Section 3.2. Preparing to Deploy Agents
3.2. Preparing to Deploy AgentsBefore deploying agents , identify the machines you are going to deploy to. Depending where the machines are in your network, you will use different methods to install and manage the agents. Leaky Faucet has to deploy agents into three different environments: the local LAN, across slow WAN links and firewalls but still in the same domain, and into a workgroup in their DMZ. The Leaky Faucet network is depicted in Figure 3-2. Figure 3-2. Leaky Faucet's network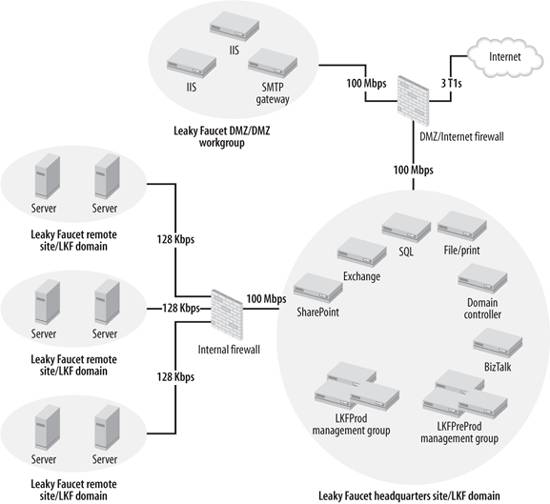 Although the method of agent deployment and management will vary based on the target computer and the environment it is in, you will go through the same deployment process and management steps.
|
EAN: 2147483647
Pages: 107