4.3 Secret key cryptography
4.3 Secret key cryptography
Secret key cryptography refers to traditional cryptography. In this kind of cryptography, a secret key is established and shared between communicating peers, and the key is used to encrypt and decrypt messages on either side. Because of its symmetry, secret key cryptography is often referred to as symmetric cryptography.
The use of a secret key cryptosystem is overviewed in Figure 4.1. We assume that A on the left side wants to send a confidential message to B on the right side. A therefore shares a secret key K with B. This key may be preconfigured manually or distributed by a key distribution center (KDC). Note that during its initial distribution, K must be secured in terms of confidentiality, integrity, and authenticity. This is usually done by having the KDC encrypt K with secret keys that it shares with A and B, respectively. With regard to the use of cryptographic algorithms and protocols, persons are usually represented by cryptographic implementations (e.g., crypto boxes that implement an encryption algorithm). In Figure 4.1, the cryptographic implementations are represented with black rectangles that are located in front of A or B, respectively. A (or the crypto box representing A) encrypts a plaintext message P by applying an encryption function E and the key K , and sends the resulting ciphertext C = E K ( P) to B. On the other side, B (or the crypto box representing B) decrypts C by applying the decryption function D and the key K . B therefore computes D K ( C ) = D K (E K (P)) = P , and recovers the plaintext P accordingly .
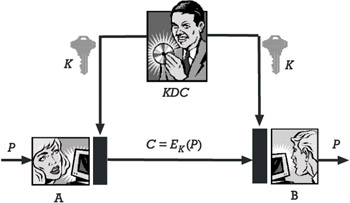
Figure 4.1: The use of a secret key cryptosystem.
Secret key cryptography has been in use for many years in a variety of forms. Two basic categories of secret key cryptosystems are block ciphers and stream ciphers . As their names suggest, block ciphers operate on blocks of data (e.g., 64 bits), whereas stream ciphers operate on data one bit or byte at a time.
Examples of secret key cryptosystems that are in widespread use are itemized in Table 4.1 and overviewed next . 3 Again, you may refer to [4] for a comprehensive description of the cryptosystems and the corresponding encryption and decryption algorithms.
4.3.1 DES
The Data Encryption Standard (DES) is still the most well-known and widely deployed secret key cryptosystem in use today. It was originally designed by a group of researchers at IBM and published as Federal Information Processing Standard (FIPS) 46 in 1977 [20]. As such, it has been used for the encryption of unclassified information by the U.S. National Institute of Standards and Technology (NIST) for almost a quarter of a century.
| Algorithm Name | Main Mode | Effective Key Length |
|---|---|---|
| DES | Block cipher | 56 bits |
| Triple-DES (3DES) | Block cipher | 112 or 168 bits |
| IDEA | Block cipher | 128 bits |
| SAFER | Block cipher | 64 or 128 bits |
| Blowfish | Block cipher | Variable from 1 up to 448 bits |
| CAST-128 | Block cipher | 128 bits |
| RC2, RC5, and RC6 | Block cipher | Variable from 1 up to 2,048 bits |
| RC4 | Stream cipher | Variable from 1 up to 2,048 bits |
DES operates as a block cipher with 64-bit blocks, 16 rounds, and a variable key length up to 56 bits. In electronic code book (ECB) mode, DES encrypts data in discrete blocks of 64 bits. To improve its cryptographical strength, DES is often used in cipher block chaining (CBC) mode. In this mode, the encryption of each block depends on the contents of the previous one, preventing an interloper from tampering with the message by rearranging the encrypted blocks. Furthermore, there are two modes that can be used to turn DES into a stream cipher: cipher feedback (CFB) mode and output feedback (OFB) mode.
DES s 56-bit effective key length was sufficiently secure during its first two decades of operation, but it is far too short today. In fact, it has become feasible to perform an exhaustive key search in a reasonable amount of time. [4]
4.3.2 Triple-DES
One way to improve the cryptographical strength of a secret key cryptosystem with limited key length (e.g., DES) is to apply the algorithm multiple times. Applying the algorithm twice does not improve the situation, because of the existence of a specific cryptanalytical attack. [5] Consequently, at least three applications are necessary for a security improvement, and the threefold application of DES is called Triple-DES (3DES). It can be used with two or three different keys, and the resulting secret key cryptosystems are usually called two-key 3DES or three-key 3DES, respectively. Many contemporary applications use 3DES as a replacement for DES. Note, however, that the use of 3DES is not very efficient (in fact, it is approximately three times slower than DES), and that there are many real-time applications that require faster encryption algorithms.
4.3.3 IDEA
The International Data Encryption Algorithm (IDEA) was developed by Xuejia Lai and James Massey in the early 1990s at the ETH Zurich, Switzerland [21]. IDEA is a 64-bit block cipher that uses a 128-bit key. The algorithm is patented and must be licensed for commercial use.
4.3.4 SAFER
After having developed IDEA, James Massey proposed SAFER K-64 and SAFER K-128. As their names suggest, SAFER K-64 uses a 64-bit key [22], whereas SAFER K-128 uses a proprietary key schedule algorithm that is able to accommodate 128-bit keys. Furthermore, SAFER K-64 uses 6 rounds, whereas SAFER K-128 recommends 10 rounds (12 maximum).
4.3.5 Blowfish
The Blowfish algorithm was developed by Bruce Schneier [23]. It is a DESlike encryption algorithm that can be used as a block cipher with 64-bit blocks, 16 rounds, and variable key lengths up to 448 bits.
4.3.6 CAST-128
The term CAST refers to a design procedure for a family of DES-like encryption algorithms with variable key size and numbers of rounds. In RFC 2144, a 128-bit CAST encryption algorithm is specified [24]. This algorithm is called CAST-128 and is used and widely deployed for Internet applications.
4.3.7 RC2, RC4, RC5, and RC6
RC2, RC4, RC5, and RC6 are secret key cryptosystems with variable key lengths that were designed by Ronald L. Rivest for RSA Security, Inc.:
-
RC2 is a block cipher (block size is 64 bits), designed as a replacement for DES.
-
RC4 is a stream cipher.
-
RC5 is a block cipher that is configurable with regard to word length and number of rounds (in addition to the ley length).
-
RC6 is a recent proposal to improve RC5.
The RC2 and RC4 algorithms were originally protected by trade secrets, but were disassembled, reverse-engineered, and anonymously posted to a Usenet newsgroup in 1996 and 1994, respectively.
4.3.8 AES
In November 2001, the U.S. NIST officially released FIPS 197 that specifies an Advanced Encryption Standard (AES) to replace DES [25]. The AES emerged from a proposal called Rijndael that originated from Belgium. You may refer to http://www.esat.kuleuven.ac.be/~rijmen/rijndael for more information about the Rijndael algorithm. In addition, there is an official AES home page [6] hosted by the U.S. NIST.
[4] Note that the cryptosystems are randomly chosen and that there are many others one may discuss.
[5] http://www:eff.org/descracker
[6] The attack is called meet-in-the-middle attack. It requires that a known plaintext is encrypted with all possible keys, and that a corresponding ciphertext is decrypted with all possible keys. If an encryption result matches a decryption result in the middle, a key candidate is found (that s why the attack is called meet-in-the-middle attack). The key candidate must be verified using another plaintext-ciphertext pair.
EAN: 2147483647
Pages: 142