Router Deployment Scenarios
Cisco VPN capabilities have their roots in Cisco IOS-based routers, where VPNs were first introduced in the Cisco router line. Cisco routers support many VPN solutions including IPsec, PPTP, L2TP, and WebVPN (in the newest IOS versions). Because of their flexibility, routers can be used in many different situations. This section will focus on how routers can be used with L2L and remote access VPNs in your network, including the router's special advantages over other Cisco VPN products.
L2L and Remote Access Connections
Cisco routers support L2L and remote access connections. As mentioned in Chapter 8, "Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN," I prefer to use Cisco routers for L2L sessions, but concentrators for remote access sessions. Routers support enhanced routing, quality of service (QoS), and L2L scalability capabilities over Cisco PIX and ASA security appliances and VPN 3000 concentrators. However, concentrators scale better for remote access sessions and are easy to set up.
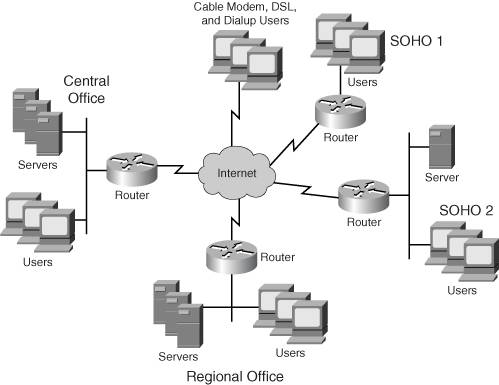
Figure 15-1 shows an example in which routers are being used to terminate VPN sessions. At the Central Office, a VPN-enabled router is used to terminate an L2L session from the Regional Office, and remote access sessions from the Cable Modem, DSL, and dial-up users, and the SOHO 1 and SOHO 2 sites. Because the number of remote access devices is small, it is more cost-effective to let the Central Office router terminate these versus buying an extra product such as a VPN 3000 series concentrator. Plus, because SOHO 2 has a server that the Central Office needs to access, the session can be set up using either remote access with network extension mode or as an L2L session.
Figure 15-1. Using Routers for VPN Solutions
Special Capabilities of Routers
As I mentioned in Chapter 8, I prefer (and Cisco recommends) to use routers for L2L sessions. I'm constantly asked why routers are better for this role than the VPN 3000 concentrators and the PIX and ASA security appliances. There are four main features the Cisco IOS-based routing products have over Cisco 3000 concentrators and PIX/ASA security appliances when it comes to VPN implementations: data transport, routing scalability, media translation, and quality of service (QoS). The next four sections will discuss these features in more depth.
Data Transport
Two limitations of IPsec for VPNs are that IPsec doesn't support IP multicasting and it doesn't support non-IP protocols such as IPX or AppleTalk. With a VPN 3000 concentrator or PIX or ASA security appliance, there's nothing you can do about these problems; however, Cisco routers can easily get around these two problems by encapsulating multicast or non-IP protocols using a GRE tunnel, and have the GRE tunnel go across a unicast IPsec sessionin other words, a tunnel (GRE) within a tunnel (IPsec). Using this approach, you can send IP multicast and broadcast traffic, including routing protocol and non-IP protocols, across an IPsec tunnel. See Chapter 1, "Overview of VPNs," for more information on GRE.
Routing Scalability
When I need to interconnect a large number of large sites, where each site has many networks connected to it, routers perform this task better than the other two products. With Cisco routers, I can use a feature called Dynamic Multipoint VPNs (DMVPNs) which simplifies the interconnection/meshing process and the routing function of learning about the destinations at each end of the tunnel (with a minimal configuration).
One problem with VPN 3000 concentrators is that you either do this manually with network lists and RRI, or automatically, with Network Auto Discovery. The problem with the latter approach is that it only works with RIP, and it requires that the two endpoints be concentrators. Cisco routers, on the other hand, support many IP routing protocols, such as RIP, IGRP, OSPF, IS-IS, EIGRP, and BGP.
With PIX and ASA security appliances, routing protocols are not supported across VPN tunnels (at least not until version 7.0) and therefore the routing must be done manually, which doesn't scale well when connecting a large number of sites, with each site having a large number of networks. As an example, if you need to connect three sites together, where each site has 100 networks, on each site's PIX or ASA, you would need to configure 200 networks for the 100 networks at each remote site. As you add more sites and more networks, managing the routing process becomes unmanageable.
