Address Translation
You can configure address translation under Configuration > Features > NAT. ASDM allows both dynamic and static NAT/PAT for either all or selected hosts on the inside and the outside networks. Click Add to define a new NAT/PAT policy in the Add Address Translation Rule window. As shown in Figure 19-6, ASDM is identifying the inside network of 192.168.10.0/24 for address translation.
Figure 19-6. Defining a NAT/PAT Policy
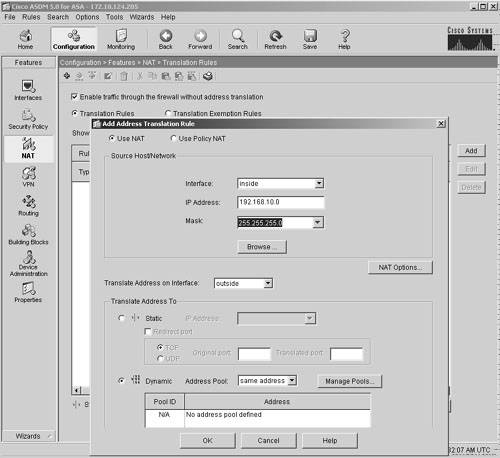
In Figure 9-6, the administrator has also checked the Enable Traffic Through the Firewall Without Address Translation window. This option appears in the main window under Configuration > Features and NAT. This option allows traffic that does not match any NAT policy to pass through the security Cisco ASA without changing the source or destination addresses. However, the packets that match the NAT/PAT policies are translated.
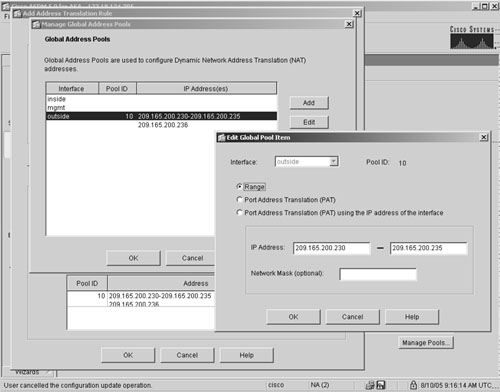
SecureMe, a fictitious company, wants to dynamically translate the inside 192.168.10.0/24 network from a pool of public addresses. Click Manage Pools to define a new pool of IP addresses, as shown in Figure 19-7. Because the inside hosts will be translated to the outside network, select the outside interface and click Add to add a range of IP addresses from 209.165.200.230 to 209.165.200.235 to be mapped to a pool ID of 10. The 209.165.200.236 address is used for PAT if all the other addresses have been assigned. Click OK to finish the setup.
Figure 19-7. Defining a Pool of Addresses
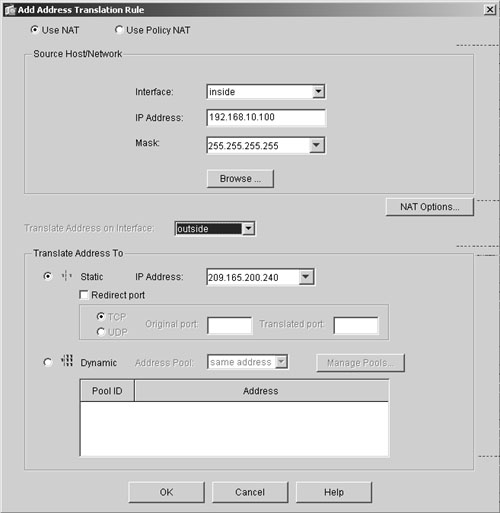
If you need to configure static NAT, click the Static radio button in the Add Address Translation Rule window and specify the translated address in the IP Address box, as shown in Figure 19-8, in which an inside host, 192.168.10.100, is being translated to 209.165.200.240.
