Security and the Stack
Apply Your Knowledge
The best way to understand packet structure is to use a packet analyzer. One good choice is Packetyzer, www.packetyzer.com. This Windows-based packet sniffer is based on Ethereal, is free, and features an easy-to-use GUI interface.
Exercises
2.1. Install a Sniffer and Perform Packet Captures
In this exercise, you will walk through the steps needed to install and use a packet analyzer. You will configure the packet analyzer to capture traffic in promiscuous mode and will examine the structure of TCP/IP traffic.
Estimated Time: 30 minutes.
- Go to the Packetyzer website located at www.packetyzer.com and download the Packetyzer application.
- Install the Packetyzer application along with Winpcap, if required. You might be asked to reboot the computer.
- Take a few minutes to review the Packetyzer user guide. This PDF can be found in the folder that you installed Packetyzer into.
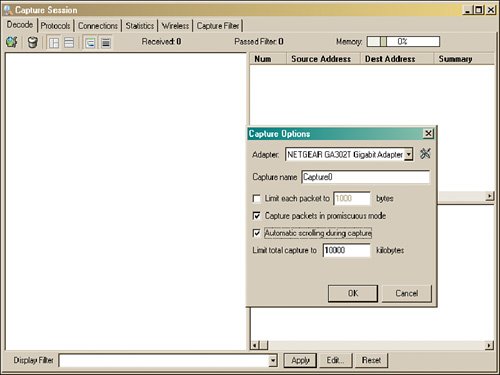
- Start Packetyzer; you will be presented with a screen requesting that you configure the capture options as shown in Figure 2.11.
Figure 2.11. Capture settings.
Exam Alert
If you have problems loading or using Winpcap, an alternative to using this sniffer would be to use Ethereal that was compiled by www.packetstuff.com. The version from packetstuff.com does not require you to install the Winpcap library.
- With the capture settings configured, you will be ready to start a packet capture. Select Session, Start Capture. You will now begin to capture traffic.
- Open a command prompt and type ping www.yahoo.com.
- Return to Packetyzer and stop the capture by choosing Session, Stop Capture.
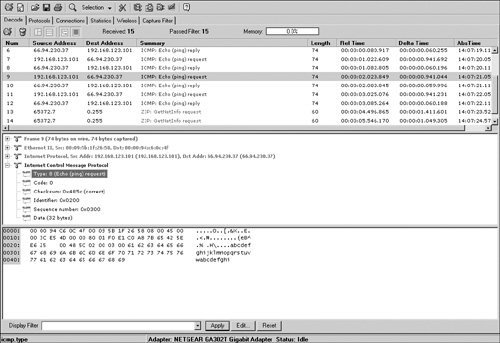
- As shown in Figure 2.12, Packetyzer has three screens. The top section or screen is known as the summary section. It contains a quick one-line description of the frame. The middle screen is considered the detail screen. It contains a detailed interpretation of the frame. The bottom most screen is the hexadecimal screen. It contains a hex dump of the individual frame, and to the right you will see readable information. Usernames, passwords, or other cleartext will be readable here.
Figure 2.12. View capture.
- Note the buttons for moving within frames or for selecting a different area of a packet. Spend some time becoming familiar with moving between frames and learning how to move about the display. You can also shrink or enlarge a specific frame by dragging the breakpoints between screens.
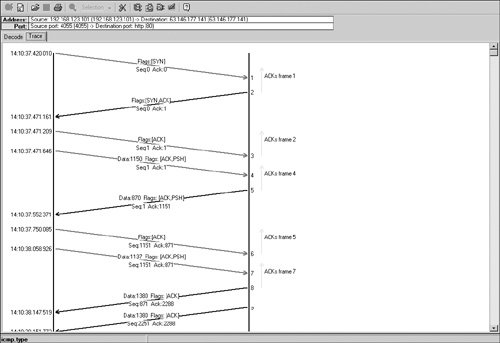
- If you captured any TCP traffic during the capture, right-click on one of the frames shown in the summary section and choose Follow TCP Flow. You will see a screen similar to the one shown in Figure 2.13.
