IPsec Remote Access and L2L Sessions on the Same Router
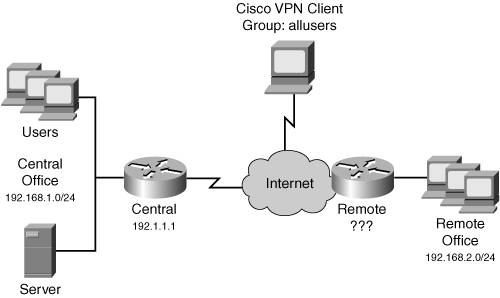
Figure 18-3 shows an example network that has both remote access and L2L sessions. In this example, the remote office network is acquiring its address dynamically, via DHCP, from its connected ISP, which also is true of the remote access clients. Because the central office router doesn't know the remote office router's IP address, you would have to configure the pre-shared key for the router as 0.0.0.0 0.0.0.0 with no XAUTH. However, doing this would cause XAUTH to not work for the remote access clients. One solution would be to use certificates instead of pre-shared keys; for small networks, though, this might not be cost-effective or practical.
Figure 18-3. Remote Access and L2L Connections
With IOS 12.2(15)T, however, you now can use ISAKMP/IKE profiles to match on other properties to determine how to do authentication during ISAKMP/IKE Phase 1, such as a client's group name, a peer's IP address, a fully qualified domain name, and other information than just the IP address of the peer. You also can define other properties to use for the ISAKMP/IKE Phase 1 connection.
Caution
Because of a bug in 12.2(15)T, the wildcarding of pre-shared keys doesn't work. This has been fixed in 12.3(3) and 12.3(2)T. Therefore, to use this feature, be sure you are running one of these two IOS versions or a later version.
The following sections will cover these topics:
- Central Office Router Configuration
- Remote Access and L2L Example Configuration
Central Office Router Configuration
When a central office router needs to terminate remote access and L2L sessions with pre-shared keys, and one or more of the L2L peers acquires its address dynamically, you can create an ISAKMP/IKE profile and use it with peers that match the components of the profile.
There are a few components you need to configure on your router to allow pre-shared keys for this particular situation above and beyond your normal configuration for L2L and remote access clients:
- A keyring, which specifies the pre-shared key to use for a peer or peers
- An ISAKMP/IKE profile for L2L peer(s)
- An ISAKMP/IKE profile for remote access clients
- A dynamic crypto map entry that specifies the ISAKMP/IKE Phase 1 profile for the remote access clients and another entry that specifies the ISAKMP/IKE Phase 1 profile for the L2L peers with dynamic IP addressing
The following sections will discuss the configuration of the above components.
Keyrings
A keyring is used to define a pre-shared key that one or more L2L peers will use. Use the following commands to configure a keyring:
Router(config)# crypto keyring keyring_name Router(conf-keyring)# description description Router(conf-keyring)# pre-shared-key address address [subnet_mask] key key Router(conf-keyring)# exit
The crypto keyring command creates the keyringeach keyring must have a unique name. This command takes you into a subcommand mode. The description command assigns a brief description to the keyring. The pre-shared-key address command assigns a pre-shared key to the keyring. For L2L peers that acquire addresses dynamically, the IP address and subnet mask should be "0.0.0.0 0.0.0.0."
L2L ISAKMP/IKE Profiles
An ISAKMP/IKE profile specifies certain properties that should be used by certain peers for establishing an ISAKMP/IKE Phase 1 connection. ISAKMP/IKE policies still need to be defined, but with the addition of profiles, you can control when certain components should be used for a peer, such as wildcarded pre-shared keys for L2L peers and group pre-shared keys for remote access groups.
You'll need to configure at least one ISAKMP/IKE profile for the L2L peers that acquire their addresses dynamically. Here is the configuration to accomplish this:
Router(config)# crypto isakmp profile ISAKMP_profile_name
Router(conf-isa-prof)# description description
Router(conf-isa-prof)# match identity address IP_address
Router(conf-isa-prof)# match identity host FQDN domain_name
Router(conf-isa-prof)# match identity host domain FQDN
Router(conf-isa-prof)# self-identity {address | fqdn}
Router(conf-isa-prof)# keyring keyring_name
Router(conf-isa-prof)# keepalive seconds
Router(conf-isa-prof)# exit
The crypto isakmp profile command creates the ISAKMP/IKE profile for Phase 1 connections. Each profile needs a unique name. This command takes you into a subcommand mode. The description command assigns a description to the profile.
The match identity commands specify how to match on a peer that should use this profile. The address parameter allows you to specify an address of a peer: if you specify 0.0.0.0, this matches on all peers. The host parameter allows you to match on a fully qualified domain name, like "router.cisco.com." The host domain parameter allows you to match on a domain name of a peer, like "cisco.com."
