Multiple Gatekeeper Configurations
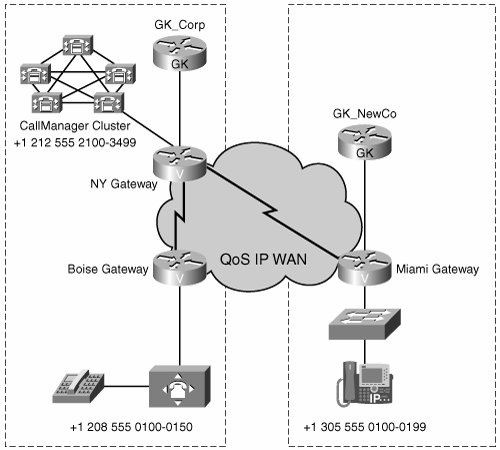
Sometimes you might want to be able to route calls between zones that different gatekeepers control. An example of this might be in a large enterprise that has multiple business units. Each business unit might have a gatekeeper that is controlling its sites. This lets each business unit manage its own bandwidth and dial plans. The corporation as a whole needs to be able to route calls between all locations. A subset of the company location is shown in Figure 17-2. Each gatekeeper also controls additional locations that are not shown in the diagram. In addition, there is PSTN connectivity at every location.
Figure 17-2. Multiple Gatekeeper Network
A zone that a different gatekeeper controls is known as a remote zone. Setting up call routing to a remote zone is similar to the basic configuration discussed in the previous section. To begin, use the zone remote zonename domainname ip-address command. The zonename and domainname must match the names that are defined on the remote gatekeeper. The ip-address is the IP address of the remote gatekeeper.
The next things to configure are the zone prefixes for the zones in the remote gatekeeper. You do this in the same manner as the basic configuration. For remote zones, you must manually configure prefixes. Prefixes cannot be learned dynamically from the remote gatekeeper. You can still use dynamic prefix registration for local zones.
Optionally, you can code the lrq reject-unknown-prefix command. This command causes the gatekeeper to reject a Location Request (LRQ) message if no matching local zone prefix is coded.
Overall, the process of configuring call routing with multiple gatekeepers is similar to configuring call routing with a single gatekeeper. The difference is the use of remote zone definitions. Example 17-7 shows the configuration of the two gatekeepers in the sample network.
CORPORATE GATEKEEPER GK_Corp#show running-config Building configuration... ! ! Unnecessary output deleted ! interface Loopback0 description Gatekeeper interface ip address 10.100.101.1 255.255.255.255 ! gatekeeper zone local ny cisco.com 10.100.101.1 zone local boise cisco.com zone remote miami cisco.com 10.100.100.1 1719 zone prefix miami 130555501.. zone prefix boise 120855501.. zone prefix ny 1212555.... gw-type-prefix 1#* default-technology rrq dynamic-prefixes-accept arq reject-unknown-prefix lrq reject-unknown-prefix no shutdown ! end |
NEW DIVISION GATEKEEPER GK_NewCo#show running-config Building configuration... ! ! Unnecessary output deleted ! interface Loopback0 description Gatekeeper interface ip address 10.100.100.1 255.255.255.255 ! gatekeeper zone local miami cisco.com 10.100.100.1 zone remote ny cisco.com 10.100.101.1 1719 zone remote boise cisco.com 10.100.101.1 1719 zone prefix miami 130555501.. zone prefix boise 120855501.. zone prefix ny 1212555.... gw-type-prefix 1#* default-technology rrq dynamic-prefixes-accept arq reject-unknown-prefix lrq reject-unknown-prefix no shutdown ! end |
The signaling is quite different when an ARQ is received for a prefix in a remote zone from one that exists in a local zone. The local gatekeeper must issue an LRQ to the remote gatekeeper to attempt to resolve the IP address of the destination. For more information, see the "H.323 Call Flows Using Gatekeepers" section in Chapter 16.
