowing an internal host, such as a Web server, to have an unregistered private IP address and still be reached over the Internet. In dynamic NAT, a private IP address is mapped to a public IP address drawn from a pool of registered public IP addresses. By keeping the internal configuration of the private network hidden, dynamic NAT helps conceal the network from outside users.
As always, it is important to also note any shortcomings. As my colleague, Dr. Art St. George of the University of New Mexico, notes, "While it is true that NAT serves many useful functions, it also serves to make end-to-end performance very difficult, if not impossible, to achieve and measure. On the LAN, use of NATs makes network diagnostics very difficult."
IPv6 Addressing
Because researchers predict that we may run out of IPv4 addresses as soon as 2009 ("IPv6: Friend or Foe," SearchNetworking.com, http://searchnetworking.techtarget.com/originalContent/0,289142,sid7_gci1156263,00.html?track=NL-81&ad=539879), a new version of IP has been developed, called IP version 6 (IPv6). IPv6 provides for an expanded address space. It uses 128-bit addressing (versus 32 bits in IPv4), which results in 340 undecillion unique addressesthat is, 340 billion billion billion billionwhich is enough to supply 75 IP addresses to every square inch of the earth's surface, including oceans! IPv6 addresses typically have two parts: a 64-bit network prefix and a 64-bit host address. The host address can be assigned sequentially or automatically generated from the interface's MAC address. The IPv6 addressing structure uses hexadecimal notation, normally written as eight groups of four hexadecimal digits, and colons replace the periods used in IPv4, as in the following example:
2001:0db8:85a3:0000:1319:8a2e:0370:7344
IPv6 has four address types: unicast (one-to-one), anycast (one-to-nearest), multicast (one-to-many), and a reserved class. A single interface may be assigned multiple IPv6 addresses of unicast, anycast, or multicast addresses. Note that IPv6 does not support broadcasting.
IPv6 is designed to be an evolutionary step from IPv4. It can be installed as a normal software upgrade in Internet devices and is interoperable with IPv4. IPv6 runs well in high-performance networks, such as Gigabit Ethernet and ATM networks, and it is also efficient for low-bandwidth networks such as wireless networks. In addition, it provides a platform for new Internet functionality that will be required in the near future. IPv6 simplifies the packet header format (see Figure 8.14). It supports autoconfiguration and multihoming. IPv6 includes the DiffServ Code Point (DSCP) in the traffic class, and it addresses authentication and privacy capabilities.
Figure 8.14. The IPv6 packet header
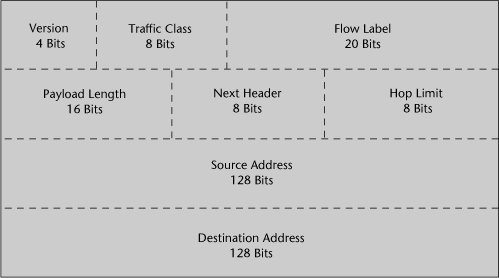
Benefits of IPv6 include improved routing efficiency due to the streamlined header format as well as simplified administration. QoS capabilities are also enhanced because the specification includes a flow label to support real-time traffic. Finally, IPv6 offers better security mechanisms, mandating the use of IPsec and IKE (which are discussed in Chapter 9, in the section "IPsec VPNs"). The encryption extension known as the Encapsulating Security Payload (ESP) service renders the packet's payload data illegible unless the recipient has the proper key to unscramble the data. Administrators can choose to encrypt only the transport and data payload of a packet or the entire packet, including headers and extensions.
The architecture for IPv6 is defined in RFC 3513, "IP Version 6 Addressing Architecture," which is available at www.ietf.org/rfc/rfc3513.txt and provides complete information on IPv6 addressing, rules, and exceptions. IPv6 addressing rules are covered by multiple RFCs.
The Transition from IPv4 to IPv6
There are several techniques for enabling IPv4-to-IPv6 interworking and coexistence:
- IPv4-to-IPv6 translation IPv4-to-IPv6 translation, shown in Figure 8.15, involves a network address translator, or a protocol translator. It employs stateless IP and ICMP translations. It is a bidirectional translation algorithm for IPv4, IPv6, ICMPv4, and ICMPv6 packet headers.
- Dual Stack With Dual Stack, which is already widely deployed, IPv4 and IPv6 exist in the same host (see Figure 8.16). New Dual Stack IPv6 devices will be backward capable with IPv4, and IPv4 devices can be programmed with both IPv4 and IPv6 stacks to process respective packets appropriately.
- 6to4 The third alternative involves IPv6 tunneling through IPv4, referred to as 6to4 (see Figure 8.17). 6to4 specifies a new technique designed for interconnecting IPv6 networks over IPv4 networks without explicitly defined tunnels. The IPv4 address (V4ADDR) portion of the special 6to4 IPv6 address identifies the IPv4 tunnel endpoints. Border routers need a default route to a 6to4 relay router, or they must run IPv6 interdomain routing protocols (such as MP-BGP). 6to4 can use special anycasts advertised by 6to4 relay routers to find the nearest one.
