Cryptography
Overview
The information system professional should have a fundamental comprehension of the following areas in cryptography:
- Definitions
- Background
- Cryptology fundamentals
- Symmetric-key cryptosystem fundamentals
- Asymmetric-key cryptosystem fundamentals
- Key distribution and management issues
- Public-key infrastructure (PKI) definitions and concepts
This chapter will address each of these areas to the level required of a practicing information system security professional.
Introduction
The purpose of cryptography is to protect transmitted information from being read and understood by anyone except the intended recipient. Ideally, unauthorized individuals would never be able to read an enciphered message. In practice, reading an enciphered communication can be a function of time; however, the effort and corresponding time that is required for an unauthorized individual to decipher an encrypted message may be so large that it can be impractical. By the time the message is decrypted, the information within the message may be of minimal value.
Cryptography can be used to implement confidentiality, integrity, authentication, and nonrepudiation.
As a basis for exploring the fundamentals of cryptography, common definitions of cryptographic terms are necessary. These definitions are presented in the following section.
Definitions
Block Cipher. Obtained by segregating plaintext into blocks of n characters or bits and applying the identical encryption algorithm and key, K, to each block. For example, if a plaintext message, M, is divided into blocks M1, M2, unicode Mp, then:
E(M, K) = E(M1, K) E(M2, K) E(Mp, K)
where the blocks on the right-hand side of the equation are concatenated to form the ciphertext.
Cipher. A cryptographic transformation that operates on characters or bits.
Ciphertext or Cryptogram. An unintelligible message.
Clustering. A situation in which a plaintext message generates identical ciphertext messages by using the same transformation algorithm but with different cryptovariables or keys.
Code. A cryptographic transformation that operates at the level of words or phrases.
Cryptanalysis. The act of obtaining the plaintext or key from the ciphertext, used to obtain the valuable information contained in the plaintext or to use the key to deceive the original intended recipient with altered or fake messages; breaking the ciphertext.
Cryptographic Algorithm. A step-by-step procedure used to encipher plaintext and decipher ciphertext.
Cryptography. The art and science of hiding the meaning of a communication from unintended recipients. The word cryptography comes from the Greek words kryptos (hidden) and graphein (to write).
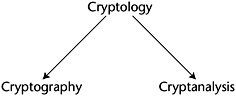
Cryptology. The body of knowledge concerning codes and ciphers, encompassing cryptography and cryptanalysis.
Cryptosystem. A set of transformations from a message space to a ciphertext space. For example, if M = Plaintext, C = Ciphertext, E = the encryption transformation, and D = the decryption transformation,
E(M) = C D[E(M)] = M
To specifically show the dependence of the encipherment and decipherment transformation on the cryptovariable or key, K,
E(M, K) = C D(C, K) = D[E(M, K), K] = M
Decipher. To undo the encipherment process and make the message readable.
Encipher. To make the message unintelligible to all but the intended recipients.
End-to-End Encryption. Sending of information that remains encrypted from its point of origin to its final destination. In symmetric-key encryption, this process requires the sender and receiver to have identical keys for the session.
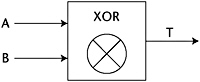
Exclusive Or. A Boolean operation that essentially performs binary addition without carrying on the input bits, as shown in Table 4-1. For two binary input variables, A and B, the Exclusive Or function produces a binary 1 output when A and B are not equal and a binary 0 when A and B are equal. The symbol ⊗ or the acronym XOR indicates the Exclusive Or operation.
|
INPUTS |
OUTPUT |
|
|---|---|---|
|
A |
B |
T |
|
0 |
0 |
0 |
|
0 |
1 |
1 |
|
1 |
0 |
1 |
|
1 |
1 |
0 |
The Exclusive Or function is easily implemented in hardware and therefore can be executed at hardware speeds. A valuable property of the Exclusive Or function is that the inverse of the function can be obtained by performing another Exclusive Or on the output. For example, assume that a transformation is performed on a stream cipher by applying the Exclusive Or operation, bit by bit, on the plaintext bits with the bits of a keystream. Then, the decipherment of the enciphered stream is accomplished by applying the Exclusive Or of the keystream, bit by bit, to the enciphered stream. This property is illustrated in Figure 4-1.
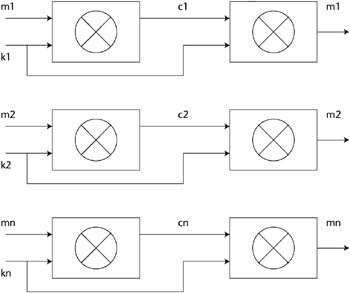
Figure 4-1: Exclusive Or (XOR) on its own output recovers the original input.
If the bits of the message stream M are m1, m2, , mn, the bits of the keystream K are k1, k2, , kn, and the bits of the cipherstream C are c1, c2, , cn, then
E(M,K) = M XOR K = C, and D(C) = D[M XOR K] = [M XOR K] XOR K
Schematically, the process is illustrated in Figure 4-2.
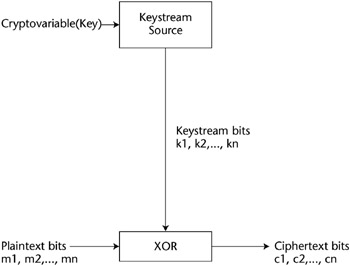
Figure 4-2: Encipherment process using Keystream with an XOR operation.
Key or Cryptovariable. Information or a sequence that controls the enciphering and deciphering of messages.
Link Encryption. Each entity has keys in common with its two neighboring nodes in the transmission chain. Thus, a node receives the encrypted message from its predecessor (the neighboring node), decrypts it, and then re-encrypts it with another key that is common to the successor node. Then, the encrypted message is sent on to the successor node, where the process is repeated until the final destination is reached. Obviously, this mode does not provide protection if the nodes along the transmission path can be compromised. A general representation of link encryption is shown in Figure 4-3.
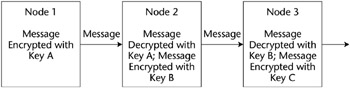
Figure 4-3: Link encryption.
One-Time Pad. Assuming an encryption key, K, with components k1, k2, , kn, the encipherment operation is performed by using each component ki of the key, K, to encipher exactly one character of the plaintext. Therefore, the key has the same length as the message. Also, the key is used only once and is never used again. Ideally, the key’s components are truly random and have no periodicity or predictability, thus making the ciphertext unbreakable. The one-time pad is usually implemented as a stream cipher by using the XOR function. The elements k1, k2, , kn of the key stream are independent and are uniformly distributed, random variables. This requirement of a single, independently chosen value of ki to encipher each plaintext character is stringent and may not be practical for most commercial IT applications. The one-time pad was invented in 1917 by Major Joseph Mauborgne of the United States Army Signal Corps and Gilbert Vernam of AT&T.
Plaintext. A message in cleartext readable form.
Steganography. Secret communication in which the existence of the message is hidden. For example, in a digital image the least-significant bit of each word can be used to encode a message without causing any significant change in the image.
Work Function (Factor). The difficulty in recovering the plaintext from the ciphertext as measured by cost and/or time. A system’s security is directly proportional to the value of the work function. The work function needs only to be large enough to suffice for the intended application. If the message to be protected loses its value after a short time period, the work function needs only to be large enough to ensure that the decryption would be highly infeasible in that period of time.
Background
Secret writing can be traced back to the Egyptians. About 1900 B.C., over a thousand years after they had invented their writing system that we call hieroglyphics, from the Greek words hieros (sacred) and gluphein (to carve), a scribe employed the signs of the hieroglyphic script in a nonstandard way to conceal the content of an inscription from unintended readers. Around 400 B.C., military cryptography was employed by the Spartans in the form of a strip of papyrus or parchment wrapped around a wooden rod. This system is called a Scytale and is shown in Figure 4-4.
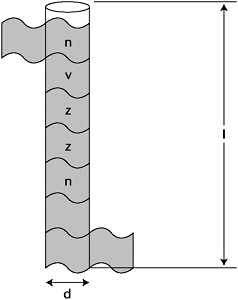
Figure 4-4: A Spartan scytale.
The message to be encoded was written lengthwise down (or up) the rod on the wrapped material. Then the material was unwrapped and carried to the recipient. In its unwrapped form, the writing appeared to be random characters. When the material was rewound on a rod of the same diameter, d, and minimum length, l, the message could be read. Thus, as shown in Figure 4-4, the keys to deciphering the message are d and l.
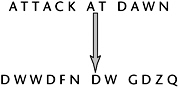
Around 50 B.C., Julius Caesar, the emperor of Rome, used a substitution cipher to transmit messages to Marcus Tullius Cicero. In this cipher, letters of the alphabet are substituted for other letters of the same alphabet. Because only one alphabet was used, this cipher was a monoalphabetic substitution. This particular cipher involved shifting the alphabet by three letters and substituting those letters. This substitution, sometimes known as C3 (for Caesar shifting three places), is shown in Figure 4-5.
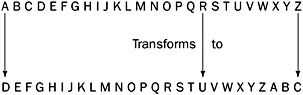
Figure 4-5: Caesar C3 substitution cipher.
In general, the Caesar system of ciphers can be written as follows:
Zi = Cn (Pi),
where the Zi are ciphertext characters, Cn is a monoalphabetic substitution transformation, n is the number of letters shifted, and the Pi are plaintext characters. Thus, the message ATTACK AT DAWN would be enciphered by using C3 as follows:
Disks have played an important part in cryptography for the past 500 years. In Italy around 1460, Leon Battista Alberti developed cipher disks for encryption (Figure 4-6). His system consisted of two concentric disks. Each disk had an alphabet around its periphery, and by rotating one disk with respect to the other, a letter in one alphabet could be transformed to a letter in another alphabet.
Figure 4-6: Cipher disks.
Cryptographic Technologies
The two principal types of cryptographic technologies are symmetric-key (secret-key or private-key) cryptography and asymmetric-key (public-key) cryptography. In symmetric-key cryptography, both the receiver and sender share a common secret key. In asymmetric-key cryptography, the sender and receiver respectively use a public and a private key, sharing only the public key. The public and private keys are related mathematically, and in an ideal case, they have the characteristic that an individual who has the public key cannot derive the private key.
Because of the amount of computation involved in public-key cryptography, private-key cryptography is on the order of 1,000 times faster than public-key cryptography.
Classical Ciphers
In this section, the basic encipherment operations are discussed in detail in order to provide a basis for understanding the evolution of encryption methods and the corresponding cryptanalysis efforts.
Substitution
The Caesar cipher, as we discussed earlier in this chapter, is a simple substitution cipher that involves shifting the alphabet three positions to the right. The Caesar cipher is a subset of the Vigenère polyalphabetic cipher. In the Caesar cipher, the message’s characters and repetitions of the key are added together, modulo 26, giving the letters A to Z of the alphabet values of 0 to 25, respectively. Two parameters have to be specified for the key:
- D, the number of repeating letters representing the key
- K, the key
In the following example, D = 3 and K = BAD:
The message is: ATTACK AT DAWN
Assigning numerical values to the message yields
0 19 19 0 2 10 0 19 3 0 22 13 A T T A C K A T D A W N
The numerical values of K are
1 0 3 B A D
Now, the repetitive key of 103 is added to the letters of the message as follows:
1 0 3 1 0 3 1 0 3 1 0 3 Repeating Key 0 19 19 0 2 10 0 19 3 0 22 13 Message ______________________________________________________ 1 19 22 1 2 13 1 19 6 1 22 16 Ciphertext Numerical Equivalents B T W B C N B T G B W Q Ciphertext
Converting the numbers back to their corresponding letters of the alphabet produces the ciphertext as shown.
For the special case of the Caesar cipher, D is 1 and the key is D(2). Taking the same message as an example, using the Caesar cipher yields the following:
2 2 2 2 2 2 2 2 2 2 2 2 Repeating Key 0 19 19 0 2 10 0 19 3 0 22 13 Message ______________________________________________________ 2 21 21 2 4 12 2 21 5 2 24 15 Ciphertext Numerical Equivalents C V V C E M C V F C Y P Ciphertext
Converting the numbers back to their corresponding letters of the alphabet produces the ciphertext, which is the letters of the original message text shifted three positions to the right.
If the sum of any of the additions yields a result greater than or equal to 26, the additions would be modulo 26, in which the final result is the remainder over 26. The following examples illustrate modulo 26 addition:
14 12 22 24 12 22 8 5 _________________________________________________________ 26 32 30 29 Apparent Sum 0 6 4 3 Result of modulo 26 addition
These ciphers can be described by the general equation
C = (M + b)mod N
where:
- b is a fixed integer
- N is the size of the alphabet
- M is the plaintext message in numerical form
- C is the ciphertext in numerical form
This representation is a special case of an affine cryptosystem, which is described in the following equation:
C = (aM + b)mod N
where a and b constitute the key.
