Delegating Control of an OU
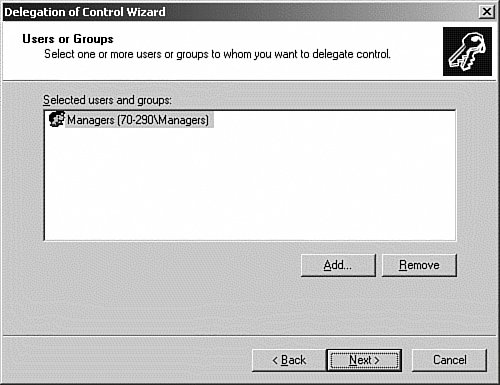
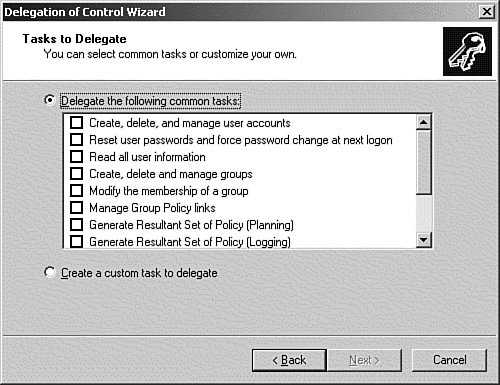
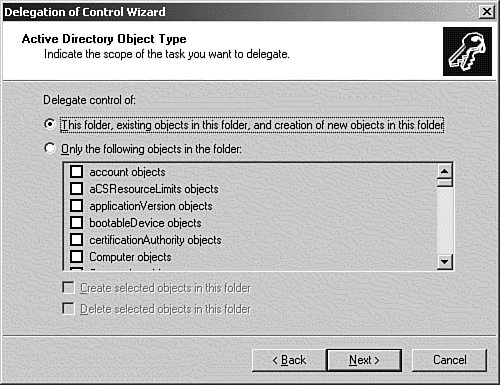
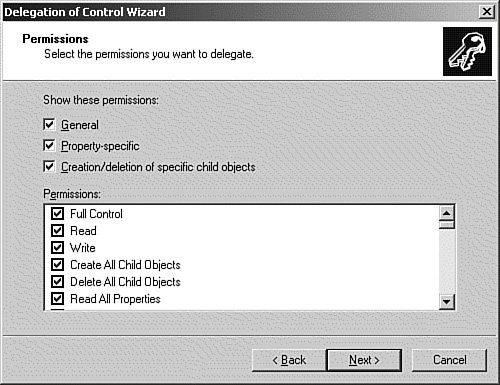
| Inheritance and delegation are probably two of the most important features of Active Directory management. We already discussed how inheritance is used to allow the permissions set on a parent object to be automatically propagated to the child objects. This simplifies the administrative tasks of the directory because the network administrator does not have to manually assign permissions on each object. Through the use of delegation, the network administrator can grant specific administrative rights for containers and objects to users or groups. This allows selected users to perform some of the management and administrative tasks that would normally be the responsibility of the network administrator. Properly used, this has the potential to lighten the administrator's workload and push specific administrative duties down the hierarchy closer to the end user, where they can usually be performed more efficiently. For example, if you have a department that prefers to manage itself, either for security or political reasons, you can create an OU that contains all the users, computers, and resources for that department. Then you can assign full control for that OU to an administrators group that consists of the users who are the designated administrators of that department. In Windows NT, the domain was the administrative and security boundary. Starting with the Windows 2000 versions of Active Directory, although the domain can be used in the same way, it is advantageous to use the OU in this role because OUs are easier to create, delete, move, and modify than domains are. Windows Server 2003 allows the administrator to delegate the ability to create, delete, or modify objects at the container, OU, object, or property level. In most cases, it will be best to not assign administrative control at lower than the container or OU level. Note: Containers? If you look closely in the left pane of the Active Directory Users and Computers MMC, you will notice that all the folder icons are not the same. Some icons are plainthese are containers. The other icons have an open folder label on themthese are OUs. Most of the containers are automatically created by the operating system, and control of some of them cannot be delegated. The Delegation of Control Wizard should be used to delegate administrative control of OUs and containers. The wizard allows you to select the OUs and objects to be controlled, the user or group to which you want to delegate control, and the permissions to access and modify objects. To grant permissions at the property level, you must manually configure the properties of the objects. The Delegation of Control Wizard is available in the Active Directory Users and Computers snap-in. It will lead you step by step through the process of delegating control at the OU or container level. To see how the wizard accomplishes these types of tasks, follow the procedure outlined in Step by Step 8.6 to delegate control of the Kansas City\Users OU to members of the Managers Group.
The proper use of delegation can also enhance network security. In Windows NT, few of the administrative tasks could be assigned to other users. Because of this, it was necessary to give more people user accounts with administrative access than it was probably wise to do. By being able to delegate specific tasks and control the level of access at a granular level, you can limit the number of accounts that are members of the Domain Admins group to a highly trusted few. Exam Alert: Limitations of the Delegation of Control Wizard The Delegation of Control Wizard can only apply permissions, not remove them. In addition, if you run the wizard multiple times, the permissions assigned are cumulative, and cannot be viewed using the wizard. To view and remove the permissions, you will have to view the Security tab for the object that you assigned permissions on using the wizard. Watch for Delegation of Control Wizard questions on the exam. |
EAN: 2147483647
Pages: 219