OSNOS Hardening
|
|
OS/NOS Hardening
Operating Systems (OS) and Network Operating Systems (NOS) hardening refers to the process of making the environment more secure from attacks and intruders. This section discusses the process of hardening an operating system and the methods of keeping them hardened as new threats emerge. This section will also discuss some of the vulnerabilities of the more popular operating systems and what can be done to harden them.
| Note | The current exam does not test specifics of operating systems hardening. You should know and understand the general principles of hardening. Each product has a different set of procedures and methods to accomplish this. Review your software and hardware vendors' websites, literature, and installation documentation to more fully understand these procedures. |
Network Protocol Configuration
Configuring an OS's network protocols properly is a major factor in hardening. Three primary network protocols are used in PC systems: NetBEUI, IPX/SPX, and TCP/IP. This section touches on the areas you must consider when you are configuring these network protocols. Each of these protocols can transport the Microsoft native networking protocol NetBIOS across networks. NetBIOS protocol-enabled systems periodically announce names, service types, and other information on the networks that are bound to it. NetBIOS is also used for programming interfaces and other things.
The following sections provide additional information on how network protocols are configured, how they are installed, and how they operate in a PC environment.
Network Binding Binding is the process of associating a network protocol to another network protocol or to a network interface card. In a Microsoft network, NetBIOS can be bound to any of the three protocols that have been introduced. This binding process is where the security vulnerability is found.
For example, binding NetBIOS to TCP/IP encapsulates NetBIOS messages into TCP/IP packets. TCP/IP can then be used to send NetBIOS traffic across the network. This is a major vulnerability, as the ability to communicate with your system using NetBIOS creates a huge vulnerability. The problem lies in the fact that NetBIOS information becomes encapsulated in TCP/IP packets, making them vulnerable to sniffing. Figure 5.1 illustrates the process of network binding. If the TCP/IP packet is intercepted, critical systems information, including passwords, can be discovered.

Figure 5.1: NetBIOS binding to TCP/IP network protocolMake sure that your network protocols and adapters have the proper binding configurations. Do not bind NetBIOS to a protocol unless it is necessary. Figure 5.2 shows the network binding of a typical Windows 98 system. Notice that the NetBIOS protocol has not been bound to the TCP/IP protocol and network controller. Binding this protocol introduces the potential for a security problem in this system.
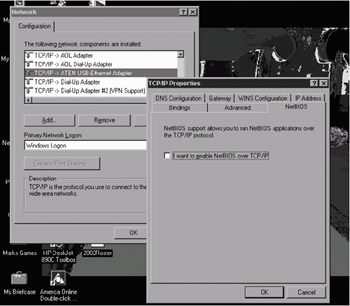
Figure 5.2: Network binding in a Windows 98 systemNetBEUI NetBEUI is a proprietary protocol developed by Microsoft for Windows networks. If your entire network is configured for NetBEUI, your network will be almost invulnerable to outside attack. This is because NetBEUI is not routable, and you would not be able to connect it to an outside network using a router. Tools such as Network Neighborhood, Explorer, and file sharing use NetBIOS for communications. Virtually all internal networking functions will operate properly if NetBEUI is used for internal networking. NetBEUI was not designed to provide any security capabilities, and it discloses a great deal of information in its packets about system configuration, services running, and other information that can be used to identify weaknesses in a system. NetBEUI, however, is not intended for large networks and is less efficient than IPX/SPX or TCP/IP in a large network.
TCP/IP TCP/IP is vulnerable to all of the threats that were discussed in Chapter 2, "Know Your Enemy." If your system is connected to the Internet, or other large-scale networks, the security of the system is tied to the vulnerability of the TCP/IP network protocol. The current implementations of TCP/IP are relatively secure. Earlier versions of TCP/IP, as implemented by Microsoft, Novell, Apple, and other vendors had a huge number of technical problems and security vulnerabilities. The security of the network, regardless of the manufacturer, is only as good as the implementation that the manufacturer accomplishes.
IPX/SPX IPX/SPX is a very efficient, routable protocol that was originally designed for use with Novell NetWare systems. The routers in use today do not generally route IPX/SPX protocol unless specifically configured to do so. NetBIOS can be bound to IPX/SPX, and it will not be vulnerable to external attack, unless this protocol is routed.
Microsoft has been suggesting that TCP/IP be the primary network protocol used in networks for several years, and they are concentrating more effort in making this protocol secure.
