7.8.1 Single Sign-on Objective To illustrate how to add a new Service Provider in a SAML-based Single Sign-on environment. Exercise Netegrity's jSAML Toolkit ( http://www.netegrity.com/products/index.cfm?leveltwo=JSAML&levelthree=download ) provides a simple Single Sign-on demo environment. This exercise will demonstrate how to add a Foreign Exchange currency exchange service URL (refer to the "Paper and Pencil" exercise in Chapter 3, Web Services Technology Overview, and the demo in Chapter 8, Web Services in Action: Case Study) to the Single Sign-on content provider. It will also be used and referenced in Chapter 8, Web Services in Action: Case Study, as a case study with more details. - Step 1. Set up jSAML Toolkit Demo
Follow the instructions in Appendix C of this book to download and set up a copy of Netegrity's jSAML Toolkit. Extract and install the demo code ( JSAML-toolkit.zip ) under Java the %JWSDP_HOME%\webapps of the Web Services Developer Pack's Tomcat server. The following subdirectories should be expected (see Figure 7-30).
Figure 7-30. jSAML Demo Files Installed under Web Container  - Step 2. Verify Set-up
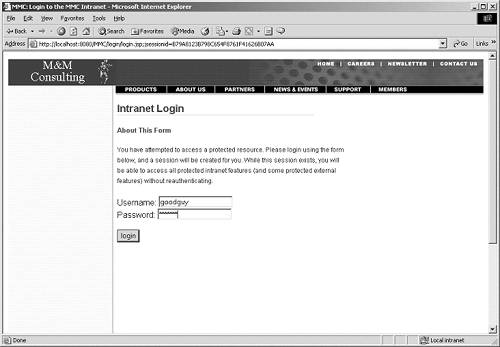
It is recommended to verify the configuration by checking the procedures defined in the jSAML Toolkit documentation "Netegrity JSAML Toolkit Installation Guide" version 1.0 from the above URL. Upon successful set-up, developers should see the sign-on screen shown in Figure 7-31 by issuing the URL http://localhost:8080/MMC/ docs/index.html.
Figure 7-31. Sign-on Screen Shown upon Successful Configuration of Jsaml Toolkit Demo 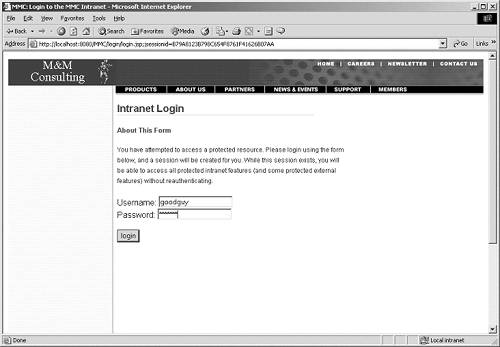 - Step 3. Add New Service URL
Assuming that a new service URL is ready for deploying under a SAML-based Single Sign-on environment, developers can add this new entry in the XML configuration file containing the trading partner URL or service end-point URLs. It is also assumed that the new service URL can be accessed by the same demo id (in this case, goodguy) with full access rights. In some implementations , this may be added as an LDAP entry or an entry in the Policy Server with an administration front-end. In this demo, this entry is added in the configuration file %JWSDP_HOME%\webapps\ MMC\conf\ entries.xml under Java Web Services Developer Pack's Tomcat server. Refer to Figure 7-32 for an example.
Figure 7-32 Sample Entry in the Service URL Configuration File [View full width] <ContentsConfiguration> <EntryList> <Entry> <Name>Stock Services</Name> <URL>http://www.nasdaq.com</URL> <Description>Stock Services</Description> <SiteID>0001</SiteID> </Entry> <Entry> <Name>Techie News</Name> <URL>http://www.news.com</URL> <Description>Techie News Service</Description> <SiteID>0001</SiteID> </Entry> <Entry> <Name>Financial News</Name> <URL>http://www.bloomberg.com</URL> <Description>News about finance and stock</Description> <SiteID>0001</SiteID> </Entry> <Entry> <Name>FX Spot Rate Quote</Name> <URL>http://localhost:8080/ContentProvider/docs/defaultContent.htm</URL> <Description>Online indicative Foreign Exchange Spot Rate quote service to  meet your traveling and online shopping needs</Description> <SiteID>0001</SiteID> </Entry> </EntryList> </ContentsConfiguration> meet your traveling and online shopping needs</Description> <SiteID>0001</SiteID> </Entry> </EntryList> </ContentsConfiguration> In this sample configuration file, it relates the service URL http://localhost:8080/ContentProvider/docs/defaultContent.htm to the SiteID 0001 (which is the Service Provider MMC providing Single Sign-on). - Step 4. Modify the Redirect Page to New Service URL
Modify the defaultContent.htm file (see Figure 7-33) to include a URL link to the new service end-point URL http://localhost:8080/myFX/getFXQuote . Refer to the HTML file and the sample screen in Figure 7-34.
