How Client Pull and Server Push Animation Work
Client PullClient pull is executed by the Refresh command. A refresh command is written into an HTML document using the <META> tag. The contents of the <META> tag are added to the header's meta-information that the server sends along with the HTTP response. During a client pull sequence, the browser reads this header information that instructs it to use your PC's internal clock to keep track of the time elapsed between pages retrieved. When the time has elapsed, the browser requests and displays the next page.
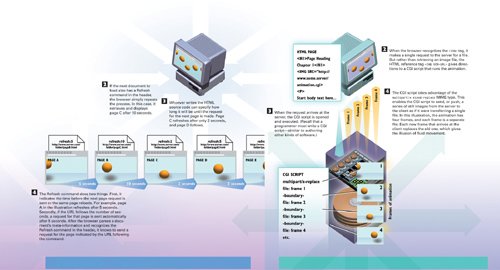 Note A client pull sequence might continue for as many or as few pages as the site designer wants. The last page will simply not have a Refresh command in the header. A user can stop the process manually by clicking the browser's Stop button. Server PushServer push is more complicated than client pull, but it enables inline animation that does not require an entire web page to load each animation frame.
Note The server and client make one connection that is open for as long as the CGI script runs. You can manually end a server push animation by clicking the browser's Stop button. |
EAN: 2147483647
Pages: 223