LAN Characteristics
LANs are grouped according to four key characteristics:
- The types of transmission media over which they can operate
- The transport technique they use to transmit data over the network (i.e., broadband or baseband)
- The access method, which is involved in determining which device or network node gets to use the network and when it gets to use it
- The topology, or mapping, of the network (i.e., the physical and logical connections between the nodes on the network)
The following sections describe each of these four characteristics in detail.
LAN Transmission Media
This section talks specifically about the considerations in selecting the appropriate media for a LAN. For information on the characteristics and the advantages and disadvantages of the media types, see Chapter 2, "Traditional Transmission Media."
First and foremost, when selecting transmission media for a LAN, you need to think about bandwidth. You must evaluate the kind of capacity you need: How much do you need per client? How much do you need per server? Typically, servers require more capacity than clients because they service multiple simultaneous sessions, but some clients in an organization might use applications such as three-dimensional modeling and simulation and therefore require as much capacity as some of the shared servers. You should also evaluate the bandwidth based on traffic inside workgroups and traffic over the backbone between workgroups. Clusters or workgroups are made up of users who form a community of interest, and therefore the majority of traffic sharing occurs within each cluster. However, there are reasons to have interdepartmental or interworkgroup communications as well, and therefore you need the backbone to provide connectivity between all the distinct clusters. The backbone should be engineered for great future capacityprovisioned to meet user needs in peak times with the ability to be upgraded as neededand the workgroups should be set up so that they can easily be adjusted for moves, adds, and other changes.
The second consideration regarding LAN transmission media has to do with cost and ease of connectivity, and that speaks specifically to the installation, as well as to moves, adds, and other changes. In the average, rather stable environment, the majority of the employees are relocated at least once a year, so equipment, features, and services must move along with them. And, of course, some environments have many reorganizations and require yet more consideration in this area. For example, in an enterprise where reorganization is common, using a wireless LAN is probably the easiest way to support such a dynamic environment. (Of course, if every desktop has an RJ-45 in place, moving may be just as easy as with wireless.) The tradeoff is that wireless media provide less bandwidth than, say, fiber, and with a wireless LAN, you have to create smaller clusters. Again, what media you choose depends greatly on the application.
The third consideration regarding LAN transmission media is sensitivity to interference and noise. If a LAN is being deployed in a manufacturing plant where other equipment emits interfering levels of noise, the noise could play havoc with a twisted-pair or wireless LAN, whereas coax and fiber would be much less susceptible to the interference.
Finally, of course, you need to consider security requirements. Again, there is no such thing as complete security, and each situation needs a different amount of security. You need to add encryption and other security mechanisms in almost any environment, but in some cases, you need to take the extra step of choosing a medium that's more difficult to tap into, such as coax or fiber. Mind you, both can be breached; it's a matter of how easy it is to do so (based on physical access) and how quickly unauthorized taps can be detected (with the help of testing equipment).
Most of the LAN standards today support the full range of media types. They vary in terms of factors such as the distances allowed between the devices and their backbones, so you need to choose the media appropriate to your situation.
LAN Transport Techniques and Standards
An important feature of a LAN is its transport technique: whether it is broadband or baseband (see Figure 6.2). Broadband means multichannel, so a broadband LAN implies that, through Frequency Division Multiplexing (FDM), multiple independent channels can carry analog or digital information, depending on the interfaces. This is essentially the way traditional cable TV operates: There are multiple channels of programming, and each one runs over a different portion of the frequency band. When you request a particular channel from the interface device (the set-top box), the device selects the frequency band on which that channel is allocated. Cable TV is a multichannel coaxial system.