Figure 8.15. IPv4-to-IPv6 translation
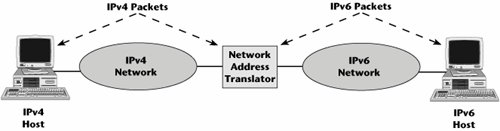
Figure 8.16. Dual Stack
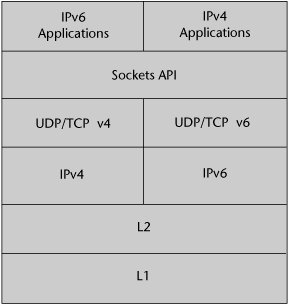
Figure 8.17. 6to4

The Status of IPv6 Deployment
The push to IPv6 was initially driven by a concern that the supply of available IP addresses would soon run out and that the addressing scheme had to be changed to allow for more addresses. However, especially in the United States, this shortage has not yet been realized. Most large enterprises have address blocks so big that they have never felt any address crunch at all. Furthermore, CIDR, NAT, network address port translation, and similar technologies have helped ease the strain on IP addresses. Fears about imminent IP address depletion were somewhat exaggerated. Nevertheless, Asia, especially China, is currently experiencing significant difficulty with IP address allocations. All of China has fewer IP addresses allocated to it than does Stanford University. Europe's IP address space issues are somewhat less pressing than Asia's but are still of concern, especially as mobile 3G networks begin to be deployed. In contrast, there is a general sense of complacency about these issues in the United States. Therefore, IPv6 had dropped off the radar screen of U.S. enterprises for a while, but now, with the government specifying that all federal agencies must deploy IPv6 by 2008, more attention is being focused on how migration to IPv6 will affect enterprises and providers alike. Again, IPv6 has also become a strategic priority in Europe and a pressing issue in Asia.
The European Union issued a consultation report on infrastructure for fully distributed mobile and shared applications. This report, which analyzes the development and deployment of IPv6, states that IPv6 will be of strategic importance to Europe for the next generation of communication systems. Meanwhile, the Japanese government has mandated that all its public networks must adopt IPv6. This is in part because Japan has embraced 3G wireless phones, which require IPv6 for networking. It is believed that the mobile market will be the greatest pusher of IPv6 because wireless is going to challenge IPv4's address availability. Currently it is not possible to expand the address range with NAT and retain functionality for wireless devices. With the proliferation of globally routable IP-aware devicessuch as mobile phones, videogame consoles, PDAs, smart cars, and wearablesan accompanying demand for wireless Web access is occurring, making migration to IPv6 a necessity.
There is very little end-user or application demand for IPv6, however. The current stumbling blocks to major deployment of IPv6 networks globally include the lack of wide-scale network infrastructure deployment and a lack of killer applications that require IPv6 to function. The primary benefits of IPv6 at this time accrue at the network management level, in areas such as intradomain routing, network configuration, end-to-end security, and address space management.
In 1996 the IETF established 6bone (www.6bone.net) as an IPv6 testbed network to enable IPv6 testing as well as to assist in the transitioning of IPv6 into the Internet. It operated under the IPv6 address allocation 3FFE::/16. More than 1,173 networks in some 60 countries were connected to the 6bone IPv6 network. 6bone started as a virtual network, using IPv6-over-IPv4 tunneling/encapsulation, operating over the IPv4-based Internet to support IPv6 transport. It slowly migrated to native links for IPv6 transport. 6bone ceased to operate in June 2006, and IANA reclaimed all 6bone prefixes.
The Moonv6 Project
The Moonv6 project (http://moonv6.sr.unh.edu) is a global effort led by the North American IPv6 Task Force (NAv6TF; www.nav6tf.org), involving the University of New Hampshire InterOperability Laboratory (UNH IOL; www.iol.unh.edu), Internet 2 (www.internet2.edu), vendors, service providers, and regional IPv6 Forum (www.ipv6forum.org) task force network pilots worldwide. Taking place across the United States at multiple locations, the Moonv6 project is the largest permanently deployed multivendor IPv6 network in the world. The U.S. Department of Defense (DoD) Joint Interoperability Test Command (JITC; http://jitc.fhu.disa.mil) and other government agencies, the Defense Research and Engineering Network (DREN; www.v6.dren.net), and the High Performance Computing Modernization Program (HPCMP; www.hpcmo.hpc.mil) play significant roles in the Moonv6 demonstrations, ensuring that DoD interoperability and migration objectives are identified and demonstrated.
