Attacker Types
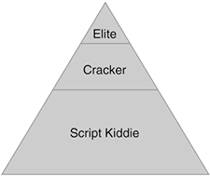
Network attackers have a wide variety of backgrounds, experience levels, and objectives. Any attempt to categorize them can't possibly succeed on all counts. Some categorizations define 26 kinds of attackers, although this does not necessarily help you design your security architecture. To adhere to the persistent theme in this book, the categorization presented here focuses on simplicity and relevance to the network designer. Figure 3-3 shows three types of attackersscript kiddie, cracker, and elitein proportions roughly analogous to their actual numbers.
Figure 3-3. Attacker Types
NOTE
Attackers are a notoriously hard group to track. I don't have any hard data to back up my estimations on attacker group sizes. Figure 3-3 is based purely on my own empirical data.
The next sections describe each type of attacker in more detail.
Script Kiddie
On the bottom tier of Figure 3-3, you see the ever popular "script kiddie." Script kiddies are so named because stereotypically they are young and often have very little real hacking talent, hence the need to use scripts that do the bulk of the work for them. For as little as they know about attacking networks, script kiddies usually know far more about protecting computers and common vulnerabilities than the average citizen. The motivations of a script kiddie are varied, but generally these attackers do not discriminate in who they attack. Script kiddies prefer to use an attack sequence that they learn and attempt to use it over and over again to seek out resources that are vulnerable to their specific attack.
NOTE
Although hopefully none of the readers of this book are setting out to be script kiddies, it is useful to understand just how easy it is to become one and cause real damage on the Internet today. Here's a description of how to be a script kiddie in seven easy steps:
|
1. |
Install some variety of UNIX on a spare machine. |
|
2. |
Spend a lot of time on Internet Relay Chat (IRC) learning the signature speaking style of your fellow kiddies; try to pick up as much information as you can. |
|
3. |
Subscribe to BugTraq and vuln-dev. You needn't even directly contribute to any discussions, and these lists will provide you with your attack tools. |
|
4. |
Watch the posts for a new vulnerability affecting large numbers of users (such as a problem with a popular web server, for example). |
|
5. |
Using a network scanner such as Nmap, find systems on the Internet that might be vulnerable to this attack. |
|
6. |
Take the sample code provided on the mailing list and run it against the systems you suspect might be vulnerable. |
|
7. |
Use the compromised systems to attack other systems, launch denial of service (DoS) attacks, disclose confidential information, and so on. |
The key thing to remember as a network designer is that script kiddies don't necessarily care whether there is anything of value on your machine. Many will be happy to compromise the machine anyway and use it to attack other systems, potentially attracting unwanted attention to your organization.
Cracker
The middle tier of attackers comprises more experienced and more dangerous opponents. They are distinguished from script kiddies in their ability to think up and launch new attacks against specific targets. Although this group is not easily labeled, "cracker" and "black hat" have both been used in various publications. The one term that should not be used to describe this group is "hacker," which used to be, and for many still is, a badge of honor. The Jargon File (http://www.jargon.org) defines hacker (among other similar definitions) as follows:
A person who enjoys exploring the details of programmable systems and how to stretch their capabilities, as opposed to most users, who prefer to learn only the minimum necessary.
The Jargon File defines cracker as follows:
One who breaks security on a system.
The Jargon File goes on to say that the term cracker was coined in 1985 by hackers in an attempt to offer the media an alternative to calling malicious network intruders "hackers." Unfortunately, this fight was lost in the mainstream media. When the media says "hacker," they mean the person doing the illegal stuff.
NOTE
I personally find the term cracker a bit silly and tough to read in paragraphs where it occurs more than once or twice. Instead, the term attacker is used throughout this book to denote an individual who attempts to gain unauthorized access to information assets.
Elite
Finally, the top tier includes the people you rarely read about and certainly don't want attacking your network, the attacker elite. They are the well-paid corporate spies, government-funded information warfare groups, political radicals, and terrorists. Although not always, you can expect this group to be better funded and have very specific targets that they attack relentlessly.
NOTE
I am always a bit cautious about bringing up this category of top-tier attackers because mentioning them is most often used as a scare tactic when selling security products to big business. "Hey, Mr. Customer, you must buy our new product or your competitor's spies will get you." The fact is, the threat from these sorts of individuals is real but generally for a very specific type of organization under very specific circumstances. If you manage a network that controls a critical infrastructure in your country (electric power, water, emergency services, and so on), you should be concerned about the risk. Likewise, if you work in a competitive market in which your intellectual property is of very high value, it would be naive to assume that all of your competitors are law-abiding citizens.