Figure 6.2. Broadband versus baseband
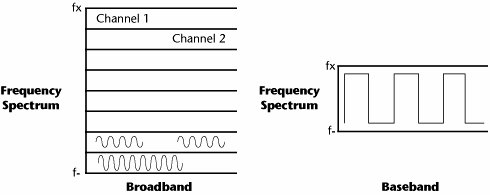
Baseband implies a single-channel digital system, and this single channel carries information in containersthat is, packets or framesthat are specified by the LAN standard in use. The traditional LAN standards are Ethernet, Token Ring, and Fiber Distributed Data Interface (FDDI). Table 6.1 compares these three standards.
|
Characteristic |
Ethernet |
Token Ring |
FDDI |
|---|---|---|---|
|
Standard |
IEEE 802.3 |
IEEE 802.5 |
ANSI X3T9.5, IEEE 802.6 |
|
Logical topology |
Bus |
Ring |
Ring |
|
Physical topology |
Bus, star |
Ring, star |
Dual ring, dual bus |
|
Media |
Coax, UTP, STP, fiber |
Coax, UTP, STP |
Fiber (CDDI) |
|
Transmission mode |
Baseband |
Baseband |
Baseband |
|
Bandwidth |
10Mbps, 100Mbps, 1Gbps, 10Gbps |
4Mbps, 16Mbps, 100Mbps, 1Gbps |
100Mbps |
|
Media access |
Nondeterministic |
Deterministic |
Deterministic |
|
Control |
CSMA/CD, CSMA/CA |
Token passing |
Token passing |
The vast majority of LANsprobably 85% or moreare baseband Ethernet LANs. IEEE 802.3 is the working group that creates and defines the entire family of Ethernet standards (see Table 6.2). The major milestones include the first generation, which emerged in 1983 as the IEEE 802.3 standard and defines 10Mbps Ethernet over thick coax. Later, in 1995, 802.3u introduced 100Mbps or Fast Ethernet. The next major leap occurred in 1998, producing the 1Gbps Ethernet standard, 802.3z. The latest formalized standard, 802.3ae, approved in 2003, specifies 10Gbps Ethernet. In 2004, 802.3ah specified 1Gbps Ethernet for use in the local loop. Ethernet is now also making inroads into the metro and long-haul networking spaces. Full-duplex operation and Ethernet switching have lifted the CSMA/CD distance limitation restrictions, so Ethernet is no longer technically restricted to just LANs. Long-haul Ethernet is now being applied to metropolitan area networks (MANs) and wide area network (WANs), as well. (MAN and WAN applications of Ethernet are discussed further in Chapter 11, "Optical Networking.")
|
Ethernet Standard |
Date Completed |
Description |
|---|---|---|
|
Experimental Ethernet |
1972 (patented in 1978) |
2.94Mbps over coaxial cable bus. |
|
Ethernet II (DIX v2.0) |
1982 |
10Mbps over thick coax. Frames have a Type field. The Internet Protocol suite uses this frame format on any media. |
|
IEEE 802.3 |
1983 |
10BASE5 10Mbps over thick coax; this is the same as DIX except the Type field is replaced by Length and LLC fields. |
|
802.3a |
1985 |
10BASE2 10Mbps over thin coax (thinnet or cheapernet). |
|
802.3b |
1985 |
10BROAD36. |
|
802.3c |
1985 |
10Mbps repeater specs. |
|
802.3d |
1987 |
FOIRL (Fiber-Optic Inter-Repeater Link). |
|
802.3e |
1987 |
1BASE5 or StarLAN. |
|
802.3i |
1990 |
10BASE-T 10Mbps over twisted-pair. |
|
802.3j |
1993 |
10BASE-F 10Mbps over fiber. |
|
802.3u |
1995 |
100BASE-TX, 100BASE-T4, and 100BASE-FX Fast Ethernet at 100Mbps (with autonegotiation). |
|
802.3x |
1997 |
Full-duplex and flow control; also incorporates DIX framing, so there's no longer a DIX/802.3 split. |
|
802.3y |
1998 |
100BASE-T2 100Mbps over low-quality twisted-pair. |
|
802.3z |
1998 |
1000BASE-X Gigabit Ethernet over fiber at 1Gbps. |
|
802.3-1998 |
1998 |
A revision of the base standard that incorporates the preceding amendments and errata. |
|
802.3ab |
1999 |
1000BASE-T Gigabit Ethernet over twisted-pair at 1Gbps. |