Applications such as Netscape, Internet Explorer, and Office are susceptible to exploits. Make sure that all of your applications are up to the current release level, and that all security patches have been installed.
Microsoft Windows 9x
The Windows environment has without a doubt been one of the most successful operating systems undertaken by any company. Windows continues to be one of the most popular operating systems ever made. Windows 98 was installed on virtually every desktop computer that was manufactured for several years, and it is one of the most popular operating systems ever sold. Windows ME is a minor enhancement of Windows 98, and it suffers from the same security problems as Windows 9x products. Windows 9x products were not intended to be secure, and they have very few security mechanisms designed into them.
| Note | Windows 9x systems should always be used behind some kind of firewall. These systems were not designed to be used in a hostile environment. |
There are several very effective things you can do to improve the security of these types of systems. The process involves network configuration, managing services, file sharing, and keeping applications up to date.
Despite your best efforts, you have been unable to get several of your Windows 98 clients to move to newer environments. These users feel that it is not worth the trouble, and their stuff works fine the way it is. You have a remote network that is connected using a VPN through the Internet. Several clients on both sides of the VPN use Windows 98 systems. How can you ensure their security?
The major weakness in this type of situation, which is very common, is that NetBEUI traffic is probably being passed between the two networks. This traffic is susceptible to sniffing. Make sure that your VPN uses a strong encryption method, such as IPSec. Doing so will provide you a reasonable chance of securing this network.
Microsoft Windows NT 4
Windows NT 4 has been used as a server and a workstation product since the mid-1990s. Windows NT 4 is considered by many to be the most secure product that Microsoft has released. It has had six major updates or service packs applied, and it seems to run extremely reliably. Windows NT 4 has also been approved to effectively run at the EAL 3 level.
| Note | Windows NT 4.0 achieved TCSES C2 certification in 1999. Previously, Windows NT 3.5 and Windows NT 3.51 also achieved this certification. This is equivalent to EAL 3 certification. They are the only operating systems offered by Microsoft that can make this claim to date. |
Windows NT 4 is a good, solid platform for servers. The major deficiencies that exist in Windows NT 4 are the applications that are shipped with it. Windows NT provides RAS, WWW services, FTP, and file sharing. Make sure that all of the products are up to date with the latest updates or security revisions. The last update for Windows NT 4 was announced as Service Pack (SP) 6. This service pack addresses most of the known security problems with Windows NT 4. Microsoft says that SP 6 is the last update it will provide for Windows NT 4.
Make sure that all unneeded services are turned off. To do this you must use the Control Panel. The other area of concern involves account policies; make sure that password policies are set up in the account policy screen to reflect the organizational standards.
Windows NT 4 includes extensive error logging, systems logs, and other tools to make security management an easier task. Security and access groups are supported, as well as individual file access and user permissions.
Microsoft Windows 2000
Windows 2000 entered the market at the millennia. Windows 2000 includes workstation and several server versions. These products have been accepted by the market, and they offer reasonable security when updated. Windows 2000 provides a Windows Update icon on the Start menu. This icon allows you to connect to the Microsoft website and automatically download and install updates. A great number of security updates are available for Windows 2000—make sure they are applied.
| Note | While this book was being written, Microsoft was working on EAL4 certification for Windows 2000. |
The server and workstations products operate in a similar manner to its predecessor Windows NT 4. These products seem to run into the most problems from a security aspect when they are bundled with products that Microsoft has included with them.
Some of the more attack-prone products include IIS, FTP, and the other common web technologies available. Make sure these products are disabled if they are not needed, and kept up to date with the most recent security and service packs. Many security updates have been issued for Windows 2000. The Microsoft TechNet and Security websites provide a number of tools, whitepapers, and materials to help secure Windows 2000 systems.
Windows 2000 includes extensive system logging, reporting and monitoring tools. These tools help make the job of monitoring security easier than on Windows 9x clients. Windows 2000 provides a great deal of flexibility in managing groups of users, security attributes, and access control to the environment.
The Event Viewer is the major tool for reviewing logs in Windows 2000. Figure 5.3 shows an example event viewer. A number of different types of events can be logged. Administrators have the ability to configure the level of events that are logged.
