Extended IP Access Lists
| Extended IP access lists provide far more flexibility in the specification of what is to be filtered. The basic syntax of the extended IP access list line follows: access-list access-list-number [dynamic dynamic-name [timeout minutes]] {deny | permit} protocol source source-wildcard destination destination-wildcard [precedence precedence] [tos tos] [log | log-input] [time-range time-range-name] [fragments] You can configure extended access-lists using the global access-list configuration mode in the same way it is done with standard lists. Sequence numbers can also be used with extended access lists. They are entered the same way as standard lists. Reflexive access lists can be configured only using the global access list configuration mode and can be configured only with named IP access lists. Reflexive access lists are discussed in a later section of this appendix. Some of the features here are familiar, and some are new:
A sample extended IP access list is displayed in Example B-12. Example B-12. An extended IP access list permits and denies packets in various ways.access-list 101 permit ip 172.22.30.6 0.0.0.0 10.0.0.0 0.255.255.255 time-range morning access-list 101 permit ip 172.22.30.95 0.0.0.0 10.11.12.0 0.0.0.255 access-list 101 deny ip 172.22.30.0 0.0.0.255 192.168.18.27 0.0.0.0 access-list 101 permit ip 172.22.0.0 0.0.31.255 192.168.18.0 0.0.0.255 access-list 101 deny ip 172.22.0.0 0.0.255.255 192.168.18.64 0.0.0.63 access-list 101 permit ip 0.0.0.0 255.255.255.255 0.0.0.0 255.255.255.255 time-range morning periodic weekdays 08:00 to 11:59 The following is an explanation of the lines in Example B-12:
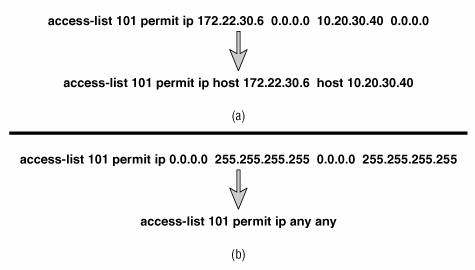
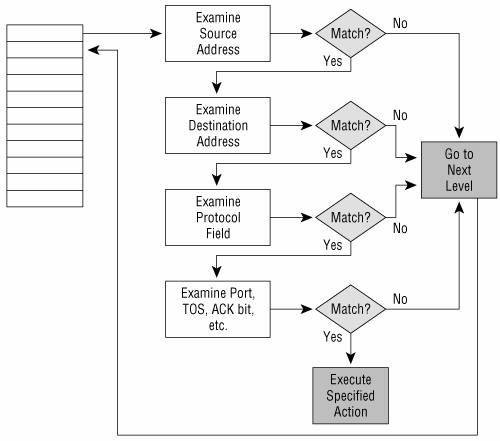
Figure B-7 shows two shortcuts that can be used when writing extended IP access lists. Recall that standard IP access lists have a default mask of 0.0.0.0. This default does not apply to extended access lists; there would be no way for the router to interpret it correctly. An alternative exists for extended lists, however. In Figure B-7(a), packets are permitted if their source is host 172.22.30.6 and their destination is host 10.20.30.40. Any time the mask in an extended IP access list is 0.0.0.0, it can be replaced by adding the keyword host before the address. Figure B-7. Two shortcuts can be used when writing extended IP access lists. The example in Figure B-7(b) permits any IP packets from any source to any destination. Just as with standard access lists, the any keyword can be used in place of the 0.0.0.0 255.255.255.255 address/inverse mask combination for the source, the destination, or both. Extended access lists can be more powerful than standard access lists because the former examine more than the packet's source address, but everything has a price. The price you pay with extended lists is increased processing (Figure B-8). Because each line of the access list is examining multiple fields within the packet, multiple CPU interrupts can occur. If the access list is large or the router is busy, this requirement can affect performance adversely. Figure B-8. The decision flow of an extended IP access list. Keeping access lists as small as possible reduces the processing burden on the router. Also notice that when a match occurs, the specified action is invoked and processing stops. Therefore, if you can write your lists so that most matches occur in the first few lines, performance will be improved. This approach isn't always feasible, but it is something to keep in mind when designing access lists. Some router platforms support a function called "Turbo ACLs," which are compiled access lists. The configured access lists are compiled into a lookup table. The sequence of the entries is maintained, but the lookup time and CPU required for lookup is greatly reduced. Certain entries, such as time ranges, cannot be included in a compiled list. To configure the router to use turbo access lists, enter the command access-list compiled. As an exercise, try making the access list given in Example B-12 more elegant. That is, rewrite the list with as few lines as possible without losing any of its functionality. (Hint: A list with the same functionality can be written with only four lines, not including the two time commands at the end.) An answer is given in the next paragraph. Try to rewrite the list before reading further. Line 1 can be removed. Line 1 permits host 172.22.30.6 access to the 10.0.0.0/8 address, during the weekday mornings. Without this line, access from this host to the 10.0.0.0 address is still permitted by line 6, which permits anything that is not previously denied. Line 2 can also be