|
802.3ac |
1998 |
Maximum frame size extended to 1522 bytes (to allow Q-tag). The Q-tag includes 802.1Q virtual LAN (VLAN) information and 802.1p priority information. |
|
802.3ad |
2000 |
Link aggregation for parallel links. |
|
802.3-2002 |
2002 |
A revision of the base standard that incorporates the three prior amendments and errata. |
|
802.3ae |
2003 |
10GBASE-SR, 10GBASE-LR, 10GBASE-ER, 10GBASE-SW, 10GBASE-LW, and 10GBASE-EW 10Gbps Ethernet over fiber. |
|
802.3af |
2003 |
Power over Ethernet. |
|
802.3ah |
2004 |
Ethernet in the first mile. |
|
802.3ak |
2004 |
10GBASE-CX4 10Gbps Ethernet over twin-axial (twinax) cable. |
|
802.3-2005 |
2005 |
A revision of the base standard that incorporates the four prior amendments and errata. |
|
802.3an |
In progress |
10GBASE-T 10Gbps Ethernet over unshielded twisted-pair (UTP). |
|
802.3ap |
In progress |
Backplane Ethernet (1Gbps and 10Gbps over printed circuit boards). |
|
802.3aq |
In progress |
10GBASE-LRM 10Gbps Ethernet over multimode fiber. |
|
802.3ar |
In progress |
Congestion management. |
|
802.3as |
In progress |
Frame expansion. |
The 802.3 standards are not complete yet; the 100Gbps Ethernet prototypes are in the early stages, and they promise all the benefits of a ubiquitous and inexpensive technology for use in metro and wide area service provider networks.
Due to the pervasive use of Ethernet and the extremely low cost of the hardware required, most manufacturers today build the functionality of an Ethernet NIC directly into PC motherboards. Even though Ethernet has gone through quite a few generational changes, from thick coax supporting 10Mbps in traditional LAN environments to the emerging use of Gigabit Ethernet in the local loop and 10Gbps point-to-point links in MANs and WANs, from the programmer's perspective, the variations are pretty much the same Ethernet and are easily interconnected using inexpensive and readily available hardware. Many Ethernet cards and switch ports support multiple speeds, using autonegotiation to set the speed and duplexing to match the best parameters supported by both devices. In the event that autonegotiation fails, a device designed to support multiple speeds senses the speed used by the other device but assumes half-duplex mode. For example, a 10/100 Ethernet port supports 10BASE-T and 100BASE-TX, while a 10/100/1000 Ethernet port supports 10BASE-T, 100BASE-TX, and 1000BASE-T.
Token Ring originated in the IBM environment in the early 1980s. Although it was very successful initially, after the Ethernet twisted-pair standard emerged in the early 1990s, the use of Token Ring declined. IBM no longer uses or promotes the Token Ring technology, but Madge Networks (www.madge.com) continues to provide it. The IEEE 802.5 working group has standardized token-ring LAN speeds of 4Mbps, 16Mbps, 100Mbps, and 1Gbps.
Despite the fact that FDDI was the first LAN standard to provide 100Mbps for use in a backbone application, it did not capture a major market share. The transition to a higher grade of Ethernet is much simpler for companies than is a transition to an entirely new protocol.
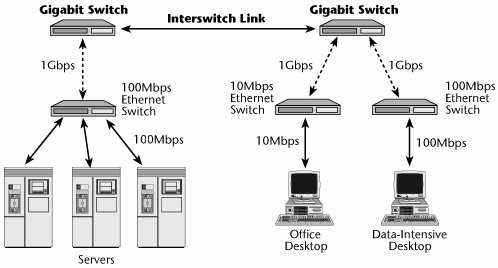
The prevailing standard in the world is Ethernet, which generally appears as Fast Ethernet or Gigabit Ethernet in the backbone, connecting individual Fast Ethernet or 10Mbps Ethernet LAN segments (see Figure 6.3).