Recall that the following transformation is implemented by the Caesar cipher:
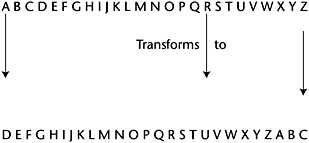
This type of cipher can be attacked by using frequency analysis. In frequency analysis, the frequency characteristics shown in the use of the alphabet’s letters in a particular language are used. This type of cryptanalysis is possible because the Caesar cipher is a monoalphabetic or simple substitution cipher, where a character of ciphertext is substituted for each character of the plaintext.
A polyalphabetic cipher is accomplished through the use of multiple substitution ciphers. Thus, the same plaintext letter is converted into a different ciphertext letter during the encryption process. For example, using the alphabets shown in Figure 4-7, a Caesar cipher with D = 3, and K = BAD (103), the plaintext EGGA is enciphered into YGZR. Note that the letter G is encrypted into the letter Z for one encryption and into the letter G for a second encryption. Blaise de Vigenère, a French diplomat born in 1523, consolidated the cryptographic works of Alberti, Trithemius, and Porta to develop the polyalphabetic cipher, a very strong cipher at that time. Vigenère’s cipher used 26 alphabets.
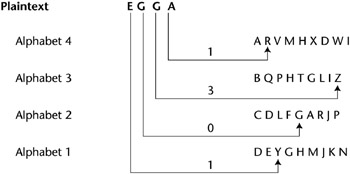
Figure 4-7: Polyalphabetic substitution.
Because multiple alphabets are used, this approach counters frequency analysis. It can, however, be attacked by discovery of the periods - when the substitution repeats.
Transposition (Permutation)
Another type of cipher is the transposition cipher. In this cipher, the letters of the plaintext are permuted.
For example, the letters of the plaintext A T T A C K A T D A W N could be permuted to D C K A A W N A T A T T.
A columnar transposition cipher is one where the plaintext is written horizontally across the paper and is read vertically, as shown in Figure 4-8.
|
N O W I S T H E |
|
T I M E F O R A |
|
L L G O O D M E |
|
N T O C O M E T |
|
O T H E A I D O |
|
F T H E I R P A |
|
R T Y |
Figure 4-8: A columnar transposition cipher.
Reading the ciphertext vertically yields: NTLNOFROILTTTTWMGOHHY
The transposition cipher can be attacked through frequency analysis, but it hides the statistical properties of letter pairs and triples, such as IS and TOO.
Vernam Cipher (One Time Pad)
The one-time pad or Vernam cipher is implemented through a key that consists of a random set of nonrepeating characters. Each key letter is added modulo 26 to a letter of the plaintext. In the one-time pad, each key is used one time for only one message and is never used again. The length of the key character stream is equal to the length of the message. For megabyte and gigabyte messages, the one-time pad is not practical, but it is approximated by shorter random sets of characters with very long periods.
An example of a one-time pad encryption is as follows:
Plaintext HOWAREYOU 7 14 22 0 17 4 24 14 20 One-time pad key XRAQZTBCN 23 17 0 16 25 19 1 2 13 Apparent sum 30 31 22 16 42 23 25 16 33 Sum Mod 26 4 5 22 16 16 23 25 16 7 Ciphertext E F W Q Q X Z Q H
The Vernam machine (shown in Figure 4-9) was developed at AT&T, and the original system performed an XOR of the message bits in a Baudot code with the key bits.
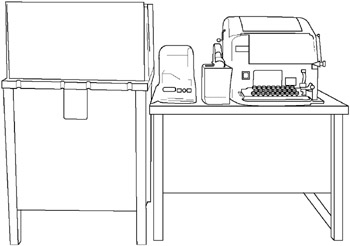
Figure 4-9: A Vernam machine.
Book or Running Key Cipher
This cipher uses text from a source (say, a book) to encrypt the plaintext. The key, known to the sender and the intended receiver, might be the page and line number of text in the book. This text is matched character for character with the plaintext, and modulo 26 addition is performed to effect the encryption.
The running-key cipher eliminates periodicity, but it is attacked by exploiting the redundancy in the key.
Codes
Codes deal with words and phrases and relate these words as phrases to corresponding groups of numbers or letters. For example, the numbers 526 might mean: “Attack at dawn.”
Steganography
Steganography is the art of hiding the existence of a message. The word steganography comes from the Greek words steganos, meaning “covered,” and graphein, meaning “to write.” An example is the microdot, which compresses a message into the size of a period or dot. Steganography can be used to make a digital “watermark” to detect the illegal copying of digital images.
Secret Key Cryptography (Symmetric Key)
Secret-key cryptography is the type of encryption that is familiar to most people. In this type of cryptography, the sender and receiver both know a secret key. The sender encrypts the plaintext message with the secret key, and the receiver decrypts the message with the same secret key. Obviously, the challenge is to make the secret key available to both the sender and receiver without compromising it. For increased security, the secret key should be changed at frequent intervals. Ideally, a particular secret key should only be used once.
Figure 4-10 illustrates a secret (symmetric)-key cryptographic system.
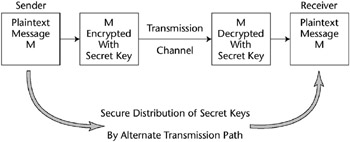
Figure 4-10: A symmetric (secret)-key cryptosystem.
A secret-key cryptographic system comprises information that is public and private. The public information usually consists of the following:
- The algorithm for enciphering the plaintext copy of the enciphered message
- Possibly, a copy of the plaintext and an associated ciphertext
- Possibly, an encipherment of the plaintext that was chosen by an unintended receiver
Private information is:
- The key or cryptovariable
- One particular cryptographic transformation out of many possible transformations
An important property of any secret-key cryptographic system is that the same key can encipher and decipher the message. If large key sizes (>128 bits) are used, secret-key systems are very difficult to break. These systems are also relatively fast and are used to encrypt large volumes of data. There are many symmetric-key algorithms available because of this feature. One problem with using a symmetric-key system is that because the sender and receiver must share the same secret key, the sender requires a different key for each intended receiver. Thus, for n individuals, n(n – 1)/2 keys are required for each person to communicate in secret with any one of the other participants. One commonly used approach is to use public-key cryptography to transmit a symmetric session key that can be used for a session between the sender and receiver. Time stamps can be associated with this session key so that it is valid only for a specified period of time. Time stamping is a counter to a replay attack, in which a session key is somehow intercepted and used at a later time. Symmetric-key systems, however, do not provide mechanisms for authentication and nonrepudiation. The best-known symmetric-key system is probably the Data Encryption Standard (DES). DES evolved from the IBM Lucifer cryptographic system in the early 1970s for commercial use.
Data Encryption Standard (DES)
DES is a symmetric-key cryptosystem that was devised in 1972 as a derivation of the Lucifer algorithm developed and patented[*] by Horst Feistel at IBM. DES is used for commercial and nonclassified purposes. DES describes the Data Encryption Algorithm (DEA) and is the name of the Federal Information Processing Standard (FIPS) 46-1 that was adopted in 1977.[†] DEA is also defined as the ANSI Standard X3.92.[‡] The National Institute of Standards and Technology (NIST) recertified DES in 1993. DES was not recertified after that and has been replaced by the Advanced Encryption Standard (AES).
DEA uses a 64-bit block size and a 56-bit key. It begins with a 64-bit key and strips off eight parity bits. DEA is a 16-round cryptosystem and was originally designed for implementation in hardware. With a 56-bit key, one would have to try 256 or 70 quadrillion possible keys in a brute force attack. Although this number is huge, large numbers of computers cooperating over the Internet could try all possible key combinations. Because of this vulnerability, the U.S. government has not used DES since November 1998. Triple DES - three encryptions using the DEA - replaced DES and were used until the AES was adopted.
As previously stated, DES uses 16 rounds of transposition and substitution. It implements the techniques that were suggested by Claude Shannon, the father of information theory. Shannon proposed two techniques, confusion and diffusion, for improving the encryption of plaintext. Confusion conceals the statistical connection between ciphertext and plaintext. It is accomplished in DES through a substitution by means of nonlinear substitution S-boxes. An S-box is nonlinear because it generates a 4-bit output string from a 6-bit input string.
The purpose of diffusion is to spread the influence of a plaintext character over many ciphertext characters. Diffusion can be implemented by means of a product cipher. In a product cipher, a cryptosystem (E1) is applied to a message (M) to yield ciphertext (C1). Then, another cryptosystem (E2) is applied to ciphertext (C1) to yield ciphertext (C2). Symbolically, this product is generated by E1(M) = C1; E2(C1) = C2. DES implements this product 16 times. Diffusion is performed in DES by permutations in P-boxes.
DES operates in four modes:
- Cipher Block Chaining (CBC)
- Electronic Code Book (ECB)
- Cipher Feedback (CFB)
- Output Feedback (OFB)
Cipher Block Chaining
Cipher Block Chaining (CBC) operates with plaintext blocks of 64 bits. A randomly generated 64-bit initialization vector is XORed with the first block of plaintext used to disguise the first part of the message that might be predictable (such as Dear Sir). The result is encrypted by using the DES key. The first ciphertext will then XOR with the next 64-bit plaintext block. This encryption continues until the plaintext is exhausted. Note that in this mode, errors propagate.
A schematic diagram of CBC is shown in Figure 4-11.
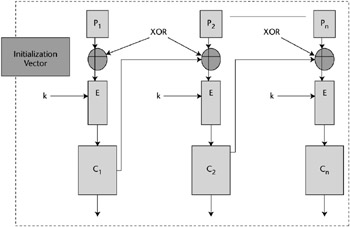
Figure 4-11: Cipher Block Chaining (CBC).
Electronic Code Book (ECB)
Electronic Code Book (ECB) is the “native” mode of DES and is a block cipher. ECB is best suited for use with small amounts of data. It is usually applied to encrypt initialization vectors or encrypting keys. ECB is applied to 64-bit blocks of plaintext, and it produces corresponding 64-bit blocks of ciphertext. ECB operates by dividing the 64-bit input vector into two 32-bit blocks, called a Right Block and a Left Block. The bits are then recopied to produce two 48-bit blocks. Then, each of these 48-bit blocks is XORed with a 48-bit encryption key. The term “code book” is derived from the notion of a codebook in manual encryption, which has pairs of plaintext words or phrases and their corresponding codes. For example, the word “RETREAT” in the codebook may correspond to a code 5374.
Cipher Feedback (CFB)
The Cipher Feedback (CFB) mode of DES is a stream cipher in which the ciphertext is used as feedback into the key generation source to develop the next key stream. The ciphertext generated by performing an XOR of the plaintext with the key stream has the same number of bits as the plaintext. In this mode, errors will propagate. A diagram of the CFB is shown in Figure 4-12.
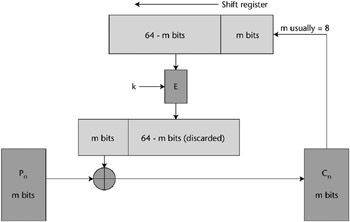
Figure 4-12: DES Cipher Feedback operation.
Output Feedback
The DES Output Feedback (OFB) mode is also a stream cipher that generates the ciphertext key by XORing the plaintext with a key stream. In this mode, errors will not propagate. Feedback is used to generate the key stream; therefore, the key stream varies. An initialization vector is required in OFB. OFB is depicted in Figure 4-13.
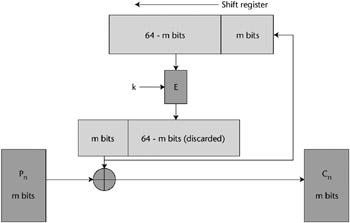
Figure 4-13: DES Output Feedback operation.
DES Security
As a result of the Increase in computing power that is capable of being incorporated onto very-large-scale integration (VLSI) chips and the corresponding decrease in cost, DES has been broken. The following list summarizes the major DES cracking efforts:
- In 1997, DES was cracked in 90 days by a distributed software effort performing a brute force search of the DES key space (256 or 72 quadrillion keys). The search was run on approximately 14,000 computers per day, searching at an average rate of 232 keys per second.
- In 1998, DES was cracked in 39 days by a distributed software effort performing a brute force search of the DES key space (256 or 72 quadrillion keys). The search was done at an average rate of 234 keys per second.
- In 1998, the Electronic Frontier Foundation (EFF) built a hardware DES cracker for approximately $250,000 that could test 90 billion keys per second. The cracker machine conducted a brute force search of DES key space. The device comprises 1,856 custom DES-cracker chips built with 29 circuit boards holding 64 chips each. The project required 18 months to complete, and the effort used approximately 10 people working part-time.
- In July of 1998, the EFF DES machine found the DES key in 56.05 hours at a search rate of 236 keys per second.
- In January of 1999, the EFF DES machine combined with a distributed, worldwide network of approximately 100,000 computers on the Internet to find the DES key in 22.25 hours at an average search rate of 237 keys per second.
- In 2001, a Field Programmable Gate Array (FPGA) design running at 33.33 MHz performed a brute force DES key search at a rate of 225 keys per second. With this hardware, depending on where in the key space the key was located, the DES key could be found anywhere from 25 hours to 10 days.
Because DES was shown to be too vulnerable to such attacks, DES was replaced by Triple DES, and then by the Advanced Encryption Standard (AES).