The self-identity command allows you to specify how the local router will identify itself to the remote router, by an IP address or a FQDN; if you omit this command, it defaults to the globally configured identity type configured with the crypto isakmp identity command, which was discussed in Chapter 16, "Router ISAKMP/IKE Phase 1 Connectivity."
The keyring command specifies the keyring (i.e., the pre-shared key) to use for peers that match the match identity commands in the ISAKMP/IKE profile. The keepalive command specifies the keepalive interval for dead peer detection (DPD).
Note
You can use ISAKMP/IKE profiles with DMVPN configurations. When you are creating your IPsec profile with the crypto ipsec profile command, in the subcommand mode, use the set isakmp-profile command to reference your ISAKMP/IKE Phase 1 profile.
Remote Access ISAKMP/IKE Profiles
For every remote access group you have, you'll need to create a separate ISAKMP/IKE profileone for each group. Here are the commands to create a profile for a remote access group:
Router(conf)# crypto isakmp profile ISAKMP_profile_name
Router(conf-isa-prof)# description description
Router(conf-isa-prof)# match identity group group_name
Router(conf-isa-prof)# match identity host FQDN domain_name
Router(conf-isa-prof)# match identity host domain FQDN
Router(conf-isa-prof)# self-identity {address | fqdn}
Router(conf-isa-prof)# client authentication list
AAA_authentication_list_name
Router(conf-isa-prof)# isakmp authorization list group_name
Router(conf-isa-prof)# client configuration address
{respond | initiate}
Router(conf-isa-prof)# keepalive seconds
Router(conf-isa-prof)# exit
Some of the ISAKMP/IKE profile commands are the same as those used for L2L peers, so I'll focus only on the ones unique to remote access groups. The match identity group command allows you to associate the specified remote access group with this particular profile. Optionally, you can further subqualify matches with FQDN or domain names. The client authentication list command associates this profile with the aaa authentication login command the router should use for XAUTH authentication. The isakmp authorization list command specifies the aaa authorization network command that is used by remote access groups that match this profile: this command gives you the flexibility to have different groups on different AAA servers, or one group on an AAA server and one group defined locally. The client configuration address command specifies whether the central office router should initiate IKE Mode Config or respond to initiations from the remote access users. For the Cisco VPN Client and other Easy VPN Remotes, set this to respond; for other clients, set it to initiate.
Dynamic Crypto Maps and Profiles
To use the ISAKMP/IKE profiles you have created, you need to reference them in a crypto map entry. For remote access users or L2L peers with dynamically acquired addresses, this is in a dynamic crypto map entry:
Router(config)# crypto dynamic-map dynamic_map_name seq_# Router(config-crypto-map)# set transform-set transform_set_name Router(config-crypto-map)# set isakmp-profile ISAKMP_profile_name
In the dynamic crypto map entry, only two commands are required:
- The set transform-set command specifies the transform set or sets that should be used to protect the data connections between the router and the remote peer.
- The set isakmp-profile command specifies the ISAKMP/IKE profile that should be used to build and manage the management connection to the remote peer.
Note
Each profile needs to be in a different dynamic crypto map entry. The profile you place in an entry does matter. The remote access group ISAKMP/IKE profiles should be placed in dynamic crypto map entries with a higher priority (lower sequence number) than the L2L profiles. If you reverse the order, the remote access users would match against the wildcarded pre-shared key in the keyring and thus fail XAUTH.
Remote Access and L2L Example Configuration
To understand how to configure both remote access and L2L peers (with dynamically acquired addresses) on the same router, I'll show you an example configuration based on the network in Figure 18-3. Example 18-11 shows the central office router's configuration that accepts the L2L and remote access sessions.