Figure 6.3. An example of Gigabit Ethernet
LAN Access Methods
The third main LAN characteristic is the access methods, which are involved in determining who gets to use the network and when they get to use it. There are two main approaches to LAN access: token passing and Carrier Sense Multiple Access/Collision Detection (CSMA/CD).
Token Passing
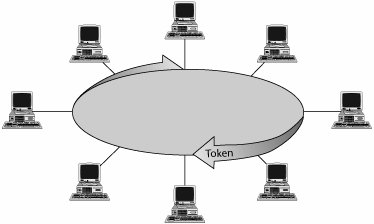
Token passing, shown in Figure 6.4, is used with the token-ring and FDDI architectures. Here is how token ring works:
- The active master, chosen through a process called beaconing, inserts a token (i.e., a specially formatted packet) into the ring.
- The token circulates around the ring and is regenerated by each workstation it passes. (In token-ring networks, a workstation obtains data from only its upstream neighbor, regenerates it, and sends it to its downstream neighbor.)
- When a workstation has data to send, it waits for the token to pass by and grabs it off the wire, holding it until it has finished its transmission. The station then injects its data packets onto the wire.
- The packets circulate around the ring and are examined and regenerated by each workstation. When the receiving workstation receives the packets, it marks them as received when it regenerates and reinjects them. This marking notifies the sender that the data was in fact received when it finally returns to the sender. The sender then generates a new token and injects it into the ring. To prevent any particular workstation from hogging the ring, a transmitting station can hold the token (and thus transmit data packets) for a specific interval, called the token hold time. If the time expires before the station has transmitted all its information, it must stop transmitting and put a new token back on the ring so that other stations have a chance to communicate. When the token gets back to the waiting workstation, it can resume transmitting.
Figure 6.4. Token passing
A benefit of token passing is that it is a deterministic technique: You can always calculate the maximum delay that you'll encounter in moving information between any two points on that network, and this is especially important for applications with defined response times, such as process control. For example, an oil pipeline may have sensors in the pipelines to detect minute leakage. The oil company wants to know exactly how long it will take for the alarm from the sensor to reach the control station to shut off the valve, in order to avoid leaking oil into the community. In a LAN where there's a need to determine the delay, token passing works very well. The disadvantage of token passing is that it occurs in a unidirectional ring, so it takes time to pass the tokens. A device has to wait until it receives a token before it can send it, and if the ring is broken because a device goes down, the ring is then unable to send tokens until the ring is recovered (i.e., the failed device is either taken out of commission or reinitiated). Today, almost all token-ring interfaces include an electrical shunt to prevent this from happening.
CSMA/CD
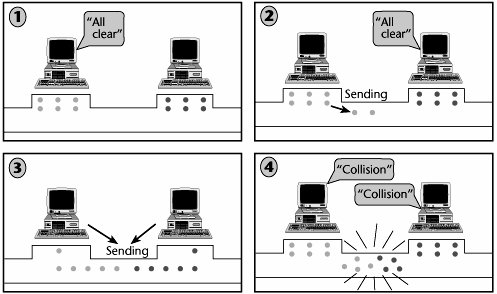
CSMA/CD is used with the Ethernet standard. CSMA/CD is a nondeterministic access method, meaning that any device can send whenever it determines that the network is clear. However, each device must listen to the network at all times because there is the potential for a collision. If a collision occurs, both sending devices back off the network and wait a random number of nanoseconds or milliseconds before attempting to retransmit.
As shown in Figure 6.5, CSMA/CD works as follows:
- The terminals listen to the network.