Triple DES
It has been shown that encrypting plaintext with one DES key and then encrypting it with a second DES key is no more secure than using a single DES key. It would seem at first glance that if both keys have n bits, a brute force attack of trying all possible keys would require trying 2n × 2n or 22n different combinations. However, Merkle and Hellman showed that a known-plaintext, meet-in-the-middle attack could break the double encryption in 2n + 1 attempts. This type of attack is achieved by encrypting from one end, decrypting from the other, and comparing the results in the middle. Therefore, Triple DES is used to obtain stronger encryption.
Triple DES encrypts a message three times. This encryption can be accomplished in several ways. For example, the message can be encrypted with Key 1, decrypted with Key 2 (essentially another encryption), and encrypted again with Key 1:
[E{D[E(M,K1)],K2},K1]
A Triple DES encryption in this manner is denoted as DES–EDE2. If three encryptions are performed using the two keys, it is referred to as DES–EEE2:
[E{E[E(M,K1)],K2},K1]
Similarly,
E{E[E(M,K1)],K2},K3]
describes a triple encryption DES–EEE3 with three different keys. This encryption is the most secure form of Triple DES.
The Advanced Encryption Standard (AES)
AES is a block cipher that has replaced DES as a Federal standard, but it is anticipated that Triple DES will remain an approved algorithm for U.S. Government use. Triple DES and DES are specified in FIPS 46-3. The AES initiative was announced in January 1997 by NIST, and candidate encryption algorithm submissions were solicited. On August 29, 1998, a group of 15 AES candidates were announced by NIST. In 1999, NIST announced five finalist candidates. These candidates were MARS, RC6, Rijndael, Serpent, and Twofish. NIST closed Round 2 of public analyses of these algorithms on May 15, 2000.
On October 2, 2000, NIST announced the selection of the Rijndael Block Cipher, developed by the Belgian cryptographers Dr. Joan Daemen and Dr. Vincent Rijmen, as the proposed AES algorithm. Rijndael was formalized as the Advanced Encryption Standard (AES) on November 26, 2001, as Federal Information Processing Standard Publication (FIPS PUB 197). FIPS PUB 197 states that, “This standard may be used by Federal departments and agencies when an agency determines that sensitive (unclassified) information (as defined in P.L. 100-235) requires cryptographic protection. Other FIPS-approved cryptographic algorithms may be used in addition to, or in lieu of, this standard.” Depending upon which of the three keys is used, the standard may be referred to as “AES-128,” “AES-192,” or “AES-256.” AES is being adopted by other private and public organizations inside and outside the United States.
The Rijndael Block Cipher
The Rijndael algorithm was designed to have the following properties:
- Resistance against all known attacks
- Design simplicity
- Code compactness and speed on a wide variety of platforms
The Rijndael cipher can be categorized as an iterated block cipher with a variable block length and key length that can be independently chosen as 128, 192, or 256 bits.
In decimal terms, there are approximately 3.4 × 1038 possible 128-bit keys, 6.2 × 1057 possible 192-bit keys, and 1.1 × 1077 possible 256-bit keys.
AES specifies three key sizes - 128, 192, and 256 bits - with a fixed block size of 128 bits.
As a measure of the relative strength of the Rijndael encryption algorithm, if a computer could crack the DES encryption by trying 256 keys in one second, the same computer would require 149 trillion (149 × 1012) years to crack Rijndael. For a comparison, the universe is estimated to be fewer than 20 billion (20 × 109) years old.
Rijndael defines an intermediate cipher result as a State, upon which the transformations that are defined in the cipher operate.
Instead of a Feistel network, which takes a portion of the modified plaintext and transposes it to another position (see the discussion of Twofish in the following subsection), the Rijndael cipher employs a round transformation that comprises three layers of distinct and invertible transformations. These transformations are also defined as uniform, which means that every bit of the State is treated the same. Each of the layers has the following respective functions:
- The nonlinear layer. The parallel application of S-boxes that have optimum worst-case nonlinearity properties.
- The linear mixing layer. A layer that provides a guarantee of a high diffusion of multiple rounds.
- The key addition layer. An Exclusive Or of the Round key to the intermediate State.
Round keys are derived from the Cipher key through a key schedule, which consists of a key expansion and Round key selection - defined as follows in the Rijndael Block Cipher AES Proposal submitted to NIST:[*]
The total number of Round key bits is equal to block length multiplied by the number of rounds plus 1 (e.g., for a block length of 128 bits and 10 rounds, 1408 Round Key bits are needed). The Cipher Key is expanded into an Expanded Key. Round Keys are taken from the Expanded Key.
The number of rounds used in the Rijndael cipher is a function of the key size as follows:
- 256-bit key: 14 rounds
- 192-bit key: 12 rounds
- 128-bit key: 10 rounds
The Rijndael Block Cipher is suited for the following types of implementations:
- High-speed chips with no area restrictions
- A compact coprocessor on a smart card
The Twofish Algorithm
Another example of the evolution of cryptographic technology is found in the Twofish algorithm, one of the finalists in the AES competition.
In summary, Twofish is a symmetric block cipher that operates on 128-bit blocks in 16 rounds that works in all standard modes. It can accept key lengths up to 256 bits.
Twofish is a Feistel network in that in each round, one-half of the 128-bit block of plaintext or modified plaintext is fed into an element called the F Function box and then is XORed with the other half of the text in the network. This one-half block is broken into two 32-bit units that are, in turn, broken into four bytes. These four bytes are fed into four different, key-dependent S-boxes and emerge from the S-boxes as four transformed output bytes.
The four output bytes of the S-boxes are combined in a Maximum Distance Separable (MDS) matrix to form two 32-bit units. These two 32-bit units are then combined by using a pseudo-Hadamard transform (PHT) and are added to two round subkeys. The PHT is a linear operation of the form
d1 = (2b1 + b2)mod 256
where b1 and b2 are the inputs and d1 is the output.
These results are XORed with the right half of the 64 bits of the plaintext. In addition, 1-bit rotations are performed before and after the XOR. These operations are then repeated for 15 more rounds.
Twofish also employs what is termed as prewhitening and postwhitening, where additional subkeys are XORed with the plaintext before the first round and after the 16th round. This approach makes cryptanalysis more difficult because the whitening subkeys have to be determined in addition to the algorithm key.
In the Twofish algorithm, the MDS matrix, the PHT, and key additions provide diffusion.
The IDEA Cipher
The International Data Encryption Algorithm (IDEA) cipher is a secure, secret, key-block encryption algorithm that was developed by James Massey and Xuejia Lai.[*] It evolved in 1992 from earlier algorithms called the Proposed Encryption Standard and the Improved Proposed Encryption Standard. IDEA operates on 64-bit Plaintext blocks and uses a 128-bit key. It applies both confusion and diffusion.
The IDEA algorithm performs eight rounds and operates on 16-bit subblocks by using algebraic calculations that are amenable to hardware implementation. These operations are modulo 216 addition, modulo 216 + 1 multiplication, and the Exclusive Or.
With its 128-bit key, an IDEA cipher is much more difficult to crack than DES. IDEA operates in the modes described for DES and is applied in the Pretty Good Privacy (PGP) e-mail encryption system that was developed by Phil Zimmerman.
RC5 RC6
RC5 is a family of cryptographic algorithms invented by Ronald Rivest in 1994. It is a block cipher of variable block length and encrypts through integer addition, the application of a bitwise Exclusive Or, and variable rotations. The key size and number of rounds are also variable. Typical block sizes are 32, 64, or 128 bits. The number of rounds can range from 0 to 255, and the key size can range from 0 to 2,048 bits. RSA Data Security patented RC5 in 1997. RC6 is an upgrade that is similar to RC5 in specifications, but adds integer multiplication and additional working registers to increase the encryption speed.
[*]H. Feistel, “Block Cipher Cryptographic System,” U.S. Patent #3,798,539, March 19, 1974.
[†]Data Encryption Standard, FIPS PUB 46-1 (Washington, D.C.: National Bureau of Standards, January 15, 1977).
[‡]ANSI X3.92, “American National Standard for Data Encryption Algorithm (DEA),” American National Standards Institute, 1981.
[*]AES Proposal: Rijndael, Joan Daemen and Vincent Rijmen, version 2, 9/8/99.
[*]X. Lai, “On the Design and Security of Block Ciphers,” ETH Series on Information Processing, v. 1 (Konstanz: Hartung-Gorre Verlag, 1992).
Public Key (Asymmetric) Cryptosystems
Unlike secret-key cryptosystems, which make use of a single key that is known to both the sender and the receiver, public-key systems employ two keys: a public key and a private key. The recipient makes the public key available to anyone wanting to encrypt and send a message. The private key is used to decrypt the message. Thus, the need to exchange secret keys is eliminated. The following are the important points to note:
- The public key cannot decrypt the message that it encrypted.
- Ideally, the private key cannot be derived from the public key.
- A message that is encrypted by one of the keys can be decrypted with the other key.
- The private key is kept private.
When Kp is the public key and Ks is the private key, the process is illustrated as follows:
C = Kp(P) and P = Ks(C)
where C is the ciphertext and P is the plaintext.
In addition, the reverse is also true:
C = Ks(P) and P = Kp(C)
One Way Functions
Public-key cryptography is possible through the application of a one-way function. A one-way function is a function that is easy to compute in one direction but difficult to compute in the reverse direction. For such a function, if y = f(x), it would be easy to compute y if given x, but it would be very difficult to derive x when given y. A simple example would be the telephone directory. It is easy to find a number when given a name, but it is difficult to find the name when given a number. For a one-way function to be useful in the context of public key cryptography, it should have a trap door. A trap door is a secret mechanism that enables one to easily accomplish the reverse function in a one-way function. Thus, if you know the trap door, you can easily derive x in the previous example when given y.
In the context of public-key cryptography, it is very difficult to calculate the private key from the public key unless you know the trap door.
Public Key Algorithms
Several public-key algorithms have been developed. Some of these algorithms are applicable to digital signatures, encryption, or both. Because there are more calculations associated with public-key cryptography, it is 1000 to 10,000 times slower than secret-key cryptography. Thus, hybrid systems have evolved that use public-key cryptography to safely distribute the secret keys used in symmetric-key cryptography.
Some of the important public-key algorithms that have been developed include the Diffie-Hellman key exchange protocol, RSA, El Gamal, Knapsack, and Elliptic Curve.
RSA
RSA is derived from the last names of its inventors, R. L. Rivest, A. Shamir, and L. M. Adleman.[*] This algorithm is based on the difficulty of factoring a number, N, which is the product of two large prime numbers. These numbers might be 200 digits each. Thus, the difficulty in obtaining the private key from the public key is a hard, one-way function that is equivalent to the difficulty of finding the prime factors of N.
In RSA, public and private keys are generated as follows:
- Choose two large prime numbers, p and q, of equal length and compute p × q = n, which is the public modulus.
- Choose a random public key, e, so that e and (p – 1)(1q – 1) are relatively prime.
- Compute e × d = 1 mod (p – 1)(q – 1), where d is the private key.
- Thus, d = e-1 mod [(p – 1)(q – 1)].
From these calculations, (d, n) is the private key, and (e, n) is the public key.
The plaintext, P, is thus encrypted to generate ciphertext C as follows:
C = Pe mod n
and is decrypted to recover the plaintext, P, as
P = Cd mod n
Typically, the plaintext will be broken into equal length blocks, each with fewer digits than n, and each block will be encrypted and decrypted as shown.
RSA can be used for encryption, key exchange, and digital signatures.
Diffie-Hellman Key Exchange
The Diffie-Hellman Key Exchange is a method where subjects exchange secret keys over a nonsecure medium without exposing the keys. Dr. Whitfield Diffie and Dr. Martin Hellman disclosed the method in their seminal 1976 paper entitled “New Directions in Cryptography.”[†]
The method enables two users to exchange a secret key over an insecure medium without an additional session key. It has two system parameters, p and g. Both parameters are public and can be used by all the system’s users. Parameter p is a prime number, and parameter g, which is usually called a generator, is an integer less than p that has the following property: For every number n between 1 and p – 1 inclusive, there is a power k of g such that gk mod p = n.
For example, if given the following public parameters,
- p = prime number
- g = generator
- Generating equation y = gx mod p
then Alice and Bob can securely exchange a common secret key as follows:
- Alice uses her private value a to calculate:
ya = ga mod p
- Bob uses his private value b to calculate the following:
yb = gb mod p
- Alice can now send ya to Bob, and Bob can send yb to Alice. Knowing her private value, a, Alice can calculate (yb)a, which yields the following:
gba mod p
- Similarly, with his private value, b, Bob can calculate (ya)b as such:
gab mod p
- Because gba mod p is equal to gab mod p, Bob and Alice have securely exchanged the secret key.
In their paper, Diffie and Hellman primarily described key exchange, yet they also provided a basis for the further development of public-key cryptography.
