Types of IPsec VPNs
VPNs, as discussed in this book, come in one of two flavors: site-to-site or remote user. Most organizations deploy a mix of these two VPN types to meet their specific needs.
Site-to-Site VPNs
Site-to-site VPNs are also known as LAN-to-LAN or gateway-to-gateway VPNs. They are built around the idea that the benefits IPsec provides are not needed from host to host, only from one location to another. A common site-to-site VPN is shown in Figure 10-1.
Figure 10-1. Site-to-Site VPN
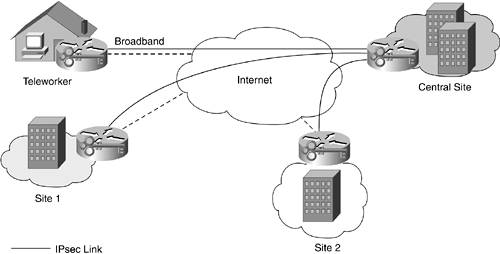
Site-to-site VPNs can be used as private WAN security solutions, private WAN replacements, or private WAN backups. There are three major reasons for deploying a site-to-site VPN. First, in the case of a security solution to an existing private WAN, all communications are encrypted and authenticated before they enter the SP's network. Second, site-to-site VPNs are quick to get started. Business partners looking to communicate with one another can do so easily, provided they both have an Internet connection. The same is true for companies merging with one another. An IPsec link can be built in hours, not weeks, as is generally needed for dedicated circuits. Finally, site-to-site VPNs offer a substantial cost savings over private WAN links in certain situations. The country from which you operate and the distance between sites factors in when considering any savings. Long-haul international connections are ideal candidates for site-to-site VPNs.
Remote User VPNs
Remote user VPNs are also called remote access or host-to-gateway VPNs. They are generally deployed as a remote connectivity option to augment or replace traditional dial-up Public Switched Telephone Network (PSTN) links, as shown in Figure 10-2.
Figure 10-2. Remote User VPN
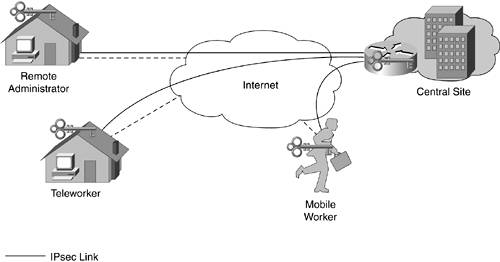
By far, the most common method of deploying remote user VPNs is to use an IPsec software client that resides on the remote host, which then connects to an IPsec gateway. This client connects to an IPsec gateway of some kind, as shown in Figure 10-2. By migrating to a remote user IPsec VPN instead of using traditional dial-up links, you can achieve the "holy grail" of IT: save money and provide a better service to your users. This is because now a remote worker can use an existing home broadband link, or perhaps one provided by your organization, to connect at high speed to your central site. While on the road, the user can take advantage of WLAN links in airports and hotels instead of connecting at slow speeds over PSTN. The cost savings for your organization comes in three forms:
- You can eliminate your network access servers and modem banks. (This is partially offset by the need to buy new IPsec gateways.)
- More important, you can eliminate the recurring telecom charges for all the digital or analog phone lines you need to support at the head end for traditional dial-in.
- Still more important, by using high-speed public connectivity options that are insecure without IPsec, users are able to do more while on the road than when they have only dial-up.
To ensure that your remote users are able to get connectivity when all they have access to is a phone line, many organizations contract with nationwide (or worldwide) Internet service providers (ISPs) to provide local phone numbers for user access.
NOTE
You might have noticed that teleworkers were in both the site-to-site topology (Figure 10-1) and the remote user topology (Figure 10-2). How teleworkers are classified largely depends on their method of connectivity. When connecting using a software IPsec client running on a host, they are considered remote users. When connecting using a hardware device of some kind, they are more like site-to-site links. In this case, their home LAN becomes almost like a very small satellite office. There are some caveats to these classifications, which are highlighted in Chapter 15, "Teleworker Security Design."
Part I. Network Security Foundations
Network Security Axioms
- Network Security Axioms
- Network Security Is a System
- Business Priorities Must Come First
- Network Security Promotes Good Network Design
- Everything Is a Target
- Everything Is a Weapon
- Strive for Operational Simplicity
- Good Network Security Is Predictable
- Avoid Security Through Obscurity
- Confidentiality and Security Are Not the Same
- Applied Knowledge Questions
Security Policy and Operations Life Cycle
- Security Policy and Operations Life Cycle
- You Cant Buy Network Security
- What Is a Security Policy?
