Putting Together a Toolkit
The tools we are about to discuss have been arranged into a logical order. Assessments usually follow a well-defined methodology. That is the focus hereto step you through the process and briefly discuss some of the tools that can be used at each particular step. The tools are divided into the following categories:
- Information-gathering tools and techniques
- Scanning tools
- Enumeration tools
- Wireless tools
- Password auditing tools
- Vulnerability scanning tools
- Automated exploit tools
Note
Remember that tools come and go, but the methodology of an assessment stays the same. Some of these tools are free, such as Nmap and SuperScan, whereas others, such as L0phtcrack and LANguard, must be purchased.
Information-Gathering Tools and Techniques
This first step of the assessment is about discovery: How much information is exposed to outsiders and what is its potential damage? One of the best tools you can use at this step of the engagement is your brain. This step is all about old-fashioned detective work. Before you fire off a single port scanner or ping sweep, you'll want to start here and see what the rest of the world may already know.
Begin with the organization's website. It's surprising what type of information can be found there. Email addresses, employee names, organization locations, and technologies are just a few of the items you may dig up. Spend a little time and use a site ripper like Blackwidow Pro or Wget to pull down the contents of the site. Again, you may be surprised at what you find. While you quest for information, also check out SiteDigger. Foundstone developed this tool to automatically scan websites and report security vulnerabilities available via public search engines. It's possible to uncover additional amounts of sensitive information that should not be publicly available with this tool. The biggest drawback is that it's structured around Google's API; you'll be limited to 1,000 searches per day.
On the subject of manipulating Google searches, you should also check out the Google Hacking Guide by Johnny Long; his website is at http://johnny.ihackstuff.com. It offers insight into some of the ways you can easily find exploitable targets and sensitive data by using Google's built-in functionality. Google commands such as intitle instruct Google to search for a term within the title of a document; others, like filetype, allow individuals to search only within the text of a particular type of file.
Next, take a look at the IANA/ARIN/RIPE databases. You can manually step through this process or use one of the many websites set up for this purpose, including dnsstuff.com, centralops.net, all-nettools.com, and geektools.com. Many organizations have removed names and other information from these databases. but sometimes you still get lucky.
It's sad but true that not everyone in an organization may be happy about his or her current status. Offshoring, outsourcing, and reductions in force can add to individuals' frustrations. These unhappy individuals are also potential sources of information leakage. This information may be posted on a blog, some type of "sucks" domain, or other site. Shown in Figure 8.1 is the stinky gateway domain that was up for a while before Gateway computer corporation found out and requested that the former employee remove it.
Figure 8.1. Stinky Gateway site.

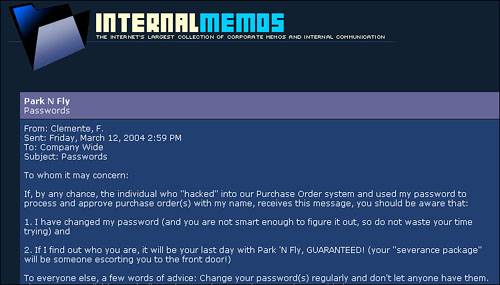
Frustrated employees will always find some way to vent their thoughts, even if not from a "sucks" domain. One such site that may offer other insider information is internalmemos.com. This site lists information that is usually sensitive and probably shouldn't be released to the world. Although some of the content is free, other content is considered premium and must be purchased to be viewed. A sample shot of the site is shown in Figure 8.2. Don't be surprised if you find some of your company's memos there!
Figure 8.2. Internalmemos.com.
With some basic information gathering completed, we can move on to more in-depth techniques. In the following sections we will discuss scanning tools, enumeration tools, wireless tools, password auditing tools, vulnerability scanning tools, and automated exploit tools. Combined, these will provide you with most of what is needed for a level II or level III assessment.
Scanning Tools
With the basic information gathering out of the way, it's time to start getting interactive. At this phase of an assessment, you are looking for active machines and networks. No matter which tools you use, activity here can be boiled down to three steps:
- The first step is network discovery. Network discovery tools use ICMP ECHO_REQUEST/REPLY packets to see if a target is live. If ping hasn't been blocked, it can reveal which machines are active on the network.
- The second step is port scanning. Ports are tied to services and as such, provide a list of what potential applications are active. Ports are placed into TCP and UDP packets so the correct application can be passed to the required protocols. Although applications can be made to operate on nonstandard ports, the established port numbers serve as the de facto standard. Although there are approximately 65,000 ports, they are divided into well-known ports (0-1024), registered ports (1024-49151), and dynamic ports (49152-65535).