El Gamal
Dr. T. El Gamal extended the Diffie-Hellman concepts to apply to encryption and digital signatures.[*] The El Gamal system is a nonpatented public-key cryptosystem that is based on the discrete logarithm problem. Encryption with El Gamal is illustrated in the following example:
Given the prime number p and the integer g, Alice uses her private key, a, to compute her public key as ya = ga mod p.
For Bob to send message M to Alice:
- Bob generates random number b < p.
- Bob computes yb = gb mod p and ym = M XOR yab = M XOR gab mod p.
- Bob sends yb, ym to Alice, and Alice computes yba = gab mod p.
- Therefore, M = yba XOR ym = gab mod p XOR M XOR gab mod p.
Merkle-Hellman Knapsack
The Merkle-Hellman Knapsack[*] is based on the problem of having a set of items with fixed weights and determining which of these items can be added in order to obtain a given total weight.
This concept can be illustrated by using a superincreasing set of weights. Superincreasing means that each succeeding term in the set is greater than the sum of the previous terms. The set [2, 3, 6, 12, 27, 52] has these properties. If we have a knapsack with a total weight of 69 for this example, the problem would be to find the terms whose sum is equal to 69. The solution to this simple example is that terms 52, 12, 3, and 2 would be in the knapsack. Or equivalently, if we represent the terms that are in the knapsack by 1s and those that are not by 0s, the ciphertext representing the “plaintext” 69 is 110101.
Elliptic Curve (EC)
Elliptic curves are another approach to public-key cryptography. This method was developed independently by Neal Koblitz[†] and V.S. Miller.[‡] Elliptic curves are usually defined over finite fields, such as real and rational numbers, and implement an analog to the discrete logarithm problem.
An elliptic curve is defined by the following equation:
- y2 = x3 + ax + b along with a single point O, the point at infinity.
The space of the elliptic curve has properties such that:
- Addition is the counterpart of modular multiplication.
- Multiplication is the counterpart of modular exponentiation.
Thus, given two points, P and R, on an elliptic curve where P = KR, finding K is the hard problem that is known as the elliptic curve discrete logarithm problem.
Because it is more difficult to compute elliptic curve discrete logarithms than to compute conventional discrete logarithms or to factor the product of large prime numbers, smaller key sizes in the elliptic curve implementation can yield higher levels of security. For example, an elliptic curve key of 160 bits is equivalent to a 1024-bit RSA key. This characteristic means fewer computational and memory requirements. Therefore, elliptic curve cryptography is suited to hardware applications such as smart cards and wireless devices. Elliptic curves can be used to implement digital signatures, encryption, and key management capabilities.
Public Key Cryptosystem Algorithm Categories
Public-key encryption utilizes hard, one-way functions. The calculations associated with this type of encryption are as follows:
- Factoring the product of large prime numbers
- RSA
- Finding the discrete logarithm in a finite field
- El Gamal
- Diffie-Hellman
- Schnorr’s signature algorithm
- Elliptic curve
- Nybergrueppel’s signature algorithm
Asymmetric and Symmetric Key Length Strength Comparisons
A comparison of the approximate equivalent strengths of public- and private-key cryptosystems is provided in Table 4-2.
|
ASYMMETRIC KEY SIZE |
SYMMETRIC KEY SIZE |
|---|---|
|
512 Bits |
64 Bits |
|
1792 Bits |
112 Bits |
|
2304 Bits |
128 Bits |
Digital Signatures
The purpose of digital signatures is to detect unauthorized modifications of data and to authenticate the identity of the signatories and nonrepudiation. These functions are accomplished by generating a block of data that is usually smaller than the size of the original data. This smaller block of data is bound to the original data and to the identity of the sender. This binding verifies the integrity of data and provides nonrepudiation. To quote the NIST Digital Signature Standard (DSS):
Digital signatures are used to detect unauthorized modifications to data and to authenticate the identity of the signatory. In addition, the recipient of signed data can use a digital signature in proving to a third party that the signature was in fact generated by the signatory.[*]
To generate a digital signature, the digital signal program passes the file to be sent through a one-way hash function. This hash function produces a fixed-size output from a variable-size input. The output of the hash function is called a message digest. The message digest is uniquely derived from the input file, and if the hash algorithm is strong, the message digest has the following characteristics:
- The hash function is considered one-way because the original file cannot be created from the message digest.
- Two different files should not have the same message digest.
- Given a file and its corresponding message digest, it should not be feasible to find another file with the same message digest.
- The message digest should be calculated by using all the original file’s data.
After the message digest is calculated, it is encrypted with the sender’s private key. The encrypted message digest is then attached to the original file and is sent to the receiver. The receiver then decrypts the message digest by using the sender’s public key. If this public key opens the message digest and it is the true public key of the sender, verification of the sender is then accomplished. Verification occurs because the sender’s public key is the only key that can decrypt the message digest encrypted with the sender’s private key. Then, the receiver can compute the message digest of the received file by using the identical hash function as the sender. If this message digest is identical to the message digest that was sent as part of the signature, the message has not been modified.
Digital Signature Standard (DSS) and Secure Hash Standard (SHS)
NIST announced the Digital Signature Standard (DSS) Federal Information Processing Standard (FIPS) 186-1 and issued an updated version, FIPS 186-2, in January of 2000. This standard enables the use of the RSA digital signature algorithm, the Elliptic Curve Digital Signature Algorithm (ECDSA), or the Digital Signature Algorithm (DSA). The DSA is based on a modification of the El Gamal digital signature methodology and was developed by Claus Schnorr.[*]
These digital signature algorithms use the Secure Hash Algorithm (SHA-1) as defined in FIPS 180-1.[†]
SHA-1 computes a fixed-length message digest from a variable length input message. The DSA then processes this message digest to either generate or verify the signature. Applying this process to the shorter message digest is more efficient than applying it to the longer message.
As previously discussed, any modification to the message being sent to the receiver results in a different message digest being calculated by the receiver. Thus, the signature will not be verified.
SHA-1 produces a message digest of 160 bits when any message less than 264 bits is used as an input.
SHA-1 has the following properties:
- It is computationally infeasible to find a message that corresponds to a given message digest.
- It is computationally infeasible to find two different messages that produce the same message digest.
For SHA-1, the length of the message is the number of bits in a message. Padding bits are added to the message to make the total length of the message, including padding, a multiple of 512. To quote from the NIST DSS/SHS document:
The SHA-1 sequentially processes blocks of 512 bits when computing a message digest. The following specifies how the padding shall be performed. As a summary, a “1” followed by m “0’s” followed by a 64-bit integer are applied to the end of the message to produce a padded message of length 512*n. The 64-bit integer is l, the length of the original message. The padded message is then processed by the SHA-1 as n 512-bit blocks.
SHA-1 has been broken and is now not recommended for use. As a result, four additional different versions of SHA have been developed with their numbers indicating the length of their output message digests. These versions are designated SHA-224, SHA-256, SHA-384, and SHA-512 and are collectively referred to as SHA-2.
MD5
MD5 is a message digest algorithm that was developed by Ronald Rivest in 1991. MD5 takes a message of an arbitrary length and generates a 128-bit message digest. In MD5, the message is processed in 512-bit blocks in four distinct rounds.
Sending a Message with a Digital Signature
In summary, to send a message:
- A hash algorithm is used to generate the message digest from the message.
- The message digest is fed into the digital signature algorithm that generates the signature of the message. The signing of the message is accomplished by encrypting the message digest with the sender’s private key and attaching the result to the message. Thus, the message is a signed message.
- The message and the attached message digest are sent to the receiver. The receiver then decrypts the attached message digest with the sender’s public key.
The receiver also calculates the message digest of the received message by using the same hash function as the sender. The two message digests should be identical. If they are not identical, the message was modified in transmission. If the two message digests are identical, the message sent is identical to the message received, the sender is verified, and the sender cannot repudiate the message.
Hashed Message Authentication Code (HMAC)
An HMAC is a hash algorithm that generates a Message Authentication Code (MAC). A MAC is a type of checksum that is a function of the information in the message. The MAC is generated before the message is sent, then appended to the message, and then both are transmitted.
At the receiving end, a MAC is generated from the message alone by using the same algorithm as that used by the sender. This MAC is compared to the MAC sent with the message. If they are not identical, the message was modified en route.
Hashing algorithms can be used to generate the MAC and hash algorithms using secret keys that provide stronger protection than an ordinary MAC generation. The methodology is the same as using a non-keyed hashed MAC, but the hash algorithm requires a secret key to generate the MAC message digest. This secret key is protected and should be known only to the sender and receiver.
Hash Function Characteristics
As described in the previous section, a hash function (H) is used to condense a message of an arbitrary length into a fixed-length message digest. This message digest should uniquely represent the original message, and it will be used to create a digital signature. Furthermore, it should not be computationally possible to find two messages, M1 and M2, such that H(M1) = H(M2). If this situation were possible, an attacker could substitute another message (M2) for the original message (M1), and the message digest would not change. Because the message digest is the key component of the digital signature authentication and integrity process, a false message could be substituted for the original message without detection. Specifically, it should not be computationally possible to find:
- A message (M2) that would hash to a specific message digest generated by a different message (M1)
- Two messages that hash to any common message digest
These two items refer to an attack against the hash function known as a birthday attack. This attack relates to the paradoxes that are associated with the following questions:
- If you were in a room with other people, what would be the sample size, n, of individuals in the room to have a better than 50/50 chance of someone having the same birthday as you? (The answer is 253.)
- If you were in a room with other people, what would be the sample size, n, of individuals in the room to have a better than 50/50 chance of at least two people having a common birthday? (The answer is 23, because with 23 people in a room, there are n(n – 1)/2 or 253 pairs of individuals in the room.)
[*]R. L. Rivest, A. Shamir, and L. M. Adleman, “A Method for Obtaining Digital Signatures and Public-Key Cryptosystems,” Communications of the ACM, v. 21, n. 2, February 1978, pp. 120–126.
[†]W. Diffie and M. E. Hellman, “New Directions in Cryptography,” IEEE Transactions on Information Theory, Vol. IT-22, November 1976, pp. 644–654.
[*]T. El Gamal, “A Public-Key Crypto System and a Signature Scheme Based on Discrete Logarithms,” Advances in Cryptography: Proceedings of CRYPTO 84 (Springer-Verlag, 1985), pp. 10–18.
[*]R. C. Merkle and M. Hellman, “Hiding Information and Signatures in Trapdoor Knapsacks,” IEEE Transactions on Information Theory, v. 24, n. 5, September 1978, pp. 525–530.
[†]N. Koblitz, “Elliptic Curve Cryptosystems,” Mathematics of Computation, v. 48, n. 177, 1987, pp. 203–209.
[‡]V.S. Miller, “Use of Elliptic Curves in Cryptography,” Advances in Cryptology - CRYPTO ‘85 Proceedings (Springer-Verlag, 1986), pp. 417–426.
[*]National Institute of Standards and Technology, NIST FIPS PUB 186, “Digital Signature Standard,” U.S. Department of Commerce, May 1994.
[*]C.P. Schnorr, “Efficient Signature Generation for Smart Cards,” Advances in Cryptology - CRYPTO ‘89 Proceedings (Springer-Verlag, 1990), pp. 239–252.
[†]NIST, NIST FIPS PUB 180-1, “Secure Hash Standard,” U.S. Department of Commerce, April 1995.
Cryptographic Attacks
As defined earlier, cryptanalysis is the act of obtaining the plaintext or key from the ciphertext. Cryptanalysis is used to obtain valuable information and to pass on altered or fake messages in order to deceive the original intended recipient. This attempt at cracking the cipher is also known as an attack. The following are examples of some common attacks:
- Brute force. Trying every possible combination of key patterns; the longer the key length, the more difficult it is to find the key with this method. This method is also known as exhaustive search and is becoming increasingly effective through the use of large numbers of computers operating on the Internet searching different parts of the key space until the correct key is discovered.
- Known plaintext. The attacker has a copy of the plaintext corresponding to the ciphertext and uses this information to attempt to determine the key.
- Chosen plaintext. Chosen plaintext is encrypted and the output ciphertext is obtained.
- Adaptive chosen plaintext. A form of a chosen plaintext attack in which the selection of the plaintext is altered according to the previous results.
- Ciphertext only. Only the ciphertext is available, and the attacker attempts to determine the corresponding plaintext.
- Chosen ciphertext. Portions of the ciphertext are selected for trial decryption while having access to the corresponding decrypted plaintext.
- Adaptive chosen ciphertext. A form of a chosen ciphertext attack in which the selection of the portions of ciphertext for the attempted decryption is based on the results of previous attempts.
- Birthday attack. Usually applied to the probability of two different messages using the same hash function, which produces a common message digest; or given a message and its corresponding message digest, finding another message that when passed through the same hash function generates the same specific message digest. The term birthday comes from the fact that in a room with 23 people, the probability of two or more people having the same birthday is greater than 50 percent.
- Meet-in-the-middle. An attack that is applied to double encryption schemes by encrypting known plaintext from one end with each possible key (K) and comparing the results “in the middle” with the decryption of the corresponding ciphertext with each possible K.