- If you examine Figure 2.13 closely, you can see the four steps of the TCP shutdown. See if you can identify the proper flag sequence.
Figure 2.13. TCP flow.
2.2. List the Protocols, Applications, and Services Found at Each Layer of the Stack
In this exercise, you will list the various layers, the protocols that function at each layer, and which attacks they are vulnerable to.
Estimated Time: 30 minutes.
- Using the information found in the Chapter, complete the following table.
Layer
Layer Responsibility
Protocol or Ports
Potential Attacks
Application
Host-to-host
Internet
Network Access
- Once you complete the table, compare it to the following.
Layer
Layer Responsibility
Protocol or Ports
Potential Attacks
Application
Communication with applications
FTP, SNMP, Telnet, HTTP, SMTP, DNS, SSH
Password capture, spoofing, DNS poisoning, enumeration
Host-to-host
Connection and connectionless communciation
TCP and UDP
DoS, Session hijacking, scanning
Internet
Deliver of data, error and diagnostics, address resolution
IP, ICMP, and ARP
Routing attacks, fragmentation attacks, diagnostics, man-in-the-middle attacks
Network access
Physical layer delivery
PPP, SLIP
MAC address spoofing
Exam Questions
| 1. |
When referring to the domain name service, what is a zone?
|
| 2. |
You have gone to an organization's website to gather information, such as employee names, email addresses, and phone numbers. Which step of the hacker's methodology does this correspond to?
|
| 3. |
Kevin and his friends are going through a local IT firm's garbage. Which of the following best describes this activity?
|
| 4. |
You've just captured some packets that you believe to be forged. They all begin with the following hex values when viewed with an analyzer: Ethernet II = 00 00 9C C6 4C 4F FF FF FF FF FF FF 08 00. Which of the following statements is true?
|
| 5. |
The Nimda worm took advantage of this application to quickly move data from outside the firewall to a targeted web server.
|
| 6. |
This application uses clear text community strings that default to public and private. Which of the following represents the correct port and protocol?
|
| 7. |
Which of the following attacks is considered a type of overlapping fragment attack, and what protocol does it alter?
|
| 8. |
What flags are set on the second step of the three-way TCP handshake?
|
| 9. |
What flag sequence is set in a TCP packet to terminate an abnormal transmission?
|
| 10. |
Which rule means that all ports and applications are turned off, and only the minimum number of applications and services are turned on that are needed to accomplish the organization's goals?
|
| 11. |
During a packet capture, you have found several packets with the same IPID. You believe these packets to be fragmented. One of the packets has an offset value of 5dc hex, and the more bit is off. With this information, which of the following statements is true?
|
| 12. |
You have just started using traceroute and were told that it can use ICMP time exceeded messages to determine the route a packet takes. Which of the following ICMP type codes map to time exceeded?
|
| 13. |
Which layer of the OSI model could ARP poisoning occur?
|
| 14. |
Which type of attack sends fake entries to a DNS server to corrupt the information stored there?
|
| 15. |
In which layer of the OSI model do SYN attacks occur?
|
| 16. |
Blackhat Bob would like to redirect his coworker's traffic to his computer so that he can monitor his activities on the Internet. The local area network is fully switched and sets behind a NATing router and a firewall. Which of the following techniques would work best?
|
| 17. |
Which DNS record gives information about the zone, such as administrator contact, and so on?
|
| 18. |
Setting which IP option allows hackers the ability to specify the path an IP packet would take?
|
| 19. |
You have captured packets that you believe have had the source address changed to a private address. Which of the following is a private address?
|
| 20. |
Which layer of the OSI model is responsible for encryption?
