Strive for Operational Simplicity
Network designers make decisions regarding operational complexity every day. Most don't call it that, though; they tend to think along the lines of the difficulty and burden that specific technology places on administrators or users. This section gets to a key aspect of your network security system: achieving operational simplicity can mean the difference between a security system that works for you and a security system that you work for.
Some hard and soft metrics to measure your system include the following:
- How many INFOSEC engineers does it take to maintain the system?
- When tensions are elevated when you are under real attack, how easy is it for a security operator to make a mistake?
- When searching for attack details, how much logging data must you sift through to find the pertinent information?
- When turning over forensic evidence to law enforcement, how easy is it to collate the relevant information?
Don't take the notion of operational simplicity too far, however. For example, operational simplicity is often not improved by topological simplicity. I've heard designers associate topological simplicity with such terms as "elegance." Unfortunately, as any fashion designer will tell you, elegance often flies right in the face of utility, which is a critical aspect of any security system. If you can't respond to the threats you encounter in an easy and obvious way, any amount of "elegance" you achieve through topological simplicity is meaningless.
As an example, let's look at the traditional design of Internet edges. I've seen many network edges that resemble the network shown in Figure 1-4.
Figure 1-4. Traditional Internet Edge Design

Often the network edge looks this way not because it was the best way to design the network, but because the company's security policy dictated that all traffic flow through a single "choke point." Although the design is topologically simple, it has lots of problems. The one on which I focus in this discussion is the potential for human error, or operational complexity. Human error is one of the biggest root causes of configuration problems, especially at 2 a.m. when security administrators find themselves troubleshooting an issue.
Although the design shown in Figure 1-4 might seem simple, in fact it is needlessly difficult because of its operational complexity. The configuration on the firewall and attached switch in this example are so complex and prone to operator error that the slightest mistake causes the entire security deployment to be compromised.
To remedy this problem, create a network that at first glance introduces much more topological complexity, as shown in Figure 1-5.
Figure 1-5. Design with Operational Simplicity
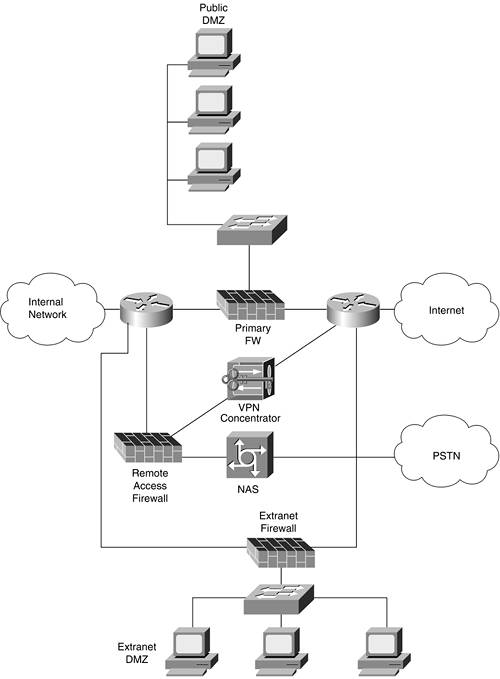
The topology in Figure 1-5 shows an implementation that is easy to understand and much harder to misconfigure. Although it has more devices and doesn't look as "elegant" as the previous example in Figure 1-4, the paths of communication and the insecure and secure parts of the network are much more apparent and securely segmented. In this amended design, outbound Internet access is handled by one firewall, and inbound virtual private network (VPN) access is handled by another firewall with a VPN device. In addition, separate L2 switches are deployed as opposed to relying on a single switch with multiple VLANs. In the heat of the moment, the access rules and potential configuration changes are much simpler.
To ensure operational simplicity, you must constantly evaluate the level of complexity you are comfortable with to ensure that your security is both simple to deploy and straightforward to maintain. Throughout this book, I offer many alternate designs for secure network architectures. Although often some level of topological complexity is introduced to solve a particularly hard problem, all the designs strive toward simplicity of planning, design, implementation, and, most important, operation.
Part I. Network Security Foundations
Network Security Axioms
- Network Security Axioms
- Network Security Is a System
- Business Priorities Must Come First
- Network Security Promotes Good Network Design
- Everything Is a Target
- Everything Is a Weapon
- Strive for Operational Simplicity
- Good Network Security Is Predictable
- Avoid Security Through Obscurity
- Confidentiality and Security Are Not the Same
- Applied Knowledge Questions
Security Policy and Operations Life Cycle
- Security Policy and Operations Life Cycle
- You Cant Buy Network Security
- What Is a Security Policy?
