Wireless Hacking Tools
|
Objective:
|
There is no shortage of wireless tools for the attacker or the ethical hacker performing a security assessment or a pen test. Over time, tools come and go as technologies change and vulnerabilities are fixed. Therefore, it is important to understand what the tools do and where they fit in the methodology of a security assessment. Just listing all the available tools could easily fill a Chapter; therefore, some of the more well-known tools are discussed here:
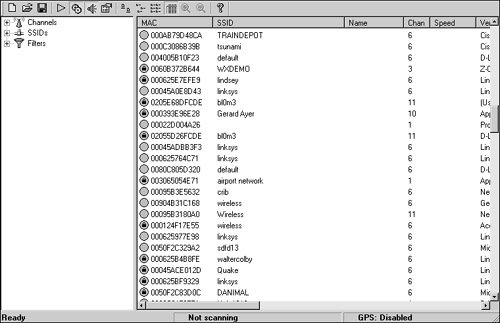
- NetStumbler This Windows-only tool is designed to locate and detect wireless LANs using 802.11b, 802.11a (XP only), and 802.11g WLAN standards. It is used for wardriving, verifying network configurations, detecting of rogue access points, and aiming directional antennas for long-haul WLAN links. A screenshot of NetStumbler can be seen in Figure 9.4. There's a trimmed down mini version designed for Windows CE called MiniStumbler.
Figure 9.4. NetStumbler.
- Mognet An open source Java-based wireless sniffer that was designed for handhelds but will run on other platforms as well. It performs real-time frame captures and can save and load frames in common formats, such as Ethereal, Libpcap, and TCPdump.
- WaveStumbler Another sniffing tool that was designed for Linux. It reports basic information about access points such as channel, SSID, and MAC.
- AiroPeek A Windows-based commercial wireless LAN analyzer designed to help security professionals deploy, secure, and troubleshoot wireless LANs. AiroPeek has the functionality to perform site surveys, security assessments, client troubleshooting, WLAN monitoring, remote WLAN analysis, and application layer protocol analysis.
- AirSnort A Linux-based WLAN WEP cracking tool that recovers encryption keys. AirSnort operates by passively monitoring transmissions and then computing the encryption key when the program captures enough packets.
- Kismet A useful Linux-based 802.11 wireless network detector, sniffer, and intrusion detection system. Kismet identifies networks by passively collecting packets and detecting standard named networks, detecting masked networks, and inferring the presence of nonbeaconing networks via data traffic.
- Void11 A wireless network penetration utility. It implements deauthentication DoS attacks against the 802.11 protocol. It can be used to speed up the WEP cracking process.
- THC-wardrive A Linux tool for mapping wireless access points works with a GPS.
- AirTraf A packet capture decode tool for 802.11b wireless networks. This Linux tool gathers and organizes packets and performs bandwidth calculation, as well as signal strength information on a per wireless node basis.
- Airsnarf Airsnarf is a simple rogue wireless access point setup utility designed to demonstrate how a rogue AP can steal usernames and passwords from public wireless hotspots. Airsnarf was developed and released to demonstrate an inherent vulnerability of public 802.11b hotspotssnarfing usernames and passwords by confusing users with DNS and HTTP redirects from a competing AP.
- Aircrack A set of tools for auditing wireless networks that includes airodump (a 802.11 packet capture program), aireplay (a 802.11 packet injection program), aircrack (a static WEP and WPA-PSK key cracker), and airdecap (a decryptor for WEP/WPA capture files). This is one of a new set of tools that can quickly crack WEP keys; it's much faster than older tools.
Review Break
Many types of tools are available for wireless networks. You need to know the names of the tools and their functions to successfully pass the CEH exam.
