Designing and Implementing L2TPv2 and L2TPv3 Remote Access VPNs
In Chapter 2, "Designing and Deploying L2TPv3-Based Layer 2 VPNs (L2VPN)," you saw how Layer Two Tunneling Protocol version 3 (L2TPv3) can be used to transport a number of Layer 2 protocols in a site-to-site configuration. This chapter shows how L2TPv2 (RFC2661) and L2TPv3 (RFC3931) can be used to provide home workers, telecommuters, or "road warriors" with access to a corporate or other organization network.
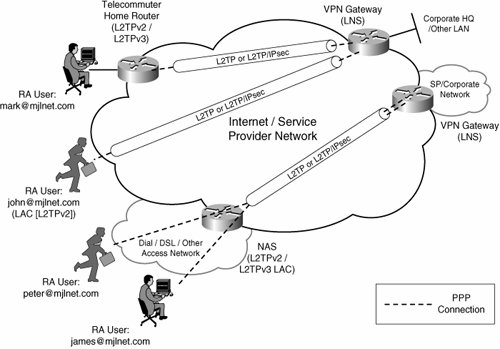
Figure 8-1 depicts L2TP remote access VPNs.
Figure 8-1. L2TP Remote Access VPNs
L2TP can be used to provide remote access in two different ways:
- Voluntary/client-initiated tunnel mode In this mode, PPP connections are tunneled over L2TP directly to a remote VPN gateway called an L2TP Network Server (LNS) from a remote access client or client router.
The key point to note is that the PPP connection and L2TP tunnel are terminated on the same device when using voluntary/client-initiated tunnel mode.
- Compulsory/NAS-initiated tunnel mode In this mode, remote users connect to a Network Access Server (NAS) called an L2TP Access Concentrator (LAC), and PPP frames (to and from the remote access users) are tunneled via L2TP to an LNS.
In this mode, the LAC does not terminate PPP connections (at least PPP connections that are transported over the L2TP tunnel).
In Figure 8-1, remote access users mark@mjlnet.com and john@mjlnet.com are taking advantage of L2TP voluntary/client-initiated tunnel mode to connect to a corporate VPN gateway (LNS).
mark@mjlnet.com is a telecommuter, and uses a small home router to tunnel traffic to and from a VPN gateway. john@mjlnet.com, on the other hand, is a "road warrior" who uses the built-in L2TP/IPsec (L2TP protected by IPsec) client software on his laptop to connect over an Internet connection to the VPN gateway.
peter@mjlnet.com and james@mjlnet.com, on the other hand, do not directly use L2TP to connect to a VPN gateway. Instead, they connect via PPP (over dialup, DSL, or other access technologies) to a service provider LAC, which then tunnels both PPP connections over the same compulsory/NAS-initiated L2TP tunnel to a VPN gateway.
In Figure 8-1, telecommuter home router (mark@mjlnet.com) and john@mjlnet.com are labeled 'L2TPv2/L2TPv3' and 'LAC [L2TPv2]' respectively. You may be wondering why two different versions of L2TP are used depending on whether a remote access user is mobile (a 'road-warrior') or a telecommuter. This is because, to date, all implementation of L2TP included with host operating systems (Windows/Mac OS X) utilize L2TPv2, while Cisco routers (used in Figure 8-1 for telecommuter remote access) support both L2TPv2 and L2TPv3.
This chapter concentrates on L2TPv2 because of its much wider deployment as a remote access VPN protocol.
Part I: Understanding VPN Technology
What Is a Virtual Private Network?
- What Is a Virtual Private Network?