Part I: Voice Gateways and Gatekeepers
Gateways and Gatekeepers
- Gateways and Gatekeepers
- The Role of Voice Gateways
- The Role of Voice Gatekeepers
- The Role of IP-to-IP Gateways
- Introduction to Voice Protocols
- Call Control Agents
- Deployment Scenarios
- Case Study: Introduction
- Chapter Review Questions
Part II: Gateways
Media Gateway Control Protocol
- Media Gateway Control Protocol
- Introduction to MGCP
- MGCP Operation
- Call Flow with MGCP
- Dial Plan Considerations
- Implementing MGCP Gateways
- Securing MGCP Gateways
- Troubleshooting Tools
- Case Study: Configuring an MGCP Gateway
- Review Questions
H.323
- H.323
- H.323 Specifications
- H.323 Network Components
- Call Flow
- H.323 Protocol Pros and Cons
- When to Use H.323
- Dial Plan Considerations
- Implementing H.323 Gateways
- Securing H.323 Gateways
- Troubleshooting Tools
- Case Study: Configuring an H.323 Gateway
- Review Questions
Session Initiation Protocol
- Session Initiation Protocol
- Description of SIP
- SIP Call Flow
- SIP Pros and Cons
- When to Use SIP
- Dial Plan Considerations
- Implementing SIP Gateways
- Securing SIP Gateways
- Allowing H.323 to SIP Connections
- Troubleshooting Tools
- Case Study: Configuring SIP Between a Gateway and CallManager 5.x
- Review Questions
Circuit Options
Connecting to the PSTN
- Connecting to the PSTN
- PSTN Circuit Selection Overview
- Analog Trunks
- Digital Trunks
- Case Study: Add an E1 R2 Connection to the Leeds Gateway
- Review Questions
Connecting to PBXs
- Connecting to PBXs
- Analog Trunks
- Digital Trunks
- Configuring Transparent Common Channel Signaling
- Case Study: Implementing a Cisco Voice Gateway at the Shanghai Office
- Review Questions
Connecting to an IP WAN
- Connecting to an IP WAN
- Applications for Connecting to an IP WAN
- Design Considerations
- Quality of Service
- Providing Fax and Modem Services
- Security
- Case Study: Using a T1 Link as a Tie Line
- Review Questions
Dial Plans
- Dial Plans
- Numbering Plans
- Overlapping Numbering Plans
- Building a Scalable Dial Plan
- Dial Peers
- Dial Peer Matching
- Case Study: Configuring PSTN Access
- Review Questions
Digit Manipulation
- Digit Manipulation
- Basic Digit Manipulation
- Number Expansion
- Voice Translation Rules and Profiles
- Manipulating Caller ID
- Order of Operation in Digit Manipulation
- Troubleshooting Digit Manipulation
- Case Study
- Review Questions
Influencing Path Selection
- Influencing Path Selection
- Hunt Groups
- Using Trunk Groups
- Tail-End Hop-Off
- Call Admission Control
- POTS-to-POTS Call Routing Considerations
- Case Study: Implementing Gateway-Controlled RSVP
- Review Questions
Configuring Class of Restrictions
- Configuring Class of Restrictions
- COR Overview
- COR Operation
- Implementing COR
- Assigning COR Lists with SRST
- Assigning COR Lists with Cisco CallManager Express
- Restricting Inbound Calls
- Case Study: Implementing COR for Miami
- Review Questions
SRST and MGCP Gateway Fallback
- SRST and MGCP Gateway Fallback
- SRST Overview
- Configuring SRST
- Dial Plan Considerations
- SRST Features
- SIP SRST
- Call Preservation
- Secure SRST
- MGCP Gateway Fallback
- Configuring MGCP Gateway Fallback
- Verifying and Troubleshooting SRST
- Verifying and Troubleshooting MGCP Gateway Fallback
- Case Study: Integrating SRST with an Analog Voice-Mail System
- Review Questions
DSP Resources
- DSP Resources
- Need for DSP Resources
- Determining the DSP Resources Required
- Configuring DSP Resources
- Transcoding for CallManager Express
- Case Study: Add DSP Resources to the Miami Gateway
- Review Questions
Using Tcl Scripts and VoiceXML
- Using Tcl Scripts and VoiceXML
- Tcl IVR and VoiceXML Application Overview
- Sample Applications
- Downloading Tcl Scripts from Cisco.com
- Configuring the Gateway to Use a Tcl Script
- Implementing the AA Tcl Script
- Creating Audio Files
- Restrictions and Caveats
- Case Study: Implementing ACD Application
- Review Questions
Part III: Gatekeepers
Deploying Gatekeepers
- Deploying Gatekeepers
- Gatekeeper Functionality
- Gatekeeper Signaling
- E.164 Number Resolution
- Call Admission Control
- Gatekeeper Deployment Models
- Gatekeepers with CallManager
- Security with Gatekeepers
- Review Questions
Gatekeeper Configuration
- Gatekeeper Configuration
- Configuring Basic Gatekeeper Functionality
- Multiple Gatekeeper Configurations
- Configuring Directory Gatekeepers
- Troubleshooting Gatekeepers
- CallManager and Gatekeepers
- Gatekeeper Redundancy
- Configuring Resource Availability Indicator
- Configuring Gatekeeper Security
- Case Study: Deploying Gatekeepers to Assist in Migration to VoIP
- Review Questions
Part IV: IP-to-IP Gateways
Cisco Multiservice IP-to-IP Gateway
- Cisco Multiservice IP-to-IP Gateway
- IP-to-IP Gateway Overview
- Cisco Multiservice IP-to-IP Gateway
- Basic Configuration
- IP-to-IP Gateway Features
- Case Study: Providing Enterprise VoIP Trunking to VoIP Service of the Service Provider
- Review Questions
Appendix A. Answers to Chapter-Ending Review Questions
Index
EAN: 2147483647
Pages: 218
