Maintaining Folder and File Permissions
On an NTFS volume, you can set permissions down to the file level. This means for any file you can give individual users different types of access. Although you can set such detailed permissions, this way lies madness for all but the most meticulous of control freaks (who are, arguably, already mad).
Always try to operate with the simplest possible permissions. Set as few restrictions as possible. Assign permissions to groups, not individuals. Don't set file-by-file permissions unless it is unavoidable. Managing the minutiae of permissions can easily and quickly soak up all your time and much of your life's blood as well—unless you guard against it.
Considering Inheritance
Just to complicate matters a bit more, there are two types of permissions, explicit and inherited permissions. Explicit permissions are the ones you set on folders that you create. Inherited permissions are those that flow from a parent object to a child object. By default, when you create a subfolder, it inherits the permissions of the parent folder.
If you don't want the child objects to inherit the permissions of the parent, you can block inheritance at the parent level or at the child level. Where you block inheritance is important. Block at the parent level and no subfolders will inherit permissions. Block selectively at the child level and some folders will inherit permissions and others will not.
To block inheritance at the parent level, choose This Folder Only when assigning special permissions. To block only a certain file or folder from inheriting permissions, right-click the folder, select Properties, and then click the Security tab. Clear the check box for Allow Inheritable Permissions From Parent To Propagate To This Object.
If the check boxes for permissions appear shaded (Figure 9-33), it means the permissions are inherited from a parent object. There are three ways to this situation change:
- Clear the check box for Allow Inheritable Permissions From Parent To Propagate To This Object. Once the check box is cleared, you can make changes to the permissions or change the users or groups in the list.
- Change the permissions of the parent folder.
- Select the opposite permission—Allow or Deny—to override the inherited permission.
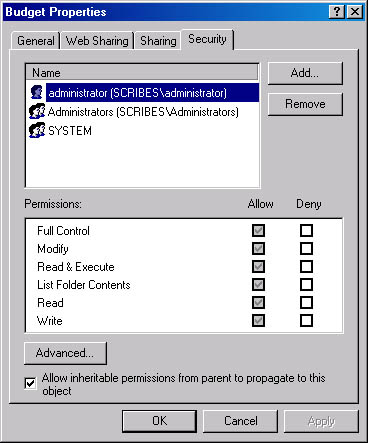
Figure 9-33. Viewing a folder with inherited permissions.
![]()
NOTE
If neither Allow nor Deny is checked, the users/groups may have acquired the permission through a group membership. Otherwise, failure to explicitly configure Allow or Deny effectively denies the permission.
What the Permissions Mean
Windows 2000 Server has a set of standard permissions that are combinations of specific kinds of access. The individual permissions are Full Control, Modify, Read & Execute, List Folder Contents, Read, and Write. Table 9-9 shows the special permissions and the standard permissions to which they apply.
Table 9-9. Special permissions for folders
| Special Permission | Full Control | Modify | Read & Execute | List Folder Contents | Read | Write |
|---|---|---|---|---|---|---|
| Traverse Folder/Execute File | Yes | Yes | Yes | Yes | Yes | No |
| List Folder/Read Data | Yes | Yes | Yes | Yes | Yes | No |
| Read Attributes | Yes | Yes | Yes | Yes | Yes | No |
| Read Extended Attributes | Yes | Yes | Yes | Yes | Yes | No |
| Create Files/Write Data | Yes | Yes | No | No | No | Yes |
| Create Folders/Append Data | Yes | Yes | No | No | No | Yes |
| Write Attributes | Yes | Yes | No | No | No | Yes |
| Write Extended Attributes | Yes | Yes | No | No | No | Yes |
| Delete Subfolders and Files | Yes | No | No | No | No | No |
| Delete | Yes | Yes | No | No | No | No |
| Read Permissions | Yes | Yes | Yes | Yes | Yes | Yes |
| Change Permissions | Yes | No | No | No | No | No |
| Take Ownership | Yes | No | No | No | No | No |
File permissions include Full Control, Modify, Read & Execute, Read, and Write. As with folders, each of these permissions controls a group of special permissions. Table 9-10 shows the special permissions associated with each standard permission.
Table 9-10. Special permissions associated with standard permissions
| Special Permission | Full Control | Modify | Read & Execute | Read | Write |
|---|---|---|---|---|---|
| Traverse Folder/Execute File | Yes | Yes | Yes | No | No |
| List Folder/Read Data | Yes | Yes | Yes | Yes | No |
| Read Attributes | Yes | Yes | Yes | Yes | No |
| Read Extended Attributes | Yes | Yes | Yes | Yes | No |
| Create Files/Write Data | Yes | Yes | No | No | Yes |
| Create Folders/Append Data | Yes | Yes | No | No | Yes |
| Write Attributes | Yes | Yes | No | No | Yes |
| Write Extended Attributes | Yes | Yes | No | No | Yes |
| Delete Subfolders and Files | Yes | No | No | No | No |
| Delete | Yes | Yes | No | No | No |
| Read Permissions | Yes | Yes | Yes | Yes | Yes |
| Change Permissions | Yes | No | No | No | No |
| Take Ownership | Yes | No | No | No | No |

TIP
Any user or group assigned Full Control on a folder can delete files and subfolders no matter what the permissions are on the individual files or subfolders.