Just finding an open port in no way means that vulnerability has been found. Further analysis must be performed to pry additional information from the server. Port-scanning programs typically manipulate the TCP handshake process to find out what's really running on that open port. These techniques can include the following:
- TCP SYN scan This half-open scan was developed to evade IDS systems, although most now detect it. Open ports reply with a SYN/ACK, whereas closed ports respond with a RST/ACK.
- TCP FIN scan Forget trying to set up a connection; this technique jumps straight to the shutdown. This type of scan sends a FIN packet to the target port. Closed ports should send back a RST. This technique is effective on Unix devices.
- TCP NULL scan Sure, there should be some type of flag in the packet but a NULL scan sends a packet with no flags set. Closed ports should return a RST.
- TCP ACK scan This scan attempts to determine rulesets or identify whether stateless inspection is being used. If an ICMP destination unreachable message is returned, the port is considered to be filtered.
- TCP XMAS scan Sorry, no Christmas presents here, just a port scan that has toggled on the FIN, URG, and PSH flags. Closed ports should return a RST.
- TCP SYN scan This half-open scan was developed to evade IDS systems, although most now detect it. Open ports reply with a SYN/ACK, whereas closed ports respond with a RST/ACK.
- The third step is OS identification. Tools that fingerprint the OS can be passive or active. Passive tools sniff network traffic and make a determination of what type of OS is generating the traffic. Passive identification requires a large amount of traffic but offers a level of stealth that is lacking in active tools. Active fingerprinting tools can be very accurate but can easily be detected by IDS systems. Active fingerprinting tools can craft packets and probe for responses by using the following:
- The FIN bit
- Various TTL options
- The TCP Win Size
- The Don't Fragment (DF) setting in the IP header
- Manipulating TOS settings
Each of the scanning tools is covered in detail next.
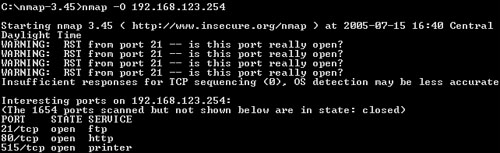
Nmap
Nmap (as shown in Figure 8.3) was developed by a hacker named Fyodor Yarochkin. This popular application is available for Windows and Linux as a GUI and command-line program. It is probably the most widely used port scanner ever developed. It can do many type of scans and OS identification. It also has the capability to do blind scanning, zombie scanning, and allows you to control the speed of the scan from slow to insane. Its popularity can be seen by the fact that it's incorporated into other products and was even used in the movie Matrix.
Figure 8.3. Nmap
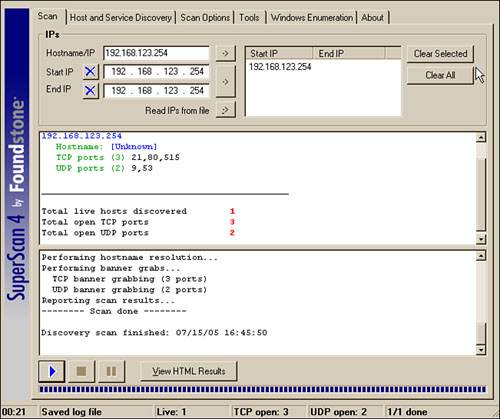
SuperScan
SuperScan is a Windows GUI-based scanner developed by Foundstone. It will scan TCP and UDP ports and perform ping scans. It will allow you to scan all ports, use a built-in list of defined ports, or specify the port range. As far as the price, it's free and offers great features if you are looking for a Windows GUI scanner. It's shown in Figure 8.4.
Figure 8.4. SuperScan
Scanrand
Scanrand is part of a suit of tools known as Paketto Keiretsu developed by Dan Kaminsky. Scanrand is a fast scanning tool. What makes this tool so fast is that it uses a unique method of scanning TCP ports. Most TCP scanners take the approach of scanning one port at a time. After all, TCP is a stateful protocol, so traditional scanners must probe each port, wait for the response, store the connection in memory, then move on. Traditional scanning is a serial process.
Scanrand implements stateless scanning. This parallel approach to scanning breaks the process into two distinct processes. One process sends out the requests at a high rate of speed while the other independent process is left to sort out all the incoming responses and figure out how it all matches up. The secret to the program's speed is in its use of something called inverse SYN cookies. Basically, Scanrand builds a hashed sequence number that is placed in the outgoing packet that can be identified upon return. This value contains information that identifies source IP, source port, destination IP, and destination port. If you're tasked with scanning a large number of IP addresses quickly, this is something you'll want to check out.
