Managing the Active Directory Schema
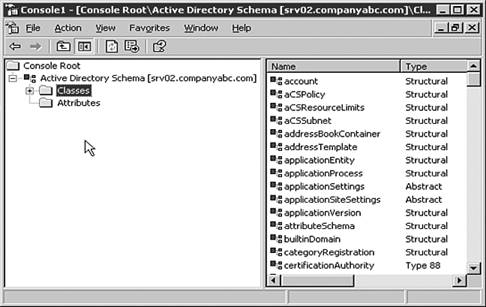
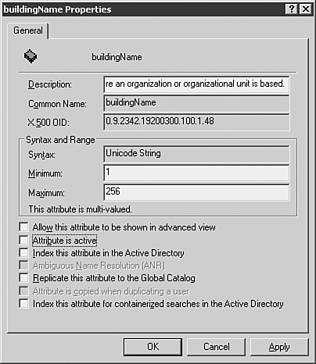
| The schema is to the Active Directory what the Registry is to the Windows operating system. The schema is a database of definitions for all object types within the directory structure, which determines how all Active Directory objects can and are configured. Just as care is extended to managing and modifying the Windows Registry, extreme care should be extended to the administration of the schema. Changes to the schema affect the entire Active Directory environment. As such, the schema is not a database that should be modified casually. If modifications will be made, either for troubleshooting or development purposes, it is important to test these modifications in a test lab environment before implementing them in production. The next section discusses the tools used to manage the schema and a new feature in Windows Server 2003 that allows for schema attribute deletes. Using Active Directory Service Interfaces (ADSI) EditOne method for viewing and modifying the Active Directory schema is by using the Active Directory Service Interfaces (ADSI) Edit utility. The ADSIEdit utility provides a GUI interface similar to Active Directory Users and Computers, but with a much lower level view of Active Directory objects. ADSI Edit is installed with the Support Tools available on the installation media in the Tools/Support folder. Once installed, ADSI Edit can be accessed through the MMC snap-in, or by executing adsiedit.msc from the run line. Although ADSI Edit provides a method for modifying Active Directory objects, the tool is best used as a method for troubleshooting or gaining detailed configuration information about a particular Active Directory implementation. When changes to Active Directory fail to work through the normal administration tools, such as Active Directory Users and Computers and Active Directory Sites and Services, ADSI Edit can be used as a last resort to repair the AD database. For example, as was discussed in an earlier section of this chapter, DCPromo can be used to promote a member server to a domain controller and demote a domain controller to a member server. If a DCPromo demotion process fails, it might become necessary to delete the specific domain controller object from Active Directory by using the ADSI Edit utility. Using the Active Directory Schema Snap-inThe easiest way to view and modify the Active Directory schema is by using the Active Directory schema snap-in. Unlike other Active Directory snap-ins that are installed by default with the Windows Server 2003 Administration Tools, the Schema snap-in must be activated by running the following command at a command prompt: regsvr32 schmmgmt.dll . After the program is registered on the computer, the snap-in can be access by adding it to an MMC session. When executed, the Schema snap-in provides a GUI interface that lists both Active Directory classes and attributes, as shown in Figure 12.8 Figure 12.8. Viewing schema classes and attributes. In the schema, an object class represents a category of directory objects, such as users, printers, or application programs, that share a set of common characteristics. The definition for each object class contains a list of the schema attributes that can be used to describe instances of the class. For example, the Computer class has attributes such as Network Address, Operating System, and Machine Role. The Schema snap-in provides a low-level view of the classes and associated attributes in Active Directory providing schema administrators to view and modify individual characteristics of Active Directory objects. The Schema Admins Group By default, only members of the Schema Admins group have the capability to write to the schema. Also, by default only the administrator account of the root domain of a forest is a member of the Schema Admins group. Schema DeactivationIn Windows 2000, as with Windows Server 2003, it is possible to extend the schema with new classes and attributes. Installing Exchange 2000, for example, extends to the schema to almost double its original size. But after classes and attributes were added to the schema, it was not possible to remove them. Although it is still the case that added classes and attributes cannot be deleted, with Windows Server 2003, schema administrators now have the capability to deactivate and redefine classes and attributes. Classes, Attributes, and the Forest Functional Level Classes and attributes added to the base schema can be deactivated without raising the forest functional level. However, they can be redefined only in forests with the forest functional level set to Windows Server 2003. To deactivate an attribute, for example to deactivate an attribute called BuildingName, perform the following steps:
|
EAN: 2147483647
Pages: 325