|
Answers to Exam Questions
| A1: |
1. C. Each zone is a collection of structured resource records. Answer A is incorrect, as it is not a collection of domains; zones are a collection of resource records that can include an SOA record, A record, CNAME record, NS record, PTR record, and the MX record. Answer B is incorrect because it does not describe a zone namespace; that is the purpose of the SOA record. Answer D is incorrect, as a collection of aliases is a CNAME. |
| A2: |
2. B. Reconnaissance includes the act of reviewing an organization's website to gather as much information as possible. Answer A is incorrect because scanning and enumeration is not a passive activity. Answer C is incorrect because fingerprinting is performed to identify a systems OS. Answer D is incorrect, as gaining access is the equivalent of breaking and entering. |
| A3: |
3. D. Dumpster diving is the act of going through someone's trash. All other answers are incorrect because they do not describe dumpster diving. Reconnaissance is information gathering; intelligence gathering is another name for reconnaissance; and social engineering is the art of manipulating people. |
| A4: |
4. B. The format for an Ethernet II frame is target MAC address, source MAC address, and type field. The second six bytes equal FF FF FF FF FF FF, which indicates that they are from a broadcast address. Answer A is incorrect, as the information shown does not indicate an ARP packet. ARP packets can be identified by the hex value 08 06 in the type field. Answer C is incorrect because the destination is not set to a broadcast address. Answer D is incorrect, as the packet is not from a multicast address. |
| A5: |
5. C. TFTP was used by the Nimda worm to move the infected file to the victim's web server, admin.dll. Answer A is incorrect, as Nimda does not use Telnet. Answer B is incorrect, as Nimda did not use FTP. Answer D is incorrect because Nimda targeted IIS, not Apache. |
| A6: |
6. D. SNMP is UDP based and uses port two separate portsone of which is 161. It is vulnerable, as it can send the community strings in clear text. Answer A is incorrect because port 69 is TFTP. Answer B is incorrect, as SNMP is not TCP based. Answer C is incorrect, as TCP 69 is not used for SNMP. |
| A7: |
7. B. A teardrop attack is considered a type of overlapping fragment attack. It targets the IP header. Answer B is incorrect, as Smurf alters an ICMP ping packet. Answer C is incorrect, as the ping of death is also an ICMP attack. Answer D is incorrect because a LAND attack is not an overlapping fragment attack; it alters the port numbers. |
| A8: |
8. B. The second step of the three-step handshake sets the SYN ACK flags. Answer A is incorrect because the SYN flag is set on the first step. Answer C is incorrect, as the ACK flag occurs to acknowledge data. Answer D is incorrect, as the ACK PSH flags are not set on the second step of the handshake. |
| A9: |
9. D. RST is used to terminate a session that is abnormal or is non-responsive. Answer A is incorrect, as the default flag sequence to terminate is not RST FIN. Answer B is incorrect because FIN PSH is not used to terminate an abnormal session. Answer C is incorrect, as FIN is used to shut down a normal session. |
| A10: |
10. A. Deny all means that by default all ports and services are turned off; then only when a service or application is needed to accomplish a legitimate function of the organization is the service turned on. Answer B is incorrect, as the principle of least privilege means that you give employees only the minimum services needed to perform a task. Answer C is incorrect because an access control list is used for stateless inspection and can be used to block or allow approved services. Answer D is incorrect because defense in depth is the design of one security mechanism layered on top of another. |
| A11: |
11. D. The last fragmented packet will have the more bit set to 0 to indicate that no further packets will follow. Answer A is incorrect as it must be the last packet in the series if the more bit is set to 0. Answer B is incorrect as the more bit indicates that it must be the last packet. Answer C is incorrect as it cannot be the first packet with the more bit set to 0. |
| A12: |
12. C. ICMP type 11 is the correct code for time exceeded. All other answers are incorrect, as type 3 is for destination unreachable, type 5 is for redirects, and type 13 is for timestamp requests. |