How Permissions Work
If you take no action at all, the files and folders inside a shared folder will have the same permissions as the share. Permissions for both directories and files can be assigned to
- Domain local groups, global groups, universal groups, and individual users.
- Global groups, universal groups, and individual users from domains that this domain trusts.
- Special identities such as Everyone and Authenticated Users.
The important rules for permissions can be summarized as follows:
- By default, a folder inherits permissions from its parent folder. Files inherit their permissions from the folder in which they reside.
- Users can access a folder or file only if they've been granted permission to do so or they belong to a group that has been granted permission.
- Permissions are cumulative, but the Deny permission trumps all others. For example, if the Technical Writers group has Read access to a folder and the Project group has Modify permission for the same folder, and Alex is a member of both groups, Alex will have the higher level of permission, which is Modify. However, if the Technical Writers group permission is changed to explicitly Deny, Alex will be unable to use the folder, despite his membership—and ostensibly higher level of access—in the Project group.
- The user who creates a file or folder owns that object and can set permissions to control access.
- An administrator can take ownership of any file or folder but cannot pass ownership along to anyone else.
Configuring Folder Permissions
Before sharing a folder on an NTFS volume, set all the permissions on the folder. When you set folder permissions, you're also setting permissions on all the files and subfolders in the folder.
To assign permissions to a folder, right-click the folder in Explorer and choose Properties. Then click the Security tab and select Permissions.
To remove an individual or group from the list, just highlight the name and click Remove.
To add to the list of those with permissions, click the Add button. This opens the Select Users, Computers, Or Groups dialog box (Figure 9-34).
Click OK when you're done and the Folder Permissions box opens with the new names.
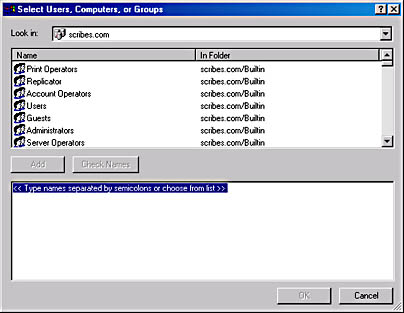
Figure 9-34. Selecting users and groups.
Assigning Permissions to Files
Permissions for individual files are assigned in the same way as folders. There are, however, some special considerations:
- Remember to grant permissions to groups, rather than individuals.
- Create groups and assign file permissions to them rather than assign permissions directly to local groups.
Configuring Special Permissions
In some circumstances, you may find it necessary to set, change, or remove special permissions on either a file or folder. (Special permissions on a folder affect only the folder). To access special permissions, follow these steps:
- In Explorer, right-click the file or folder and choose Properties from the shortcut menu.
- Click the Security tab, and then click the Advanced button.
- To add a user or group, click the Add button. Double-click the user or group name to open the Permission Entry dialog box.
- To view or modify existing special permissions, highlight the name of the user or group and click the View/Edit button.
- To remove special permissions, highlight the name of the user or group and click Remove. If the Remove button is dimmed, clear the check box for Allow Inheritable Permissions From Parent To Propagate To This Object, and skip to step 6.
- In the Permission Entry dialog box (Figure 9-35), select where you want the permissions applied in the Apply Onto box. (See Table 9-11 and Table 9-12 for explanations of the choices in this drop-down box.) Apply Onto is available for folders only.
- In Permissions, click Allow or Deny for each permission.
- To prevent subfolders and files from inheriting these permissions, select Apply These Permissions To Objects And/Or Containers Within This Container Only.
- Click OK to close the dialog boxes.
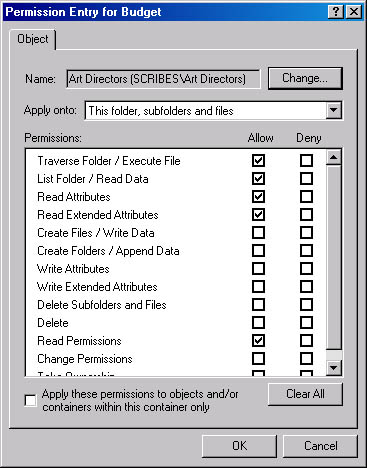
Figure 9-35. Setting special permissions for a folder.
In the Permission Entry dialog box for folders, you can choose how and where the special permissions are applied. Tables 9-11 and 9-12 demonstrate the application of the special permissions depending on whether Apply These Permissions To Objects And/Or Containers Within This Container Only is selected or not.