Xprobe2
Xprobe 2 is an active operating system fingerprinting tool with a different approach to operating system fingerprinting. Xprobe2 relies on fuzzy signature matching. In layman's terms, this means that targets are run through a variety of tests. These results are totaled and the user is presented with a score that tells the probability of the targeted machine's OSfor example, 75% Windows XP and 60% Windows 2000. Xprobe is also unique in that it uses a mixture of TCP, UDP, and ICMP to slip past firewalls and avoid IDS systems.
THC-Amap
THC-Amap is another example of scanning and banner grabbing. One problem that traditional scanning programs have is that not all services are ready and eager to give up the appropriate banner. For example, some services, such as SSL, expect a handshake. Amap handles this by storing a collection of responses that it can fire off at the port to interactively elicit it to respond. Another is that scanning programs sometimes make basic assumptions that might be flawed. Many port scanners assume that if a particular port is open, the default application for that port must be present. Amap probes these ports to find out what is really running there. Therefore, this tool excels at allowing a security professional to find services that may have been redirected from their standard ports. One of the ways to use this program is by taking the greppable format of nmap as an input to scan for those open services. Defeating or blocking Amap is not easy, although one technique would be to use a port knocking technique.
Want to Know More?
If, after this brief introduction to these tools, you would like to learn more, the best place to start is the vendors' websites. These URLs are provided next, as are several URLs that discuss port knocking and passive fingerprinting in-depth.
Port scanning basics www.garykessler.net/library/is_tools_scan.html
Passive fingerprinting http://project.honeynet.org/papers/finger/
Nmap www.insecure.org
SuperScan www.foundstone.com/resources/freetools.htm
Scanrand www.lurhq.com/scanrand_dissected.pdf
Xprobe www.net-security.org/article.php?id=540
TCH-Amap http://thc.org/thc-amap/
Port Knocking www.portknocking.org
Enumeration Tools
Enumeration is the process of gathering information from a system without logging on. It can be seen as an extension of the scanning process. Information that can be obtained from enumeration includes the following:
- Usernames
- Open shares
- Active Directory information
- Router information
- Device information
Although not all the tools and techniques are guaranteed to produce results, it is worth the time to investigate each of them. Services that can be used to target and enumerate Linux include finger, SNMP, SMTP, RPC, and TFTP. Many of the techniques used to target Windows rely on the weaknesses of the null session. The null session is the result of the Windows IPC$ (InterProcess Communications) share. This default share can be found on Windows NT, 2000, and XP. The purpose of the IPC$ share is to handle communication between applications located on one machine or distributed between two or more systems. There is quite a bit of information that can be leaked by probing this process. This can be done with an array of tools or manually by executing the following command:
C:>net use \targetipc$ "" /u:""
You'll be happy to know that there are ways to lock down the IPC$ share, which is what Microsoft attempted to do in Windows 2003 when it changed the default restrict anonymous setting. Linux can also be subjected to this type of enumeration if Samba is being used. Table 8.1 will give you some idea of what type of information can be extracted from the system running the default settings.
|
Operating System |
Enumerate Shares |
Enumerate Usernames |
Enumerate SIDs |
Enumerate Running Services |
|---|---|---|---|---|
|
Windows 2003 and XP |
Yes |
Yes |
Yes |
No |
|
Windows 2000 |
Yes |
Yes |
Yes |
No |
|
Windows NT |
Yes |
Yes |
Yes |
Yes |
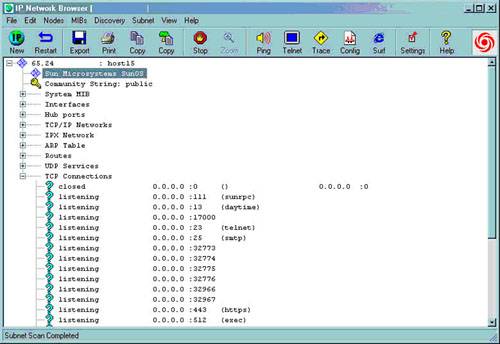
SolarWinds IP Network Browser
Following is a technique that you would expect to fail, but we have been amazed at the number of times we have seen this tool enumerate information that shouldn't be available. SolarWinds IP Network Browser is a tool that probes Simple Network Management Protocol (SNMP) communication. SNMP version 3 offers data encryption and authentication, although version one, which is a clear text protocol, is still widely used. The key to SNMP is the community strings. SNMP uses both public and private community strings. Therefore, if they have not been changed or if they have and someone can sniff the traffic, they can then launch this tool effectively. Although the tool is not free, you can download a demo from the solarwinds.net website. A screen shot is shown in Figure 8.5.