| A13: |
13. B. ARP poisoning occurs at the Data Link layer. Answer A is incorrect because the Network layer is associated with IP addresses. Answer C is incorrect, as the Session layer is in charge of session management. Answer D is incorrect because the Transport layer is associated with TCP and UDP. |
| A14: |
14. B. DNS cache poisoning is a technique that tricks your DNS server into believing it has received authentic information when in reality, it has been deceived. Answer A is incorrect, as a DoS attack's primary goal is to disrupt service. Answer C is incorrect because DNS pharming is used to redirect users to an incorrect DNS server. Answer D is incorrect, as an illegal zone transfer is an attempt to steal the zone records, not poison them. |
| A15: |
15. D. The Transport layer is the correct answer. TCP can be the target for SYN attacks, which are a form of DoS. Answer A is incorrect because the Network layer is not associated with TCP. Answer B is incorrect, as the Data Link layer is responsible for frames. Answer C is incorrect, as the Physical layer is the physical media on which the bits or bytes are transported. |
| A16: |
16. A. ARP spoofing is used to redirect traffic on a switched network. Answer B is incorrect because setting this MAC address to be the same as the coworker would not be effective. Answer C is incorrect, as DNS spoofing would not help in this situation because DNS resolves FQDNs to Unknown IP addresses. Answer D is incorrect, as ARP poisoning requires a hacker to set his MAC address to be the same as the default gateway, not his IP address. |
| A17: |
17. D. The Start of Authority record gives information about the zone, such as the administrator contact. Answer A is incorrect, as CNAME is an alias. Answer B is incorrect, as MX records are associated with mail server addresses, and answer C is incorrect because an A record contains IP addresses and names of specific hosts. |
| A18: |
18. B. Source routing was designed to allow individuals the ability to specify the route that a packet should take through a network or to allow users to bypass network problems or congestion. Answer A is incorrect, as routing is the normal process of moving packets from node to node. Answer C is incorrect because RIP is a routing protocol. Answer D is incorrect because traceroute is the operation of sending trace packets to determine node information and to trace the route of UDP packets for the local host to a remote host. Normally, traceroute displays the time and location of the route taken to reach its destination computer. |
| A19: |
19. C. The Internet Assigned Numbers Authority (IANA) has reserved the following three blocks of the IP address space for private networks: Class A network IP address range = 10.0.0.010.255.255.255, Class B network IP address range = 172.31.0.0172.31.255.255, and Class C network IP address range = 192.168.255.0192.168.255.255. Check out RFC 1918 to learn more about private addressing. Answers A, B, and D are incorrect, as they do not fall within the ranges shown here. |
| A20: |
20. B. The presentation layer is responsible for encryption. Answer A is incorrect because the Application layer is responsible for program support. Programs are typically accessed by port number. Answer C is incorrect, as the Session layer handles such functions as the TCP startup and TCP shutdown. Answer D is incorrect, as the Transport layer is the home of TCP and UDP, which are connection and connectionless protocols. |
Suggested Reading and Resources
http://librenix.com/?inode=4569Understanding DNS attacks
www.stamey.nu/DNS/DNSTerms.aspUnderstanding DNS
www.novell.com/connectionmagazine/2000/03/hand30.pdfUnderstanding the TCP handshake
http://www.isecom.org/projects/osstmm.shtmlOSSTMM
www.openbsd.org/faq/pf/filter.html#tcpflagsTCP flags and packet filtering
www.techexams.net/technotes/securityplus/attacks-DDOS.shtmlHow teardrop and other DoS attacks work
http://netsecurity.about.com/cs/hackertools/a/aa121403.htmUsing a packet sniffer
www.tildefrugal.net/tech/arp.phpHow ARP works
www.stamey.nu/DNS/DNSHowItWorks.aspHow DNS works
www.chebucto.ns.ca/~rakerman/trojan-port-table.htmlDangerous ports used for Trojan and hacking software
www.insecure.org/nmap/hobbit.ftpbounce.txtFTP bounce attack
