Using Group Policy
Using Group PolicyCentralized management of computer and user configuration settings within Windows Server 2003 is accomplished through Group Policy management, which was introduced in Windows Server 2000. Group Policy settings are configured within Group Policy Objects (GPOs), which can be linked to container locations throughout the Active Directory. The container objects will inherit the proper GPO settings based on object location within the site, domain, or OU to which the GPO has been linked. Group Policy settings are grouped into the following general categories:
Configuration of individual settings is managed within the Group Policy Object Editor (see Figure 3.8), which is almost identical to its Windows Server 2000 equivalent. Windows Server 2003 has added more than 200 new settings that can be configured using this tool. Figure 3.8. The Group Policy Object Editor showing current manipulation of the Maximum Password Age policy setting. Using the Group Policy Management ConsoleOne key technology introduced in Windows Server 2003 is the Group Policy Management Console (GPMC), which brings together many standard management functions for the manipulation of GPOs and their links into a single utility.
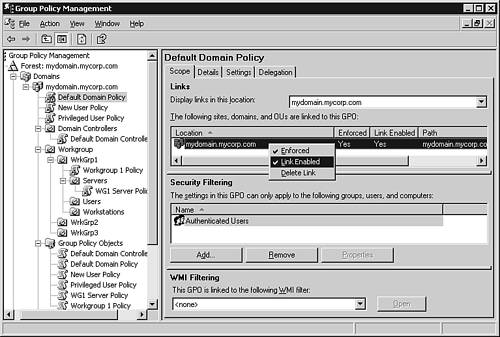
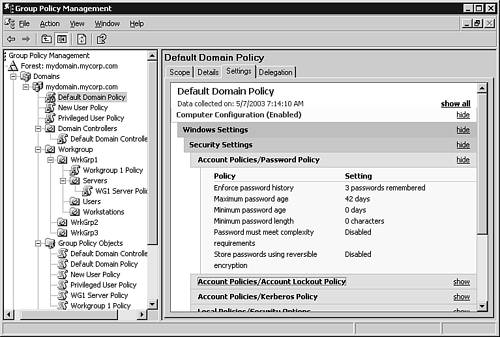
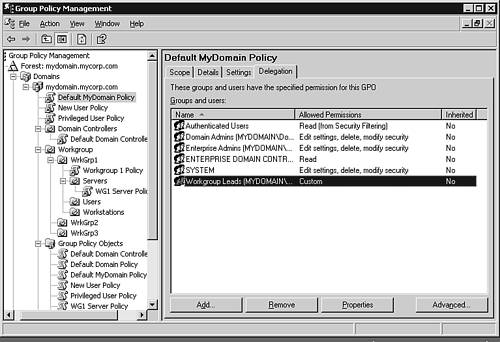
Using this utility, individual GPOs can be configured and linked, and each link's enforcement managed through a simple user interface, as shown in Figure 3.9. Figure 3.9. The Group Policy Management Console showing a current manipulation of the enforcement status of the Default Domain Policy link to the mydomain.mycorp.com domain. The current status of each GPO can be manipulated using the GPMC, as shown in Figure 3.10. Figure 3.10. The Group Policy Management Console showing a current manipulation of the GPO status of the Default MyDomain Policy. The GPMC also includes a well-developed reporting capability, which can be used to display the settings of an individual GPO, as shown in Figure 3.11. Figure 3.11. The Group Policy Management Console showing a report of the current Default MyDomain Policy GPO settings. Because accounts and groups inherit Group Policy settings based on their access privileges, the GPMC includes the capability to manipulate GPO delegation, as shown in Figure 3.12. Figure 3.12. The Group Policy Management Console showing the current delegation settings for the groups and users with permissions to the Default MyDomain Policy. By manipulating the privileges for each group or user, it's possible to further refine the application of Group Policy settings based on as complex a scheme of inheritance as is desirable. To block the application of a particular GPO's settings to a group or user, the rights to Read and Apply Group Policy can be denied , as shown in Figure 3.13. Figure 3.13. Restricting the Read and Apply Group Policy rights of the Workgroup Leads group with regard to the Default MyDomain Policy. The GPMC provides a convenient method for the review of all linked GPOs for a particular container, including the order in which the links will be evaluated, as shown in Figure 3.14. Figure 3.14. The Group Policy Management Console showing all linked GPOs and their evaluation order for the mydomain.myserver.com domain. Copying a GPOThe GPMC can be used to copy an existing GPO to any trusted domain in which the administrator using the GPMC utility has the right to create new GPOs. This can be accomplished by the following:
Backing Up and Restoring GPOsIn addition to the ability to copy GPOs between domains, the GPMC can also be used to back up existing GPOs so that they can be recovered later through a restore procedure. Backing up a GPO stores a copy of the GPO's settings to a selected file location, which can be used to store multiple versions of the same GPO, allowing for versioned recovery to prior GPO settings through a simple restoration of the earlier form. A GPO backup can be accomplished by performing the following steps:
Restoration of an existing backup can be accomplished by the following procedure:
It's also possible to manage all existing backups by right-clicking on the Group Policy Objects node and selecting Manage Backups from the drop-down list of options. Within the Manage Backups dialog box, you can view a listing of existing backups that can be restored and deleted from this interface; you can also view the settings for each. Importing GPO SettingsPrevious GPO backups can also be used for migration of settings when interforest GPO copying is not convenient, such as between testing and production environments. The following procedure can be used to perform an importation of GPO settings from an available backup:
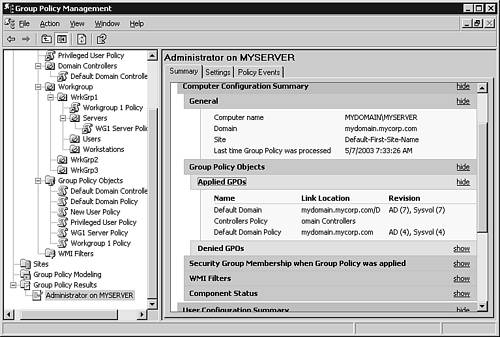