- Security System Development and Operations Overview
- References
- Applied Knowledge Questions
Secure Networking Threats
- Secure Networking Threats
- The Attack Process
- Attacker Types
- Vulnerability Types
- Attack Results
- Attack Taxonomy
- References
- Applied Knowledge Questions
Network Security Technologies
- Network Security Technologies
- The Difficulties of Secure Networking
- Security Technologies
- Emerging Security Technologies
- References
- Applied Knowledge Questions
Part II. Designing Secure Networks
Device Hardening
- Device Hardening
- Components of a Hardening Strategy
- Network Devices
- NIDS
- Host Operating Systems
- Applications
- Appliance-Based Network Services
- Rogue Device Detection
- References
- Applied Knowledge Questions
General Design Considerations
- General Design Considerations
- Physical Security Issues
- Layer 2 Security Considerations
- IP Addressing Design Considerations
- ICMP Design Considerations
- Routing Considerations
- Transport Protocol Design Considerations
- DoS Design Considerations
- References
- Applied Knowledge Questions
Network Security Platform Options and Best Deployment Practices
Common Application Design Considerations
- Common Application Design Considerations
- DNS
- HTTP/HTTPS
- FTP
- Instant Messaging
- Application Evaluation
- References
- Applied Knowledge Questions
Identity Design Considerations
- Identity Design Considerations
- Basic Foundation Identity Concepts
- Types of Identity
- Factors in Identity
- Role of Identity in Secure Networking
- Identity Technology Guidelines
- Identity Deployment Recommendations
- References
- Applied Knowledge Questions
IPsec VPN Design Considerations
- IPsec VPN Design Considerations
- VPN Basics
- Types of IPsec VPNs
- IPsec Modes of Operation and Security Options
- Topology Considerations
- Design Considerations
- Site-to-Site Deployment Examples
- IPsec Outsourcing
- References
- Applied Knowledge Questions
Supporting-Technology Design Considerations
- Supporting-Technology Design Considerations
- Content
- Load Balancing
- Wireless LANs
- IP Telephony
- References
- Applied Knowledge Questions
Designing Your Security System
- Designing Your Security System
- Network Design Refresher
- Security System Concepts
- Impact of Network Security on the Entire Design
- Ten Steps to Designing Your Security System
- Applied Knowledge Questions
Part III. Secure Network Designs
Edge Security Design
- Edge Security Design
- What Is the Edge?
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Edge Security Design
- Medium Network Edge Security Design
- High-End Resilient Edge Security Design
- Provisions for E-Commerce and Extranet Design
- References
- Applied Knowledge Questions
Campus Security Design
- Campus Security Design
- What Is the Campus?
- Campus Trust Model
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Campus Security Design
- Medium Network Campus Security Design
- High-End Resilient Campus Security Design
- References
- Applied Knowledge Questions
Teleworker Security Design
- Teleworker Security Design
- Defining the Teleworker Environment
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Software-Based Teleworker Design
- Hardware-Based Teleworker Design
- Design Evaluations
- Applied Knowledge Questions
Part IV. Network Management, Case Studies, and Conclusions
Secure Network Management and Network Security Management
- Secure Network Management and Network Security Management
- Utopian Management Goals
- Organizational Realities
- Protocol Capabilities
- Tool Capabilities
- Secure Management Design Options
- Network Security Management Best Practices
- References
- Applied Knowledge Questions
Case Studies
- Case Studies
- Introduction
- Real-World Applicability
- Organization
- NetGamesRUs.com
- University of Insecurity
- Black Helicopter Research Limited
- Applied Knowledge Questions
Conclusions
- Conclusions
- Introduction
- Management Problems Will Continue
- Security Will Become Computationally Less Expensive
- Homogeneous and Heterogeneous Networks
- Legislation Should Garner Serious Consideration
- IP Version 6 Changes Things
- Network Security Is a System
References
Appendix A. Glossary of Terms
Appendix B. Answers to Applied Knowledge Questions
Appendix C. Sample Security Policies
INFOSEC Acceptable Use Policy
Password Policy
Guidelines on Antivirus Process
Index
EAN: 2147483647
Pages: 249