Figure 8.5. SolarWinds SNMP enumeration.
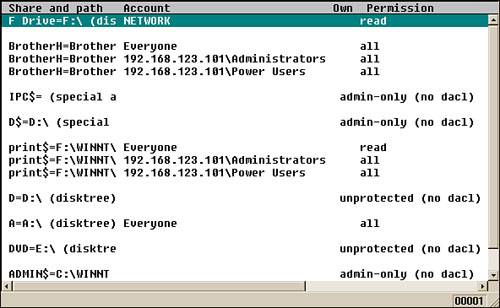
DumpSec
DumpSec is a Windows-based tool from SomarSoft. It allows you to remotely connect to Windows machines and dump account details, share permissions, and user information. It is shown in Figure 8.6. Its GUI-based format makes it easy to take the results and port them into a spreadsheet so that holes in system security are readily apparent and easily tracked.
Figure 8.6. DumpSec Enumeration tool.
USE42
USE42 is a combination of three existing tools combined into a Windows GUI program. USE42 includes NBTscan, IPEye, and Enum. This combination of tools enables you to obtain a list of NETBIOS names, portscan a range of devices, pull down password policies, user account information, group information, and share details on Windows computers.
Want to Know More?
If, after this brief introduction to these tools, you would like to learn more, the best place to start is the vendors' websites. You can download the tools there as well as gather more information. Their URLs follow:
Windows Enumeration http://www.sans.org/rr/whitepapers/windows/286.php
SolarWinds www.solarwinds.com
DumpSec www.somarsoft.com
USE42 www.inetcat.org/software
Wireless Tools
802.11 wireless connectivity is probably something you are going to want to look at during the assessment. Even if your organization is not officially using wireless, you will want to make sure that there are not any rouge wireless access points. Wireless networks have become popular because of their low cost and convenience. It's so much easier to plug in a wireless access point (WAP) than to run 1,000 feet of cable. Unfortunately, many end users who are moving to wireless still don't have any appreciation of the security measures they should employ.
Originally, 802.11 wireless was protected with Wired Equivalent Privacy (WEP). WEP encrypts data with the RC4 encryption algorithm. The key was limited to 40 bits. This provides a very limited level of encryption that is relatively easy to compromise. This weakness led to several changes in the industry. First, many WAPs began incorporating 802.1x into many wireless devices. 802.1x provides port-based access control. Second, the industry released WiFi Protected Access (WPA). WPA is much more secure because it uses Temporal Key Integrity Protocol (TKIP). In 2004, the IEEE approved the next upgrade to wireless security, which was WPA2. It is officially known as 802.11.i. This wireless security standard makes use of the Advanced Encryption Standard (AES). WAPs can now be found with key sizes of up to 256 bits, which is a vast improvement from the original 40-bit encryption WEP used. Now that you are primed to perform a wireless assessment, you'll need a few items for the task:
- Software Discussed in the sections that follow. A nice collection is available on the Linux Auditor distribution.
- Wireless card Prism and Orinoco chipsets offer the most compatibility with existing software.
- External antenna You don't really want to go around holding that laptop over your head, do you? One popular choice is the cantenna from cantenna.com.
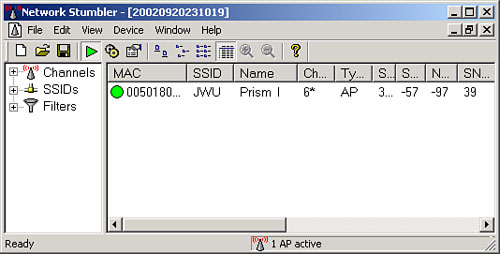
NetStumbler
NetStumbler is a Windows-based GUI tool that acts as a wireless scanner. It operates by sending out a steady stream of broadcast packets on all channels. It's useful for checking the coverage of an organization's wireless LAN. A screenshot is shown in Figure 8.7. It displays signal strength, MAC addresses, SSID, and integrates with GPS systems to facilitate mapping. MiniStumbler is a version of the software that is available for handhelds.
Figure 8.7. NetStumbler wireless capture.
Kismet
Kismet is a Linux-based 802.11 wireless sniffer that can monitor and sniff raw packets from wireless networks. Kismet can detect standard and hidden network names and doesn't analyze beaconing hidden networks. Kismet is useful for detecting rogue access points and can be used for site surveys.
LinkFerret
If you're looking for a Windows tool to handle a similar task, you'll want to consider LinkFerret. This commercial 802.11 network monitor and packet sniffer can also detect rogue assess points, provide signal monitoring for site surveys, and can perform WEP decryption. LinkFerret is an easy-to-use tool that will pay for itself very quickly.