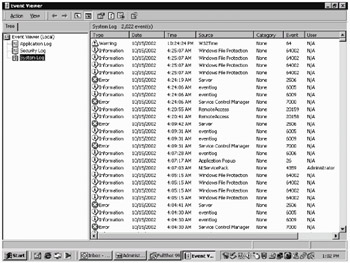
Figure 5.3: Event view log of a Windows 2000 system
Windows 2000 servers can run a product called Active Directory (AD), which allows control of security configuration options of Windows 2000 systems in a network. Unfortunately, the full power of AD does not work unless all of the systems in the network are running Windows 2000 or higher.
Microsoft Windows XP
Windows XP is the newest entry into the field by Microsoft. Windows XP functions as both a replacement for the Windows 9x family, and Windows 2000. There are currently two versions of XP: Home and Professional.
The Home version of XP is intended to specifically replace Windows 9x clients. XP Home can be installed as either an upgrade from Windows 9x or as a fresh installation on new systems.
Windows XP Professional is designed to be an upgrade for Windows 98 in the corporate environment. Windows 98 systems could not take advantage of the security capabilities of a Windows NT–based or 2000-based network. Many people use Windows 98 at home, and they want the same capabilities at the office. Windows XP provides this capability in a standard format to both home users and corporate users. Windows XP Professional can take advantage of Windows 2000 servers running AD.
| Note | Microsoft recommends that you have your antivirus software installed and running before you begin an update from Windows 9x to Windows XP. During the upgrade, the system will need to make online connections to Microsoft. This connection could potentially introduce vulnerabilities into the system. |
Windows XP is the newest product in the Microsoft product line. With the increased emphasis that Microsoft has announced it is making toward security, it is reasonable to expect that they will be working very hard to make this product secure.
Windows .NET Server 2003
Microsoft has announced the replacement product for Windows 2000 Server. This product is .NET Server. Microsoft indicates that this product will address all of the major issues that presented themselves with earlier products. Specifically, Microsoft is introducing the following features (according to their press releases):
-
Internet connection firewall
-
Secure authentication (locally and remotely)
-
Secure wireless connections
-
Software restriction policies
-
Secure Web Server (IIS 6)
-
Encryption and cryptography enhancements
-
Improved security in VPN connections
-
PKI and X.509 certificate support
In short, they intend to make a product that is both secure and flexible.
UNIX/Linux
The UNIX environment and its derivatives are some of the most installed server products in the history of the computer industry. Over a dozen different versions of UNIX are available; the most popular is a product called Linux.
UNIX began its journey to stardom in the 1970s. The product designers took an open-systems approach, meaning that the entire source code for the operating system is readily available for most versions. This open source philosophy has allowed tens of thousands of programmers, computer scientists, and systems developers to tinker and improve on the product.
| Note | In June 2002, the National Security Agency released a set of enhancements to provide additional security to Linux Systems. These enhancements are bundled in a set of tools called Security Enhanced Linux (SELinux). SELinux uses mandatory access control methods as part of the mechanisms for improved security. |
Linux, and UNIX when properly configured, provide a high level of security. The major challenge with the UNIX environment is configuring it properly.
UNIX includes almost every protocol, service, and capability that computer scientists have designed. Most of the services should be turned off when they are not needed. Turn them off by running a script during system startup. The script will configure the protocols, and it will determine which services are started.
All UNIX security is handled at the file level. Files and directories need to be established properly in order to ensure correct access permissions. The file structure is hierarchical by nature, and when a file folder access level is set, all of the subordinate file folders usually inherit this access. This inheritance of security is established by the systems administrator or by a user who knows how to adjust directory permissions.
Keeping patches and updates current is essential in the UNIX environment. You can accomplish this by regularly visiting the developer's website and downloading the latest fixes.
Linux also provides a great deal of activity logging. These logs are essential in establishing patterns of intrusion.
An additional method of securing Linux systems is accomplished by adding TCP wrappers. TCP wrappers are a low-level logging package designed for UNIX systems. Wrappers provide additional detailed logging on activity using a specific protocol. Each protocol or port must have a wrapper installed for it. Wrappers are then used to record activities and deny access to the service or server.
| Note | Linux is considered an open source program. This means that all of the source code for the system is available for examination, and modification. This typically requires a high-level of programming expertise. Many vendors such as SUN, IBM, and HP have implemented UNIX-based or Linux-based systems to simplify the process. In most cases, they make the modifications available to customers. According to many industry analysts, open source is a "good thing." |
Novell NetWare
Novell was one of the first companies to introduce a network operating system. Early versions of NetWare provided the ability to connect PCs together into primitive but effective LANs. The most recent version of NetWare, Version 6, includes file sharing, print sharing, support for most clients, and good security.
