Active Directory Sites and Services Snap-in
|
|
Active Directory Sites and Services Snap-in
The Active Directory Sites and Services snap-in is the main GUI tool that allows an administrator to configure Active Directory as a distributed network service. (Other administrative tools consider Active Directory as a whole, at a logical level.) You might almost forget about this snap-in in a small, single-site network with just a few domain controllers. However, in large networks with many sites, this snap-in becomes one of the essential administrative tools.
The Active Directory Sites and Services snap-in allows you to perform the following operations:
-
Designate domain controllers as Global Catalog servers.
-
Modify forest replication topology (create/delete sites, subnets, links, link bridges, and connections); view replication contexts.
-
Enable caching of universal group membership.
-
Design a location scheme used by the printer, computer, site, and subnet objects (for detailed information, search in the Help and Support Center for "Enabling printer location tracking").
-
Trigger intra-site and inter-site replication events.
-
Trigger the Knowledge Consistency Checker (KCC) to re-generate replication topology.
-
Change schedules and intervals for intra-site and inter-site replications.
-
Assign costs to links.
-
Designate domain controllers as bridgehead servers.
-
Delegate control over sites, subnets, servers, and other containers to users or groups.
-
Define security and auditing settings for various replication topology objects.
-
Select Group Policy Objects (GPO), link GPOs to sites, and start the Group Policy Object Editor snap-in for editing GPO.
-
Select LDAP query policies.
In Fig. 7.17, you can see the main window of the Active Directory Sites and Services snap-in, which displays practically all major elements of network configuration: sites, subnets, inter-site links, connections, and servers (domain controllers). Use and configuration of these elements is discussed in other chapters of the book, since it is more advantageous to describe these questions in the context of specific administrative tasks rather than in isolation.
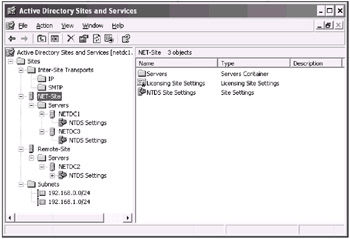
Fig. 7.17: An example of a simple network with two sites
Caching Universal Group Membership
Domain controllers running Windows .NET can store universal group membership information locally, and refresh it periodically (by default, every 8 hours). This diminishes the necessity to have a Global Catalog server in branch office locations; as well, it reduces network traffic that occurs when users are authenticated in a forest.
To enable that option:
-
In the tree pane, select a site where GC server is not designated.
-
Right click the corresponding NTDS Site Settings object (of the nTDSSiteSettings type) and select the Properties command on the context menu.
-
On the Site Settings tab of the Properties window, check the Enable Universal Group Membership Caching box and select a site from the Refresh cache from list (Fig. 7.18).

Fig. 7.18: Enabling universal group caching -
Click Apply and OK.
|
|
EAN: 2147483647
Pages: 154