Overview of the 3002 Hardware Client
The 3002 is a hardware version of the Cisco VPN software client. Like the software client, it is easy to use, but provides much more scalability where a large number of SOHO sites need to connect to a central site. It is easy to deploy and support; most IPsec functionality is hidden from the user who has to deploy and manage it, just as is the case with the Cisco VPN Client software. The 3002 fully supports Cisco Easy VPN Remote technologies and is used as a remote access device, protecting traffic for users behind it.
Because the 3002 is an Easy VPN Remote, you can centralize policies on an Easy VPN Server and push them down to the 3002. The 3002 supports two modes for protecting users' traffic to a central site: client and network extension modes (these will be discussed later in the "Connection Modes" section). The following sections will discuss the features, models, and deployment options for the 3002.
3002 Features
The 3002 is easy to deploy and support. It already is a DHCP client on its public interface, acquiring addressing information dynamically from the ISP (the 3002 also supports PPPoE on its public interface in addition to static IP addressing). It has a static IP address on its private interface and is a DHCP server on the private interface, giving out addressing information to internal devices. It supports a Quick Configuration process similar to the VPN 3000 concentrators, making it easy to set it up to connect to an Easy VPN Server. Here are some of the 3002's many features:
- It is fully IPsec-compliant and supports the following IPsec functions: Automatic configuration of ISAKMP/IKE Phase 1 Policies and Phase 2 transformsyou don't need to configure these on the client; authentication with pre-shared keys and digital certificates; DH groups 1, 2, and 5; ESP in tunnel mode, NAT-T, IPsec over UDP, and IPsec over TCP; DES, 3DES, AES-128, and AES-256 encryption algorithms; and SHA-1 and MD5 HMAC functions.
Note
Due to limited room for storing transforms on the 3002, it does not support AES-192 for encryption.
- It supports Path MTU discovery and manual MTU adjustment to reduce the likelihood of IPsec fragmentation.
- It can be upgraded from policies defined by an Easy VPN Server and pushed down to the 3002 during IKE Phase 1 in the IKE Mode Config step, allowing the 3002 to automatically download a new software image from a TFTP server and then reboot itself.
- It supports client and network extension modes. In client mode, the 3002 is assigned a single internal address and PATs all user's addresses to the internally assigned address from the concentrator; this makes all devices at the SOHO appear as one logical device from the corporate office's perspective. In network extension mode, the 3002 simulates an L2L tunnel, where no address translation is performed on the SOHO devices' addresses, making them appear as an extension of the corporate office network.
- It provides authentication credentials to bring up the IPsec tunnel (default or unit authentication), or one (interactive unit authentication) or more users (user authentication) can provide this information.
- It is fully compliant with the load balancing features of the VPN 3000 concentrators and ASA security appliances via VCA, and supports a backup server list for redundancy.
- It supports up to 253 devices behind its private interface.
3002 Models
There are two 3002 models, as shown in Figure 14-1 (rear of the chassis).
Figure 14-1. 3002 Models
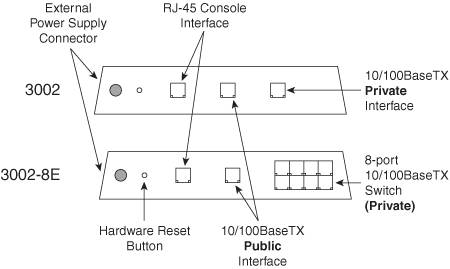
In the figure, both models have an external power supply, a hardware reset button, an RJ-45 console interface (uses a roll-over cable), and a 10/100BaseTX public interface. The only difference between the two models is that the 3002 has a single 10/100BaseTX private interface and the 3002-8E has an 8-port 10/100BaseTX auto-sensing private interface. The front of the 3002 chassis has three LEDs. Table 14-1 explains the status of the LEDs.
|
LED |
Color |
Description |
|---|---|---|
|
PWR |
Off |
3002 is powered off |
|
Green |
3002 is powered on |
|
|
SYS |
Green |
3002 is operational |
|
Flashing green |
3002 is negotiating on its public interface using DHCP or PPPoE |
|
|
Flashing amber |
3002 is performing diagnostic tests |
|
|
Solid amber |
3002 has failed diagnostic tests |
|
|
VPN |
Off |
No VPN tunnel has been established |
|
Amber |
Establishing a VPN tunnel has failed |
|
|
Green |
A VPN tunnel is established |
Deployment of the 3002
Normally small remote offices or SOHO environments use remote access solutions to provide secure connections to a central site. Deploying a VPN gateway for an L2L connection is typically not necessary and cost-prohibitive. Therefore, there are four choices for VPN solutions in small remote office or SOHO environments:
- Software clients installed on users' desktops
- A small VPN-enabled router appliance
- A small VPN-enabled security appliance
- A 3002 hardware client appliance
The following sections will discuss the advantages and disadvantages of using software and hardware clients.
Software Client Option
The main advantage that VPN software client solutions have over hardware solutions is that software clients are typically free, like the Cisco VPN Client and Microsoft's L2TP/IPsec client. However, they have many disadvantages:
- They scale poorly if you need to support a large number of them.
- They require more management and administration on a network administrator's part.
- They have limited operating system support (only Microsoft Windows 98 and higher, Linux/Intel, Solaris/UltraSparc, and MAC OS X are supported) for the Cisco software client.
The software client commonly is used for the home user and, more commonly, mobile users.
Hardware Client Option
Hardware clients can handle the limitations that software clients have:
- They can handle protection of traffic for multiple computers, thereby offloading the administration and maintenance to a smaller number of devicesthis is ideal for small branch offices or SOHO environments.
- They can protect any traffic the PC users send to the corporate office (typically limited to IP).