Figure 19-8. Static Address Translation
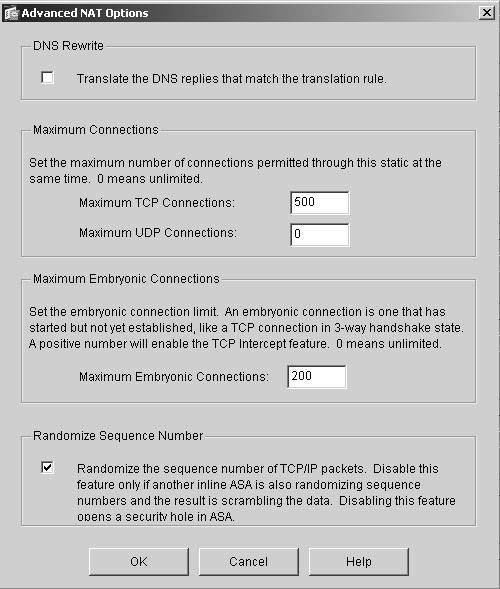
To configure DNS Doctoring and the maximum connection limits, discussed in Chapter 5, click NAT Options in the Add Address Translation Rule window to open the Advanced NAT Options window, shown in Figure 19-9. In this case, the administrator has restricted the maximum TCP-based connections to not exceed 500 for the static entry created in the previous step. The maximum embryonic connection limit is 200, and Cisco ASA is being set up to randomize the sequence numbers in the TCP packets.
Figure 19-9. Setting the TCP-Based and Embryonic Connection Limits
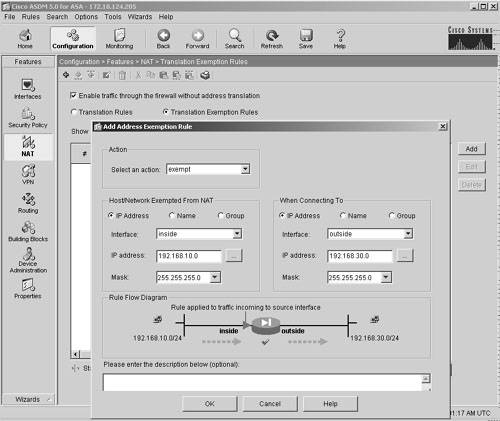
ASDM also supports NAT exemption policies to bypass address translation. You configure these policies under Configuration > Features > NAT > Translation Exemption Rules, as shown in Figure 19-10. This process is important if packets are traversing over a site-to-site VPN tunnel and do not need to be translated. In Figure 19-10, if packets are sourced from 192.168.10.0/24 and destined for 192.168.30.0/24, the security Cisco ASA will not translate them.
Figure 19-10. Setting Translation Exemption Rules
Note
For NAT order of operation, consult Chapter 5.
Example 19-3 shows the relevant configuration generated by ASDM for address translation.
Example 19-3. Address Translation Configuration Generated by ASDM
access-list inside_nat0_outbound line 1 extended permit ip 192.168.10.0 255.255.255.0 192.168.30.0 255.255.255.0 nat (inside) 0 access-list inside_nat0_outbound static (inside,outside) 209.165.200.240 192.168.10.100 netmask 255.255.255.255 tcp 500 200 udp 0 no nat-control nat (inside) 10 192.168.10.0 255.255.255.0 tcp 0 0 udp 0 global (outside) 10 209.165.200.230-209.165.200.235 global (outside) 10 209.165.200.236
Part I: Product Overview
Introduction to Network Security
- Introduction to Network Security
- Firewall Technologies
- Intrusion Detection and Prevention Technologies
- Network-Based Attacks
- Virtual Private Networks
- Summary
Product History
- Product History
- Cisco Firewall Products
- Cisco IDS Products
- Cisco VPN Products
- Cisco ASA All-in-One Solution
- Summary
Hardware Overview
Part II: Firewall Solution
Initial Setup and System Maintenance
- Initial Setup and System Maintenance
- Accessing the Cisco ASA Appliances
- Managing Licenses
- Initial Setup
- IP Version 6
- Setting Up the System Clock
- Configuration Management
- Remote System Management
- System Maintenance
- System Monitoring
- Summary
Network Access Control
- Network Access Control
- Packet Filtering
- Advanced ACL Features
- Content and URL Filtering
- Deployment Scenarios Using ACLs
- Monitoring Network Access Control
- Understanding Address Translation
- DNS Doctoring
- Monitoring Address Translations
- Summary
IP Routing
Authentication, Authorization, and Accounting (AAA)
- Authentication, Authorization, and Accounting (AAA)
- AAA Protocols and Services Supported by Cisco ASA
- Defining an Authentication Server
- Configuring Authentication of Administrative Sessions
- Authenticating Firewall Sessions (Cut-Through Proxy Feature)
- Configuring Authorization
- Configuring Accounting
- Deployment Scenarios
- Troubleshooting AAA
- Summary
Application Inspection
- Application Inspection
- Enabling Application Inspection Using the Modular Policy Framework
- Selective Inspection
- Computer Telephony Interface Quick Buffer Encoding Inspection
- Domain Name System
- Extended Simple Mail Transfer Protocol
- File Transfer Protocol