WEP Cracking
If you are interested in cracking WEP and would like to see how strong the keys are, you'll want to consider the following tools. If the access point is vulnerable to this type of attack, you may be able to crack the WEP keys in a very short period of time. The tools are shown in their order of use:
- Airodump This program scans a wireless network for packets and captures these packets into files.
- Void11 This program will deauthenticate wireless clients from the wireless access point and force them to reassociate to the AP, creating many ARP requests.
- Aireplay This program takes ARP requests generated by VOID11 and resends it to the AP, spoofing the ARP request from the valid wireless client.
- Aircrack Takes the captured files generated by airodump and extracts the WEP key.
Want to Know More?
If, after this brief introduction to these tools, you would like to learn more, the best place to start is the vendors' websites. You can download the tools there as well as gather more information. Their URLs are provided next. The first link in the list provides some useful information about cracking WEP.
Cracking WEP www.tomsnetworking.com/Sections-article120-page1.php
Auditor http://new.remote-exploit.org/index.php/Auditor_tools
NetStumbler www.netstumbler.org
Kismet www.kismetwireless.net
LinkFerret www.linkferret.ws
Aircrack www.cr0.net:8040/code/network/
Password Auditing Tools
Password auditing tools can test the strength of your passwords in one of three ways: dictionary, hybrid, and brute force attacks.
- Dictionary password cracking pulls words from a dictionary or word list to attempt to discover a user's password. A dictionary attack uses a predefined dictionary to look for a match between the encrypted password and the encrypted dictionary word. Many times, dictionary password audits will recover a user's password in a very short period of time. If passwords are well-known, dictionary-based words, dictionary tools will crack them quickly.
- A hybrid attack uses a dictionary or word list, then prepends and appends characters and numbers to dictionary words in an attempt to crack the user's password. These programs are comparatively smart because they can manipulate a word and use its variations. For example, take the word "password." A hybrid password audit would attempt variations such as 123password, abcpassword, drowssap, p@ssword, pa44w0rd, and so on. These various approaches increase the odds of successfully cracking an ordinary word that has had a little variation added in.
- Brute force attacks use random numbers and characters to crack a user's password. A brute-force audit on an encrypted password may take hours, days, months, or years, depending on the complexity and length of the password. The speed of success here will be dependent on the speed of the CPU's power. Brute force audits attempt every combination of letters, numbers, and characters.
Historically, the preceding three approaches were the primary methods that someone would use to test the strength of a password or attempt to crack it. Some passwords were considered secure because of the time it would take to crack them. The time factor was what made these passwords seem secure. Sure, it could be cracked, but who is going to spend a month trying. This theory no longer holds completely true. A relative new approach is to use a rainbow table. The RainbowCrack technique is the implementation of Philippe Oechslin's faster time-memory trade-off technique. It works by precomputing all possible passwords in advance. Once this time-consuming process is complete, the passwords and their corresponding encrypted values are stored in a file called the rainbow table. An encrypted password can be quickly compared to the values stored in the table and cracked within a few seconds. This should drive home the point that you should:
- Select and configure strong network authentication protocols.
- Protect password databases.
- Have a strong password policy, enforce it, and schedule awareness training and password audits.
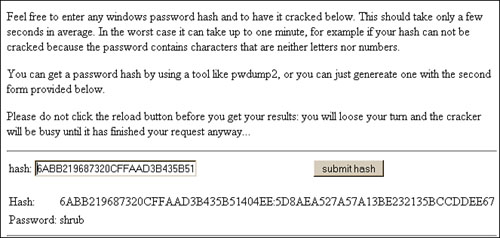
Ophcrack
Ophcrack is a password cracking tool that implements the rainbow table techniques previously discussed. It has several tables that can be downloaded, or you can search the Web for others. What's most important to note here is that if a password is in the table, it will be cracked quickly. Their website also lets you enter a hash and reveal the password in just a few seconds. An example of this is shown in Figure 8.8.
Figure 8.8. Ophcrack online password cracking.
John the Ripper
John the Ripper is a great password auditing tool. It is available for 11 types of Unix systems plus Windows. It can crack most common passwords, including Kerberos AFS and Windows NT/2000/XP/2003 LM hashes. There is also a large amount of add-on modules available for John that can allow it to crack OpenVMS passwords, Windows credentials cache, and MySQL passwords.
L0phtCrack
L0phtcrack was released way back in 1997 and became famous as the premiere Windows password cracking tool. Symantec now owns the rights to this tool, but it continues to be improved. LC5 is the current version. It can extract hashes from the local machine, a remote machine, and can sniff passwords from the local network.
