Issuing and Revoking Certificates
| Certificate authorities are responsible for issuing and revoking certificates for users, computers, devices, and even other CAs. Before a certificate can be issued, a request must be generated. Once a certificate has been issued to a requestor , it can be revoked at any time by an administrator. The following section looks at the certificate enrollment process, the different methods for generating a certificate request, and how certificates can be revoked . Certificate EnrollmentThe first step in obtaining a certificate is to submit a certificate request. The process is referred to as certificate enrollment . The following steps outline the basic process that occurs during certificate enrollment:
There are several ways in which a certificate request can be generated. This includes:
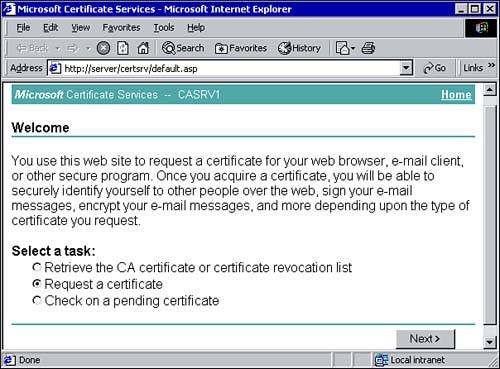
If an enterprise CA is available, the Certificate Request wizard can be used to generate a certificate request. The wizard can be found within the Certificates snap-in. Administrators can use the snap-in to manage their user account, computer account, or local services. Regular users can use the snap-in to manage their own account certificates. When requesting a certificate, you must choose the appropriate certificate template. The ACLs for the templates determine which users and computers can enroll for the different certificates. Using the Certificate Services Enrollment pages, clients can also enroll for a certificate. The Certificate Enrollment Web Pages are installed on the computer running Certificate Services (although the pages can be added to other systems). As shown in Figure 9.12, the enrollment page is accessible from the following URL: http://server_name/certsrv/default.asp . Figure 9.12. Using Web-based certificate enrollment.
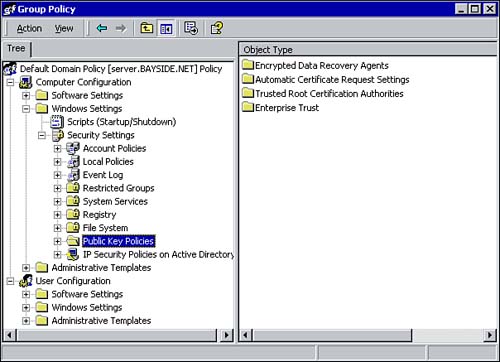
The third option is to use automated enrollment, which relies on the Windows 2000 Group Policy. When automated enrollment is configured, the specified certificates are automatically issued to all computers and users within the scope of the policy. Again, this enrollment method is supported only when an Enterprise CA is available. Using automated enrollment is further discussed in the following section. Using Public Key Group PolicyOne of the benefits of configuring the Public Key Group Policy is that you can automate the enrollment of computer certificates. You can use the Group Policy snap-in to configure a Public Key Policy for sites, domains, organizational units, and local computers. To configure automated certificate enrollment, follow these steps:
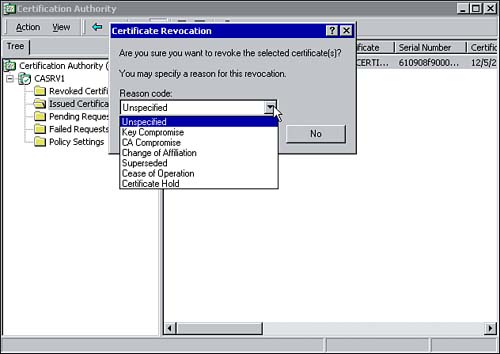
Once the automatic certificate request has been created, the certificate templates are issued the next time a computer within the scope of the policy is restarted or logs onto the domain. Revoking CertificatesOne of the tasks associated with managing certificates is revoking them. At some point you may find it necessary to revoke an issued certificate. For example, if an employee leaves an organization, his or her certificate must be revoked. Once a certificate is marked as revoked, it is moved to the Certificate Revocation List (CRL) . (You learn more about the CRL in a moment.) The revoked certificate appears on the CRL the next time it is published. All revoked certificates appear on the list so others can verify valid certificates. An Administrator can use the Certificate Authority snap-in to revoke a certificate. To revoke a certificate, follow these steps:
Before you revoke a certificate, keep in mind that once it is revoked it cannot be made valid again. The user must be issued a new certificate to replace the revoked one.
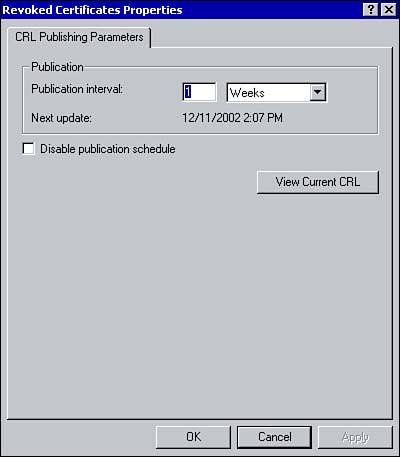
Certificate Revocation ListPeriodically, Windows 2000 Certificate Services publishes a Certificate Revocation List (CRL) . This list is used to inform other entities which certificates have been revoked and are therefore no longer valid. The CRL is automatically published once every week, although an administrator can configure the interval for a different time period. For example, if you expect the number of certificate revocations per week to be high, you may want to decrease the Publication interval so it occurs more frequently. This can be done through the Certificate Authority snap-in by right-clicking the Revoked Certificate folder and choosing Properties. In the resulting property box, you can make your adjustments to the time cycle for the CRL's publication (see Figure 9.15). Figure 9.15. Configuring the CRL publication interval. Although the CRL is published by default once a week, you can manually publish a CRL if you revoke a certificate between publication intervals and need to immediately notify other entities of the change. To do so, right-click the Revoked Certificates folder within the Certificate Authority snap-in, choose All Tasks and choose Publish. The CRL is published in the < systemroot >\system32\CertSrv\CertEnroll folder, as well as in Active Directory if the CRL is published by an Enterprise CA. Manually publishing a CRL does not interfere with the regular publication interval.
|
EAN: 2147483647
Pages: 167