www.hackinthebox.org/modules.php?op=modload&name=News&file=article&sid=7944&mode=thread&order=0&thold=0Using MAC addresses to enumerate and hack computer systems
Footprinting and Scanning |
Part I: Exam Preparation
The Business Aspects of Penetration Testing
- The Business Aspects of Penetration Testing
- Study Strategies
- Security Fundamentals
- Security Testing
- Hacker and Cracker Descriptions
- Ethical Hackers
- Test PlansKeeping It Legal
- Ethics and Legality
- Summary
- Key Terms
- Apply Your Knowledge
The Technical Foundations of Hacking
- The Technical Foundations of Hacking
- Study Strategies
- The Attackers Process
- The Ethical Hackers Process
- Security and the Stack
- Summary
- Key Terms
- Apply Your Knowledge
Footprinting and Scanning
- Footprinting and Scanning
- Study Strategies
- Determining Assessment Scope
- The Seven-Step Information Gathering Process
- Summary
- Key Terms
- Apply Your Knowledge
Enumeration and System Hacking
- Enumeration and System Hacking
- Study Strategies
- The Architecture of Windows Computers
- Enumeration
- Windows Hacking
- Summary
- Key Terms
- Apply Your Knowledge
Linux and Automated Security Assessment Tools
- Linux and Automated Security Assessment Tools
- Study Strategies
- Linux
- Automated Assessment Tools
- Picking the Right Platform
- Summary
- Key Terms
- Apply Your Knowledge
Trojans and Backdoors
- Trojans and Backdoors
- Study Strategies
- An Overview of TrojansThe History of Trojans
- Covert Communications
- Trojan and Backdoor Countermeasures
- Summary
- Key Terms
- Apply Your Knowledge
Sniffers, Session Hijacking, and Denial of Service
- Sniffers, Session Hijacking, and Denial of Service
- Study Strategies
- Sniffers
- Session Hijacking
- Denial of Service
- Summary
- Key Terms
- Apply Your Knowledge
Web Server Hacking, Web Applications, and Database Attacks
- Web Server Hacking, Web Applications, and Database Attacks
- Study Strategies
- Web Server Hacking
- Web Application Hacking
- Database Overview
- Summary
- Key Terms
- Apply Your Knowledge
Wireless Technologies, Security, and Attacks
- Wireless Technologies, Security, and Attacks
- Study Strategies
- Wireless TechnologiesA Brief History
- Wireless LANs
- Wireless Hacking Tools
- Securing Wireless Networks
- Summary
- Key Terms
- Apply Your Knowledge
IDS, Firewalls, and Honeypots
- IDS, Firewalls, and Honeypots
- Study Strategies
- Intrusion Detection Systems
- Firewalls
- Honeypots
- Summary
- Key Terms
- Apply Your Knowledge
Buffer Overflows, Viruses, and Worms
- Buffer Overflows, Viruses, and Worms
- Study Strategies
- Buffer Overflows
- Viruses and Worms
- Summary
- Key Terms
- Apply Your Knowledge
Cryptographic Attacks and Defenses
- Cryptographic Attacks and Defenses
- Study Strategies
- Functions of Cryptography
- History of Cryptography
- Algorithms
- Hashing
- Digital Signatures
- Steganography
- Digital Certificates
- Public Key Infrastructure
- Protocols, Standards, and Applications
- Encryption Cracking and Tools
- Summary
- Key Terms
- Apply Your Knowledge
Physical Security and Social Engineering
- Physical Security and Social Engineering
- Study Strategies
- Physical Security
- Social Engineering
- Summary
- Key Terms
- Apply Your Knowledge
Part II: Final Review
- Fast Facts
- Ethics and Legality
- Footprinting
- Scanning
- Enumeration
- System Hacking
- Trojans and Backdoors
- Sniffers
- Denial of Service
- Social Engineering
- Session Hijacking
- Hacking Web Servers
- Web Application Vulnerabilities
- Web-Based Password Cracking Techniques
- SQL Injection
- Hacking Wireless Networks
- Virus and Worms
- Physical Security
- Linux Hacking
- Evading Firewalls, IDS, and Honeypots
- Buffer Overflows
- Cryptography
- Penetration Testing
- Certified Ethical Hacker
- Practice Exam Questions
- Answers to Practice Exam Questions
- Glossary
Part III: Appendixes
Appendix A. Using the ExamGear Special Edition Software
- Appendix A. Using the ExamGear Special Edition Software
- Exam Simulation
- Study Tools
- How ExamGear Special Edition Works
- Installing ExamGear Special Edition
- Using ExamGear Special Edition
- Contacting Que Certification
- License
- Software and Documentation
- License Term and Charges
- Title
- Updates
- Limited Warranty and Disclaimer
- Limitation of Liability
- Miscellaneous
- U.S. Government Restricted Rights
EAN: 2147483647
Pages: 247
 A. A collection of domains.
A. A collection of domains.