How Phishing Works
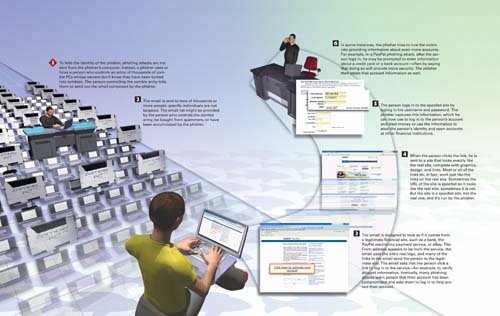 |
How Personal & Internet Security Works
ISBN: 0789735539
EAN: 2147483647
EAN: 2147483647
Year: 2004
Pages: 161
Pages: 161
Authors: Preston Gralla
- Measuring and Managing E-Business Initiatives Through the Balanced Scorecard
- A View on Knowledge Management: Utilizing a Balanced Scorecard Methodology for Analyzing Knowledge Metrics
- Measuring ROI in E-Commerce Applications: Analysis to Action
- Managing IT Functions
- Governance in IT Outsourcing Partnerships