Public Key Infrastructure
Public key infrastructure (PKI) is a framework that consists of hardware, software, and policies that exist to manage, create, store, and distribute keys and digital certificates. Although PKI is not needed for small groups, exchanging keys becomes difficult as the groups become bigger. To respond to this need, PKI was developed. The components of the PKI framework include the following:
- The Certificate Authority (CA) A function maintained by a person or group that is used to issue certificates to authorized users. The CA creates and signs the certificate. The CA is the one that guarantees the authenticity of the certificate.
- The Certificate Revocation List (CRL) The CA maintains the CRL list. The list is signed to verify its accuracy, and the list is used to report problems with certificates. When requesting a digital certificate, anyone can check the CRL to verify the certificates integrity. A compromised certificate or one that has been revoked before its expiration data will be reported through by the CRL
- The Registration Authority (RA) Reduces the load on the CA. The RA cannot generate a certificate, but it can accept requests, verify an owner's identity, and pass along the information to the CA for certificate generation.
- Certificate Server The certificate server maintains the database of stored certificates.
- X.509 Standard The accepted standard for digital certificates. An X.509 certificate includes the following elements:
Version
Serial Number
Algorithm ID
Issuer
Validity
- Not Before
- Not After
Subject
Subject Public Key Info
- Public Key Algorithm
- Subject Public Key
Issuer Unique Identifier (Optional)
Subject Unique Identifier (Optional)
Extensions (Optional)
Trust Models
Trust isn't a problem in small organizations, but when you need to communicate within large organizations, with external clients, and third parties, it's important to develop a working trust model. Organizations typically follow one of several well-known trust models. Three of the most common include
- Single-authority trust
- Hierarchical trust
- Web of trust
Single Authority
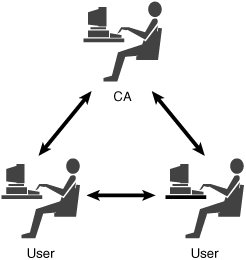
A single authority trust model uses a single third-party central agency. This agency provides the trust, the authority, and any keys issued by that authority. An example of this is shown in Figure 12.9.
Figure 12.9. Single trust model.
Hierarchical Trust
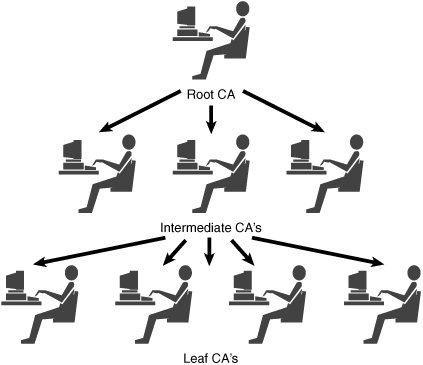
The hierarchical trust is actually a rather common model. It is based on the principle that people know one common entity in which they truly trust. This top layer of trust is known as the root CA. The root CA can issue certificates to intermediate CAs. Intermediate CAs issue certificates to leaf CAs. Leaf CAs issue certificates to users. An example of this is shown in Figure 12.10.
Figure 12.10. Hierarchical trust model.
Web of Trust
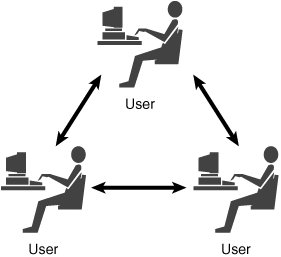
A web of trust consists of many supporters that sign each other's certificates. Users are validated on the knowledge of other users. PGP is an example of an application that uses the web of trust model. A vulnerability of the web of trust is that a malicious user can sign bad or bogus keys and endanger the entire group. An example of the web of trust can be seen in Figure 12.11.
Figure 12.11. Web of trust model.