- Man-in-the-middle. An attacker taking advantage of the store-and-forward nature of most networks by intercepting messages and forwarding modified versions of the original message while between two parties attempting secure communications.
- Differential cryptanalysis. A method usually applied to block-cipher private-key cryptographic systems by looking at ciphertext pairs that were generated through the encryption of plaintext pairs with specific differences and analyzing the effect of these differences.
- Linear cryptanalysis. Using pairs of known block-cipher plaintext and corresponding ciphertext to generate a linear approximation of a portion of the key.
- Differential linear cryptanalysis. Using both differential and linear approaches.
- Factoring. Using a mathematical approach to determine the prime factors of large numbers.
- Algebraic. An attack applied to block ciphers that exhibit mathematical relationships when encrypted with different keys.
- Statistical. Exploiting the lack of randomness in key generation.
Public Key Certification Systems
A source that could compromise a public-key cryptographic system is an individual (A) who is posting a public key under the name of another individual (B). In this scenario, the people who are using this public key to encrypt the messages that were intended for individual B will actually be sending messages to individual A. Because individual A has the private key that corresponds to the posted public key, individual A can decrypt the messages that were intended for individual B.
Digital Certificates
To counter this type of attack, a certification process can be used to bind individuals to their public keys. A Certificate Authority (CA) acts as notary by verifying a person’s identity and issuing a certificate that vouches for a public key of the named individual. This certification agent signs the certificate with its own private key. Therefore, the individual is verified as the sender if that person’s public key opens the data. The certificate contains the subject’s name, the subject’s public key, the name of the certificate authority, and the period in which the certificate is valid. To verify the CA’s signature, its public key must be cross-certified with another CA. (The X.509 standard defines the format for public key certificates.) This certificate is then sent to a repository, which holds the certificates and Certificate Revocation Lists (CRLs) that denote the revoked certificates. The diagram shown in Figure 4-14 illustrates the use of digital certificates in a transaction between a subscribing entity and a transacting party. Digital certificates will be discussed in more detail in the following sections.
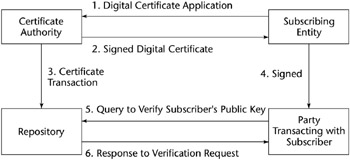
Figure 4-14: A transaction with digital certificates.
Public Key Infrastructure (PKI)
The integration of digital signatures and certificates and the other services required for E-commerce is called the Public-Key Infrastructure (PKI). These services provide integrity, access control, confidentiality, authentication, and non-repudiation for electronic transactions. The PKI includes the following elements:
- Digital certificates
- Certificate authority (CA)
- Registration authorities
- Policies and procedures
- Certificate revocation
- Non-repudiation support
- Timestamping
- Lightweight Directory Access Protocol (LDAP)
- Security-enabled applications
Digital Certificates
The digital certificate and management of the certificate are major components of PKI. Remember: The purpose of a digital certificate is to verify to all that an individual’s public key - posted on a public “key ring” - is actually his. A trusted, third-party CA can verify that the public key is that of the named individual and then issue a certificate attesting to that fact. The CA accomplishes the certification by digitally signing the individual’s public key and associated information.
A CA acts as notary by verifying a person’s identity and issuing a certificate that vouches for the public key of the named individual. This certification agent signs the certificate with its own private key. The certificate is then sent to a repository, which holds the certificates and CRLs that denote the revoked certificates. To verify the CA’s signature, its public key must be cross-certified with another CA’s.
Certificates and CRLs can be held in a repository, with responsibilities defined between the repository and the CA. The repository access protocol determines how these responsibilities are assigned. In one protocol, the repository interacts with other repositories, CAs, and users. The CA deposits its certificates and CRLs into the repository. The users can then access the repository for this information.
Directories and X.500
In PKI, a repository is usually referred to as a directory. The directory contains entries associated with an object class. An object class can refer to individuals or other computer-related entities. The class defines the attributes of the object. Attributes for PKI are defined in RFC 2587, Internet X.509 Public Key Infrastructure LDAP v2 Schema by Boeyen, Howes, and Richard, published in 1999. Additional information on attributes can be found in RFC 2079, Definition of an X.500 Attribute Type and an Object Class to Hold Uniform Resource Identifiers (URLs), by M. Smith, published in January 1997.
The X.509 certificate standard defines the authentication bases for the X.500 directory. The X.500 directory stores information about individuals and objects in a distributed database residing on network servers. Some of the principal definitions associated with X.500 include the following:
- Directory User Agents (DUAs) - clients
- Directory Server Agents (DSAs) - servers
- Directory Service Protocol (DSP) - enables information exchanges between DSAs
- Directory Access Protocol (DAP) - enables information exchanges from a DUA to a DSA
- Directory Information Shadowing Protocol (DISP) - used by a DSA to duplicate or “shadow” some or all its contents
DSAs accept requests from anonymous sources as well as authenticated requests. They share information through a chaining mechanism.
The Lightweight Directory Access Protocol
The Lightweight Directory Access Protocol (LDAP) was developed as a more efficient version of DAP and has evolved into a second version (Yeong, Y., T. Howes, and S. Killie, Lightweight Directory Access Protocol, RFC 1777, 1995). LDAP servers communicate through referrals (that is, a directory receiving a request for information it does not have will query the tables of remote directories). If it finds a directory with the required entry, it sends a referral to the requesting directory. LDAP v2 does not have chaining and shadowing capabilities, but additional protocols can be obtained to provide these functions.
LDAP provides a standard format to access the certificate directories. These directories are stored on network LDAP servers and provide public keys and corresponding X.509 certificates for the enterprise. A directory contains information, such as individuals’ names, addresses, phone numbers, and public key certificates. The standards under X.500 define the protocols and information models for computer directory services that are independent of the platforms and other related entities. LDAP servers are subject to attacks that affect availability and integrity. For example, Denial of Service attacks on an LDAP server could prevent access to the CRLs and thus permit the use of a revoked certificate.
The DAP protocol in X.500 was unwieldy and led to most client implementations using LDAP. LDAP version 3 is under development; it will include extensions that provide shadowing and chaining capabilities.
X.509 Certificates
The original X.509 certificate (CCITT, The Directory - Authentication Framework, Recommendation X.509, 1988) was developed to provide the authentication foundation for the X.500 directory. Since then, a version 2, version 3, and recently, a version 4 have been developed. Version 2 of the X.509 certificate addresses the reuse of names, version 3 provides for certificate extensions to the core certificate fields, and version 4 provides additional extensions. These extensions can be used as needed by different users and different applications. A version of X.509 that takes into account the requirements of the Internet was published by the IETF (Housley, R., W. Ford, W. Polk, and D. Solo, Internet X.509 Public Key Infrastructure Certificate and CRL Profile, RFC 2459, 1999).
The Consultation Committee, International Telephone and Telegraph, International Telecommunications Union (CCITT-ITU)/International Organization for Standardization (ISO) has defined the basic format of an X.509 certificate. This structure is outlined in Figure 4-15.
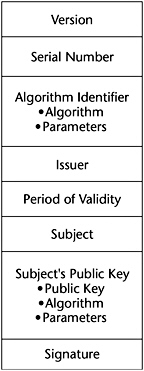
Figure 4-15: The CCITT-ITU/ ISO X.509 certificate format.
If version 3 certificates are used, the optional extensions field can be used. It comes before the signature field components in the certificate. Some typical extensions are the entity’s name and supporting identity information, the attributes of the key, certificate policy information, and the type of the subject. The digital signature serves as a tamper-evident envelope.
Some of the different types of certificates that are issued include the following:
- CA certificates. Issued to CAs, these certificates contain the public keys used to verify digital signatures on CRLs and certificates.
- End entity certificates. Issued to entities that are not CAs, these certificates contain the public keys that are needed by the certificate’s user in order to perform key management or verify a digital signature.
- Self-issued certificates. These certificates are issued by an entity to itself to establish points of trust and to distribute a new signing public key.
- Rollover certificates. These certificates are issued by a CA to transition from an old public key to a new one.
Certificate Revocation Lists
Users check the certificate revocation list (CRL) to determine whether a digital certificate has been revoked. They check for the serial number of the signature. The CA signs the CRL for integrity and authentication purposes. A CRL is shown in Figure 4-16 for an X.509 version 2 certificate.
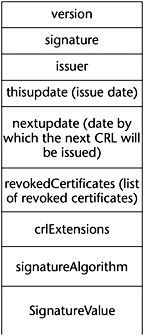
Figure 4-16: CRL format (version 2).
The CA usually generates the CRLs for its population. If the CA generates the CRLs for its entire population, the CRL is called a full CRL.
Key Management
Obviously, when dealing with encryption keys, the same precautions must be used as with physical keys to secure the areas or the combinations to the safes. The components of key management are listed in the following sections.
Key Distribution
As noted earlier, distributing secret keys in symmetric-key encryption poses a problem. Secret keys can be distributed by using asymmetric-key cryptosystems. Other means of distributing secret keys include face-to-face meetings to exchange keys, sending the keys by secure messenger, or some other secure alternate channel. Another method is to encrypt the secret key with another key, called a key encryption key, and send the encrypted secret key to the intended receiver. These key encryption keys can be distributed manually, but they need not be distributed often. The X9.17 Standard (ANSI X9.17 [Revised], “American National Standard for Financial Institution Key Management [Wholesale],” American Bankers Association, 1985) specifies key encryption keys as well as data keys for encrypting the plaintext messages.
Key distribution can also be accomplished by splitting the keys into different parts and sending each part by a different medium.
In large networks, key distribution can become a serious problem because in an N-person network, the total number of key exchanges is N(N – 1)/2. Using public key cryptography or the creation and exchange of session keys that are valid only for a particular session and time are useful mechanisms for managing the key distribution problem.
Keys can be updated by generating a new key from an old key. If, for example, Alice and Bob share a secret key, they can apply the same transformation function (a hash algorithm) to their common secret key and obtain a new secret key.
Key Revocation
A digital certificate contains a timestamp or period for which the certificate is valid. Also, if a key is compromised or must be made invalid because of business- or personnel-related issues, it must be revoked. The CA maintains a CRL of all invalid certificates. Users should regularly examine this list.
Key Recovery
A system must be put in place to decrypt critical data if the encryption key is lost or forgotten. One method is key escrow. In this system, the key is subdivided into different parts, each of which is encrypted and then sent to a different trusted individual in an organization. Keys can also be escrowed onto smart cards.
Key Renewal
Obviously, the longer a secret key is used without changing it, the more it is subject to compromise. The frequency with which you change the key is a direct function of the value of the data being encrypted and transmitted. Also, if the same secret key is used to encrypt valuable data over a relatively long period of time, you risk compromising a larger volume of data when the key is broken. Another important concern if the key is not changed frequently is that an attacker can intercept and change messages and then send different messages to the receiver.
Key encryption keys, because they are not used as often as encryption keys, provide some protection against attacks.
Typically, private keys used for digital signatures are not frequently changed and may be kept for years.
Key Destruction
Keys that have been in use for long periods of time and are replaced by others should be destroyed. If the keys are compromised, older messages sent with those keys can be read.
Keys that are stored on disks or EEPROMS should be overwritten numerous times. One can also destroy the disks by shredding and burning them. However, in some cases, it is possible to recover data from disks that were put into a fire. Any hardware device storing the key, such as an EPROM, should also be physically destroyed.
Older keys stored by the operating system in various locations in memory must also be searched out and destroyed.
Multiple Keys
Usually, an individual has more than one public/private key pair. The keys may be of different sizes for different levels of security. A larger key size may be used for digitally signing documents and a smaller key size may be used for encryption. A person may also have multiple roles or responsibilities wherein they want to sign messages with a different signature. One key pair may be used for business matters, another for personal use, and another for some other activity, such as being a school board member.
Distributed versus Centralized Key Management
A CA is a form of centralized key management. It is a central location that issues certificates and maintains CRLs. An alternative is distributed key management, in which a “chain of trust” or “web of trust” is set up among users who know each other. Because they know each other, they can trust that each one’s public key is valid. Some of these users may know other users and can thus verify their public key. The chain spreads outward from the original group. This arrangement results in an informal verification procedure that is based on people knowing and trusting each other.
Approaches to Escrowed Encryption
In some instances, there is a need for law enforcement agencies to have access to information transmitted electronically over computer networks. To have this access, law enforcement agencies need the encryption keys to read the enciphered messages. At the same time, the privacy of citizens must be protected from illegal and unauthorized surveillance of their digital communications. This section describes two approaches to this issue.
The Escrowed Encryption Standard
This standard (National Institute of Standards and Technology, NIST FIPS PUB 185, “Escrowed Encryption Standard,” U.S. Department of Commerce, Feb 1994) strives to achieve individual privacy and, at the same time, strives to provide for legal monitoring of the encrypted transmissions. The idea is to divide the key into two parts and then to escrow two portions of the key with two separate trusted organizations. Then law enforcement officials, after obtaining a court order, can retrieve the two pieces of the key from the organizations and decrypt the message. The Escrowed Encryption Standard is embodied in the U.S. Government’s Clipper Chip, which is implemented in tamper-proof hardware. The Skipjack Secret Key algorithm performs the encryption. Figure 4-17 is a block diagram of the Clipper Chip and the components of a transmitted message.