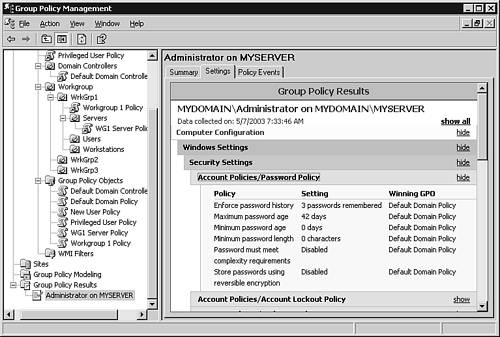
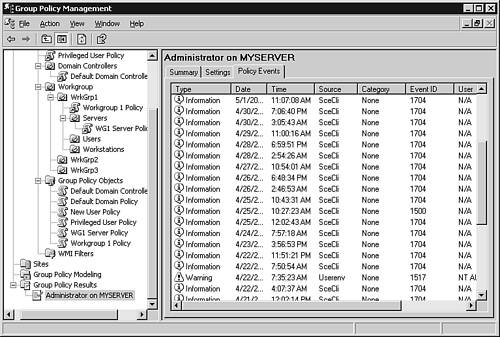
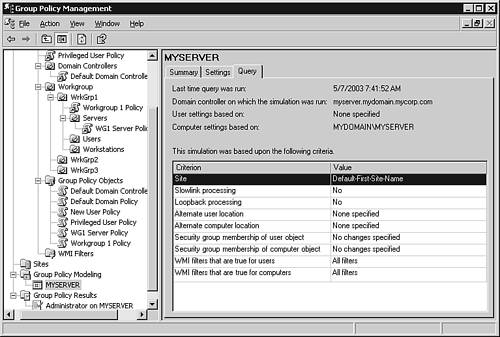
Configuring the Resultant Set of PolicyThe GPMC includes several features beyond the manipulation of individual GPO links, such as the ability to evaluate the overall Resultant Set of Policy (RSoP) with regard to a particular account or group, as shown in Figure 3.15. Figure 3.15. The Group Policy Management Console showing an evaluation of the RSoP for the Administrator account. This capability is invaluable for troubleshooting the resulting settings that are produced through the application of GPO links across many levels of container inheritance. Each resulting setting and the GPO link that is its source can be displayed, as shown in Figure 3.16. Figure 3.16. The Group Policy Management Console showing each setting and the Winning GPO that produces the configuration result. In addition to static information such as GPO settings, the GPMC's reporting capability for modeling Resulting Set of Policy details can also be used to review policy- related events generated within the target system's event logs, as shown in Figure 3.17. Figure 3.17. The Group Policy Management Console showing policy-related events queried from the target server's event logs. Performing Policy SimulationThe GPMC also includes the capability to perform an evaluative simulation of the effect of a particular GPO's application to the current GPO configuration through the use of the Group Policy Modeling subcomponent, which includes the ability to perform a simulated application of a GPO's settings based on a detailed query specification, as shown in Figure 3.18. Figure 3.18. The Group Policy Management Console showing the query settings for an evaluation of GPO application. Group Policy settings can be evaluated within this testing environment before rolling out the results within the production environment. This feature, along with others present within the GPMC, make it possible to perform complex troubleshooting and testing of planned changes to policy settings to facilitate centralized management over even very extensive and complex directory structures. Configuring Security Policy ManagementMicrosoft Windows Server 2003 provides many different means by which individual settings can be configured, including the Group Policy Management Console as well as the Active Directory Users and Computers, Active Directory Domains and Trusts, and Active Directory Sites and Services MMC snap-ins. After the Group Policy Management Console has been installed, the Group Policy tab (displayed in the Properties pages of sites, domains, and OUs when the MMC is started in Author mode) displays an Open button that redirects GPO access attempts to the GPMC, making this utility a one-stop solution for all categories of GPO manipulation. The Group Policy Object Editor accessible through the aforementioned MMC snap-ins (refer to Figure 3.8) provides the ability to manipulate all possible settings for a particular GPO. Additionally, Microsoft Windows Server 2003 also includes more focused utilities, such as the Local Security Policy, Domain Security Policy, and Domain Controllers Security Policy MMC snap-ins. These utilities allow the manipulation of security settings within the appropriate GPO, where templates can be used to apply standard configuration settings based on the intended role of the target system. A number of preconfigured security templates are stored in %systemroot%\Security\Templates and include the following:
Using Security Policy MMC Snap-insWindows Server 2003 includes several MMC snap-ins that can be added to custom MMCs. Two in particular are useful in the manipulation of security template settings: the Security Configuration and Analysis MMC snap-in and the Security Templates MMC snap-in. The following steps can be used to create a custom MMC with these snap-ins configured:
The Security Templates MMC snap-in can be used to create and modify templates, which can then be modeled and applied within the Security Configuration and Analysis MMC snap-in using the same techniques described within the Group Policy Editor MMC snap-in accessed through the GPMC. When a target template is analyzed against current security settings, the Security Configuration and Analysis MMC snap-in produces a comparative analysis of each setting, as shown in Figure 3.19. Managing Policies Through the Command LineMicrosoft Windows Server 2003 includes command-line utilities that mirror much of the same functionality present in the graphical user interface utilities previously discussed in this chapter, including
The GPMC's Software Development Kit (SDK) includes a number of scripts that can be used to automate GPO troubleshooting, including the following:
|
EAN: 2147483647
Pages: 132