Know Who is Connected Using Two-factor Authentication
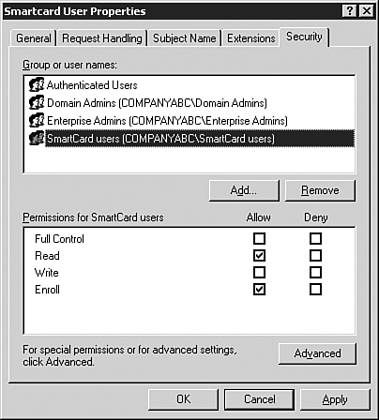
Know Who is Connected Using Two-factor AuthenticationUsernames and passwords have long been the standard for user authentication. Windows NT improved on this concept by adding a machine account that was needed to log into a domain. Although this was good for domain logins it could be bypassed to attach to network resources via pass-through authentication. Many companies need stronger methods of authentication. This is especially critical when dealing with remote users. Modem pools and VPN devices are relatively easy to find. Malicious hackers can spend time trying to get through these devices with relative impunity. This concern is addressed by the concept of two-factor authentication such as smartcards and biometric authentication. Utilizing SmartcardsA smartcard is a portable programmable device containing an integrated circuit that stores and processes information. Smartcards traditionally take the form of a device the size of a credit card that is placed into a reader but they can also be USB-based devices or integrated into employee badges. Windows 2003 and Windows XP have native support for smartcards as an authentication method. Smartcards are combined with a PIN, which can be thought of as a password, to provide two-factor authentication. Physical possession of the smartcard and knowledge of the PIN must be combined to successfully authenticate. To use a smartcard, a domain user must have a smart card certificate. The administrator must prepare a Certificate Authority (CA) to issue smart card certificates before the CA can issue them. The CA needs both the Smart Card Logon and Enrollment Agent certificate templates installed. If smart card certificates for secure e-mail messages are to be used, the administrator must also install the Smart Card User certificate template. To configure a Windows-based Enterprise CA to Issue Smart Card Certificates, follow these steps:
Leveraging Biometrics to Enhance SecurityBiometrics refers to unique biological information that can be used to determine the identity of a user. This, combined with a name /password authentication, provides a two-factor authentication that cannot be duplicated . Thumbprints, bone density, and retinal patterns are all commonly used with biometric security. Third-party biometric solutions leverage proprietary authentication mechanisms to work in tandem with existing authentication protocols in network operating systems. Technologies like retinal scanners are usually standalone devices whereas items like fingerprint readers can integrate into the user's keyboard. |
EAN: 2147483647
Pages: 325