NetWare provides a server product. The server has its own operating system. The server product also includes client applications for a number of different types of systems, including Macintoshes and PCs.
NetWare security is accomplished by a combination of access controls, user rights, security rights, and authentication. NetWare version 6 appears to be primarily susceptible to DoS types of attacks, as opposed to exploitation and other attacks.
The server services can be extended by adding NetWare Loadable Modules (NLMs) to the server. These modules allow executable code to be patched or inserted into the operating system.
| Note | The heart of Novell security is the Network Directory Service (NDS) or eDirectory (for newer Novell implementations). NDS and eDirectory maintain information about rights, access, and usage on a NetWare-based network. |
A number of additional capabilities make NetWare a product worth evaluating in implementation. These include e-commerce products, document retrieval, and enhanced network printing.
IBM
IBM supports multiple operating systems and environments. The most common environments besides the Microsoft environment are AIX, OS/2 WARP, and AS/400. IBM has a great deal of experience in the computer security area because of its long involvement in government and military applications. Most of the vulnerabilities are at the applications level, as opposed to the operating system level.
Apple Macintosh
The Macintosh operating system seems to be the most vulnerable to attacks and compromises that require physical access to the computer. The network implementations seem to be as secure and capable of withstanding assault as any other systems.
Where the Macintosh security breaks down is in its access control and authentication systems. The Mac uses a simple 32-bit password encryption scheme that is relatively easy to crack. The password file is located in the preference folder. If the folder is shared, or part of a network share, the file may be vulnerable to decryption.
Mac systems also have several proprietary network protocols that are not intended for routing. Recently, Mac systems implemented TCP/IP networking as an integral part of the operating system.
The Mac systems seem to be most the most vulnerable to physical access attacks targeted through the console. The network implementations are as secure as any of the other systems discussed in this chapter.
File Systems
Several file systems are involved in these operating systems, and they have a high-level of interoperability between them—from a network perspective, that is.
Through the years, the different vendors have implemented their own sets of file standards. Some of the more common file systems include:
Microsoft FAT Microsoft's earliest file system was referred to as File Allocation Table (FAT). FAT is designed for relatively small disk drives. FAT was first upgraded to FAT-16, and finally to FAT-32. Fat-32 allows large disk systems to be used on Windows systems. FAT allows only two types of protection. These two methods are share level, and user level access privileges. If a user has write or change access to a drive or directory, they have access to any file in that directory. This is very unsecure in an Internet environment.
Microsoft NTFS The New Technology File System (NTFS) was introduced with Windows NT to address security problems. With NTFS, files, directories, and volumes can each have their own security. This allows a great deal of flexibility in setting up a network. Microsoft strongly recommends that all network shares be established using the NTFS file system.
Novell NetWare Storage Services Novell, like Microsoft, implemented a proprietary file structure called NetWare File System. This system allows complete control of every file resource on a NetWare Server. The NetWare File System was upgraded to NetWare Storage Service (NSS) in version 6. NSS provides higher performance and larger file storage capacities than the NetWare File System. NSS, like its predecessor Netware File System, uses the NDS or eDirectory to provide authentication for all access.
UNIX File System The UNIX file system is a completely hierarchical file system. Each file, file system, and subdirectory have complete granularity of access control. The three primary attributes in a UNIX file or directory are Read, Write, or Execute. The ability to individually create these capabilities, as well as to establish inheritance to subdirectories, gives UNIX the highest level of security available for commercial systems. The major difficulty with UNIX is that establishing these access-control hierarchies can be time-consuming when the system is initially configured. Figure 5.4 illustrates this hierarchical file structure. Most current operating systems have embraced this method of file organization.
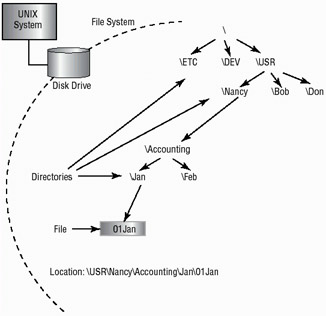
Figure 5.4: Hierarchical file structure used in Unix and other operating systemsUNIX NFS Network File Systems (NFS) is a UNIX protocol that allows systems to mount file systems from remote locations. This ability allows a client system to view the server or remote desktop storage as a part of the local client. NFS, while functional, is very difficult to secure. The discussion of this process is beyond the scope of this book. The major issue lies in the inherent trust that UNIX has of authentication processes. NFS was originally implemented by Sun Microsystems. NFS has become a standard protocol in UNIX environments.