The Moonv6 network is a set of native IPv6 connections between sites on the global Internet that forward packets to other Moonv6 peering sites. Participants can have a native IPv6 connection to the Internet, and Moonv6 permits IPv6-in-IPv4 tunnel hops for a 90-day period to test on the Moonv6 network, provided that the requestor, not Moonv6 administration, defines and administers those tunnels. A Moonv6 site forwards packets within the Moonv6 peering network and also participates as a Moonv6 site for collaborative testing of IPv6 implementations for interoperability and verification of functions within the IPv6 protocol and architecture. To become a Moonv6 peering network, a network must be an IPv6 peer with an existing Moonv6 peering network. To become a Moonv6 site, one must connect to an existing Moonv6 peering network.
DNS
DNS is a distributed database system that operates on the basis of a hierarchy of names. DNS provides translation between host names (such as www.lidoorg.com or www.telecomwebcentral.com) and the difficult-to-remember numeric IP addresses. It identifies a domain's mail servers and a domain's name servers. When you need to contact a particular URL, the host name portion of the URL must be resolved to the appropriate IP address (see Figure 8.18).
Figure 8.18. How DNS servers work
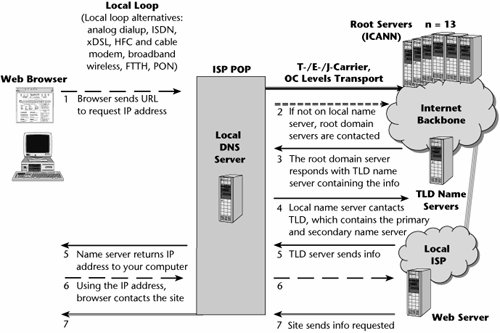
Your Web browser goes to a local name server, maintained either by your ISP, your online service provider, or your company. If the IP address is a local onethat is, if it's on the same network as the one you are onthen the name server will be able to resolve that URL with the IP address right away. In this case, the name server sends the true IP address to your computer, and because your Web browser now has the real address of the place you're trying to locate, it contacts that site, and the site sends the information you have requested.
If the local name server determines that the domain you have requested is not on the local network, it must get the information from a name server on the Internet. The local name server contacts 1 of the 13 root domain servers, each of which contains a list of the TLD name servers managed by ICANN. All 13 root servers contain the same vital information to spread the workload and back each other up. They contain the IP addresses of all the TLD registries, and they address both the global registries, such as .com and .org, and the 250 country-specific registries, such as .fr (for France). The root domain server tells the local server which TLD name server contains the domain specified in the URL.
Scattered across the Internet are thousands of computerscalled domain name resolvers or just resolversthat routinely download and copy the information contained in the root servers. These resolvers are located strategically with ISPs or institutional networks. They are used to respond to a user's request to resolve a domain name (i.e., to find the corresponding IP address).
TLD registry organizations house online databases that contain information about the domain names in that TLD. The .org registry database, for example, contains the IP address of the primary DNS server for the domain icann.org. In trying to find the Internet address of www.icann.org, your computer must first find the .org registry database. The TLD name server tells the local server which primary name server and secondary name server are authoritative for the domain in the requested URL (icann.org in our example). The local name server can then contact the domain's primary name server to resolve the full name of the host in the URL (www.icann.org in our example). If the primary name server does not respond, the local name server contacts the secondary name server. One of those name servers will have the proper information, and it will then pass that information back to the local name server. The local name server sends the information back to your browser, which then uses the IP address to contact the proper site.
Top-Level Domains
For some time, there have been seven generic TLDs (gTLDs):
|
.com |
commercial |
|
.gov |
government |
|
.mil |
military |
|
.edu |
education |
|
.net |
for network operation |
|
.org |
nonprofit organizations |
|
.int |
international treaty organizations |
gTLDs are unrestricted; this means anyone from anywhere can register as many of these domain names as they like.
In addition, 11 TLDs have been added since 2001:
|
.aero |
air-transport industry |
|
.arpa |
infrastructure |
|
.biz |
businesses |
|
.coop |
cooperatives |
|
.info |
any use |
|
.job |
related to jobs |
|
.museum |
museums |
|
.name |
individuals |
|
.pro |
accountants, lawyers, and physicians |
|
.root |
infrastructure |
|
.travel |
travel-related sites |
A few more TLDs are in the startup phase, including .cat, .mobi, .post, and .tel. In addition, some new TLDs have been proposed, including .asia, .geo, .kid, .mail, .sco, .web, and .xxx. The .nato TLD has been retired, and .example, .invalid, .localhost, and .test are held in reserve at this time.
There are also country code TLDs (ccTLDs). Each of these is a two-letter country code (e.g., .au, .ca), and there are 250 ccTLDs, including a .us domain for the United States. If you wanted to protect your domain name in the .com domain, for example, you would actually have to register it in 251 domains.com and then .com with the appropriate two-letter country code after thatand if you really wanted to get serious about branding, you would probably want to register another 250 each in the .net, .org, and .biz domains! Of course, very few organizations actually do this.