Protocols, Standards, and Applications |
Part I: Exam Preparation
The Business Aspects of Penetration Testing
- The Business Aspects of Penetration Testing
- Study Strategies
- Security Fundamentals
- Security Testing
- Hacker and Cracker Descriptions
- Ethical Hackers
- Test PlansKeeping It Legal
- Ethics and Legality
- Summary
- Key Terms
- Apply Your Knowledge
The Technical Foundations of Hacking
- The Technical Foundations of Hacking
- Study Strategies
- The Attackers Process
- The Ethical Hackers Process
- Security and the Stack
- Summary
- Key Terms
- Apply Your Knowledge
Footprinting and Scanning
- Footprinting and Scanning
- Study Strategies
- Determining Assessment Scope
- The Seven-Step Information Gathering Process
- Summary
- Key Terms
- Apply Your Knowledge
Enumeration and System Hacking
- Enumeration and System Hacking
- Study Strategies
- The Architecture of Windows Computers
- Enumeration
- Windows Hacking
- Summary
- Key Terms
- Apply Your Knowledge
Linux and Automated Security Assessment Tools
- Linux and Automated Security Assessment Tools
- Study Strategies
- Linux
- Automated Assessment Tools
- Picking the Right Platform
- Summary
- Key Terms
- Apply Your Knowledge
Trojans and Backdoors
- Trojans and Backdoors
- Study Strategies
- An Overview of TrojansThe History of Trojans
- Covert Communications
- Trojan and Backdoor Countermeasures
- Summary
- Key Terms
- Apply Your Knowledge
Sniffers, Session Hijacking, and Denial of Service
- Sniffers, Session Hijacking, and Denial of Service
- Study Strategies
- Sniffers
- Session Hijacking
- Denial of Service
- Summary
- Key Terms
- Apply Your Knowledge
Web Server Hacking, Web Applications, and Database Attacks
- Web Server Hacking, Web Applications, and Database Attacks
- Study Strategies
- Web Server Hacking
- Web Application Hacking
- Database Overview
- Summary
- Key Terms
- Apply Your Knowledge
Wireless Technologies, Security, and Attacks
- Wireless Technologies, Security, and Attacks
- Study Strategies
- Wireless TechnologiesA Brief History
- Wireless LANs
- Wireless Hacking Tools
- Securing Wireless Networks
- Summary
- Key Terms
- Apply Your Knowledge
IDS, Firewalls, and Honeypots
- IDS, Firewalls, and Honeypots
- Study Strategies
- Intrusion Detection Systems
- Firewalls
- Honeypots
- Summary
- Key Terms
- Apply Your Knowledge
Buffer Overflows, Viruses, and Worms
- Buffer Overflows, Viruses, and Worms
- Study Strategies
- Buffer Overflows
- Viruses and Worms
- Summary
- Key Terms
- Apply Your Knowledge
Cryptographic Attacks and Defenses
- Cryptographic Attacks and Defenses
- Study Strategies
- Functions of Cryptography
- History of Cryptography
- Algorithms
- Hashing
- Digital Signatures
- Steganography
- Digital Certificates
- Public Key Infrastructure
- Protocols, Standards, and Applications
- Encryption Cracking and Tools
- Summary
- Key Terms
- Apply Your Knowledge
Physical Security and Social Engineering
- Physical Security and Social Engineering
- Study Strategies
- Physical Security
- Social Engineering
- Summary
- Key Terms
- Apply Your Knowledge
Part II: Final Review
- Fast Facts
- Ethics and Legality
- Footprinting
- Scanning
- Enumeration
- System Hacking
- Trojans and Backdoors
- Sniffers
- Denial of Service
- Social Engineering
- Session Hijacking
- Hacking Web Servers
- Web Application Vulnerabilities
- Web-Based Password Cracking Techniques
- SQL Injection
- Hacking Wireless Networks
- Virus and Worms
- Physical Security
- Linux Hacking
- Evading Firewalls, IDS, and Honeypots
- Buffer Overflows
- Cryptography
- Penetration Testing
- Certified Ethical Hacker
- Practice Exam Questions
- Answers to Practice Exam Questions
- Glossary
Part III: Appendixes
Appendix A. Using the ExamGear Special Edition Software
- Appendix A. Using the ExamGear Special Edition Software
- Exam Simulation
- Study Tools
- How ExamGear Special Edition Works
- Installing ExamGear Special Edition
- Using ExamGear Special Edition
- Contacting Que Certification
- License
- Software and Documentation
- License Term and Charges
- Title
- Updates
- Limited Warranty and Disclaimer
- Limitation of Liability
- Miscellaneous
- U.S. Government Restricted Rights
EAN: 2147483647
Pages: 247
- Chapter III Two Models of Online Patronage: Why Do Consumers Shop on the Internet?
- Chapter VII Objective and Perceived Complexity and Their Impacts on Internet Communication
- Chapter XIV Product Catalog and Shopping Cart Effective Design
- Chapter XV Customer Trust in Online Commerce
- Chapter XVIII Web Systems Design, Litigation, and Online Consumer Behavior