- Both of the terminals assume that the network is clear. They both start sending, but they continue listening because they know there's a chance that their messages will collide.
- The messages do collide, so both terminals produce a jam signal, which carries a bit pattern sent by a data station to inform the other stations that they must not transmit.
- One terminal waits 20 milliseconds, and the other waits 50 milliseconds, and then they again attempt to transmit, assuming that their messages won't bump into each other. Because the terminals waited different amounts of time, most likely the messages don't collide and therefore get transmitted. However, if the messages collide again, the terminals repeat the back-off and random-wait procedure up to 16 times before the frames are dropped.
Figure 6.5. CSMA/CD
In this type of environment, the more devices added and the greater the traffic volumes, the more likely collisions will occur. When collisions start to exceed the available throughput, you need to start segmenting the LAN into smaller clusters, called collision domains in Ethernet parlance, or consider making the move to switched Ethernet LANs.
LAN Topologies
The final characteristic of a LAN is its topologythe physical and logical mapping of the network. The most common LAN topologies are the tree, bus, ring, and star topologies, which are illustrated in Figure 6.6. The tree topology is commonly used in broadband LANs, and the bus, ring, and star topologies are used in baseband LANs. In today's environment, the most common physical topology is the star, and the most common logical topologythat is, how the signals are exchanged between stationsis the bus.
Figure 6.6. LAN topologies

Tree Topology
In the tree topology, the root of the tree is the headend, or the central retransmission facility. The trunk cable is attached to this root. Various branch cables are attached to the trunk cable. From there, user devices can be connected. Although most broadband networks use a single cable, some use a dual-cable systemone cable for each direction to and from the headend. All transmissions must pass through the headend because each device transmits on one frequency and receives on another. The headend is responsible for translating the device's transmit frequency to the receive frequency of another device, and this frequency translation is called remodulation.
Bus Topology
The bus topology, which is the oldest topology, functions like a multipoint circuit. All stations are attached via cable taps or connections to a single length of cablea wire with two open ends that are terminated by a resistor. The single cable is referred to as a trunk, backbone, or segment.
Each station can detect and place signals on the bus according to the access method. Only one computer at a time can send data on a bus network. Signals travel in both directions along the bus, from the point of insertion. Any other station on the network can receive a transmission from the station. Because the data is sent to the entire network, it travels from one end of the cable to the other. If the signal were to be allowed to continue uninterrupted, it would keep bouncing back and forth along the cable, preventing other computers from sending signals. Therefore, the signal must be stopped after it has had a chance to reach the proper destination address. A component called a terminator is placed at each end of the cable to absorb free signals and to clear the cable so that other computers can send data.
The bus topology is a passive topology. Computers only listen for data being sent on the network; they are not responsible for moving data from one computer to the next. An advantage of the bus topology is that it uses short cable lengths, and therefore it uses cable economically. Because the transmission media are inexpensive and easy to work with, the network is easy to extend. A disadvantage of the bus topology is that problems are difficult to isolate. A cable break can affect many users, and the network can become slow when traffic is heavy.
Ring Topology
In the ring topology, the nodes are connected by point-to-point links that are arranged to form an unbroken loop configuration. At each station the signal is received, regenerated, and transmitted to the next station on the ring, and data is transmitted in one direction around the ring. The ring is an active topology. That is, each computer acts like a repeater to boost the signal and send it on to the next computer. Because the signal passes through each computer, the failure of one computer can affect the entire networkbut in practice this rarely occurs because the ring interfaces contain passive electrical shunts that allow the ring to remain intact in case a station goes down or malfunctions.
An advantage of the ring topology is that it can spread over long distances because each station regenerates the signal. Another advantage is ease of implementing distributed control and checking facilities; all computers have equal access, and the performance is even, despite the fact that there are many users. A potential disadvantage is sensitivity to station failures (i.e., one failed station might break the ring). Also, problems in a ring network are difficult to isolate, and network reconfiguration disrupts the operation of the entire network.