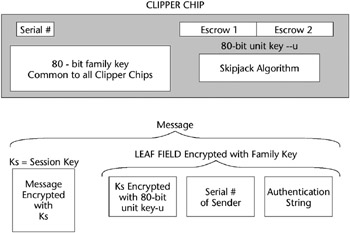
Figure 4-17: A Clipper Chip block diagram.
Each Clipper Chip has a unique serial number and an 80-bit unique unit or secret key. The unit key is divided into two parts and is stored at two separate organizations with the serial number that uniquely identifies that particular Clipper Chip. Initially, two parties that wish to exchange information agree on a session key, Ks. Ks can be exchanged by using a Diffie-Hellman or an RSA key exchange. The plaintext message, M, is encrypted with the session key, Ks. Ks is not escrowed. In addition, a Law Enforcement Access Field (LEAF) is transmitted along with the encrypted message, M. The LEAF is encrypted with the family key, which is common to all Clipper Chips, and contains the following:
- Ks encrypted with secret key, u
- The serial number of sending Clipper Chip
- An authentication string
When the intended individual receives the transmitted items, this person decrypts the message with the mutually known session key, Ks.
A law enforcement agency can obtain the session key as follows:
- Decrypt the LEAF with a family key to obtain the particular Clipper Chip serial number and encrypted session key. Ks is still encrypted with the secret family key, u.
- Present an authorization court order to the two escrow agencies and obtain the two portions of the key, u.
- Decrypt Ks with the key, u.
- Decrypt the message, M, with Ks.
The 80-bit key of the Clipper Chip is weak. Concerns also exist over the escrow agencies’ abilities to protect the escrowed keys, and whether these agencies may divulge them in unauthorized ways.
Key Escrow Approaches Using Public Key Cryptography
Another key escrow approach is Fair Cryptosystems. In 1992, Sylvio Micali introduced the concept of Fair Cryptosystems (S. Micali, “Fair Cryptosystems,” MIT/LCS/TR-579.b, MIT Laboratory for Computer Science, Nov. 1993), where the private key of a public/private key pair is divided into multiple parts and distributed to different trustees. In 1994, Micali obtained patents on this approach that were eventually purchased by Banker’s Trust.
One valuable characteristic of Micali’s approach is that each portion of the secret key can be verified as correct without having to reconstruct the entire key. This is accomplished by giving each trustee a piece of each public key and private key. Micali also developed calculations that can be used on each trustee’s private/public key pieces to verify that they are correct. If authorities have the legal permission to decrypt a message that is encrypted with the secret key, they can obtain all the portions of the private key and read the message. Micali also proposed a threshold approach where some subset of the trustee’s set would be sufficient to recover the entire secret key.
Micali’s approach can be applied by voluntary trustees in different countries or business areas rather than by a controlled, governmental entity.
Identity Based Encryption
As noted in the sections on digital certificates and PKI, there is a substantial amount of overhead required to implement and apply these concepts. Some of the issues involved are that users must be online to effect secure communications, certificates must be located and identified for intended message recipients, and certificates must be validated prior to use.
An alternative approach, proposed by Adi Shamir in 1984, is Identity-Based Encryption (IBE). The IBE concept proposes that any string can be used as an individual’s public key, including his or her e-mail address. Two additional features of IBE are that the sender does not have to go online to obtain the intended recipient’s certificate, and mail can be sent to recipients who have not established a public key. IBE, however, was not workable until 2001, when Dr. Daniel Boneh of Stanford University and Dr. Matt Franklin of the University of California at Davis developed a solution (D. Boneh and M. Franklin, “Identity-Based Encryption from the Weil Paring,” Crypto 2001, Lecture Notes in Computer Science, Vol. 2139, Springer-Verlag, 2001, pp. 213–229.) The solution involves points on an elliptic curve and the mathematical concept of a bilinear map. Using the Weil Pairing form of a bilinear map, the bilinear map exhibits the property that Pair (a∞P, b ∞Q) = Pair (b∞P, a ∞Q), where the operation ∞ is multiplication in the elliptic curve space, a and b are integers, and P and Q are points on an elliptic curve. The key to this approach is the one-way function wherein it is easy to perform a∞P but virtually impossible to find a, given P and a∞P.
Using the Weil Pairing, the IBE algorithm can be developed as follows:
- Parameters x and P are generated as random numbers by a key server. x is a parameter that is to be kept secret.
- P and x∞P are sent to all users.
- The key server generates a private key for all users based on the users’ IDs. For example, if Alice’s ID is alice@mymail.com, Alice’s private key is x∞alice@mymail.com.
- For Bob to send an encrypted e-mail message to Alice, Bob generates a random number, y, and then generates the key, K, as K = Pair(y∞alice@mymail.com, x∞P).
- Bob sends the message M, encrypted with K, to Alice as Ek(M), along with the product y∞P.
- Alice receives the message and now needs the key, K, to decrypt the message.
- Alice generates the key through the calculation of K = Pair(x∞alice@mymail.com, y∞P).
- Because Alice is the only one who has the value x∞alice@mymail.com, she is the only person that can decrypt the message.
- Again, this sequence is possible because under the Weil Pairing, K= Pair(y∞alice@mymail.com, x∞P) = Pair(x∞alice@mymail.com, y∞P).
To summarize, the IBE algorithm has four components:
- SETUP - generates the global parameters and a master-key
- EXTRACTING - generates the private key corresponding to an individual’s public key string ID, using the master-key
- ENCRYPTING - based on the public key ID, encrypts the messages
- DECRYPTING - decrypts the messages with the corresponding private key
Thus, based on the IBE algorithm, for Bob to send an encrypted e-mail to Alice, he does not need to acquire Alice’s digital certificate. He encrypts the message by using Alice’s public key string, “alice@mymail.com.” Upon receipt of the encrypted message, Alice contacts a third party, a Private Key Generation Server. After authenticating Alice, the Server provides Alice with her private key, which she uses to decrypt the e-mail from Bob. With this approach, Bob can send encrypted e-mail to Alice even though she has not yet established her public-key certificate.
Cryptographic Export Issues
In the 1990’s, 17 members of the international community formed the Coordinating Committee for Multilateral Export Controls (COCOM). COCOM developed regulations for exporting mass-market cryptographic software among its members and for preventing such exports to terrorist countries such as North Korea, Iran, and Syria. COCOM was discontinued in 1994 but, in 1995, a new agreement addressing cryptographic exports was produced by a group of 28 countries. These new controls were issued under the title, Wasssenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies. The original Wassenaar Arrangement was modified in 1998 to permit the export of symmetric-key products with keys up to 56 bits and public-key cryptographic products using up to 512-bit keys. It also relaxed the export of encryption products used to protect intellectual property. Also, public domain cryptographic software was declared eligible for export without restriction.
In the European Union (EU), the export of cryptographic products comes under the regulation of dual-use goods covered by the European Council (EC) regulation, 1334/2000. Exports within EU countries are minimally regulated, except for items that perform cryptanalysis. These products are handled by Intra-Community Licenses that permit such exports under certain specified conditions.
In July 2000, the United States announced a relaxation of its encryption export policy to certain countries. To quote the President’s Chief of Staff, John D. Podesta, “Under our new policy, American companies can export any encryption product to any end user in the European Union and eight other trading partners. We’re also speeding up the time to market by eliminating the thirty-day waiting period when exporting encryption goods to these countries.” Podesta also pointed out the effect that advancing technology has had on the Electronic Communications and Privacy Act (ECPA). He pointed out “ECPA, like its predecessors, has, in many ways, become outdated by the new advances in computer technology and electronic communication. Since its passage in 1986, we’ve seen a communications revolution with the explosion of the cell phone and the development and use of the World Wide Web. Today, there more than 95 million cell phone users, and more than 50 million households on line in the United States. More than 1.4 billion e-mails change hands every day ECPA was not devised to address many of the issues related to these newer, faster means of electronic communication. It doesn’t extend the stringent Title III protections to the capture of e-mail that you send to your friends or business partners.” Podesta cited legislation, which is being proposed to amend existing statutes and outmoded language, which applies primarily to wiretapping and to define protections for hardware and software systems in general.
The United States does not permit the knowing export of cryptographic source code to terrorist countries such as North Korea, Iran, Syria, and Sudan.
Quantum Computing
In digital computers, a bit is in either a one or zero state. In a quantum computer, through linear superposition, a quantum bit (qubit) can be in both states, essentially simultaneously. For example, a qubit can be can be represented by atoms or subatomic particles that exhibit a spin. A clockwise spin can be used to represent the digital value of 1 and a counterclockwise spin can represent a 0. In the quantum world, both values can exist simultaneously unless the particle is disturbed by outside influences. Thus, computations consisting of trial evaluations of large binary patterns can, theoretically, take place simultaneously in polynomial time instead of exponential time.
An example of quantum computing applied to cryptography is through the implementation of Shor’s algorithm (P.W. Shor, “Polynomial-time Algorithms for Prime Factorization and Discreet Logarithms on a Quantum Computer.” SIAM Journal on Computing 26, no. 5, 1997, pp. 1484–1509). This algorithm applies Fourier transforms with the linear superposition property of qubits to factor large numbers. As discussed in the RSA public-key algorithm description, the strength of that approach is the difficulty of factoring large numbers that are a product of two prime numbers. Thus, if a quantum computer can be physically realized, it will make it possible to defeat cryptographic systems that are now deemed impossible to break. Quantum computing also holds promise in the area of cryptographic transmissions that are impossible to intercept and break because of the property that the state of linear superposition collapses when disturbed by outside influences, such as attempts to intercept the message.
E mail Security Issues and Approaches
The main objectives of e-mail security are to ensure the following:
- Non-repudiation
- Messages are read only by their intended recipients
- Integrity of the message
- Authentication of the source
- Verification of delivery
- Labeling of sensitive material
- Control of access
The following standards have been developed to address some or all of these issues:
Secure Multi Purpose Internet Mail Extensions (S MIME)
S/MIME is a specification that adds secure services to e-mail in a MIME format. S/MIME provides for authentication through digital signatures and the confidentiality of encryption. S/MIME follows the Public Key Cryptography Standards (PKCS) and uses the X.509 standard for its digital certificates.
MIME Object Security Services (MOSS)
MOSS provides flexible e-mail security services by supporting different trust models. Introduced in 1995, MOSS provides authenticity, integrity, confidentiality, and non-repudiation to e-mail. It uses MD2/MD5, RSA Public Key, and DES. MOSS also permits user identification outside of the X.509 Standard.
Privacy Enhanced Mail (PEM)
Privacy Enhanced Mail (PEM) is a standard that was proposed by the IETF to be compliant with the Public Key Cryptography Standards (PKCS), which were developed by a consortium that included Microsoft, Novell, and Sun Microsystems. PEM supports the encryption and authentication of Internet e-mail. For message encryption, PEM applies Triple DES-EDE, using a pair of symmetric keys. RSA Hash Algorithms MD2 or MD5 are used to generate a message digest, and RSA public-key encryption implements digital signatures and secure key distribution. PEM employs certificates that are based on the X.509 standard and are generated by a formal CA.
Pretty Good Privacy (PGP)
In order to bring e-mail security to the “masses,” Phil Zimmerman developed the Pretty Good Privacy (PGP) software (Zimmerman, Philip R., The Official PGP User’s Guide, Cambridge, MA: MIT Press, 1995). Zimmerman derived the PGP name from Ralph’s Pretty Good Grocery, which sponsors Garrison Keillor’s A Prairie Home Companion radio show. PGP uses the symmetric cipher IDEA to encipher the message and RSA for symmetric key exchange and for digital signatures.
Instead of using a CA, PGP uses a Web of Trust. Users can certify each other in a mesh model, which is best applied to smaller groups (as shown in Figure 4-18).
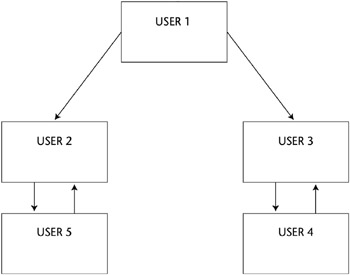
Figure 4-18: A PGP Web of Trust.
Internet Security Applications
With the growing use of the Internet and World Wide Web for commercial transactions, there is a need for providing confidentiality, integrity, and authentication of information. This section describes some of the approaches to obtain secure Internet and World Wide Web e-commerce.
Message Authentication Code (MAC) or the Financial Institution Message Authentication Standard (FIMAS)
In order to protect against fraud in electronic fund transfers, the Message Authentication Code (MAC), ANSI X9.9, was developed. As discussed earlier in this chapter, the MAC is a check value derived from the contents of the message itself that is sensitive to the bit changes in a message. It is similar to a Cyclic Redundancy Check (CRC). A MAC is appended to the message before it is transmitted. At the receiving end, a MAC is generated from the received message and is compared to the MAC of an original message. A match indicates that the message was received without any modification occurring while en route.