Example 18-11. Central Office Router with L2L and Remote Access Peers
Central(config)# username user secret userpassword Central(config)#!images/U2192.jpg border=0> Central(config)# aaa new-model Central(config)# aaa authentication login remoteaccess local Central(config)# aaa authorization network allusers local Central(config)# crypto isakmp policy 10 Central(config-isakmp)# encryption 3des Central(config-isakmp)# hash sha Central(config-isakmp)# authentication pre-share Central(config-isakmp)# group 2 Central(config-isakmp)# exit Central(config)# ip local pool clientpool 192.168.1.240 192.168.1.254 Central(config)# crypto isakmp client configuration group allusers Central(config-isakmp-group)# key allusers123 Central(config-isakmp-group)# dns 192.168.1.2 Central(config-isakmp-group)# wins 192.168.1.3 Central(config-isakmp-group)# domain cisco.com Central(config-isakmp-group)# pool clientpool Central(config-isakmp-group)# exit Central(config)# crypto isakmp profile allusersprofile Central(conf-isa-prof)# description Remote access users profile Central(conf-isa-prof)# match identity group allusers Central(conf-isa-prof)# client authentication list remoteaccess Central(conf-isa-prof)# isakmp authorization list allusers Central(conf-isa-prof)# client configuration address respond Central(conf-isa-prof)# keepalive 20 3 Central(conf-isa-prof)# exit Central(config)# crypto keyring L2Lkeyring Central(conf-keyring)# description Pre-shared key for L2L peers with dynamic addressing Central(conf-keyring)# pre-shared-key address 0.0.0.0 0.0.0.0 key cisco123 Central(conf-keyring)# exit Central(config)# crypto isakmp profile L2Lprofile Central(conf-isa-prof)# description All L2L peers Central(conf-isa-prof)# keyring L2Lkeyring Central(conf-isa-prof)# match identity address 0.0.0.0 Central(conf-isa-prof)# keepalive 20 3 Central(conf-isa-prof)# exit Central(config)# crypto ipsec transform-set transset esp-3des esp-sha-hmac Central(cfg-crypto-tran)# exit Central(config)# crypto dynamic-map dynmap 5 Central(config-crypto-m)# set transform-set transset Central(config-crypto-m)# set isakmp-profile allusersprofile Central(config-crypto-m)# exit Central(config)# crypto dynamic-map dynmap 10 Central(config-crypto-m)# set transform-set transset Central(config-crypto-m)# set isakmp-profile L2Lprofile Central(config-crypto-m)# exit Central(config)# crypto map staticmap 10 ipsec-isakmp dynamic dynmap Central(config)# interface Ethernet0/0 Central(config-if)# description Internet interface Central(config-if)# ip address 192.1.1.1 255.255.255.0 Central(config-if)# crypto map staticmap Central(config-if)# exit Central(config)# interface Ethernet0/1 Central(config-if)# description Local LAN interface Central(config-if)# ip address 192.168.1.1 255.255.255.0
In this example, XAUTH authentication is performed locally on the router using the username commands. One group, called "allusers," is configured. Both the VPN Client software clients and the remote office router use the same ISAKMP/IKE Phase 1 policy to build the management connection, policy 10, which uses pre-shared keys for device authentication.
The remote access group "allusers" is assigned addresses from the "clientpool" address pool. The pre-shared key is "allusers123." An ISAKMP/IKE profile is defined for the group, called "allusers," which specifies that any user from the "allusers" group (the match identity group allusers command) will use this profile to supplement the building of the management connection. XAUTH authentication is done with the aaa authentication login remote access command and authorization with the aaa authorization network allusers command.
A keyring is created for the remote office router, which is acquiring its IP address dynamically. A pre-shared key of "cisco123" is defined for all L2L routers. This key is then referenced in the ISAKMP/IKE "L2Lprofile" for the L2L routers. The match identity address 0.0.0.0 command matches on all devices.
A transform set is defined that both the remote office router and the remote access group will use. There are two dynamic crypto map entries. Notice that entry 5, the first one, references the remote access ISAKMP/IKE profile: "allusersprofile." It is important that this appears before the L2L profile because the matching is based on a group name. If you would re-order the two entries in the dynamic crypto map, because the L2L profile matches on all addresses (the match identity address 0.0.0.0 command), this would also include the remote access users, thereby not invoking XAUTH to perform user authentication. Toward the end of the configuration, the dynamic crypto map is referenced in a static crypto map and the static crypto map is activated on the central office router's Internet interface.
The remote office router is configured as normal, as shown in Example 18-12.
