Form Security
Before delving into the specifics of how the InfoPath event-driven programming model works, you need to understand how the security model works.
InfoPath was designed to be "secure by default" to provide protection for the end users using InfoPath to fill out your forms. As an InfoPath developer, the burden is on you to ensure your form can be deployed without problems. The method of deployment you choose can affect which parts of the InfoPath object model your code will be allowed to use. To understand how the method of deployment you choose can affect decisions during form development, take a look at the InfoPath security model.
Form Security Levels
InfoPath defines three security levels: restricted, domain, and full trust. Each InfoPath form requires and is granted a certain level. If the granted level is lower than the required level, the form will not run. This security system is enforced regardless of whether there is code behind the form.
Forms in the restricted security level can only access resources within the form template itself. A form that requires this security level must not attempt to access local files, for instance.
Forms in the domain security level can use files and connect to resources on the machine hosting the form without asking the user. If a form in the domain security level attempts to read or write information from a different machine, InfoPath prompts the user to ensure that the cross-domain access is acceptable.
Forms in the full trust security level have complete and unrestricted access to every resource that the user running the form has access to. Only forms installed to trusted locations or digitally signed with a trusted signature are fully trusted. (Deployment location and security are discussed below.)
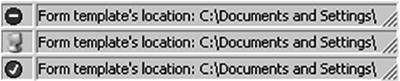
When running a form, you can see whether it was granted the restricted, domain, or full trust security level by looking at the icon in the status bar as shown in Figure 12-5.
Figure 12-5. The form's security level and location are shown in the status bar when a user fills out a form. The icons shown are for the restricted, domain, and full trust security levels, respectively.
Automatically and Manually Setting the Required Security Level
InfoPath 2003 Service Pack 1 automatically sets the required security level as you design your form. It can do so by determining which features the form uses and the minimum security level the form needs to function properly.
For example, if a form on the local intranet (\MyComputerMyShareTemplate1.xsn), posts to a Web server on the Internet (http://www.contoso.com), that is potentially dangerous. A malicious form might be attempting to trick you into entering sensitive information that would then be sent across the Internet. The form would require at a minimum the domain security level, not the restricted security level. If a user runs this form without sufficient evidence for InfoPath to grant the form the domain security level, the form will not run. Even if it is granted the domain security level, at runtime InfoPath warns the user when the form attempts to post the information to the new domain.
|
InfoPath can automatically determine the required security level by looking at the properties of the form, but it does not look at the code behind the form, and therefore might set the required security level too low. For example, if you deploy a form that successfully requests domain trust but calls XDocument.SaveAs in an event handler, the form will load but will fail at runtime if the event handler is called. In this case, InfoPath shows an error to the end user explaining there is not sufficient permission to perform the operation. |
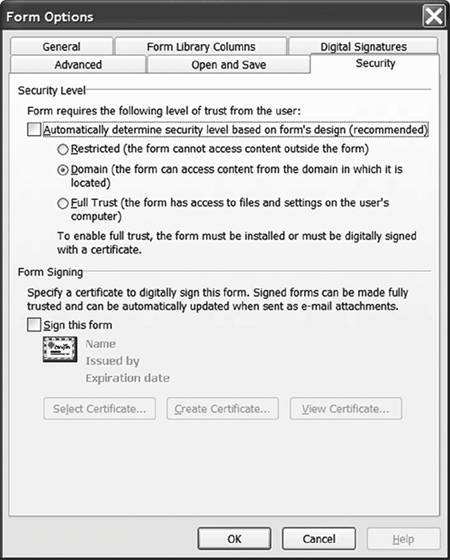
To manually change the required security level of an InfoPath form, open the form template in design mode. Select the Form Options menu item located in the Tools menu, and click the Security tab as shown in Figure 12-6.
Figure 12-6. Specifying the required security level for a form.
Deployment Location and Security
You have many options when deploying forms, and covering them completely is beyond the scope of this chapter. For the purposes of this chapter, we discuss only the impact of deployment location on security level.
You can deploy a form in two ways: the "URL" and the "URN". URL deployment is used by default when you use Save or Save As from the InfoPath designer. Use URL deployment to publish the form to some shared location such as a Web server, SharePoint site, shared network directory, and so on.
InfoPath uses Internet Explorer security settings to determine what security level to grant to URL-deployed forms. If Internet Explorer would classify the form's location as an internet or local intranet site, InfoPath will grant the form the restricted security level. If Internet Explorer thinks that the form's location is a "trusted site" or the "my computer" domain, InfoPath will grant the domain security level. Forms from locations on Internet Explorer's "restricted sites" list are not allowed to run at all.