- General Packet Radio Service Tunneling Protocol
- H.323
- HTTP
- ICMP
- ILS
- MGCP
- NetBIOS
- PPTP
- Sun RPC
- RSH
- RTSP
- SIP
- Skinny
- SNMP
- SQL*Net
- TFTP
- XDMCP
- Deployment Scenarios
- Summary
Security Contexts
- Security Contexts
- Architectural Overview
- Configuration of Security Contexts
- Deployment Scenarios
- Monitoring and Troubleshooting the Security Contexts
- Summary
Transparent Firewalls
- Transparent Firewalls
- Architectural Overview
- Transparent Firewalls and VPNs
- Configuration of Transparent Firewall
- Deployment Scenarios
- Monitoring and Troubleshooting the Transparent Firewall
- Summary
Failover and Redundancy
- Failover and Redundancy
- Architectural Overview
- Failover Configuration
- Deployment Scenarios
- Monitoring and Troubleshooting Failovers
- Summary
Quality of Service
- Quality of Service
- Architectural Overview
- Configuring Quality of Service
- QoS Deployment Scenarios
- Monitoring QoS
- Summary
Part III: Intrusion Prevention System (IPS) Solution
Intrusion Prevention System Integration
- Intrusion Prevention System Integration
- Adaptive Inspection Prevention Security Services Module Overview (AIP-SSM)
- Directing Traffic to the AIP-SSM
- AIP-SSM Module Software Recovery
- Additional IPS Features
- Summary
Configuring and Troubleshooting Cisco IPS Software via CLI
- Configuring and Troubleshooting Cisco IPS Software via CLI
- Cisco IPS Software Architecture
- Introduction to the CIPS 5.x Command-Line Interface
- User Administration
- AIP-SSM Maintenance
- Advanced Features and Configuration
- Summary
Part IV: Virtual Private Network (VPN) Solution
Site-to-Site IPSec VPNs
- Site-to-Site IPSec VPNs
- Preconfiguration Checklist
- Configuration Steps
- Advanced Features
- Optional Commands
- Deployment Scenarios
- Monitoring and Troubleshooting Site-to-Site IPSec VPNs
- Summary
Remote Access VPN
- Remote Access VPN
- Cisco IPSec Remote Access VPN Solution
- Advanced Cisco IPSec VPN Features
- Deployment Scenarios of Cisco IPSec VPN
- Monitoring and Troubleshooting Cisco Remote Access VPN
- Cisco WebVPN Solution
- Advanced WebVPN Features
- Deployment Scenarios of WebVPN
- Monitoring and Troubleshooting WebVPN
- Summary
Public Key Infrastructure (PKI)
- Public Key Infrastructure (PKI)
- Introduction to PKI
- Enrolling the Cisco ASA to a CA Using SCEP
- Manual (Cut-and-Paste) Enrollment
- Configuring CRL Options
- Configuring IPSec Site-to-Site Tunnels Using Certificates
- Configuring the Cisco ASA to Accept Remote-Access VPN Clients Using Certificates
- Troubleshooting PKI
- Summary
Part V: Adaptive Security Device Manager
Introduction to ASDM
- Introduction to ASDM
- Setting Up ASDM
- Initial Setup
- Functional Screens
- Interface Management
- System Clock
- Configuration Management
- Remote System Management
- System Maintenance
- System Monitoring
- Summary
Firewall Management Using ASDM
- Firewall Management Using ASDM
- Access Control Lists
- Address Translation
- Routing Protocols
- AAA
- Application Inspection
- Security Contexts
- Transparent Firewalls
- Failover
- QoS
- Summary
IPS Management Using ASDM
- IPS Management Using ASDM
- Accessing the IPS Device Management Console from ASDM
- Configuring Basic AIP-SSM Settings
- Advanced IPS Configuration and Monitoring Using ASDM
- Summary
VPN Management Using ASDM
- VPN Management Using ASDM
- Site-to-Site VPN Setup Using Preshared Keys
- Site-to-Site VPN Setup Using PKI
- Cisco Remote-Access IPSec VPN Setup
- WebVPN
- VPN Monitoring
- Summary
Case Studies
EAN: 2147483647
Pages: 231