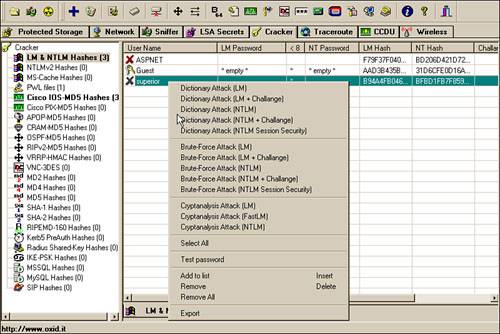
Cain
Cain is a multipurpose tool that has the capability to perform a variety of tasks, including Windows enumeration, sniffing, and password cracking. Cain is shown in Figure 8.9. The password-cracking portion of the program can perform dictionary and brute force attacks and can use precomputer hash tables.
Figure 8.9. Cain password cracking.
Want to Know More?
If, after this brief introduction to these tools, you would like to learn more, the best place to start is the vendors' websites. You can download the tools there as well as gather more information at
Rainbow tables www.antsight.com/zsl/rainbowcrack
Ophcrack http://lasecwww.epfl.ch/~oechslin/projects/ophcrack/
John the Ripper www.openwall.com/john
Cain and Abel www.oxid.it
Vulnerability Scanning Tools
You'll find that there is no shortage of vulnerability assessment tools on the market. These tools can be used to scan internal or external computers for vulnerabilities. Some of these tools are commercial and may require an annual subscription, whereas others are open source and won't cost you anything to initially acquire. All of these tools can be broken into three basic categories:
- Source code scanners examine the source code of an application.
- Application scanners examine a specific application or type of application.
- System scanners examine entire systems or networks for configuration or application-level problems.
Source Code Scanners
Source code scanners can be used to assist in auditing security problems in source code. Many of these tools are available for free; Rough Auditing Tool for Security (RATS) and FlawFinder are two such tools. Source code scanners can detect problems such as buffer overflows, race conditions, privilege escalation, and tainted input. Buffer overflows allow data to be written over portions of your executable, which can allow a malicious user to do just about anything. Race conditions can prevent protective systems from functioning properly or deny the availability of resources to their rightful users. Privilege escalation occurs when code runs with higher privileges than that of the user who executed it. Tainting of input allows potentially unchecked data through your defenses, possibly qualified as already-error-checked information.
Application-Level Scanners
Application-level scanners are the next type of vulnerability scanner we will examine. Application scanners provide testing against completed applications or components rather than the source code. They scan applications for vulnerabilities that occur at runtime and they test such issues as user input and bounds testing. Application-level scanners aren't just useful for security testing either; the amount of time that you can save by using automated bounds-testing software and the like can be amazing. AppDetective is an example of one of these programs. AppDetective scans, locates, examines, reports, and fixes security holes and misconfigurations in database applications.
System-Level Scanners
The final category of scanners is system-level scanners, which are intended for probing systems and their components rather than individual applications. The scanners can be run against a single address or a range of addresses and can also test the effectiveness of layered security measures, such as a system running behind a firewall. Nessus is an example of a well-known system-level scanner.
The primary advantage of system-level scanners is that they can probe entire local or remote systems or networks for a variety of vulnerabilities. If you need to test a large number of installations, remote system-level scanners can be far more efficient than auditing the configuration of each machine individually. System scanners do have their disadvantages as well. For example, it is not possible to audit the source of the processes that are providing services. Additionally, scanning results have to rely on the responses of a service to a finite number of probes, meaning that all possible inputs cannot be reasonably tested. If the production environment of your organization is experiencing services unexpectedly coming online or going offline, you might run a system scanner to see if the cause of the problem can be detected. In another example, if the target system has been patched or experienced other recent upgrades, you might run a system scanner to double-check everything.
Probably most important, system scanners do not substitute for more thorough measures in that they are a part of the vulnerability assessment process, but not the sole component. They are intended to supplement other measures, such as secure architecture and design practices and decisions. Source code and application scanning should also be done where applicable. An in-depth vulnerability assessment consists of all the components we have discussed: information gathering, wireless surveys, password audits, source code scanners, application-level scanners, and system-level scanners. None can be substituted for another component.
Nessus
Nessus is an open source, comprehensive cross-platform vulnerability scanner with CLI and GUI interfaces. Nessus has a client/server architecture, with clients available for Unix, Linux, and Windows and servers available for Unix, Linux, and Windows (commercial). Nessus is a powerful, flexible security scanning and auditing tool. It takes a basic "nothing for granted" approach. For example, an open port does not necessarily mean that a service is active. Nessus tells you what is wrong and provides suggestions for fixing a given problem. It also supports many types of plug-ins, which range from harmless to those that can bring down a server. The plug-in menu is shown in Figure 8.10.