- They can provide additional features that PCs lack, such as stateful firewall functions, address translation, quality of service, and so on.
- The user can't mess up the VPN configuration because this is located on the secured hardware appliance (in this situation, two or three service calls to fix a user's software client configuration typically can pay for the cost of a VPN-enabled hardware appliance.
- You might not have control of the users' desktops, and therefore a hardware client solution is a better fit in this scenario.
If a VPN-enabled hardware appliance is a better fit for many sites in your network, you now need to decide which type of hardware appliance to use: security appliances (like the PIX 501 or 506E), routers (like the Cisco IOS 830s, UBR900s, and 1700s), or VPN 3002s. Table 14-2 displays when each type of hardware appliance should be deployed.
|
Device |
Best for these purposes |
|---|---|
|
IOS Router |
Need a non-Ethernet interface connection to the ISP, such as ISDN, xDSL, or serial Need enhanced QoS Need voice support |
|
PIX |
Need a hardware-based stateful firewall Implements split tunneling Need complex address translation policies, especially with protocols that have problems with address translation (For non-Ethernet ISP connections, you'll still need a router) |
|
3002 |
Need ease of implementation, upgrades, and support Requires little training since the GUI interface is the same as the VPN 3000 concentrators (For non-Ethernet ISP connections, you'll still need a router) |
TIP
In most cases, if I needed to support voice connections or I needed a non-Ethernet-based ISP connection, I would use a router; for enhanced throughput, I'd get a 1700 series router with the VPN encryption module. If I needed to allow for split tunneling at the remote access site, or had need of complex address-translation policies, I would use a small-end PIX security appliance. If I had none of these concerns, then I would prefer to use a 3002 hardware client, because, of the three solutions, it is the easiest to install, upgrade, and maintain.
Part I: VPNs
Overview of VPNs
- Overview of VPNs
- Traffic Issues
- VPN Definition
- VPN Components
- VPN Designs
- VPN Implementations
- VPNs: Choosing a Solution
- Summary
VPN Technologies
IPsec
PPTP and L2TP
SSL VPNs
Part II: Concentrators
Concentrator Product Information
- Concentrator Product Information
- Concentrator Models
- Concentrator Modules
- Concentrator Features
- Introduction to Accessing a Concentrator
- Summary
Concentrator Remote Access Connections with IPsec
- Concentrator Remote Access Connections with IPsec
- Controlling Remote Access Sessions to the Concentrator
- IPsec Remote Access
- Network Access Control (NAC) for IPsec and L2TP/IPsec Users
- Summary
Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- PPTP and L2TP Remote Access
- WebVPN Remote Access
- Summary
Concentrator Site-to-Site Connections
- Concentrator Site-to-Site Connections
- L2L Connectivity Example
- ISAKMP/IKE Phase 1 Preparation
- Adding Site-to-Site Connections
- Address Translation and L2L Sessions
- Summary
Concentrator Management
- Concentrator Management
- Bandwidth Management
- Routing on the Concentrator
- Chassis Redundancy
- Administration Screens
- Summary
Verifying and Troubleshooting Concentrator Connections
- Verifying and Troubleshooting Concentrator Connections
- Concentrator Tools
- Troubleshooting Problems
- Summary
Part III: Clients
Cisco VPN Software Client
- Cisco VPN Software Client
- Cisco VPN Client Overview
- Cisco VPN Client Interface
- IPsec Connections
- VPN Client GUI Options
- VPN Client Software Updates
- VPN Client Troubleshooting
- Summary
Windows Software Client
- Windows Software Client
- Windows Client
- Configuring the Windows VPN Client
- Configuring the VPN 3000 Concentrator
- Microsoft Client Connections
- Troubleshooting VPN Connections
- Summary
3002 Hardware Client
- 3002 Hardware Client
- Overview of the 3002 Hardware Client
- Initial Access to the 3002
- Authentication and Connection Options
- Connection Modes
- Administrative Tasks
- Summary
Part IV: IOS Routers
Router Product Information
Router ISAKMP/IKE Phase 1 Connectivity
- Router ISAKMP/IKE Phase 1 Connectivity
- IPsec Preparation
- ISAKMP/IKE Phase 1 Policies
- ISAKMP/IKE Phase 1 Device Authentication
- Monitoring and Managing Management Connections
- Routers as Certificate Authorities
- Summary
Router Site-to-Site Connections
- Router Site-to-Site Connections
- ISAKMP/IKE Phase 2 Configuration
- Viewing and Managing Connections
- Issues with Site-to-Site Connections
- Summary
Router Remote Access Connections
- Router Remote Access Connections
- Easy VPN Server
- Easy VPN Remote
- IPsec Remote Access and L2L Sessions on the Same Router
- WebVPN
- Summary
Troubleshooting Router Connections
- Troubleshooting Router Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- New IPsec Troubleshooting Features
- Fragmentation Problems
- Summary
Part V: PIX Firewalls
PIX and ASA Product Information
- PIX and ASA Product Information
- PIX Deployment Scenarios
- PIX and ASA Feature and Product Overview
- Summary
PIX and ASA Site-to-Site Connections
- PIX and ASA Site-to-Site Connections
- ISAKMP/IKE Phase 1 Management Connection
- ISAKMP/IKE Phase 2 Data Connections
- L2L Connection Examples
- Summary
PIX and ASA Remote Access Connections
- PIX and ASA Remote Access Connections
- Easy VPN Server Support for 6.x
- Easy VPN Remote Support for 6.x
- Easy VPN Server Support for 7.0
- Summary
Troubleshooting PIX and ASA Connections
- Troubleshooting PIX and ASA Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- Summary
Part VI: Case Study
Case Study
Index
EAN: 2147483647
Pages: 178