removed. The host 172.22.30.95 is also permitted access to 10.11.12.0/24 in line 6. You might be tempted to think that line 4 can also be removed, but notice that line 5 denies a larger range of addresses that includes those permitted in line 4. Therefore, line 4 is necessary to permit a small subset of addresses before the rest of the addresses specified in line 5 are dropped. TCP Access ListsThe syntax for an extended access list line that examines a TCP segment follows: access-list access-list-number [dynamic dynamic-name [timeout minutes]] {deny | permit} tcp source source-wildcard [operator [port]] destination destination-wildcard[operator [port]] [established] [precedence precedence] [tos tos] [log | log-input] [time-range time-range-name] [fragments] Notice that the protocol variable is tcp. Probably the most significant feature here is that the access list can examine the source and destination port numbers in the TCP segment header. As a result, you have the option of filtering packets not only to and from a particular address, but also to and from a particular socket (an IP address/application port combination). The features of the TCP access list that have not yet been explained are operator and port:
What happens if you implemented an access list to prevent TCP sessions from being established into your network, but you want to ensure that the access list passes the responses if your network establishes a TCP session? The established keyword allows this event by checking the ACK and RST flags in the TCP segment header. If one of these flags is set, a match occurs. If neither bit is set, the source is trying to establish a TCP connection to the destination, and a match will not occur. The packet will be denied on a subsequent line of the access list. A sample TCP access list is displayed in Example B-13. Example B-13. This TCP access list permits established sessions and permits certain addresses access for SMTP and Telnet.access-list 110 permit tcp any 172.22.0.0 0.0.255.255 established access-list 110 permit tcp any host 172.22.15.83 eq 25 access-list 110 permit tcp 10.0.0.0 0.255.255.255 172.22.114.0 0.0.0.255 eq 23 The following is an explanation of the lines in Example B-13:
All other packets will be dropped by the implicit deny any. UDP Access ListsThe syntax for an extended access list line that examines a UDP segment follows: access-list access-list-number [dynamic dynamic-name [timeout minutes]] {deny | permit} udp source source-wildcard [operator [port]] destination destination-wildcard [operator [port]] [precedence precedence] [tos tos] [log | log-input] [time-range time-range-name] [fragments] This format is similar to the TCP format, except that the protocol variable now is udp. The other difference is that there is no established keyword. The reason is that UDP is a connectionless transport service, and no connections are established between hosts. In Example B-14, three lines have been added to the previous TCP example. Example B-14. This access list permits TCP and UDP packets.access-list 110 permit tcp any 172.22.0.0 0.0.255.255 established access-list 110 permit tcp any host 172.22.15.83 eq 25 access-list 110 permit tcp 10.0.0.0 0.255.255.255 172.22.114.0 0.0.0.255 eq 23 access-list 110 permit udp 10.64.32.0 0.0.0.255 host 172.22.15.87 eq 69 access-list 110 permit udp any host 172.22.15.85 eq 53 access-list 110 permit udp any any eq 161 The following is an explanation of the lines in Example B-14:
The implicit deny any still drops all packets not finding a match in the list. ICMP Access ListsThe syntax for an extended access list line that examines an ICMP packet follows: access-list access-list-number [dynamic dynamic-name [timeout minutes]] {deny | permit} icmp source source-wildcard destination destination-wildcard [icmp-type[icmp-code] | icmp-message] [precedence precedence] [tos tos] [log | log-input] [time-range time-range-name] [fragments] icmp is now in the protocol field. Notice that there are no source or destination ports here; ICMP is a network layer protocol. This line can be used to filter all ICMP messages, or you can use the following options to filter specific ICMP messages:
A sample of an ICMP access list is displayed in Example B-15. Example B-15. This ICMP access list denies specific packets and permits all others.access-list 111 deny icmp 172.22.0.0 0.0.255.255 any 0 access-list 111 deny icmp 172.22.0.0 0.0.255.255 any 3 9 access-list 111 deny icmp 172.22.0.0 0.0.255.255 any 3 10 access-list 111 deny icmp 172.22.0.0 0.0.255.255 any traceroute access-list 111 permit ip any any The following is an explanation of the lines in Example B-15:
|
EAN: 2147483647
Pages: 233