Figure 8.10. Nessus plug-ins.

SAINT
SAINT is a commercial application from Saint Corporation, providing industry respected vulnerability scanning and identification. It has a web-based interface and the deployment platforms for this product are Linux and Unix. It is certified CVE-compliant and allows you to prioritize and rank vulnerabilities to determine which critical security issues you should tackle first.
ISS Internet Scanner
ISS Internet Scanner is one of the products available from Internet Security Systems. Its deployment platform is Windows NT/2000/XP/2003. The package provides extensive vulnerability scanning and identification across network platforms and devices via CLI and GUI interfaces. It can identify more than 1,300 types of networked devices. After these devices have been scanned and identified, Internet Scanner can analyze their configuration, patch levels, operating systems, and installed applications. Then it can generate a report identifying vulnerabilities.
NetRecon
NetRecon is a commercial scanner produced by Symantec. It provides vulnerability scanning and identification with a unique, "cooperative" approach. NetRecon actually learns about the network as it scans it. If it finds and cracks a password on one machine, that password will be tried on others. The application has a GUI interface and its deployment platform is Windows NT/2000.
Retina
Retina is a commercial product from eEye Digital Security. It provides "gentle" vulnerability scanning across systems and network devices. Not only can it scan a class C network in about 20 minutes, it also discovers devices through wired and wireless connections. Retina has a GUI interface and its deployment platform is Windows NT/2000/XP/2003.
Security Auditor's Research Assistant (SARA)
SARA is a CLI and web-based GUI freeware application. Instead of inventing a new module for every conceivable action, SARA is adapted to interface to other open source products. For example, SARA works with NMAP and SAMBA to perform OS fingerprinting and SMB security analysis. It's considered a gentle scanner. The term gentle means that the scan does not present a risk to the operating network infrastructure. It's compliant with SANS Top 20, supports CVE references for identified vulnerabilities, and can be deployed on Unix, Linux, and Mac OS X.
Other Choices
A host of other scanners are available. Several are mentioned next:
- VLAD An open source vulnerability scanner. Written in Perl, VLAD is designed to identify vulnerabilities in the SANS Top 10 list.
- N-Stealth Another vulnerability assessment product that specifically scans web servers to identify security problems and weaknesses that might allow an attacker to gain privileged access.
- LANguard A full service scanner that reports information such as the service pack level of each machine, missing security patches, open shares, open ports, services/application active on the computer, key Registry entries, weak passwords, users and groups, and more.
Want to Know More?
If, after this brief introduction to these tools, you would like to learn more, the best place to start is the vendors' websites. You can download the tools there as well as gather more information. Their URLs follow:
Nessus www.nessus.org
SAINT www.saintcorporation.com
ISS Internet Scanner www.iss.net
NetRecon www.symantec.com
Retina www.eeye.com
SARA www.arc.com
VLAD www.bindview.com
Automated Exploit and Assessment Tools
If the tools you've seen so far have piqued your interest, you're bound to find the next three tools very interesting. These tools represent where vulnerability assessment tools are headed. Tools such as Nessus and others have had the capability to integrate scanning, assessing, and reporting functions. The tools described in the following sections take this functionality to the next step by tightly integrating the capability to exploit a suspected vulnerability.
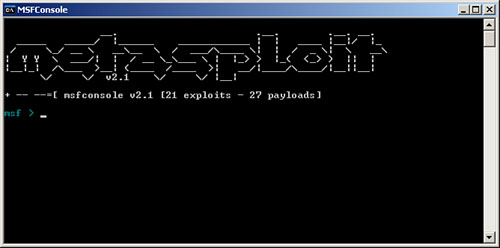
Metasploit
Metasploit is an all-in-one exploit testing and development tool. Metasploit allows you to enter an IP address and port number of a targeted machine and run the chosen exploit against the targeted machine quite easily. This is an open source tool that can be compared to CANVAS and Core IMPACT. Metasploit was developed using Perl, C, and Python. It is available for Linux and Windows and is shown in Figure 8.11. It can have the victim connect back to you, open a command shell on the victim, or allow you to execute code on the victim.
Figure 8.11. Metasploit demo.