Note Do not confuse NetWare File Systems with Network File Systems; they are two entirely different technologies.
Apple File Sharing The Apple File Sharing (AFS) was intended to provide simple networking for Apple Macintosh systems. This system used a proprietary network protocol called AppleTalk. This network is not routed through the Internet and is not considered secure. AFS allows password and access privileges to be established by the file owner. This process is similar to the UNIX file system. OS X, the newest version of the Macintosh operating system, has more fully implemented a file system that is based on the UNIX model. In general, Apple networking is considered as secure as the other implementations discussed in the section. The major weakness of the operating system involves physical control of the systems.
Each of these file system implementations requires careful consideration when implementing them in a network. The individual capabilities, limitations, and vulnerabilities need to be evaluated when you are choosing which protocols or systems to implement.
Most operating system providers support multiple protocols and methods. Evaluate them carefully to determine which protocols are suitable for your environment. Turn off any protocols that are not needed, as each protocol or file system running on a workstation or server increases your vulnerability and exposure to attack, data loss, or DoS attacks.
| Note | If at all possible, do not share the root directories of a disk drive. Doing so would allow access to system files, passwords, and other sensitive information. Establish shares off of hard drives that do not contain system files. |
Make sure that you periodically review the manufacturers' support websites and other support resources that are available to apply current updates and security patches to your systems. Doing this on a regular basis will lower your exposure to security risks.
Operating System Updates
Product updates are typically provided by operating system manufacturers. For example, Microsoft provides a series of regular updates for Windows 2000 (a proprietary system) and other applications. However, in the case of public source systems (such as Linux), the updates may come from a newsgroup, the manufacturer of the version you are using, or a user community.
In both cases, public and private, updates help keep operating systems up to the most current revision level. Researching updates is important, and when possible so is getting feedback from other users before you install an update. There have been a number of cases where a service pack or update has actually rendered a system unusable. Make sure your system is backed up before you install updates.
| Note | Windows NT 4 Service Pack 3 changed the file system and Registry structure of Windows NT. This update initially had problems that caused many servers to crash. The changes unfortunately could not be backed out, and they forced many administrators to reinstall and configure the operating system and applications. Make sure you test updates on test systems before you implement them on production systems. |
Three different types of updates are discussed here: hotfixes, service packs, and patches.
Hotfixes
The term hotfix is used to describe a repair that is made to a system during normal operation. A hotfix might entail moving data from a bad spot on the disk and remapping the data to a new sector. This would prevent data loss and loss of service. This type of repair may also involve reallocating a block of memory if, for example, a memory problem occurred. This would allow the system to continue normal operations until a permanent repair could be made. Microsoft refers to a bug fix as a hotfix. This involves the replacement of files with an updated version.
Service Packs
A service pack is a comprehensive set of fixes consolidated into a single product. A service pack may be used to address a large number of bugs or to introduce new capabilities in an operating system. When installed, a service pack will usually contain a number of file replacements. Make sure you check related websites to verify that the service pack works properly. Sometimes a manufacturer will release a service pack before it has been thoroughly tested. An untested service pack can cause extreme instability in an operating system or, even worse, render it inoperable.
One large operating system manufacturer released a service pack for a popular server product three times before they got it right. This service pack, when installed caused many systems to become inoperable. The service pack took down the entire server farm of a large ISP. Many users lost their servers for several days while everything was sorted out and repaired.
Patches
A patch is a temporary or "quick fix" to a program. Patches may be used to temporarily bypass a set of instructions that have malfunctioned. Several operating systems manufacturers issue patches that can either be manually applied or applied using a disk file to fix a program.
When you are working with customer support on a technical problem with an operating system or applications product, customer service may have you actually go into the code and make alterations to the binary files that run on your system. Double-check each change to prevent catastrophic failures due to improperly entered code.
| Note | Patches, while fixing problems, also add the potential for new problems. Most manufacturers would rather release a new program than patch an existing program. A new release can repair multiple problems. |
When more data is known about the problem, a service pack, or hotfix might be issued to fix the problem on a larger scale. Patching is becoming less common, as most operating system manufacturers would rather release a new version of the code rather than patch it.
|
|
EAN: 2147483647
Pages: 167