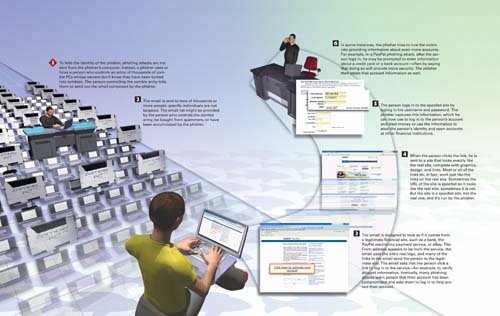
How Phishing Works
 |
How Personal & Internet Security Works
ISBN: 0789735539
EAN: 2147483647
EAN: 2147483647
Year: 2004
Pages: 161
Pages: 161
Authors: Preston Gralla
- Step 1.2 Install SSH Windows Clients to Access Remote Machines Securely
- Step 2.1 Use the OpenSSH Tool Suite to Replace Clear-Text Programs
- Step 3.3 Use WinSCP as a Graphical Replacement for FTP and RCP
- Step 3.4 Use PuTTYs Tools to Transfer Files from the Windows Command Line
- Step 4.6 How to use PuTTY Passphrase Agents