Bot Software
An underreported threat, but one that you should take very seriously, is that which bot software or automated remote attack tools pose. Similar to a worm and a Trojan, bot software automatically scans for vulnerable systems and then installs itself, giving a cracker control over the system. The cracker can order the bot software to attack other computers or use it to steal information from the infected computer(see Figure 7-11).
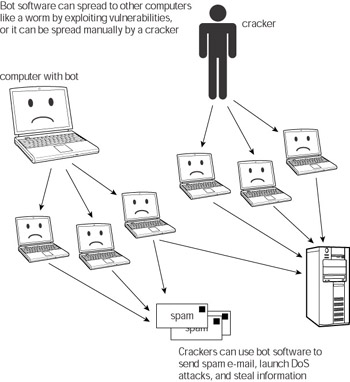
Figure 7-11: Bot software
Often, these bots run undetected, and users may be oblivious to the fact that the bot has compromised their computers. Because bots attempt to spread in a stealthier manner and don’t scan huge numbers of random IP addresses while searching for targets, they don’t create the amount of network noise that worms or blended threats do. This makes bots harder to detect through network traffic analysis.
Bots are becoming more sophisticated, incorporating more programmable functions so that attackers can use them for a number of different tasks. Some of these include:
-
Using multiple bot-infected clients to launch denial of service (DoS) attacks on Web sites
-
Using bots to spread other malicious software, including worms
-
Using bots to send unsolicited commercial e-mail (spam)
Cross-Reference Antispyware software is a good idea. There are several products available that will detect a number of different bots, Trojan programs, keyloggers, and more. For more information about spyware and ways to protect yourself against it, see the section “Introducing Spyware.”
Bot software can spread via multiple methods. Depending on the particular bot, the best strategy for protecting yourself is to do all of the following:
-
Install antivirus software, and keep it updated
-
Install and use a firewall
-
Patch your system and applications and keep them up to date
-
Install antispyware software
-
Don’t launch unexpected or otherwise suspect e-mail attachments
EAN: 2147483647
Pages: 145