Table 9-11. Application of special permissions when Apply These Permissions To Objects And/Or Containers Within This Container Only is selected
| Selected in Apply Onto | Applies to current folder? | Applies to subfolders in current folder? | Applies to files in current folder? | Applies to subsequent subfolders? | Applies to files in subsequent subfolders? |
|---|---|---|---|---|---|
| This folder only | Yes | No | No | No | No |
| This folder, subfolders, and files | Yes | Yes | Yes | No | No |
| This folder and subfolders | Yes | Yes | No | No | No |
| This folder and files | Yes | No | Yes | No | No |
| Subfolders and files only | No | Yes | Yes | No | No |
| Subfolders only | No | Yes | No | No | No |
| Files only | No | No | Yes | No | No |
Table 9-12. Application of special permissions When Apply These Permissions To Objects And/Or Containers Within This Container Only is not selected
| Selected in Apply Onto | Applies to current folder? | Applies to subfolders in current folder? | Applies to files in current folder? | Applies to subsequent subfolders? | Applies to files in subsequent subfolders? |
|---|---|---|---|---|---|
| This folder only | Yes | No | No | No | No |
| This folder, subfolders, and files | Yes | Yes | Yes | Yes | Yes |
| This folder and subfolders | Yes | Yes | No | Yes | No |
| This folder and files | Yes | No | Yes | No | Yes |
| Subfolders and files only | No | Yes | Yes | Yes | Yes |
| Subfolders only | No | Yes | No | Yes | No |
| Files only | No | No | Yes | No | Yes |
Ownership and How It Works
As you've seen, Administrators and members of a few other select groups are the only ones who can grant and change permissions. The exception is when a user is the owner of the folder or file in question. Every object on an NTFS partition has an owner and the owner is the person who created the file or folder. The owner controls access to the file or folder and can keep out anyone he or she chooses.
Figure 9-36 shows an example of a folder called Max's Private Stuff made by the user Maxwell (Figure 9-36).
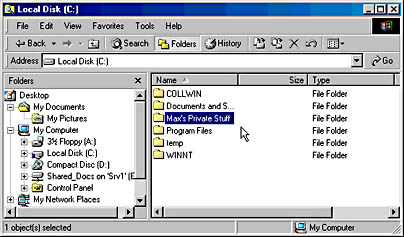
Figure 9-36. A user's new folder.
To see who has permission to access his new folder, Maxwell right-clicks the folder and chooses Properties and then clicks Security. When he clicks the Permissions button, the dialog box shown in Figure 9-37 opens.
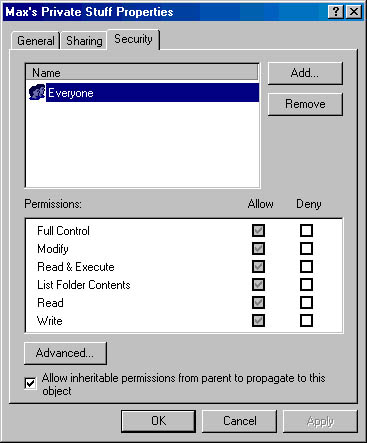
Figure 9-37. Viewing the permissions for a new folder.
Much to his surprise, it appears that everyone on the network has access to his "private" stuff. But since Maxwell is the owner of the folder, he can change the permissions so that he has the folder all to himself. To do so, he explicitly adds his name to the permissions list and clears the Allow Inheritable Permissions option.
After this is done, even the administrator will see an Access Denied message when trying to open the folder.
Of course, nothing on the network can be completely beyond the reach of administrators, so the administrator can right-click the folder and choose Properties from the shortcut menu. When he or she clicks the Security tab, the information box shown in Figure 9-38 opens.
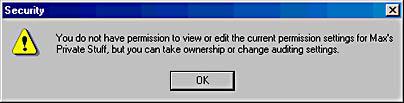
Figure 9-38. The administrator tries to view permissions for a folder owned by a user.
In the Security properties window, no changes can be made. However, if the administrator clicks the Advanced button and then the Owner tab (Figure 9-39), he or she can change the owner of the folder to an administrator.
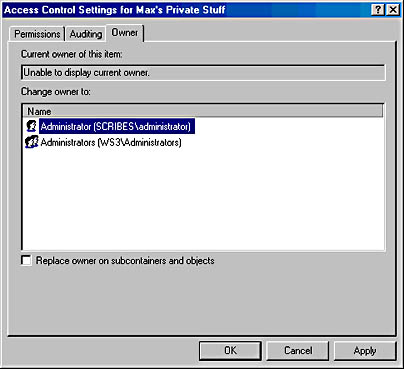
Figure 9-39. Changing the ownership of a folder.
No matter what the status of the folder, the administrator can take ownership. When Maxwell logs on the next time, he'll still have access to Max's Private Stuff, but if he clicks Advanced and then Owner, he'll see that he's no longer the owner of the folder. Thus, even though administrators can go into all areas without an invitation, they can't do so without leaving evidence of their presence.
![]()
NOTE
The owner of a file or folder can also grant the Take Ownership special permission to others, allowing those users to take ownership at any time.
EAN: 2147483647
Pages: 366