URN deployment is necessary (but not sufficient) to ensure that InfoPath grants a form full trust. Choose Publish from the File menu of InfoPath to deploy a form to a URN. A URN-published form can be installed to the local machine or digitally signed with a trusted certificate to ensure that InfoPath fully trusts the form.
Registering a Form Template to Grant Full Trust
After you have published a form using URN deployment, the easiest way to enable a form template to be granted full trust on your machine is to call the RegisterSolution method on the form. If called from within an InfoPath form itself, this would require the full trust security level. This presents somewhat of a chicken-and-egg problem: We need to be fully trusted to register a template as fully trusted.
Fortunately, InfoPath can be automated from an automation executable, much as we automated Word and Excel in Chapter 2, "Introduction to Office Solutions." We use automation to call the RegisterSolution method; because it is not an InfoPath form calling the method, but rather a fully trusted utility program, there is no chicken-and-egg problem.
Suppose we have a mortgage application form template that we want to be a full trust form template while we are developing and debugging it. There are two ways to register the form template: We can register the .XSF file or the .XSN file.
What's the difference? If you are registering the form template so that it is fully trusted on your development machine, it makes more sense just to register the .XSF file, which can be found in the InfoPath project folder. If you are registering a form template that is going to be published to a central location for end users to use, however, register the .XSN file after publishing the form.
Listing 12-1 shows a console application that registers an .XSF file so it can be granted full trust. To use this code, create a new console application and add a reference to the InfoPath PIA.
Listing 12-1. A Console Application That Registers an XSF file So That It Can Be Granted Full Trust
using System;
using System.XML;
using InfoPath = Microsoft.Office.Interop.InfoPath;
public class RegisterForm
{
public static void Main(string[] args)
{
const string xsfLocation =
@"C:InfoPathProjectsMortgageApplicationmanifest.xsf";
// Remove the publishUrl
XMLDocument xsfDom = new XMLDocument();
xsfDom.PreserveWhitespace = true;
xsfDom.Load(xsfLocation);
XMLNamespaceManager xns =
new XMLNamespaceManager(new NameTable());
xns.AddNamespace("xsf", xsfDom.DocumentElement.NamespaceURI);
XMLNode xDoc = xsfDom.SelectSingleNode(
"/xsf:xDocumentClass", xns);
xDoc.Attributes.RemoveNamedItem("publishUrl");
xsfDom.Save(xsfLocation);
// Register the file
InfoPath.ExternalApplicationClass ip =
new InfoPath.ExternalApplicationClass();
ip.RegisterSolution(xsfLocation, "overwrite");
}
}
When registering an InfoPath form to be fully trusted, it must not have a publishUrl. A publishUrl means the solution is URL-based. Remember that URN-based solutions cannot have a URL component and also be granted full trust. The console application in Listing 12-1 removes the publishUrl (if it exists) from the .XSF form template definition and then registers the .XSF file to enable this form to run with full trust permissions on your machine.
Do not forget to select the Full Trust option in the Security tab of the Form Options dialog when designing the form on which you are going to run this console application. After you have run the console application, running the form in full trust is as easy as double-clicking the manifest.xsf file.
More Information
A full discussion of the InfoPath security model and deployment system is beyond the scope of this book. For more information, refer to the InfoPath SDK documents titled "Security Guidelines for Developing InfoPath Forms" and "Form Security Model" available on MSDN at http://msdn.microsoft.com/library/en-us/ipsdk/html/ipsdkSecureAForm_HV01083590.asp and http://msdn.microsoft.com/library/en-us/ipsdk/html/ipsdkFormSecurityModel_HV01083562.asp.
For more information about digitally signing your form template, see the InfoPath Team Blog at http://blogs.msdn.com/infopath/archive/2004/05/10/129216.aspx. The InfoPath SDK, also available on MSDN, discusses using the RegForm tool to help form designers create installable form templates.
Part One. An Introduction to VSTO
An Introduction to Office Programming
- Why Office Programming?
