VPN Server Between Two Firewalls
Another configuration is when the VPN server computer is placed on the perimeter network between two firewalls. The Internet firewall, which is the firewall between the Internet and the VPN server, filters all Internet traffic from all Internet clients. The intranet firewall, which is the firewall between the VPN server and the intranet, filters intranet traffic from VPN clients.
Figure B-3 shows the VPN server on the perimeter network, between two firewalls.
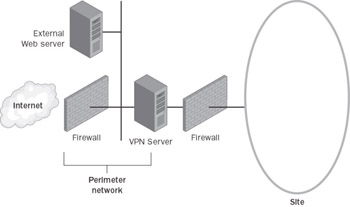
Figure B-3: The VPN server on the perimeter network, between two firewalls.
In this configuration:
-
Configure your Internet firewall and VPN server with the packet filters as described in the “VPN Server Behind the Firewall” section.
-
Configure your intranet firewall for the appropriate rules for intranet traffic to and from VPN clients according to your network security policies.
EAN: 2147483647
Pages: 128