Media Translation
A third advantage of Cisco routers is that they support a wide variety of media types, such as Ethernet, ATM, ISDN, DSL, Frame Relay, point-to-point serial links, and many others. Cisco VPN 3000 concentrators and PIX and ASA security appliances support only Ethernet-based connections. Therefore, if you only need one Layer-3 device at a small site, it makes no sense to buy two products to handle multiple functions such as terminating VPNs and firewalling, in addition to connecting to an ISP with a non-Ethernet connection. Instead, you could use a router to handle all of these functions.
Quality of Service
The fourth advantage that routers have over VPN 3000 concentrators and PIX and ASA security appliances is their support for sophisticated QoS features. For example, suppose you had implemented VoIP throughout your network in Figure 15-1. A Call Manager device is located at the Central Office and a hub-and-spoke design is used to interconnect the various users and sites (with the Central Office being the hub). Given this situation, you need to prioritize your VoIP traffic over your data traffic to ensure that phone communications receive the necessary bandwidth and minimal delay.
The problem of using a VPN 3000 concentrator for this process is that its bandwidth management features are applied to a VPN termination point, like a remote access user or an L2L session; it cannot prioritize the traffic that traverses the tunnel, like VoIP over data traffic. In 6.3 and earlier of the PIX operating system, there is no support for QoS (in Version 7, there is support for low-latency queuing (LLQ), which is used primarily for VoIP applications.
Cisco routers, when compared to the other Cisco VPN products, are feature-rich with QoS capabilities, and they do the following:
- Use and control resources efficiently
- Adapt QoS based on needs of specific groups, users, and/or applications
- Allow VoIP, mission-critical resources, and bandwidth-intensive applications to co-exist
With the Cisco QoS features, you can classify your traffic manually or dynamically based on issues such as bandwidth, delay, jitter, and data loss requirements. The Cisco router QoS capabilities allow you to avoid congestion problems, or, in a worse case, at least deal with congestion problems so that they don't create additional problems for VoIP and mission-critical resources.
Cisco QoS features implement some or all of the following functions to handle your QoS needs:
- Classifying traffic Sort traffic into different groups.
- Marking traffic Place marking information in a packet to indicate its class (priority).
- Policing traffic Compare received packets and determine whether they are following expected patterns concerning bandwidth, jitter, delay, packet loss, and so on, or are breaking a QoS policy (packets breaking a QoS policy are typically dropped but can be marked instead).
- Queuing packets Examine the classification of packets to determine how it should be placed in an egress queue before being transmitted out of the router.
- Scheduling Determine how queued traffic should be processed from the egress queue.
- Shaping traffic Send traffic out at a constant rate to remove the jitter from a traffic stream and enforce a bandwidth limit, which is important for VoIP and multimedia applications.
Cisco supports the following classification features:
- Policy-based routing (PBR)
- Priority queuing
- Custom queuing
- Committed access rate (CAR)
- Class-based policing
- Network-based application recognition (NBAR)
Cisco supports the following queuing implementations:
- First-in-first-out (FIFO)
- Class-based weighted-fair queuing (CB-WFQ)
- Custom queuing (CQ)
- Class-based low latency queuing (CB-LLQ)
- IP RTP prioritization (for multimedia applications)
- Weighted round-robin queuing (WRRQ)
- Priority queuing (PQ)
WFQ is the default for WAN interfaces that are E1 or smaller. WRRQ is used, by default, on the egress interfaces of Catalyst Layer-3 switches. It uses a queuing policy similar to PQ, except that it guarantees that no queue will ever be starved. LLQ is ideal for networks that need to transport both voice and data. It combines PQ and CB-WFQ.
Cisco supports the following congestion avoidance features:
- Tail dropping
- Weighted random early detection (WRED)
Of the two, WRED is the more sophisticated because it uses the markings in packets to determine what should be dropped, to avoid any congestion problems.
Note
This chapter will not cover any IOS QoS mechanism in depth. For a quick overview of IOS QoS mechanisms, please read Chapter 9 of my book entitled CCNP BCMSN Exam Cram 2 (642-811), Second Edition by Que Publishing (ISBN: 0789729911).