To strengthen the MAC algorithm, a keyed MAC can be generated by using a symmetric-key encryption, such as DES. Typically, the Exclusive Or function of the DES key with a message is performed on the sequential, 8-byte blocks of the message to generate the MAC. As with all symmetric-key applications, the key must be distributed securely so that sender and receiver have the same key.
Secure Electronic Transaction (SET)
A consortium including MasterCard and Visa developed SET in 1997 as a means of preventing fraud from occurring during electronic payments. SET provides confidentiality for purchases by encrypting the payment information. Thus, the seller cannot read this information. SET uses a DES symmetric-key system for encryption of the payment information and uses RSA for the symmetric-key exchange and digital signatures. SET covers the end-to-end transactions from the cardholder to the financial institution.
Secure Sockets Layer (SSL) Transaction Layer Security (TLS)
The SSL protocol was developed by Netscape in 1994 to secure Internet client-server transactions. The SSL protocol authenticates the server to the client, using public-key cryptography and digital certificates. In addition, this protocol provides for optional client-to-server authentication. It supports the use of RSA public-key algorithms; IDEA, DES, and 3DES private-key algorithms; and the MD5 hash function. Web pages using the SSL protocol start with HTTPs. SSL 3.0 and its successor, the Transaction Layer Security (TLS) 1.0 protocol, are de facto standards, but they do not provide the end-to-end capabilities of SET. TLS implements confidentiality, integrity, and authentication above the Transport Layer, and it resides between the application and TCP layer. Thus, TLS, as with SSL, can be used with applications such as Telnet, FTP, HTTP, and e-mail protocols. Both SSL and TLS use certificates for public-key verification that are based on the X.509 standard.
Internet Open Trading Protocol (IOTP)
IOTP is an Internet protocol that is aimed at the consumer-to-business transactions. It provides a buyer with the same options as in the ordinary, non–e-commerce marketplace. IOTP is similar to shopping in the real world because it gives buyers the option to choose their method of payment. It supports public and private encryption key algorithms and can use digital certificates. IOTP is designed to be flexible and to accommodate other payment models that may emerge in the future.
MONDEX
The MONDEX International Corporation operates the MONDEX payment system. This system is an example of a cash smart card application. The value of the amount of currency is stored in smart cards and a proprietary encryption algorithm provides security. Because the algorithm is not subject to public scrutiny, its strength and vulnerabilities are not known. The smart card, then, can be used in financial transactions instead of cash. Funds can be transferred among cards by using digital signatures. The smart cards are designed to preclude tampering and modifying the stored currency amount. However, if a card is lost, the finder can use it as cash.
IPSec
IPSec is a standard that provides encryption, access control, non-repudiation, and authentication of messages over IP. It is designed to be functionally compatible with IPv6. The two main protocols of IPSec are the Authentication Header (AH) and the Encapsulating Security Payload (ESP). The AH provides integrity, authentication, and non-repudiation. An ESP primarily provides encryption, but it can also provide limited authentication.
At the heart of IPSec is the Security Association (SA). An SA is required for communication between two entities. It provides a one-way (simplex) connection and is comprised of a Security Parameter Index (SPI), destination IP address, and the identity of the security protocol (AH or ESP). The SPI is a 32-bit number that is used to distinguish among various SAs terminating at the receiving station. Because an SA is simplex, two SAs are required for bidirectional communication between entities. Thus, if the AH protocol is used and bidirectional communication is required, two SAs must be established. Similarly, if both the AH and ESP protocols are to be employed bidirectionally, four SAs are needed.
IPSec in a VPN implementation can operate in either the transport or tunnel modes. In the transport mode, the data in the IP packet is encrypted, but the header is not encrypted. In the tunnel mode, the original IP header is encrypted and a new IP header is added to the beginning of the packet. This additional IP header has the address of the VPN gateway, and the encrypted IP header points to the final destination on the internal network behind the gateway.
The hashing algorithms HMAC-MD5 and HMAC-SHA-1 are used for authentication and integrity, and the IPSEC standard enables the use of a variety of symmetric-key systems.
Security Associations (SAs) can be combined into bundles to provide authentication, confidentiality, and layered communication. An SA bundle can be developed by using transport adjacency or iterated tunneling. Transport adjacency uses the transport mode for communication, whereas iterated tunneling provides for multiple levels of encapsulation as the protocol stack is being traversed.
In order to set up and manage SAs on the Internet, a standard format called the Internet Security Association and Key Management Protocol (ISAKMP) was established. ISAKMP provides for secure key exchange and data authentication. However, ISAKMP is independent of the authentication protocols, security protocols, and encryption algorithms. Strictly speaking, a combination of three protocols is used to define the key management for IPSec. These protocols are ISAKMP, Secure Key Exchange Mechanism (SKEME), and Oakley. When combined and applied to IPSEC, these protocols are called the Internet Key Exchange (IKE) protocol. In general, ISAKMP defines the phases for establishing a secure relationship, SKEME describes a secure exchange mechanism, and Oakley defines the modes of operation needed to establish a secure connection.
An initiative to specify a standard IPSEC implementation for VPNs on the Internet is known as Secure Wide Area Network (S/WAN). By defining a common set of IPSEC algorithms and modes of operation, S/WAN promotes the widespread use of VPNs on the Internet.
Secure Hypertext Transfer Protocol (S HTTP)
S-HTTP is an alternative to SSL for providing security for World Wide Web (WWW) transactions. While SSL is applied to an entire session, S-HTTP can be used to protect individual WWW documents, and it provides authentication, confidentiality, integrity, and non-repudiation. S-HTTP supports a variety of encryption algorithms.
Secure Shell (SSH 2)
Secure Shell (SSH-2) is a set of protocols that are primarily used for remote access over a network by establishing an encrypted tunnel between an SSH client and an SSH server. This protocol can be used to authenticate the client to the server. In addition, it can also provide confidentiality and integrity services. It is comprised of a Transport Layer protocol, a User Authentication protocol, and a Connection protocol.
Wireless Security
With the increasing use and popularity of Personal Digital Assistants (PDAs) and cellular telephones to access the Internet, wireless security is becoming very important. Because information is broadcast like radio transmissions, it is susceptible to interception and can be compromised. As storage and processor technologies improve, Mobile Commerce (M-commerce) will be more common. Issues that are associated with wireless security include:
- Physical security of wireless devices
- Proliferation of many different platforms
- Protection of sensitive financial transactions
- Limitations of processing power and memory due to space and weight considerations
- No standard method for securing wireless transactions
- Public Key Infrastructure (PKI)
Wireless Application Protocol (WAP)
The Wireless Application Protocol (WAP) is widely used by mobile devices to access the Internet. Because it is aimed at small displays and systems with limited bandwidth, it is not designed to display large volumes of data. In addition to cellular phones and PDAs, WAP is applied to network browsing through TV and in automotive displays. It has analogies to TCP/IP, IP, and HTML in wired Internet connections and is actually a set of protocols that cover Layer 7 to Layer 3 of the OSI model. Due to the memory and processor limitations on mobile devices, WAP requires less overhead than TCP/IP. The WAP protocol stack contains the following:
- Wireless Markup Language (WML) and Script
- Wireless Application Environment (WAE)
- Wireless Session Protocol (WSP)
- Wireless Transaction Protocol (WTP)
- Wireless Transport Layer Security Protocol (WTLS)
- Wireless Datagram Protocol (WDP)
For wireless security, WAP uses the Wireless Transport Layer Security Protocol (WTLS). WTLS provides the following three classes of security:
- Class 1 (Anonymous Authentication). The client logs on to the server, but in this mode, neither the client nor the server can be certain of the identity of the other.
- Class 2 (Server Authentication). The server is authenticated to the client, but the client is not authenticated to the server.
- Class 3 (Two-Way Client and Server Authentication). The server is authenticated to the client and the client is authenticated to the server.
Authentication and authorization can be performed on the mobile device by using smart cards to execute PKI-enabled transactions.
A specific security issue that is associated with WAP is the WAP GAP. A WAP GAP results from the requirement to change security protocols at the carrier’s WAP gateway from the wireless WTLS to SSL for use over the wired network. At the WAP gateway, the transmission, which is protected by WTLS, is decrypted and then re-encrypted for transmission by using SSL. Thus, the data is temporarily in the clear on the gateway and can be compromised if the gateway is not adequately protected. In order to address this issue, the WAP Forum has put forth specifications that will reduce this vulnerability and thus support e-commerce applications. These specifications are defined in WAP 1.2 as WMLScript Crypto Library and the WAP Identity Module (WIM). The WMLScript Crypto Library supports end-to-end security by providing for cryptographic functions to be initiated on the WAP client from the Internet content server. These functions include digital signatures originating with the WAP client and the encryption and decryption of data. The WIM is a tamper-resistant device, such as a smart card, that cooperates with WTLS and provides cryptographic operations during the handshake phase.
The WAP Forum is also considering another alternative to providing end-to-end encryption for WAP. This alternative, described in WAP specification 1.3, is the use of a client proxy server that communicates authentication and authorization information to the wireless network server.
The Handheld Device Markup Language (HDML) is a simpler alternative to WML that actually preceded the Wireless Markup Language (WML). HDML contains minimal security features, however. A direct competitor to WAP is Compact HTML (C-HTML). Used primarily in Japan through NTT DoCoMo’s I-mode service, C-HTML is essentially a stripped-down version of HTML. Due to this approach, C-HTML can be displayed on a standard Internet browser.
The Public Key Infrastructure (PKI) for mobile applications provides for the encryption of communications and mutual authentication of the user and application provider. One concern associated with the mobile PKI relates to the possible time lapse between the expiration of a public-key certificate and the reissuing of a new valid certificate and associated public key.
This “dead time” may be critical in disasters or in time-sensitive situations. One solution to this problem is to generate one-time keys for use in each transaction.
The IEEE 802 11 Wireless Standard
The IEEE 802.11 is a family of standard specifications that identify an over-the-air interface among a mobile device, wireless client, and base station and between mobile clients. Work on the standard began in 1990, and it has evolved from various draft versions.
The standard comprises a number of specifications, including the following principle ones:
- 802.11
- 802.11a
- 802.11b
- 802.11g
- 802.11e
- 802.11d
- 802.11h
- 802. 11n
802.11 is the original IEEE wireless LAN standard. The IEEE 802.11 standard places specifications on the parameters of both the physical (PHY) and medium access control (MAC) layers of the network. The PHY Layer is responsible for the transmission of data among nodes. It can use direct sequence (DS) spread spectrum, frequency-hopping (FH) spread spectrum, or infrared (IR) pulse position modulation. The standard supports data rates of 1 Mbps or 2 Mbps in the 2.4–2.4835 GHz frequency band for spread-spectrum transmission, and 300,000–428,000 GHz for IR transmission. Infrared is generally considered to be more secure against eavesdropping than multi-directional radio transmissions because infrared requires direct line-of-sight paths.
The MAC Layer is a set of protocols responsible for maintaining order in the use of a shared medium. The 802.11 standard specifies a carrier sense multiple access with collision avoidance (CSMA/CA) protocol for LANs, as described in Chapter 3. The MAC Layer provides the following services:
- Data transfer. CSMA/CA media access.
- Association. Establishment of wireless links between wireless clients and access points in infrastructure networks.
- Reassociation. This action takes place in addition to association when a wireless client moves from one Basic Service Set (BSS) to another, such as in roaming.
- Authentication. The process of proving a client’s identity through the use of the 802.11 option, Wired Equivalent Privacy (WEP). In WEP, a shared key is configured into the access point and its wireless clients. Only those devices with a valid shared key will be allowed to be associated to the access point.
- Privacy. In the 802.11 standard, data is transferred in the clear by default. If confidentiality is desired, the WEP option encrypts data before it is sent wirelessly. The WEP algorithm of the 802.11 Wireless LAN Standard uses a secret key that is shared between a mobile station (for example, a laptop with a wireless Ethernet card) and a base station access point to protect the confidentiality of information being transmitted on the LAN. The transmitted packets are encrypted with a secret key and an Integrity Check (IC) field comprised of a CRC-32 checksum that is attached to the message. WEP uses the RC4 variable key-size stream cipher encryption algorithm. RC4 was developed in 1987 by Ron Rivest and operates in output feedback mode.
Researchers at the University of California at Berkeley (wep@isaac.cs.berkeley.edu) have found that the security of the WEP algorithm can be compromised, particularly with the following attacks:
- Passive attacks to decrypt traffic based on statistical analysis
- Active attacks to inject new traffic from unauthorized mobile stations based on known plaintext
- Active attacks to decrypt traffic based on tricking the access point
- Dictionary-building attacks that, after an analysis of about a day’s worth of traffic, allow real-time automated decryption of all traffic
The Berkeley researchers have found that these attacks are effective against both the 40-bit and the so-called 128-bit versions of WEP using inexpensive off-the-shelf equipment. These attacks can also be used against networks that use the 802.11b Standard, which is the extension to 802.11 that supports higher data rates but does not change the WEP algorithm.
