Exposing Trojan Programs
Like the wooden horse of legend that the Greeks used to infiltrate the city of Troy, a Trojan program poses as one thing yet actually contains another. Like a virus, a Trojan requires an executable program that the user launches to initiate infection. Often, a Trojan appears to be a harmless game, utility, or program, but when a user launches the Trojan program the malicious code it contains is activated, and the computer becomes infected (see Figure 7-8).
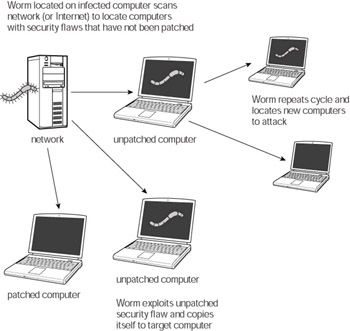
Figure 7-8: A Trojan program
Crackers use Trojans to spread viruses and worms, to install backdoors and spy- ware, or to steal and destroy data. The payload or purpose of a Trojan varies from program to program. Some computer worms create Trojan files containing copies of themselves in order to trick users into launching copies of the worm. Some worms create Trojans and copy them into shared directories of Kazaa and other peer-to-peer network services. This way, other users might download the Trojan and infect their machines.
The best way to protect yourself against Trojan programs is to avoid launching executables received in your e-mail and to install and maintain a computer antivirus program. If you download any software from the Internet, scan it to make sure it isn’t infected before you install or launch it.
EAN: 2147483647
Pages: 145