Part I: VPNs
Overview of VPNs
- Overview of VPNs
- Traffic Issues
- VPN Definition
- VPN Components
- VPN Designs
- VPN Implementations
- VPNs: Choosing a Solution
- Summary
VPN Technologies
IPsec
PPTP and L2TP
SSL VPNs
Part II: Concentrators
Concentrator Product Information
- Concentrator Product Information
- Concentrator Models
- Concentrator Modules
- Concentrator Features
- Introduction to Accessing a Concentrator
- Summary
Concentrator Remote Access Connections with IPsec
- Concentrator Remote Access Connections with IPsec
- Controlling Remote Access Sessions to the Concentrator
- IPsec Remote Access
- Network Access Control (NAC) for IPsec and L2TP/IPsec Users
- Summary
Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- Concentrator Remote Access Connections with PPTP, L2TP, and WebVPN
- PPTP and L2TP Remote Access
- WebVPN Remote Access
- Summary
Concentrator Site-to-Site Connections
- Concentrator Site-to-Site Connections
- L2L Connectivity Example
- ISAKMP/IKE Phase 1 Preparation
- Adding Site-to-Site Connections
- Address Translation and L2L Sessions
- Summary
Concentrator Management
- Concentrator Management
- Bandwidth Management
- Routing on the Concentrator
- Chassis Redundancy
- Administration Screens
- Summary
Verifying and Troubleshooting Concentrator Connections
- Verifying and Troubleshooting Concentrator Connections
- Concentrator Tools
- Troubleshooting Problems
- Summary
Part III: Clients
Cisco VPN Software Client
- Cisco VPN Software Client
- Cisco VPN Client Overview
- Cisco VPN Client Interface
- IPsec Connections
- VPN Client GUI Options
- VPN Client Software Updates
- VPN Client Troubleshooting
- Summary
Windows Software Client
- Windows Software Client
- Windows Client
- Configuring the Windows VPN Client
- Configuring the VPN 3000 Concentrator
- Microsoft Client Connections
- Troubleshooting VPN Connections
- Summary
3002 Hardware Client
- 3002 Hardware Client
- Overview of the 3002 Hardware Client
- Initial Access to the 3002
- Authentication and Connection Options
- Connection Modes
- Administrative Tasks
- Summary
Part IV: IOS Routers
Router Product Information
- Router Product Information
- Router Deployment Scenarios
- Router Product Overview
- Summary
Router ISAKMP/IKE Phase 1 Connectivity
- Router ISAKMP/IKE Phase 1 Connectivity
- IPsec Preparation
- ISAKMP/IKE Phase 1 Policies
- ISAKMP/IKE Phase 1 Device Authentication
- Monitoring and Managing Management Connections
- Routers as Certificate Authorities
- Summary
Router Site-to-Site Connections
- Router Site-to-Site Connections
- ISAKMP/IKE Phase 2 Configuration
- Viewing and Managing Connections
- Issues with Site-to-Site Connections
- Summary
Router Remote Access Connections
- Router Remote Access Connections
- Easy VPN Server
- Easy VPN Remote
- IPsec Remote Access and L2L Sessions on the Same Router
- WebVPN
- Summary
Troubleshooting Router Connections
- Troubleshooting Router Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- New IPsec Troubleshooting Features
- Fragmentation Problems
- Summary
Part V: PIX Firewalls
PIX and ASA Product Information
- PIX and ASA Product Information
- PIX Deployment Scenarios
- PIX and ASA Feature and Product Overview
- Summary
PIX and ASA Site-to-Site Connections
- PIX and ASA Site-to-Site Connections
- ISAKMP/IKE Phase 1 Management Connection
- ISAKMP/IKE Phase 2 Data Connections
- L2L Connection Examples
- Summary
PIX and ASA Remote Access Connections
- PIX and ASA Remote Access Connections
- Easy VPN Server Support for 6.x
- Easy VPN Remote Support for 6.x
- Easy VPN Server Support for 7.0
- Summary
Troubleshooting PIX and ASA Connections
- Troubleshooting PIX and ASA Connections
- ISAKMP/IKE Phase 1 Connections
- ISAKMP/IKE Phase 2 Connections
- Summary
Part VI: Case Study
Case Study
Index
EAN: 2147483647
Pages: 178
