Perimeter Denial-of-Service Protection
| The ASA/PIX Security Appliance has default protection built in for denial-of-service (DoS) attacks. However, it also provides an interface to change the parameters, if required. DoS attacks come in different flavors:
Unfortunately, DoS attacks are easy to launch and not so easy to protect against. The ASA/PIX Security Appliance, however, does have some built-in functionality to reduce the impact of the attacks. As well, you should follow some best practices to mitigate the effect of these attacks. The ASA/PIX Security Appliance mitigates against various types of DoS attacks by deploying different technologies to protect the perimeter of your network. The specific features that the ASA/PIX uses include the following:
Mitigating Network Bandwidth DoS AttacksIf an attacker has taken it upon himself to try to consume all the bandwidth on the outside of your security appliance, you will need to get your Internet security provider (ISP) involved. It would not be that difficult, depending on how much bandwidth you have available between you and your ISP, for an attacker to use several zombie machines. With these machines, attackers can start streaming data destined for your web server or your mail server until those services are no longer usable. Your ISP will have several options to help out. Most of the time, they are willing to help, because the attacks destined for you also take up bandwidth and slow down their network and the networks of their customers. Following is just a partial list of simple steps the ISP can do to help protect you under these circumstances. Most ISPs have several other options besides these that they can deploy to help stop DoS attacks:
You should always contact your ISP if you believe that you are the victim of a DoS attack so that it can deploy these methods to get you back on line as soon as possible. On your ASA/PIX Security Appliance, the default configuration called Anti-Spoofing can help during these attack conditions. Anti-Spoofing will ensure that DoS attacks are not launched from inside your own network. You should follow this procedure to enable Anti-Spoofing on your inside interface to ensure that DoS attacks are not inadvertently being launched from the inside of your security appliance:
Figure 8-9 shows the Anti-Spoofing panel with the inside interface enabled. Figure 8-9. Anti-Spoofing Panel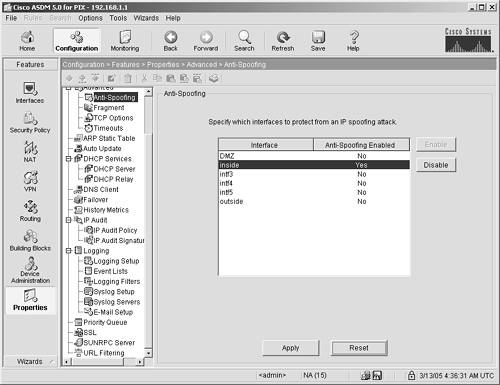 Mitigating Resource-Intensive DoS AttacksDoS attacks designed to take up system resources can, but don't usually, have the same volume of traffic as an all-out bandwidth attack described previously. These attacks are more "finesse" oriented. They are crafted attacks that try to use the features of network protocols against the devices that they are attacking. An example of this is a TCP SYN attack. In this type of attack, malicious software sends millions of requests to open network sockets on a security appliance. When a security appliance gets a SYN packet (for example, a request to open a connection), it might do the following:
If a security appliance is capable of handling only one million connections and the software running the SYN attack sends five million connections, the security appliance could conceivably crash or, at the very least, be rendered useless. To mitigate these types of attacks, the ASA/PIX Security Appliance has a mechanism built in to it that enables it to delete connections that don't have data following the acknowledgment packet after a certain amount of time. Navigate to the following ASDM panel to see the default timeouts set for the ASA/PIX Security Appliance: Configurations > Features > Properties > Advanced > Timeouts. You will see the panel shown in Figure 8-10. Figure 8-10. ASA/PIX Default Timeouts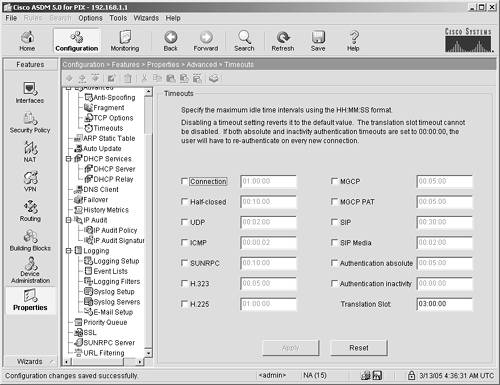 The default settings on the ASA/PIX are generally good enough to mitigate the attacks described in the previous paragraphs. However, if you find that you have an attack that isn't effectively being mitigated, you should first classify the type of traffic present in the attack and then either lower your timeouts or contact your ISP (or the Cisco Technical Assistance Center at http://www.cisco.com) for help. |
EAN: 2147483647
Pages: 120