Example 18-12. Remote Office Router's Configuration
Remote(config)# crypto isakmp policy 10 Remote(config-isakmp)# encryption 3des Remote(config-isakmp)# authentication pre-share Remote(config-isakmp)# hash sha Remote(config-isakmp)# group 2 Remote(config-isakmp)# exit Remote(config)# crypto isakmp key cisco123 address 192.1.1.1 Remote(config)# crypto ipsec transform-set transset esp-3des esp-sha-hmac Remote(cfg-crypto-tran)# exit Remote(config)# access-list 100 permit ip 192.168.2.0 0.0.0.255 192.168.1.0 0.0.0.255 Remote(config)# crypto map staticmap 10 ipsec-isakmp Remote(config-crypto-map)# set peer 192.1.1.1 Remote(config-crypto-map)# set transform-set transset Remote(config-crypto-map)# match address 100 Remote(config-crypto-map)# exit Remote(config)# interface Ethernet0/0 Remote(config-if)# description Internet interface Remote(config-if)# ip address dhcp Remote(config-if)# crypto map staticmap Remote(config-if)# exit Remote(config)# interface Ethernet0/1 Remote(config-if)# description Local LAN interface Remote(config-if)# ip address 192.168.2.1 255.255.255.0
Part I: VPNs
Overview of VPNs
- Overview of VPNs
- Traffic Issues
- VPN Definition
- VPN Components
- VPN Designs
- VPN Implementations
- VPNs: Choosing a Solution
- Summary
VPN Technologies
IPsec
PPTP and L2TP
SSL VPNs
Part II: Concentrators
Concentrator Product Information
- Concentrator Product Information
- Concentrator Models
- Concentrator Modules
- Concentrator Features
- Introduction to Accessing a Concentrator
- Summary
Concentrator Remote Access Connections with IPsec
- Concentrator Remote Access Connections with IPsec
- Controlling Remote Access Sessions to the Concentrator
- IPsec Remote Access
- Network Access Control (NAC) for IPsec and L2TP/IPsec Users
- Summary
Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- PPTP and L2TP Remote Access
- WebVPN Remote Access
- Summary
Concentrator Site-to-Site Connections
- Concentrator Site-to-Site Connections
- L2L Connectivity Example
- ISAKMP/IKE Phase 1 Preparation
- Adding Site-to-Site Connections
- Address Translation and L2L Sessions
- Summary
Concentrator Management
- Concentrator Management
- Bandwidth Management
- Routing on the Concentrator
- Chassis Redundancy
- Administration Screens
- Summary
Verifying and Troubleshooting Concentrator Connections
- Verifying and Troubleshooting Concentrator Connections
- Concentrator Tools
- Troubleshooting Problems
- Summary
Part III: Clients
Cisco VPN Software Client
- Cisco VPN Software Client
- Cisco VPN Client Overview
- Cisco VPN Client Interface
- IPsec Connections
- VPN Client GUI Options
- VPN Client Software Updates
- VPN Client Troubleshooting
- Summary
Windows Software Client
- Windows Software Client
- Windows Client
- Configuring the Windows VPN Client
- Configuring the VPN 3000 Concentrator
- Microsoft Client Connections
- Troubleshooting VPN Connections
- Summary
3002 Hardware Client
- 3002 Hardware Client
- Overview of the 3002 Hardware Client
- Initial Access to the 3002
- Authentication and Connection Options
- Connection Modes
- Administrative Tasks
- Summary
Part IV: IOS Routers
Router Product Information
Router ISAKMP/IKE Phase 1 Connectivity
- Router ISAKMP/IKE Phase 1 Connectivity
- IPsec Preparation
- ISAKMP/IKE Phase 1 Policies
- ISAKMP/IKE Phase 1 Device Authentication
- Monitoring and Managing Management Connections
- Routers as Certificate Authorities
- Summary
Router Site-to-Site Connections
- Router Site-to-Site Connections
- ISAKMP/IKE Phase 2 Configuration
- Viewing and Managing Connections
- Issues with Site-to-Site Connections
- Summary
Router Remote Access Connections
- Router Remote Access Connections
- Easy VPN Server
- Easy VPN Remote
- IPsec Remote Access and L2L Sessions on the Same Router
- WebVPN
- Summary
Troubleshooting Router Connections
- Troubleshooting Router Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- New IPsec Troubleshooting Features
- Fragmentation Problems
- Summary
Part V: PIX Firewalls
PIX and ASA Product Information
- PIX and ASA Product Information
- PIX Deployment Scenarios
- PIX and ASA Feature and Product Overview
- Summary
PIX and ASA Site-to-Site Connections
- PIX and ASA Site-to-Site Connections
- ISAKMP/IKE Phase 1 Management Connection
- ISAKMP/IKE Phase 2 Data Connections
- L2L Connection Examples
- Summary
PIX and ASA Remote Access Connections
- PIX and ASA Remote Access Connections
- Easy VPN Server Support for 6.x
- Easy VPN Remote Support for 6.x
- Easy VPN Server Support for 7.0
- Summary
Troubleshooting PIX and ASA Connections
- Troubleshooting PIX and ASA Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- Summary
Part VI: Case Study
Case Study
Index
EAN: 2147483647
Pages: 178
- Chapter I e-Search: A Conceptual Framework of Online Consumer Behavior
- Chapter X Converting Browsers to Buyers: Key Considerations in Designing Business-to-Consumer Web Sites
- Chapter XI User Satisfaction with Web Portals: An Empirical Study
- Chapter XIII Shopping Agent Web Sites: A Comparative Shopping Environment
- Chapter XVIII Web Systems Design, Litigation, and Online Consumer Behavior
