Section 7.2. Directory Services Defined
7.2. Directory Services DefinedHistorically, Unix systems have stored user and password information in "flat" text files located in the /etc directory and let applications access that data directly. This works well enough when you only have to administer one machine. However, in the 1980s, with the advent of the Unix-based workstation and the proliferation of personal computers allowing mass deployments of computers in offices and universities, managing user information on each machine became a serious administration problem. The problem only became worse as administrators tried to cope not just with setting up users, but setting up printers, servers, and other network resources. Various solutions have been invented over the years to alleviate this problem. Sun introduced Network Information Services (NIS, also known as "Yellow Pages"), NeXT developed NetInfo , Novell built a business around NetWare (and failed), and Microsoft ended up taking it away from Novell with Active Directory. All these solutions have a common goal: to centralize the information needed so that a group of users across a variety of machines can be managed effectively. When development on Mac OS X started, Apple inherited the NetInfo code that came with NEXTSTEP. The company knew it was not going to be enough to just provide for management of homogenous networks of Macs, so Apple set out on a path to build a set of technologies collectively known as Open Directory. These technologies brought support for the Lightweight Access Directory Protocol (LDAP) and Kerberos (a network authentication standard developed at the Massachusetts Institute of Technology) to the operating system. Starting with the release of Panther, Mac OS X interoperates with all the major directory services systems in use including Active Directory, as shown in Figure 7-1. The way in which applications use Open Directory is illustrated in Figure 7-1. When a native Mac OS X application, such as the login window, needs to authenticate a user, it calls into Open Directory. It then authenticates the user information against whatever data store it is configured to use. To accommodate Unix-based command-line applications, the BSD authentication routines have been modified to use PAM, which then uses Open Directory to authenticate against. Likewise, whenever any system component needs to find a resource, such as a network file share, it uses Open Directory. The end result is a system in which the applications that need authentication and configuration data can get it without knowing, or even caring, where that data is stored. It should be noted that it's not just end-user applications that use this abstracted data. The data about a user that's obtained from Open Directory is used by every part of the system. For example, the filesystem permissions scheme described in Chapter 8 relies on the user and group information stored in Open Directory. Figure 7-1. How applications and Open Directory fit together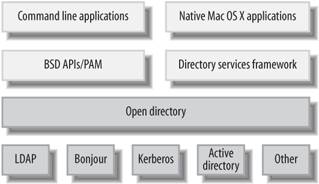 7.2.1. Kinds of Directory InformationOpen Directory can handle many different kinds of information. The following are the most common types of data that Mac OS X looks to Open Directory to provide:
7.2.2. Sources of Directory InformationOpen Directory is a flexible bridge allowing information to be obtained from many different sources. These sources fall into roughly three categories: configuration information, authentication services, and discovered services. 7.2.2.1. Sources of configuration information
7.2.2.2. Sources of authentication informationTo authenticate users, Open Directory supports the following technologies:
7.2.2.3. Sources of discovered servicesOpen Directory obtains information about network filesystems, printers, and other network devices from the following services:
|
EAN: 2147483647
Pages: 166