|
Name |
Platform |
Purpose |
|---|---|---|
|
NetStumbler |
Windows |
Wireless LAN detection |
|
Mognet |
Java |
Wireless sniffer |
|
WaveStumbler |
Linux |
Wireless LAN detection and sniffer |
|
Aeropeek |
Windows |
Sniffer and analyzer |
|
AirSnort |
Linux |
WEP cracking |
|
Kismet |
Linux |
Sniffer and wireless detector |
|
Void11 |
Linux |
Wireless DoS tool |
|
THC-Wardrive |
Linux |
Wireless WAP mapping tool |
|
AirTraf |
Linux |
Sniffer |
|
Airsnarf |
Linux |
Rogue access point |
|
Aircrack |
Linux |
WEP cracking tool kit |
Securing Wireless Networks |
Part I: Exam Preparation
The Business Aspects of Penetration Testing
- The Business Aspects of Penetration Testing
- Study Strategies
- Security Fundamentals
- Security Testing
- Hacker and Cracker Descriptions
- Ethical Hackers
- Test PlansKeeping It Legal
- Ethics and Legality
- Summary
- Key Terms
- Apply Your Knowledge
The Technical Foundations of Hacking
- The Technical Foundations of Hacking
- Study Strategies
- The Attackers Process
- The Ethical Hackers Process
- Security and the Stack
- Summary
- Key Terms
- Apply Your Knowledge
Footprinting and Scanning
- Footprinting and Scanning
- Study Strategies
- Determining Assessment Scope
- The Seven-Step Information Gathering Process
- Summary
- Key Terms
- Apply Your Knowledge
Enumeration and System Hacking
- Enumeration and System Hacking
- Study Strategies
- The Architecture of Windows Computers
- Enumeration
- Windows Hacking
- Summary
- Key Terms
- Apply Your Knowledge
Linux and Automated Security Assessment Tools
- Linux and Automated Security Assessment Tools
- Study Strategies
- Linux
- Automated Assessment Tools
- Picking the Right Platform
- Summary
- Key Terms
- Apply Your Knowledge
Trojans and Backdoors
- Trojans and Backdoors
- Study Strategies
- An Overview of TrojansThe History of Trojans
- Covert Communications
- Trojan and Backdoor Countermeasures
- Summary
- Key Terms
- Apply Your Knowledge
Sniffers, Session Hijacking, and Denial of Service
- Sniffers, Session Hijacking, and Denial of Service
- Study Strategies
- Sniffers
- Session Hijacking
- Denial of Service
- Summary
- Key Terms
- Apply Your Knowledge
Web Server Hacking, Web Applications, and Database Attacks
- Web Server Hacking, Web Applications, and Database Attacks
- Study Strategies
- Web Server Hacking
- Web Application Hacking
- Database Overview
- Summary
- Key Terms
- Apply Your Knowledge
Wireless Technologies, Security, and Attacks
- Wireless Technologies, Security, and Attacks
- Study Strategies
- Wireless TechnologiesA Brief History
- Wireless LANs
- Wireless Hacking Tools
- Securing Wireless Networks
- Summary
- Key Terms
- Apply Your Knowledge
IDS, Firewalls, and Honeypots
- IDS, Firewalls, and Honeypots
- Study Strategies
- Intrusion Detection Systems
- Firewalls
- Honeypots
- Summary
- Key Terms
- Apply Your Knowledge
Buffer Overflows, Viruses, and Worms
- Buffer Overflows, Viruses, and Worms
- Study Strategies
- Buffer Overflows
- Viruses and Worms
- Summary
- Key Terms
- Apply Your Knowledge
Cryptographic Attacks and Defenses
- Cryptographic Attacks and Defenses
- Study Strategies
- Functions of Cryptography
- History of Cryptography
- Algorithms
- Hashing
- Digital Signatures
- Steganography
- Digital Certificates
- Public Key Infrastructure
- Protocols, Standards, and Applications
- Encryption Cracking and Tools
- Summary
- Key Terms
- Apply Your Knowledge
Physical Security and Social Engineering
- Physical Security and Social Engineering
- Study Strategies
- Physical Security
- Social Engineering
- Summary
- Key Terms
- Apply Your Knowledge
Part II: Final Review
- Fast Facts
- Ethics and Legality
- Footprinting
- Scanning
- Enumeration
- System Hacking
- Trojans and Backdoors
- Sniffers
- Denial of Service
- Social Engineering
- Session Hijacking
- Hacking Web Servers
- Web Application Vulnerabilities
- Web-Based Password Cracking Techniques
- SQL Injection
- Hacking Wireless Networks
- Virus and Worms
- Physical Security
- Linux Hacking
- Evading Firewalls, IDS, and Honeypots
- Buffer Overflows
- Cryptography
- Penetration Testing
- Certified Ethical Hacker
- Practice Exam Questions
- Answers to Practice Exam Questions
- Glossary
Part III: Appendixes
Appendix A. Using the ExamGear Special Edition Software
- Appendix A. Using the ExamGear Special Edition Software
- Exam Simulation
- Study Tools
- How ExamGear Special Edition Works
- Installing ExamGear Special Edition
- Using ExamGear Special Edition
- Contacting Que Certification
- License
- Software and Documentation
- License Term and Charges
- Title
- Updates
- Limited Warranty and Disclaimer
- Limitation of Liability
- Miscellaneous
- U.S. Government Restricted Rights
EAN: 2147483647
Pages: 247