As discussed earlier in this chapter, the overall responsibility for managing DNS falls to ICANN. In addition to governing the terms and conditions of the gTLDs with the cooperation of the gTLD registries, ICANN also controls the root domain, delegating control over each TLD to a domain name registry. When it comes to the ccTLDs, the government of a given country typically controls the domain registry. Although ICANN may consult with the domain registries, it does not regulate the terms and conditions of how the domain name is allocated or who allocates it within each of the country-level domain registries.
The Importance of Domain Names
Many new domain names are registered every minute, and it seems that all the simple one- and two-word .com names have already been taken. Therefore, there's a call for new TLDs to be added. Originally IANA, which was funded by the U.S. government, administrated the DNS. From 1993 to 1998, Network Solutions (now part of VeriSign) was the sole provider of direct domain name registration services in the open gTLDs, and registration authority over the ccTLDs was relegated to the individual countries and bodies within them.
ICANN, a nonprofit, international corporation, was formed to take over in 1998. ICANN has assumed responsibility for a set of technical functions previously performed under U.S. government contract by IANA and other groups. Specifically, ICANN coordinates the assignment of the following identifiers, which must be globally unique for the Internet to function:
- Internet domain names
- IP address numbers
- IP numbers and TCP/UPD port numbers
In addition, ICANN coordinates the stable operation of the Internet's root server system. ICANN has also introduced competition into the administration of the DNS through a policy for the accreditation of registrars and a shared registry system for the .com, .net, and .org domains. As a result of competition, numerous domain name registration service providers from around the world are providing .com, .net, .org, .biz, and .info domain name registration services. The Accredited Registrar Directory provides a listing of ICANN-accredited domain name registrars that are currently taking domain name registrations (see www.icann.org).
The Organization of the Internet |
Part I: Communications Fundamentals
Telecommunications Technology Fundamentals
- Telecommunications Technology Fundamentals
- Transmission Lines
- Types of Network Connections
- The Electromagnetic Spectrum and Bandwidth
- Analog and Digital Transmission
- Multiplexing
- Political and Regulatory Forces in Telecommunications
Traditional Transmission Media
Establishing Communications Channels
- Establishing Communications Channels
- Establishing Connections: Networking Modes and Switching Modes
- The PSTN Versus the Internet
The PSTN
- The PSTN
- The PSTN Infrastructure
- The Transport Network Infrastructure
- Signaling Systems
- Intelligent Networks
- SS7 and Next-Generation Networks
Part II: Data Networking and the Internet
Data Communications Basics
- Data Communications Basics
- The Evolution of Data Communications
- Data Flow
- The OSI Reference Model and the TCP/IP Reference Model
Local Area Networking
Wide Area Networking
The Internet and IP Infrastructures
- The Internet and IP Infrastructures
- Internet Basics
- Internet Addressing and Address Resolution
- The Organization of the Internet
- IP QoS
- Whats Next on the Internet
Part III: The New Generation of Networks
IP Services
Next-Generation Networks
- Next-Generation Networks
- The Broadband Evolution
- Multimedia Networking Requirements
- The Broadband Infrastructure
- Next-Generation Networks and Convergence
- The Next-Generation Network Infrastructure
Optical Networking
- Optical Networking
- Optical Networking Today and Tomorrow
- End-to-End Optical Networking
- The Optical Edge
- The Optical Core: Overlay Versus Peer-to-Peer Networking Models
- The IP+Optical Control Plane
- The Migration to Optical Networking
Broadband Access Alternatives
- Broadband Access Alternatives
- Drivers of Broadband Access
- DSL Technology
- Cable TV Networks
- Fiber Solutions
- Wireless Broadband
- Broadband PLT
- HANs
Part IV: Wireless Communications
Wireless Communications Basics
- Wireless Communications Basics
- A Brief History of Wireless Telecommunications
- Wireless Communications Regulations Issues
- Wireless Impairments
- Antennas
- Wireless Bandwidth
- Wireless Signal Modulation
- Spectrum Utilization
Wireless WANs
- Wireless WANs
- 1G: Analog Transmission
- 2G: Digital Cellular Radio
- 5G: Enhanced Data Services
- 3G: Moving Toward Broadband Wireless
- Beyond 3G
- 4G: Wireless Broadband
- 5G: Intelligent Technologies
WMANs, WLANs, and WPANs
Emerging Wireless Applications
- Emerging Wireless Applications
- The Handset Revolution
- Mobile IP
- The IP Multimedia Subsystem
- Mobile Gaming
- Mobile Video
- Mobile TV
- Mobile Content
Glossary
EAN: 2147483647
Pages: 160
