Securing the Hatches
| Today, the whole world is looking at security. As the world becomes more information connected, issues of information privacy are on everyone's mind. Several government mandates have been issued in the area of securing identity information for medical histories and for information regarding children. Commerce across networks in the arena of business to business and business to consumer have all raised questions about whether credit card information is being stored securely or whether online transactions are safe. These issues have spawned many technologies and the corporate world has adopted many of these for internal security. As access to information becomes easier and easier, it is more and more critical to ensure that data and data transmissions are protected. Security and Company Reputation In today's market, if a company is to keep its customers, the customers must have faith in the company. Large online retailers are dependant on the confidence of their customers in their security in order to continue doing business. So long as customers feel secure that their financial information is being transmitted and stored securely, they will continue to do business with a company online. If one of these online retailers was to become compromised and information such as credit card numbers was stolen, it could potentially destroy the company. The reputation of the company is tied directly to its security. Failure to be diligent in securing the hatches of a company can quickly lead to its downfall. Implementing Transport Layer SecurityThe concept of Transport Layer Security (TLS) is that conversations between networked devices should be held in a manner such that any other device that might have intercepted the communications will be unable to use the information. TLS, which is similar to SSL, is based on an x.509 certificate which must be published from a trusted Certificate Authority (CA). TLS can do the following:
To use TLS for client/server communication, the following steps are used:
By default TLS will accept any cipher; this can be locked down further by GPO to limit the cipher choices through modification of the following Registry key: HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\ Ciphers You will find multiple cipher choices listed and can enable or disable them as appropriate. The TLS Handshake Protocol involves the following steps:
Requiring Digital SigningOlder implementations of Small Message Block (SMB) communications were susceptible to what is known as a man-in-the-middle attack. A man-in-the-middle attack occurs when an attacker masquerading as one of the legitimate parties inserts messages into the communications channel. This allows the attacker to send its own credentials and causes the other host to accept its connection. By placing a digital signature into each SMB, which is verified by both the server and the client, there is a mutual authentication that verifies the validity of both the server and the client. If this security setting is enabled on a server, the clients must support digital signing of communications or they will be unable to communicate with the server. This can be configured in the Default Domain Controller Security Settings under Security Settings/Local Policies/Security Options/Microsoft Network Server: Digitally Sign Communications (always)Enabled. Leveraging PKINot surprisingly, certificate-based technologies require access to certificates. Specifically, certificates that have been issued by a trusted Certificate Authority. Companies have the option of using an external trusted Certificate Authority such as Verisign, SecureNet, or Globalsign. One advantage of using one of these external Certificate Authorities is that Internet Explorer comes preloaded with these as trusted root authorities. This means that clients won't have to contact those root CAs and prompt the user to accept the certificate. The other option is for a company to establish its own Certificate Authority. This could be a root CA or an Enterprise CA that was built based on a certificate provided by another Root CA. If a company is going to issue its own certificates, client machines can be preloaded with the certificate via GPO settings. For example, if a company will be using digital certificates in their intranet, they might push a server certificate to the clients to define the server as an Intermediate Certification Authority. To push a certificate to clients, do the following:
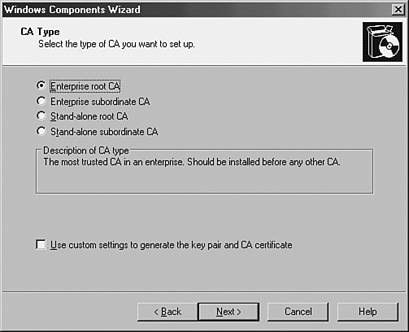
The Wizard will inform you that you are about to install a certificate claiming to be from a particular source. If this information is valid, select "yes". The Wizard will inform you that the certificate was successfully installed. Installing Certificate ServicesInstalling certificate services in Windows Server 2003 requires taking a Windows 2003 server and adding the Certificate Services component on the server. The process of adding Certificate Services to a Windows 2003 is as follows :
If IIS Is Installed on the Server, a Dialog Box Will Appear If IIS is installed on the server, a dialog box will appear noting that the IIS services will be temporarily stopped . When prompted whether it is okay to stop and restart the IIS service, choose Yes unless the service is actively in use at the time of certificate services installation. Importance of Physical SecurityNetwork security is essentially useless if the servers involved aren't physically secured. Computers don't know the difference between a local break-in and a legitimate password recovery. Although security information is stored in the Active Directory, the Active Directory still consists of a database stored on servers. This information is laid out in a specific structure and a person with physical access to a hard drive that contains an NTDS.DIT file, a sector editor, and sufficient knowledge can compromise the security database. Servers should always be located in locked data centers. Access to these data centers should be limited and audited . Security logs [%systemroot%\System32\config\SecEvent.Evt] should be duplicated in a separate location to prevent tampering. Applications like Microsoft Operations Manager, which centralize management of event logs, are useful for this task. Implementation of a syslog server will also work well for this. Access to secured data centers should require multiple forms of authentication. For example, rather than just rely on a badge reader, the lock might consist of a combination of a badge reader and a PIN code that must be entered. This way, theft of a badge would not be enough to compromise the data center.
|
EAN: 2147483647
Pages: 325