- Security System Development and Operations Overview
- References
- Applied Knowledge Questions
Secure Networking Threats
- Secure Networking Threats
- The Attack Process
- Attacker Types
- Vulnerability Types
- Attack Results
- Attack Taxonomy
- References
- Applied Knowledge Questions
Network Security Technologies
- Network Security Technologies
- The Difficulties of Secure Networking
- Security Technologies
- Emerging Security Technologies
- References
- Applied Knowledge Questions
Part II. Designing Secure Networks
Device Hardening
- Device Hardening
- Components of a Hardening Strategy
- Network Devices
- NIDS
- Host Operating Systems
- Applications
- Appliance-Based Network Services
- Rogue Device Detection
- References
- Applied Knowledge Questions
General Design Considerations
- General Design Considerations
- Physical Security Issues
- Layer 2 Security Considerations
- IP Addressing Design Considerations
- ICMP Design Considerations
- Routing Considerations
- Transport Protocol Design Considerations
- DoS Design Considerations
- References
- Applied Knowledge Questions
Network Security Platform Options and Best Deployment Practices
Common Application Design Considerations
- Common Application Design Considerations
- DNS
- HTTP/HTTPS
- FTP
- Instant Messaging
- Application Evaluation
- References
- Applied Knowledge Questions
Identity Design Considerations
- Identity Design Considerations
- Basic Foundation Identity Concepts
- Types of Identity
- Factors in Identity
- Role of Identity in Secure Networking
- Identity Technology Guidelines
- Identity Deployment Recommendations
- References
- Applied Knowledge Questions
IPsec VPN Design Considerations
- IPsec VPN Design Considerations
- VPN Basics
- Types of IPsec VPNs
- IPsec Modes of Operation and Security Options
- Topology Considerations
- Design Considerations
- Site-to-Site Deployment Examples
- IPsec Outsourcing
- References
- Applied Knowledge Questions
Supporting-Technology Design Considerations
- Supporting-Technology Design Considerations
- Content
- Load Balancing
- Wireless LANs
- IP Telephony
- References
- Applied Knowledge Questions
Designing Your Security System
- Designing Your Security System
- Network Design Refresher
- Security System Concepts
- Impact of Network Security on the Entire Design
- Ten Steps to Designing Your Security System
- Applied Knowledge Questions
Part III. Secure Network Designs
Edge Security Design
- Edge Security Design
- What Is the Edge?
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Edge Security Design
- Medium Network Edge Security Design
- High-End Resilient Edge Security Design
- Provisions for E-Commerce and Extranet Design
- References
- Applied Knowledge Questions
Campus Security Design
- Campus Security Design
- What Is the Campus?
- Campus Trust Model
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Campus Security Design
- Medium Network Campus Security Design
- High-End Resilient Campus Security Design
- References
- Applied Knowledge Questions
Teleworker Security Design
- Teleworker Security Design
- Defining the Teleworker Environment
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Software-Based Teleworker Design
- Hardware-Based Teleworker Design
- Design Evaluations
- Applied Knowledge Questions
Part IV. Network Management, Case Studies, and Conclusions
Secure Network Management and Network Security Management
- Secure Network Management and Network Security Management
- Utopian Management Goals
- Organizational Realities
- Protocol Capabilities
- Tool Capabilities
- Secure Management Design Options
- Network Security Management Best Practices
- References
- Applied Knowledge Questions
Case Studies
- Case Studies
- Introduction
- Real-World Applicability
- Organization
- NetGamesRUs.com
- University of Insecurity
- Black Helicopter Research Limited
- Applied Knowledge Questions
Conclusions
- Conclusions
- Introduction
- Management Problems Will Continue
- Security Will Become Computationally Less Expensive
- Homogeneous and Heterogeneous Networks
- Legislation Should Garner Serious Consideration
- IP Version 6 Changes Things
- Network Security Is a System
References
Appendix A. Glossary of Terms
Appendix B. Answers to Applied Knowledge Questions
Appendix C. Sample Security Policies
INFOSEC Acceptable Use Policy
Password Policy
Guidelines on Antivirus Process
Index
EAN: 2147483647
Pages: 249
