Access Lists
In the most intuitive sense, an access list is a series of rules that instruct the router on how to select or match a route or packet. IOS uses access lists as an extremely general mechanism for controlling many kinds of router behavior, but the best way to understand how they work is to start with the simplest application: controlling the traffic that flows into or out of an interface.
Each rule in a standard access list contains three important parts:
- a number that identifies the list when you refer to it in other parts of the router's configuration
- a deny or permit instruction
- a packet identifier (such as an address)
As incoming or outgoing packets reach an interface that has an access list, the router compares the packets to each rule in the access list and decides whether the traffic should be blocked (denied) or permitted.
For IP traffic, there are two fundamental types of lists: standard and extended. Standard access lists filter based on source network addresses. A typical standard access list looks like this:
access-list 1 deny 10.10.1.0 0.0.0.255 access-list 1 deny 10.10.2.0 0.0.0.255 access-list 1 permit any
This list blocks any traffic from the 10.10.1.0 and 10.10.2.0 subnets, regardless of the packet's destination, and permits anything that makes it past the first two lines. In other words, all traffic is permitted except for the 10.10.1.0 and 10.10.2.0 subnets. Once you have the list, you can apply it to the packets going into or out of a particular interface. To apply this list to the traffic arriving at (i.e., coming into) a particular interface, we would use the ip access-group command:
interface ethernet0 ip access-group 1 in
As I mentioned, there are many other contexts in which access lists can be used. You can use them to restrict who can access a particular TTY line, to specify what routes are sent in and out of various routing processes, and to perform many other functions. It's also worth noting that while applying access list 1 to the packets arriving at ethernet0 prevents traffic from subnets 10.10.1.0 and 10.10.2.0 from passing through the router, it doesn't affect traffic arriving at any other interface, nor does it have any effect on protocols other than IP. You have to watch each interface and protocol separately.
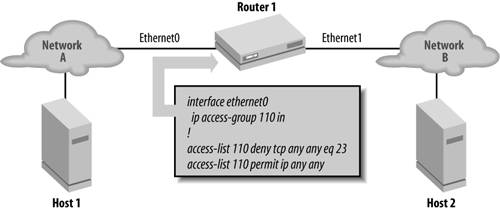
Standard access lists perform filtering on the basis of source IP addresses. Extended access lists allow you to build much more flexible filters that use source and destination addresses, in addition to higher layer protocol information. For example, you can build a filter based on ICMP type and code values. For TCP and UDP, you can filter on destination and source ports. Figure 7-1 shows a router with an extended access list applied to ethernet0. This access list blocks incoming TCP traffic for port 23, regardless of the traffic's source or destination address. Since port 23 is the telnet port, this list prevents any hosts on Network A from telnetting to hosts on Network B or to the router itself.
Figure 7-1. An extended access list to block telnet
Access lists can also be applied in the outbound direction. For example, we can create a list that denies traffic on port 80 and apply that list to outbound packets traveling through ethernet0. This will prevent hosts on Network B from accessing web servers on Network A:
! Deny traffic on port 80 (www traffic) ip access-list 111 deny tcp any any eq 80 ip access-list 111 permit ip any any ! interface ethernet0 ! Apply access list 111 in the outbound direction ip access-group 111 out
The access lists we've seen so far have been very simple, but they can be much more complex.
Getting Started
- Getting Started
- IOS User Modes
- Command-Line Completion
- Get to Know the Question Mark
- Command-Line Editing Keys
- Pausing Output
- show Commands
IOS Images and Configuration Files
- IOS Images and Configuration Files
- IOS Image Filenames
- The New Cisco IOS Packaging Model
- Loading Image Files Through the Network
- Using the IOS Filesystem for Images
- The Routers Configuration
- Loading Configuration Files
Basic Router Configuration
- Basic Router Configuration
- Setting the Router Name
- Setting the System Prompt
- Configuration Comments
- The Enable Password
- Mapping Hostnames to IP Addresses
- Setting the Routers Time
- Enabling SNMP
- Cisco Discovery Protocol
- System Banners
Line Commands
- Line Commands
- The line Command
- The Console Port
- Virtual Terminals (VTYs)
- Asynchronous Ports (TTYs)
- The Auxiliary (AUX) Port
- show line
- Reverse Telnet
- Common Configuration Items
Interface Commands
- Interface Commands
- Naming and Numbering Interfaces
- Basic Interface Configuration Commands
- The Loopback Interface
- The Null Interface
- Ethernet, Fast Ethernet, and Gigabit Ethernet Interfaces
- Token Ring Interfaces
- ISDN Interfaces
- Serial Interfaces
- Asynchronous Interfaces
- Interface show Commands
Networking Technologies
Access Lists
IP Routing Topics
- IP Routing Topics
- Autonomous System (AS) Numbers
- Interior and Exterior Gateway Protocols
- Distance-Vector and Link-State Routing Protocols
- Static Routes
- Split Horizon
- Passive Interfaces
- Fast Switching and Process Switching
Interior Routing Protocols
Border Gateway Protocol
- Border Gateway Protocol
- Introduction to BGP
- A Simple BGP Configuration
- Route Filtering
- An Advanced BGP Configuration
- Neighbor Authentication
- Peer Groups
- Route Reflectors
- BGP Confederacies
- BGP TTL Security
Quality of Service
- Quality of Service
- Marking
- Older Queuing Methods
- Modern IOS QoS Tools
- Congestion Avoidance
- Traffic Policing
- Traffic Shaping
- AutoQoS
- QoS Device Manager
Dial-on-Demand Routing
- Dial-on-Demand Routing
- Configuring a Simple DDR Connection
- Sample Legacy DDR Configurations
- Dialer Interfaces (Dialer Profiles)
- Multilink PPP
- Snapshot DDR
Specialized Networking Topics
- Specialized Networking Topics
- Bridging
- Hot Standby Routing Protocol (HSRP)
- Network Address Translation (NAT)
- Tunnels
- Encrypted Tunnels
- Multicast Routing
- Multiprotocol Label Switching (MPLS)
Switches and VLANs
- Switches and VLANs
- Switch Terminology
- IOS on Switches
- Basic Switch Configuration
- Trunking
- Switch Monitor Port for IDS or Sniffers
- Troubleshooting Switches
Router Security
- Router Security
- Securing Enable Mode Access
- Routine Security Measures
- Restricting Access to Your Router
Troubleshooting and Logging
Quick Reference
Appendix A Network Basics
Index
EAN: 2147483647
Pages: 1031