- Office Object Models
- Properties, Methods, and Events
- The Office Primary Interop Assemblies (PIAs)
- Conclusion
Introduction to Office Solutions
- The Three Basic Patterns of Office Solutions
- Office Automation Executables
- Office Add-Ins
- Code Behind a Document
- Conclusion
Part Two. Office Programming in .NET
Programming Excel
- Ways to Customize Excel
- Programming User-Defined Functions
- Introduction to the Excel Object Model
- Conclusion
Working with Excel Events
Working with Excel Objects
- Working with Excel Objects
- Working with the Application Object
- Working with the Workbooks Collection
- Working with the Workbook Object
- Working with the Worksheets, Charts, and Sheets Collections
- Working with Document Properties
- Working with the Windows Collections
- Working with the Window Object
- Working with the Names Collection and Name Object
- Working with the Worksheet Object
- Working with the Range Object
- Special Excel Issues
- Conclusion
Programming Word
Working with Word Events
Working with Word Objects
- Working with Word Objects
- Working with the Application Object
- Working with the Dialog Object
- Working with Windows
- Working with Templates
- Working with Documents
- Working with a Document
- Working with the Range Object
- Working with Bookmarks
- Working with Tables
- Conclusion
Programming Outlook
- Ways to Customize Outlook
- Introduction to the Outlook Object Model
- Introduction to the Collaboration Data Objects
- Conclusion
Working with Outlook Events
Working with Outlook Objects
- Working with Outlook Objects
- Working with the Application Object
- Working with the Explorers and Inspectors Collections
- Working with the Explorer Object
- Working with the Inspector Object
- Working with the NameSpace Object
- Working with the MAPIFolder Object
- Working with the Items Collection
- Properties and Methods Common to Outlook Items
- Outlook Issues
- Conclusion
Introduction to InfoPath
- What Is InfoPath?
- Getting Started
- Form Security
- Programming InfoPath
- Data Source Events
- Form Events, Properties, and Methods
- Conclusion
Part Three. Office Programming in VSTO
The VSTO Programming Model
- The VSTO Programming Model
- VSTO Extensions to Word and Excel Objects
- Dynamic Controls
- Advanced Topic: Dynamic Host Items
- Advanced Topic: Inspecting the Generated Code
- VSTO Extensions to the Word and Excel Object Models
- Conclusion
Using Windows Forms in VSTO
- Using Windows Forms in VSTO
- Introduction
- Adding Windows Forms Controls to Your Document
- Writing Code Behind a Control
- The Windows Forms Control Hosting Architecture
- Properties Merged from OLEObject or OLEControl
- Adding Controls at Runtime
- Conclusion
Working with Actions Pane
Working with Smart Tags in VSTO
- Introduction to Smart Tags
- Creating Document-Level Smart Tags with VSTO
- Creating Application-Level Smart Tags
- Conclusion
VSTO Data Programming
- VSTO Data Programming
- Creating a Data-Bound Customized Spreadsheet with VSTO
- Creating a Data-Bound Customized Word Document with VSTO
- Datasets, Adapters, and Sources
- Another Technique for Creating Data-Bound Spreadsheets
- Caching Data in the Data Island
- Advanced ADO.NET Data Binding: Looking Behind the Scenes
- Binding-Related Extensions to Host Items and Host Controls
- Conclusion
Server Data Scenarios
- Populating a Document with Data on the Server
- Using ServerDocument and ASP.NET
- A Handy Client-Side ServerDocument Utility
- The ServerDocument Object Model
- Conclusion
.NET Code Security
- .NET Code Security
- Code Access Security Versus Role-Based Security
- Code Access Security in .NET
- Location, Location, Location
- Strong Names
- Publisher Certificates
- Trusting the Document
- Deploying Policy to User Machines
- Conclusion
Deployment
- Deployment
- VSTO Prerequisites
- Deploying to an Intranet Shared Directory or Web Site
- Local Machine Deployment Without a Deployment Manifest
- Editing Manifests
- Creating Setup Packages
- Advanced Topic: Deploying Network Solutions to Be Cached Locally
- Conclusion
Part Four. Advanced Office Programming
Working with XML in Excel
- Introduction to Excels XML Features
- Introduction to XML Schema Creation in Visual Studio
- An End-to-End Scenario
- Advanced XML Features in Excel
- Excel-Friendly XML Schemas
- VSTO Support for Excel Schema Mapping
- Conclusion
Working with XML in Word
- Introduction to Words XML Features
- An End-to-End Scenario: Creating a Schema and Mapping It into a Word Document
- Exporting the Mapped XML in the Document to an XML Data File
- Importing an XML Data File into the Mapped Document
- The XML Options Dialog
- VSTO Support for Word Schema Mapping
- VSTO Support for the WordML File Format
- Conclusion
Developing COM Add-Ins for Word and Excel
- Introduction to Add-Ins
- Scenarios for Using Add-Ins
- How a COM Add-In Is Registered
- Implementing IDTExtensibility2
- Writing a COM Add-In Using Visual Studio
- The Pitfalls of MsCoree.dll
- COM Interop and Regasm.exe
- Shimming: A Solution to the Problems with MsCoree.dll
- Conclusion
Creating Outlook Add-Ins with VSTO
EAN: N/A
Pages: 214