- VPN Devices
- Deploying Site-to-Site and Remote Access VPNs: A Comparison
- Summary
- Review Questions
Part II: Site-to-Site VPNs
Designing and Deploying L2TPv3-Based Layer 2 VPNs
- Designing and Deploying L2TPv3-Based Layer 2 VPNs
- Benefits and Drawbacks of L2TPv3-Based L2VPNs
- L2TPv3 Pseudowire Operation
- Configuring and Verifying L2TPv3 Pseudowires
- Summary
- Review Questions
Designing and Implementing AToM-Based Layer 2 VPNs
- Designing and Implementing AToM-Based Layer 2 VPNs
- Benefits and Drawbacks of AToM-Based L2VPNs
- AToM Pseudowire Operation
- Deploying AToM Pseudowires
- Implementing Advanced AToM Features
- Summary
- Review Questions
Designing MPLS Layer 3 Site-to-Site VPNs
- Designing MPLS Layer 3 Site-to-Site VPNs
- Advantages and Disadvantages of MPLS Layer 3 VPNs
- MPLS Layer 3 VPNs Overview
- A Detailed Examination of MPLS Layer 3 VPNs
- Deploying MPLS Layer 3 VPNs
- Summary
- Review Questions
Advanced MPLS Layer 3 VPN Deployment Considerations
- Advanced MPLS Layer 3 VPN Deployment Considerations
- The Carriers Carrier Architecture
- The Inter-Autonomous System/Interprovider MPLS VPN Architecture
- Supporting Multicast Transport in MPLS Layer 3 VPNs
- Implementing QoS for MPLS Layer 3 VPNs
- Supporting IPv6 Traffic Transport in MPLS Layer 3 VPNs Using 6VPE
- Summary
- Review Questions
Deploying Site-to-Site IPsec VPNs
- Deploying Site-to-Site IPsec VPNs
- Advantages and Disadvantages of IPsec Site-to-Site VPNs
- IPsec: A Security Architecture for IP
- Deploying IPsec VPNs: Fundamental Considerations
- Summary
- Review Questions
Scaling and Optimizing IPsec VPNs
- Scaling and Optimizing IPsec VPNs
- Scaling IPsec Virtual Private Networks
- Ensuring High Availability in an IPsec VPN
- Designing QoS for IPsec VPNs
- MTU and Fragmentation Considerations in an IPsec VPN
- Summary
- Review Questions
Part III: Remote Access VPNs
Designing and Implementing L2TPv2 and L2TPv3 Remote Access VPNs
- Designing and Implementing L2TPv2 and L2TPv3 Remote Access VPNs
- Benefits and Drawbacks of L2TP Remote Access VPNs
- Operation of L2TP Voluntary/Client-Initiated Tunnel Mode
- Implementing L2TP Voluntary/Client-Initiated Tunnel Mode Remote Access VPNs
- Designing and Implementing L2TP Compulsory/NAS-Initiated Tunnel Mode Remote Access VPNs
- Integrating L2TP Remote Access VPNs with MPLS VPNs
- Summary
- Review Questions
Designing and Deploying IPsec Remote Access and Teleworker VPNs
- Designing and Deploying IPsec Remote Access and Teleworker VPNs
- Comparing IPsec Remote Access VPNs with Other Types of Remote Access VPNs
- Understanding IKE in an IPsec Remote Access VPN Environment
- Deploying IPsec Remote Access VPNs Using Preshared Key and Digital Signature Authentication
- Summary
- Review Questions
Designing and Building SSL Remote Access VPNs (WebVPN)
- Designing and Building SSL Remote Access VPNs (WebVPN)
- Comparing SSL VPNs to Other Types of Remote Access VPNs
- Understanding the Operation of SSL Remote Access VPNs
- Using Clientless SSL Remote Access VPNs (WebVPN) on the Cisco VPN 3000 Concentrator
- Implementing Full Network Access Using the Cisco SSL VPN Client
- Strengthening SSL Remote Access VPNs Security by Implementing Cisco Secure Desktop
- Enabling SSL VPNs (WebVPN) on Cisco IOS Devices
- Deploying SSL VPNs (WebVPN) on the ASA 5500
- Summary
- Review Questions
Part IV: Appendixes
Designing and Building SSL Remote Access VPNs (WebVPN)
- Designing and Building SSL Remote Access VPNs (WebVPN)
- Appendix A. VPLS and IPLS Layer 2 VPNs
- Understanding VPLS
- Understanding IPLS
- Summary: Comparing VPLS and IPLS
Appendix B. Answers to Review Questions
EAN: 2147483647
Pages: 124
- Chapter II Information Search on the Internet: A Causal Model
- Chapter V Consumer Complaint Behavior in the Online Environment
- Chapter VII Objective and Perceived Complexity and Their Impacts on Internet Communication
- Chapter XIV Product Catalog and Shopping Cart Effective Design
- Chapter XVII Internet Markets and E-Loyalty