The IEEE 802.11i Working Group has addressed the weaknesses in WEP and 802.11. WEP has been upgraded to WEP2 with the following changes:
- Modifying the method of creating the initialization vector (IV)
- Modifying the method of creating the encryption key
- Protecting against replays
- Protecting against IV collision attacks
- Protecting against forged packets
The Advanced Encryption Standard (AES) will replace the RC4 encryption algorithm originally used in WEP.
Two power modes are defined in the IEEE 802.11 standard: an active mode used in transmitting and receiving, and a power save mode that conserves power but does not enable the user to transmit or receive.
Standard 802.11b is an extension to 802.11. It provides an 11 Mbps data rate but slows down to 5.5, 2, or 1 Mbps, depending upon the strength of the signal. The 802.11b standard operates in the 2.4 GHz band and is referred to as 802.11 high rate or WI-FI (wireless fidelity). Specification 802.11a was developed as an extension to 802.11b and provides up to 54 Mbps in the 5 GHz band. Specification 802.11g provides 20 Mbps to 54 Mbps transmission rates and operates in the 2.4 GHz band. Standard 802.11e focuses on interoperability among home, business, and public environments and provides for quality of service and multimedia services. 802.11e is designed to support video on demand, audio on demand, voice over IP (VOIP), and high speed Internet communications. 802.11d is a supplement to 802.11 that adds requirements and definitions that support the operation of 802.11 in additional regulatory domains. 802.11h enhances current 802.11a PHY and 802.11 MAC and provides transmit power management and spectrum extensions in the European 5 GHz band. Specification 802.11n is targeted at providing higher throughput (>100Mbps) to the 802.11 standard.
Assessment Questions
You can find the answers to the following questions in Appendix A.
|
1. |
The Secure Hash Algorithm (SHA) is specified in the:
|
|
|
2. |
What does Secure Sockets Layer (SSL)/Transaction Security Layer (TSL) do?
|
|
|
3. |
What are MD4 and MD5?
|
|
|
4. |
Elliptic curves, which are applied to public-key cryptography, employ modular exponentiation, which characterizes the:
|
|
|
5. |
Which algorithm is used in the Clipper Chip?
|
|
|
6. |
The hashing algorithm in the Digital Signature Standard (DSS) generates a message digest of:
|
|
|
7. |
The protocol of the Wireless Application Protocol (WAP), which performs functions similar to SSL in the TCP/IP protocol stack, is called the:
|
|
|
8. |
A Security Parameter Index (SPI) and the identity of the security protocol (AH or ESP) are the components of:
|
|
|
9. |
When two different keys encrypt a plaintext message into the same ciphertext, this situation is known as:
|
|
|
10. |
What is the result of the Exclusive Or operation, 1 XOR 0?
|
|
|
11. |
A block cipher:
|
|
|
12. |
In most security protocols that support confidentiality, integrity, and authentication:
|
|
|
13. |
Which of the following is an example of a symmetric-key algorithm?
|
|
|
14. |
Which of the following is a problem with symmetric-key encryption?
|
|
|
15. |
Which of the following is an example of an asymmetric-key algorithm?
|
|
|
16. |
In public-key cryptography:
|
|
|
17. |
In a hybrid cryptographic system, usually:
|
|
|
18. |
What is the block length of the Rijndael Cipher?
|
|
|
19. |
A polyalphabetic cipher is also known as:
|
|
|
20. |
The classic Caesar cipher is a:
|
|
|
21. |
In steganography:
|
|
|
22. |
What is the key length of the Rijndael Block Cipher?
|
|
|
23. |
In a block cipher, diffusion:
|
|
|
24. |
The NIST Advanced Encryption Standard uses the:
|
|
|
25. |
The modes of DES do not include:
|
|
|
26. |
Which of the following is true?
|
|
|
27. |
The Rijndael Cipher employs a round transformation that is composed of three layers of distinct, invertible transformations. These transformations are also defined as uniform, which means that every bit of the State is treated the same. Which of the following is not one of these layers?
|
|
|
28. |
The Escrowed Encryption Standard describes the:
|
|
|
29. |
Theoretically, quantum computing offers the possibility of factoring the products of large prime numbers and calculating discrete logarithms in polynomial time. These calculations can be accomplished in such a compressed time frame because:
|
|
|
30. |
Which of the following characteristics does a one-time pad have if used properly?
|
|
|
31. |
The DES key is:
|
|
|
32. |
In a digitally signed message transmission using a hash function:
|
|
|
33. |
The strength of RSA public-key encryption is based on the:
|
|
|
34. |
Elliptic curve cryptosystems:
|
|
|
35. |
Which of the following is not a fundamental component of Identity-Based Encryption (IBE)?
|
|
Answers
|
1. |
Answer: b The correct answer is b. Answer a refers to DES, a symmetric encryption algorithm; answer c is a distracter - there is no such term; answer d is the Advanced Encryption Standard, which has replaced DES and is now the Rijndael algorithm. |
|
2. |
Answer: a The correct answer is a by definition. Answer b is incorrect because SSL/TLS operates above the Transport Layer; answer c is incorrect because authentication and integrity are provided also, and answer d is incorrect because it cites only confidentiality and SSL/TLS operates above the Transport Layer. |
|
3. |
Answer: c The correct answer is c. Answers a and b are incorrect because they are general types of encryption systems, and answer d is incorrect because hashing algorithms are not digital certificates. |
|
4. |
Answer: a The correct answer is a. Modular exponentiation in elliptic curves is the analog of the modular discrete logarithm problem. Answer b is incorrect because prime factors are involved with RSA public-key systems; answer c is incorrect because modular addition in elliptic curves is the analog of modular multiplication; and answer d is incorrect because the knapsack problem is not an elliptic curve problem. |
|
5. |
Answer: c The correct answer is c. Answers a, b, and d are other symmetric-key algorithms. |
|
6. |
Answer: b |
|
7. |
Answer: d The answer d is correct. SSL performs security functions in TCP/IP. The other answers refer to protocols in the WAP protocol stack also, but their primary functions are not security. |
|
8. |
Answer: b The correct answer is b. The SPI, AH and/or ESP, and the destination IP address are components of an IPSec Security Association (SA). The other answers describe protocols other than IPSec. |
|
9. |
Answer: c The answer c is correct. Answer a describes a type of cryptographic system using a public and a private key; answer b is the art/science of breaking ciphers; answer d is the conversion of a message of variable length into a fixed-length message digest. |
|
10. |
Answer: a An XOR operation results in a 0 if the two input bits are identical and a 1 if one of the bits is a 1 and the other is a 0. |
|
11. |
Answer: d The answer d is correct. Answer a describes a stream cipher; answer b is incorrect because a block cipher applies to symmetric-key algorithms; and answer c describes a hashing operation. |
|
12. |
Answer: a The answer a is correct. Answer b is incorrect because private-key cryptography does not create digital signatures; answer c is incorrect because DES is a private-key system and, therefore, follows the same logic as in b; and answer d is incorrect because digital signatures are implemented to obtain authentication and integrity. |
|
13. |
Answer: a The correct answer is a. The other answers are examples of asymmetric-key systems. |
|
14. |
Answer: d The answer d is correct. Answer a is incorrect because the opposite is true; answer b is incorrect because most symmetric-key algorithms are published; and answer c is incorrect because work factor is a function of key size. The larger the key is, the larger the work factor. |
|
15. |
Answer: d The answer d is correct. All the other answers refer to symmetric-key algorithms. |
|
16. |
Answer: d The answer d is correct. Answers a and b are incorrect because if one key encrypts, the other can decrypt. Answer c is incorrect because if the public key encrypts, it cannot decrypt. |
|
17. |
Answer: b The answer b is correct. Answer a is incorrect because public-key cryptography is usually used for the encryption and transmission of the secret session key. Answer c is incorrect because both public- and private-key encryption are used, and answer d is incorrect because digital certificates can be used (and normally are used). |
|
18. |
Answer: c The correct answer is c. The other answers with fixed numbers are incorrect. |
|
19. |
Answer: b The answer b is correct. Answer a is incorrect because a one-time pad uses a random key with length equal to the plaintext message and is used only once. Answer c is the process of sending a message with no indication that a message even exists. Answer d is incorrect because it applies to stream ciphers that are XORed with a random key string. |
|
20. |
Answer: b The answer b is correct. The Caesar cipher uses one alphabet shifted three places. Answers a and c are incorrect because in a polyalphabetic cipher (answer a), multiple alphabets are used, and in a transposition cipher (answer c), the letters of the message are transposed. Answer d is incorrect because code groups deal with words and phrases and ciphers deal with bits or letters. |
|
21. |
Answer: d The correct answer is d. The other answers are incorrect because neither algorithm is used. |
|
22. |
Answer: c |
|
23. |
Answer: b The answer b is correct. Answer a defines confusion; answer c defines how confusion is accomplished; and answer d is incorrect because it can be accomplished. |
|
24. |
Answer: b The correct answer is b. By definition, the others are incorrect. |
|
25. |
Answer: c The correct answer is c. There is no such encipherment mode. |
|
26. |
Answer: c The answer c is correct. The Meet-in-the-Middle attack has been successfully applied to double DES, and the work factor is equivalent to that of single DES. Thus, answer d is incorrect. Answer a is false because the work factor of triple DES is greater than that for double DES. In triple DES, three levels of encryption and/or decryption are applied to the message. The work factor of double DES is equivalent to the work factor of single DES. Answer b is false because the work factor of single DES is less than for triple DES. |
|
27. |
Answer: d The answer d is correct. This answer is a distracter and does not exist. |
|
28. |
Answer: b |
|
29. |
Answer: b In digital computers, a bit is in either a one or a zero state. In a quantum computer, through linear superposition, a quantum bit can be in both states, essentially simultaneously. Thus, computations consisting of trial evaluations of binary patterns can take place simultaneously in exponential time. The probability of obtaining a correct result is increased through a phenomenon called constructive interference of light, while the probability of obtaining an incorrect result is decreased through destructive interference. Answer a describes optical computing that is effective in applying Fourier and other transformations to data to perform high-speed computations. Light representing large volumes of data passing through properly shaped physical objects can be subjected to mathematical transformations and recombined to provide the appropriate results. However, this mode of computation is not defined as quantum computing. Answers c and d are diversionary answers that do not describe quantum computing. |
|
30. |
Answer: c If the one-time-pad is used only once and its corresponding key is truly random and does not have repeating characters, it is unbreakable. Answer a is incorrect because if used properly, the one-time-pad should be used only once. Answer b is incorrect because the key should be random. Answer d is incorrect because the key has to be of the same length as the message. |
|
31. |
Answer: c |
|
32. |
Answer: a The hash function generates a message digest. The message digest is encrypted with the private key of the sender. Thus, if the message can be opened with the sender’s public key, which is known to all, the message must have come from the sender. The message is not encrypted with the public key because the message is usually longer than the message digest and would take more computing resources to encrypt and decrypt. Because the message digest uniquely characterizes the message, it can be used to verify the identity of the sender. Answers b and d will not work because a message encrypted in the public key of the sender can be read only by using the private key of the sender. Because the sender is the only one who knows this key, no one else can read the message. Answer c is incorrect because the message is not encrypted; the message digest is encrypted. |
|
33. |
Answer: d The correct answer is d. Answer a applies to public-key algorithms such as Diffie-Hellman and Elliptic Curve. Answer b is incorrect because it is easy to multiply two large prime numbers. Answer c refers to symmetric-key encryption. |
|
34. |
Answer: a It is more difficult to compute elliptic curve discrete logarithms than conventional discrete logarithms or factoring. Smaller key sizes in the elliptic curve implementation can yield higher levels of security. Therefore, answer b is incorrect. Answers c and d are incorrect because elliptic curve cryptosystems can be used for digital signatures and encryption. |
|
35. |
Answer: d IBE is based on using an arbitrary string as an individual’s public key. It is based on public-key cryptography; therefore, a symmetric key is not involved in the process. |
Part One - Focused Review of the CISSP Ten Domains
- Information Security and Risk Management
- Access Control
- Telecommunications and Network Security
- Cryptography
- Security Architecture and Design
- Operations Security
- Application Security
- Business Continuity Planning and Disaster Recovery Planning
- Legal, Regulations, Compliance, and Investigations
- Physical (Environmental) Security
Part Two - The Certification and Accreditation Professional (CAP) Credential
- Understanding Certification and Accreditation
- Initiation of the System Authorization Process
- The Certification Phase
- The Accreditation Phase
- Continuous Monitoring Process
- Appendix A Answers to Assessment Questions
- Appendix B Glossary of Terms and Acronyms
- Appendix C The Information System Security Architecture Professional (ISSAP) Certification
- Appendix D The Information System Security Engineering Professional (ISSEP) Certification
- Appendix E The Information System Security Management Professional (ISSMP) Certification
- Appendix F Security Control Catalog
- Appendix G Control Baselines
EAN: 2147483647
Pages: 239
 Open table as spreadsheet
Open table as spreadsheet