CANVAS
CANVAS is a tool developed by Dave Aitel of Immunity.com. It was written in Python so it is portable to Windows and Linux. It's a commercial tool that can provide the security professional with attack and penetration capabilities. Like Metasploit, it is not a complete all-in-one tool. It does not do an initial discovery, so you must add your targets manually. It's cleaner and more advanced than Metasploit but requires you to purchase a license. This does, however, provide you with updates and support. Overall, this is a first-rate tool for someone with penetration and assessment experience.
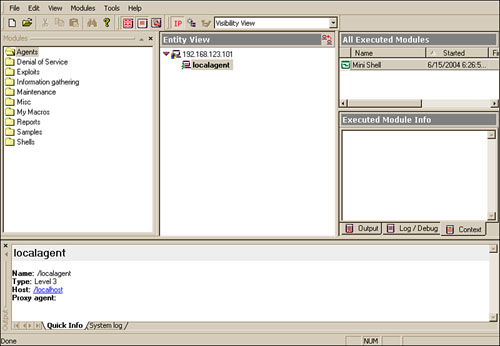
Core IMPACT
This is by far the most advanced of the three tools discussed here. Core IMPACT is a mature point-and-click automated exploit and assessment tool. It's a complete package that steps the user through the process starting at scanning and continuing through the exploit and control phase. One of its unique features is that it supports a feature known as pivoting. Basically, pivoting allows a compromised machine to be used to compromise another. This tool is useful for everyone from the novice to the seasoned security professional. Take a look at the interface shown in Figure 8.12.
Figure 8.12. IMPACT target assessment.
Want to Know More?
If after this brief introduction to these tools you would like to learn more the best place to start is the vendors website. You can download the tool there as well as gather more information at:
Metasploit www.metasploit.com
CANVAS www.immunitysec.com/products-canvas.shtml
Core IMPACT www.coresecurity.com
Introduction to Assessing Network Vulnerabilities
- Introduction to Assessing Network Vulnerabilities
- What Security Is and Isnt
- Process for Assessing Risk
- Four Ways in Which You Can Respond to Risk
- Network Vulnerability Assessment
Foundations and Principles of Security
- Foundations and Principles of Security
- Basic Security Principles
- Security Requires Information Classification
- The Policy Framework
- The Role Authentication, Authorization, and Accountability Play in a Secure Organization
- Encryption
- Security and the Employee (Social Engineering)
Why Risk Assessment
- Why Risk Assessment
- Risk Terminology
- Laws, Mandates, and Regulations
- Risk Assessment Best Practices
- Understanding the IT Security Process
- The Goals and Objectives of a Risk Assessment
Risk-Assessment Methodologies
- Risk-Assessment Methodologies
- Risk-Assessment Terminology
- Quantitative and Qualitative Risk-Assessment Approaches
- Best Practices for Quantitative and Qualitative Risk Assessment
- Choosing the Best Risk-Assessment Approach
- Common Risk-Assessment Methodologies and Templates
Scoping the Project
- Scoping the Project
- Defining the Scope of the Assessment
- Reviewing Critical Systems and Information
- Compiling the Needed Documentation
- Making Sure You Are Ready to Begin
Understanding the Attacker
- Understanding the Attacker
- Who Are the Attackers?
- What Do Attackers Do?
- Reducing the Risk of an Attack
- How to Respond to an Attack
Performing the Assessment
- Performing the Assessment
- Introducing the Assessment Process
- Level I Assessments
- Level II Assessments
- Level III Assessments
Tools Used for Assessments and Evaluations
- Tools Used for Assessments and Evaluations
- A Brief History of Security Tools
- Putting Together a Toolkit
- Determining What Tools to Use
Preparing the Final Report
- Preparing the Final Report
- Preparing for Analysis
- Ranking Your Findings
- Building the Final Report
- Contents of a Good Report
- Determining the Next Step
- Audit and Compliance
Post-Assessment Activities
- Post-Assessment Activities
- IT Security Architecture and Framework
- Roles, Responsibilities, and Accountabilities
- Security Incident Response Team (SIRT)
- Vulnerability Management
- Training IT Staff and End Users
Appendix A. Security Assessment Resources
Appendix B. Security Assessment Forms
- Information Request Form
- Document Tracking Form
- Critical Systems and Information Forms
- Level II Assessment Forms
Appendix C. Security Assessment Sample Report
- Appendix C. Security Assessment Sample Report
- Notice
- Executive Summary
- Statement of Work
- Analysis
- Recommendations
- Conclusions
Appendix D. Dealing with Consultants and Outside Vendors
- Appendix D. Dealing with Consultants and Outside Vendors
- Procurement Terminology
- Typical RFP Procurement Steps
- Procurement Best Practices
Appendix E. SIRT Team Report Format Template
EAN: 2147483647
Pages: 138