Part I. Network Security Foundations
Network Security Axioms
- Network Security Axioms
- Network Security Is a System
- Business Priorities Must Come First
- Network Security Promotes Good Network Design
- Everything Is a Target
- Everything Is a Weapon
- Strive for Operational Simplicity
- Good Network Security Is Predictable
- Avoid Security Through Obscurity
- Confidentiality and Security Are Not the Same
- Applied Knowledge Questions
Security Policy and Operations Life Cycle
- Security Policy and Operations Life Cycle
- You Cant Buy Network Security
- What Is a Security Policy?
- Security System Development and Operations Overview
- References
- Applied Knowledge Questions
Secure Networking Threats
- Secure Networking Threats
- The Attack Process
- Attacker Types
- Vulnerability Types
- Attack Results
- Attack Taxonomy
- References
- Applied Knowledge Questions
Network Security Technologies
- Network Security Technologies
- The Difficulties of Secure Networking
- Security Technologies
- Emerging Security Technologies
- References
- Applied Knowledge Questions
Part II. Designing Secure Networks
Device Hardening
- Device Hardening
- Components of a Hardening Strategy
- Network Devices
- NIDS
- Host Operating Systems
- Applications
- Appliance-Based Network Services
- Rogue Device Detection
- References
- Applied Knowledge Questions
General Design Considerations
- General Design Considerations
- Physical Security Issues
- Layer 2 Security Considerations
- IP Addressing Design Considerations
- ICMP Design Considerations
- Routing Considerations
- Transport Protocol Design Considerations
- DoS Design Considerations
- References
- Applied Knowledge Questions
Network Security Platform Options and Best Deployment Practices
Common Application Design Considerations
- Common Application Design Considerations
- DNS
- HTTP/HTTPS
- FTP
- Instant Messaging
- Application Evaluation
- References
- Applied Knowledge Questions
Identity Design Considerations
- Identity Design Considerations
- Basic Foundation Identity Concepts
- Types of Identity
- Factors in Identity
- Role of Identity in Secure Networking
- Identity Technology Guidelines
- Identity Deployment Recommendations
- References
- Applied Knowledge Questions
IPsec VPN Design Considerations
- IPsec VPN Design Considerations
- VPN Basics
- Types of IPsec VPNs
- IPsec Modes of Operation and Security Options
- Topology Considerations
- Design Considerations
- Site-to-Site Deployment Examples
- IPsec Outsourcing
- References
- Applied Knowledge Questions
Supporting-Technology Design Considerations
- Supporting-Technology Design Considerations
- Content
- Load Balancing
- Wireless LANs
- IP Telephony
- References
- Applied Knowledge Questions
Designing Your Security System
- Designing Your Security System
- Network Design Refresher
- Security System Concepts
- Impact of Network Security on the Entire Design
- Ten Steps to Designing Your Security System
- Applied Knowledge Questions
Part III. Secure Network Designs
Edge Security Design
- Edge Security Design
- What Is the Edge?
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Edge Security Design
- Medium Network Edge Security Design
- High-End Resilient Edge Security Design
- Provisions for E-Commerce and Extranet Design
- References
- Applied Knowledge Questions
Campus Security Design
- Campus Security Design
- What Is the Campus?
- Campus Trust Model
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Small Network Campus Security Design
- Medium Network Campus Security Design
- High-End Resilient Campus Security Design
- References
- Applied Knowledge Questions
Teleworker Security Design
- Teleworker Security Design
- Defining the Teleworker Environment
- Expected Threats
- Threat Mitigation
- Identity Considerations
- Network Design Considerations
- Software-Based Teleworker Design
- Hardware-Based Teleworker Design
- Design Evaluations
- Applied Knowledge Questions
Part IV. Network Management, Case Studies, and Conclusions
Secure Network Management and Network Security Management
- Secure Network Management and Network Security Management
- Utopian Management Goals
- Organizational Realities
- Protocol Capabilities
- Tool Capabilities
- Secure Management Design Options
- Network Security Management Best Practices
- References
- Applied Knowledge Questions
Case Studies
- Case Studies
- Introduction
- Real-World Applicability
- Organization
- NetGamesRUs.com
- University of Insecurity
- Black Helicopter Research Limited
- Applied Knowledge Questions
Conclusions
- Conclusions
- Introduction
- Management Problems Will Continue
- Security Will Become Computationally Less Expensive
- Homogeneous and Heterogeneous Networks
- Legislation Should Garner Serious Consideration
- IP Version 6 Changes Things
- Network Security Is a System
References
Appendix A. Glossary of Terms
Appendix B. Answers to Applied Knowledge Questions
Appendix C. Sample Security Policies
INFOSEC Acceptable Use Policy
Password Policy
Guidelines on Antivirus Process
Index
EAN: 2147483647
Pages: 249