Star Topology
In the star topology, all stations are connected by cable segments to a centralized component called a hub. Devices can communicate with each other only through the hub. The star topology offers centralized resources and management. The advantages of the star topology include ease of fault isolation, ease of bypassing and repairing faulty stations, and high cost-efficiencies. Also, it's much easier to modify or add new computers in a star network than to do so in other topologies. Disadvantages include the need for a lot of cable to interconnect all the stations and the potential for total network disruption if the central hub facility fails.
There are a number of variations on star networks. The star bus, for instance, is a combination of the bus and star topologies. It involves several star networks linked together with linear bus trunks. The star ring, sometimes referred to as the star-wired ring, looks similar to a star bus, except that the hubs in the star ring are connected in a star pattern, and the main hub contains the actual ring.
LAN Interconnection and Internetworking |
Part I: Communications Fundamentals
Telecommunications Technology Fundamentals
- Telecommunications Technology Fundamentals
- Transmission Lines
- Types of Network Connections
- The Electromagnetic Spectrum and Bandwidth
- Analog and Digital Transmission
- Multiplexing
- Political and Regulatory Forces in Telecommunications
Traditional Transmission Media
Establishing Communications Channels
- Establishing Communications Channels
- Establishing Connections: Networking Modes and Switching Modes
- The PSTN Versus the Internet
The PSTN
- The PSTN
- The PSTN Infrastructure
- The Transport Network Infrastructure
- Signaling Systems
- Intelligent Networks
- SS7 and Next-Generation Networks
Part II: Data Networking and the Internet
Data Communications Basics
- Data Communications Basics
- The Evolution of Data Communications
- Data Flow
- The OSI Reference Model and the TCP/IP Reference Model
Local Area Networking
- Local Area Networking
- LAN Basics
- LAN Characteristics
- LAN Interconnection and Internetworking
Wide Area Networking
The Internet and IP Infrastructures
- The Internet and IP Infrastructures
- Internet Basics
- Internet Addressing and Address Resolution
- The Organization of the Internet
- IP QoS
- Whats Next on the Internet
Part III: The New Generation of Networks
IP Services
Next-Generation Networks
- Next-Generation Networks
- The Broadband Evolution
- Multimedia Networking Requirements
- The Broadband Infrastructure
- Next-Generation Networks and Convergence
- The Next-Generation Network Infrastructure
Optical Networking
- Optical Networking
- Optical Networking Today and Tomorrow
- End-to-End Optical Networking
- The Optical Edge
- The Optical Core: Overlay Versus Peer-to-Peer Networking Models
- The IP+Optical Control Plane
- The Migration to Optical Networking
Broadband Access Alternatives
- Broadband Access Alternatives
- Drivers of Broadband Access
- DSL Technology
- Cable TV Networks
- Fiber Solutions
- Wireless Broadband
- Broadband PLT
- HANs
Part IV: Wireless Communications
Wireless Communications Basics
- Wireless Communications Basics
- A Brief History of Wireless Telecommunications
- Wireless Communications Regulations Issues
- Wireless Impairments
- Antennas
- Wireless Bandwidth
- Wireless Signal Modulation
- Spectrum Utilization
Wireless WANs
- Wireless WANs
- 1G: Analog Transmission
- 2G: Digital Cellular Radio
- 5G: Enhanced Data Services
- 3G: Moving Toward Broadband Wireless
- Beyond 3G
- 4G: Wireless Broadband
- 5G: Intelligent Technologies
WMANs, WLANs, and WPANs
Emerging Wireless Applications
- Emerging Wireless Applications
- The Handset Revolution
- Mobile IP
- The IP Multimedia Subsystem
- Mobile Gaming
- Mobile Video
- Mobile TV
- Mobile Content
Glossary
EAN: 2147483647
Pages: 160
