Lesson 3: Managing Certificates
Once you start issuing certificates, or clients request that you issue them, management of certificates becomes an important issue. In this lesson, you learn how to manage certificates, revoke a certificate, and implement an Encrypting File System (EFS) recovery policy.
After this lesson, you will be able to
- Describe the steps to revoke a certificate
- Describe how to issue an EFS recovery policy
Estimated lesson time: 30 minutes
Revoked Certificates
When a certificate is marked as revoked, it is moved to the Revoked Certificates folder. The revoked certificate appears on the CRL the next time it is published. Certificates revoked with the reason code Certificate Hold can be unrevoked, left on Certificate Hold until they expire, or have their revocation reason code changed. This is the only reason code that allows you to change the status of a revoked certificate. It is useful if the status of the certificate is questionable, and is meant to provide some flexibility to the CA administrator.
Issued Certificates
In the details pane, examine the certificate request by noting the values for requester name, requester e-mail address, and any other fields that you consider critical information for issuing the certificate.
Pending Requests
In the details pane, examine the certificate request by noting the values for requester name, requester e-mail address, and any other fields that you consider critical information for issuing the certificate.
Failed Requests
Failed certificate requests should only occur when a member of the Cert Publishers or Administrators groups denies a certificate request.
How a Certificate Is Issued
When a certificate is presented to an entity as a means of identifying the certificate holder (the subject of the certificate), it is useful only if the entity receiving the certificate trusts the issuing CA. Certificates are issued under the following processes:
- Key generation. The individual or applicant requesting certification generates key pairs of public and private keys. The exception to this is personal digital certificates, in which case the CA generates the public and private keys and sends them to the end user.
- Matching of policy information. The applicant packages up the additional information necessary for the CA to issue the certificate (for example, proof of identity, tax ID number, e-mail address, and so on). The precise definition of this information is up to the CA.
- Sending of public keys and information. The applicant sends the public keys and information (often encrypted using the CA's public key) to the CA.
- Verification of information. The CA applies whatever policy rules it might require to verify that the applicant should receive a certificate.
- Certificate creation. The CA creates a digital document with the appropriate information (public keys, expiration date, and other data) and signs it using the CA's private key.
- Sending or posting of certificate. The CA may send the certificate to the applicant or post it publicly. The certificate is loaded onto the individual's system.
Certificate Revocation
Certificate authorities publish CRLs containing certificates that have been revoked by the CA. The certificate holder's private key may become compromised, or false information may be used to apply for the certificate. CRLs provide a way of withdrawing a certificate after it has been issued. CRLs are made available for downloading or online viewing by client applications.
To verify a certificate, all that is necessary is the public key of the CA and a check against the revocation list published by that CA. Certificates and CAs reduce the public-key distribution problem of verifying and trusting one (or more) public keys per individual. Instead, only the CA's public key must be trusted and verified, and then that can be relied on to allow verification of other certificates.

Practice: Revoking a Certificate
In this practice, you will revoke the certificate you obtained when completing the Practice in Lesson 2.
Exercise 1: Revoking the Certificate from Lesson 2
- Open the Certificate Authority Manager.
- Right-click your request under Issued Certificates, point to All Tasks, and then click Revoke Certificate.
- When prompted for a reason code, select Cease Of Operation. Click Yes.
- In the left pane, click Revoked Certificates.
Notice your request has been revoked, as illustrated in Figure 15.5.
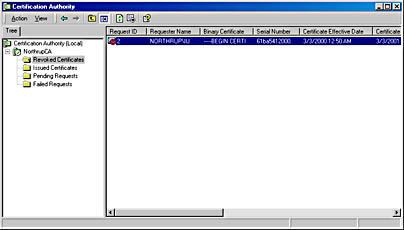
Figure 15.5 Certificate Authority revoked certificates
EFS Recovery Policy
Data recovery is available for the EFS as a part of the overall security policy for the system. For example, if you should ever lose your file encryption certificate and associated private key (through disk failure or any other reason), data recovery is available through the person who is the designated recovery agent. Or, in a business environment, an organization can recover data encrypted by an employee after the employee leaves.
EFS recovery policy specifies the data recovery agent accounts that are used within the scope of the policy. EFS requires an encrypted data recovery agent policy before it can be used, and it uses a default recovery agent account (the Administrator) if none has been chosen. In a domain, only members of the Domain Admins group can designate another account as the recovery agent account. In a small business or home environment where there are no domains, the computer's local Administrator account is the default recovery agent account. Only the Administrator account can change local recovery policy for a computer.
A recovery agent account is used to restore data for all computers covered by the policy. If a user's private key is lost, a file protected by that key can be backed up, and the backup sent by means of secure e-mail to a recovery agent administrator. The administrator restores the backup copy, opens it to read the file, copies the file in plaintext, and returns the plaintext file to the user using secure e-mail again.
As an alternative, the administrator can go to the computer that has the encrypted file, import his or her recovery agent certificate and private key, and perform the recovery there. However, this might not be safe and is not recommended because of the sensitivity of the recovery key—the administrator cannot afford to leave the recovery key on another computer.

Practice: Changing a Recovery Policy
In this practice, you change the recovery policy for the local computer. Before changing the recovery policy in any way, you should first back up the recovery keys to a floppy disk. In a domain, a default recovery policy is implemented for the domain when the first domain controller is set up. The domain administrator is issued the self-signed certificate, which designates the domain administrator as the recovery agent. To change the default recovery policy for a domain, log on to the first domain controller as an administrator.
NOTE
To complete this practice, you must have the appropriate permissions to request the certificate and the CA must be configured to issue this type of certificate.
Exercise 1: Changing the Recovery Policy for the Local Computer
- Click Start, click Run, type mmc /a and then click OK.
- On the Console menu, click Add/Remove Snap-In, and then click Add.
- Under Snap-In, click Group Policy, and then click Add.
- Under Group Policy Object, make sure that Local Computer is displayed, click Finish, click Close, and then click OK.
- In Navigate Local Computer Policy\Computer Configuration\Windows Settings\Security Settings\Public Key Policies, right-click Encrypted Data Recovery Agents, and then click one of the following options:
- The Add command designates a user as an additional recovery agent using the Add Recovery Agent wizard.
- The Delete Policy command deletes this EFS policy and every recovery agent. The effect of deleting the EFS policy and every recovery agent is that users will not be able to encrypt files on this computer. The computer issues a default self-signed certificate that designates the local administrator as the default recovery agent. If you delete this certificate without another policy in place, the computer has an empty recovery policy. An empty recovery policy means that no one is a recovery agent. This turns EFS off, thereby not allowing users to encrypt files on this computer.
- To make changes to the File Recovery certificate, start by selecting Encrypted Data Recovery Agents in the left pane, as shown in Figure 15.6. Right-click the certificate in the right pane, and then click Properties. For example, you can give the certificate a friendly name and enter a text description.
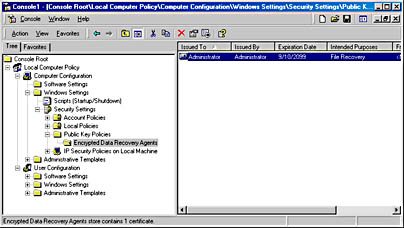
Figure 15.6 Group Policy for EFS recovery
Lesson Summary
You can manage certificates using the Certificate Authority snap-in for the Microsoft Management Console (MMC). Certificates revoked with the reason code Certificate Hold can be unrevoked. They can also be left on Certificate Hold until they expire or have their revocation reason code changed. Data recovery is available for the EFS as a part of the overall security policy for the system.
EAN: N/A
Pages: 244