Figure 7-34. Sample Screen defaultContent.htm  Figure 7-33 Modified defaultContent.htm to Redirect to New Service URL [View full width] <HTML> <title>FX Spot Rate Quote Web Service</title> <body> <h1>FX Spot Rate Quote Partner Service</h1> Please click <a href="http://localhost:8080/myFX/getFXQuote"> here </a>to enter FX Spot  Rate Quote Web Service. </body> </HTML> Rate Quote Web Service. </body> </HTML> 7.8.2 Messaging Transport Objective To illustrate how to implement a secure messaging provider class for the Messaging Transport pattern. Exercise This exercise reuses the JAXM messaging provider class from Chapter 8, Web Services in Action: Case Study, to illustrate the Messaging Transport. Can you find out what transaction information is embedded in the SOAP message with digital signature? (Answers highlighted in bold in the following excerpt). The SOAP message generated from the JAXM messaging provider class can be found in the file soap_client.out (refer to Figure 7-35) under the directory /opt/myFX/requester . Figure 7-35 Sample JAXM Message for the Service Request [View full width] Request message #1 ============================== <?xml version="1.0" encoding="UTF-8"?> <s:Envelope xmlns:s="http://schemas.xmlsoap.org/soap/envelope/"> <s:Header> <wsse:Security s:mustUnderstand="1" xmlns:wsse="http://schemas.xmlsoap.org/ws/2002/04/secext/"> <ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#"> <ds:SignedInfo> <ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10  /xml-exc-c14n#"/> <ds:SignatureMethod Algorithm="http://www.w3.org/2000/09 /xml-exc-c14n#"/> <ds:SignatureMethod Algorithm="http://www.w3.org/2000/09  /xmldsig#rsa-sha1"/> <ds:Reference URI="#xpointer(/s:Envelope/s:Body)"> <ds:Transforms> <ds:Transform Algorithm="http://www.w3.org/2001/10 /xmldsig#rsa-sha1"/> <ds:Reference URI="#xpointer(/s:Envelope/s:Body)"> <ds:Transforms> <ds:Transform Algorithm="http://www.w3.org/2001/10  /xml-exc-c14n#"/> </ds:Transforms> <ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/> <ds:DigestValue>2nEFD9/gnWcRrjRk0vHJtqfXqqU=</ds:DigestValue> </ds:Reference> </ds:SignedInfo> <ds /xml-exc-c14n#"/> </ds:Transforms> <ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/> <ds:DigestValue>2nEFD9/gnWcRrjRk0vHJtqfXqqU=</ds:DigestValue> </ds:Reference> </ds:SignedInfo> <ds  :SignatureValue>qKOD2oJUzjmk19vKc+pZ4jEVBeseYB1zZPwENI032XzEQEgSZCbqeVUsD0uDCPu9R2fIPBQs +uw7++lSQNOjHvWVD1nUTPIOp38fNU6XMWfpqF+ww2tBdwkUDiM8noYtB8CnNx9Tv5ejlzd5 dxh3NJYblZ21WDLUC2MTzF7STMU=</ds:SignatureValue> <ds:KeyInfo> <ds:KeyName>Public key of certificate</ds:KeyName> <ds:KeyValue> <ds:RSAKeyValue> <ds:Modulus>tgpcm093Tjvxi :SignatureValue>qKOD2oJUzjmk19vKc+pZ4jEVBeseYB1zZPwENI032XzEQEgSZCbqeVUsD0uDCPu9R2fIPBQs +uw7++lSQNOjHvWVD1nUTPIOp38fNU6XMWfpqF+ww2tBdwkUDiM8noYtB8CnNx9Tv5ejlzd5 dxh3NJYblZ21WDLUC2MTzF7STMU=</ds:SignatureValue> <ds:KeyInfo> <ds:KeyName>Public key of certificate</ds:KeyName> <ds:KeyValue> <ds:RSAKeyValue> <ds:Modulus>tgpcm093Tjvxi  /jVulUMvC5gov+8iamjVxkrwELUQqkFV+lwZcYrJwaXZvHlJLUw6vFCOl9m vhbIGW3t1RKo8sygCqtqe/DBR+XMGYTy6SkP24TDDI43mBgkdVauHCTgV4JYNLcIlTlPIQEm U+f8ftYPLVGFGiHGuYG/SfCnEUE=</ds:Modulus> <ds:Exponent>AQAB</ds:Exponent> </ds:RSAKeyValue> </ds:KeyValue> <ds:X509Data> <ds /jVulUMvC5gov+8iamjVxkrwELUQqkFV+lwZcYrJwaXZvHlJLUw6vFCOl9m vhbIGW3t1RKo8sygCqtqe/DBR+XMGYTy6SkP24TDDI43mBgkdVauHCTgV4JYNLcIlTlPIQEm U+f8ftYPLVGFGiHGuYG/SfCnEUE=</ds:Modulus> <ds:Exponent>AQAB</ds:Exponent> </ds:RSAKeyValue> </ds:KeyValue> <ds:X509Data> <ds  :X509Certificate>MIIDmTCCA0OgAwIBAgIQN7Dt8b73agsj5f5CW8v+jDANBgkqhkiG9w0BAQQFADCBmTERMA8G ... RzuboyCGHqCUMKrFTHr9NdWNxqYigSDIjBvoJeyA1sVXR4tbitco4Z57+mqUSak53HBOK1iW UR9EDaR70A==</ds:X509Certificate> </ds:X509Data> </ds:KeyInfo> </ds:Signature> </wsse:Security> </s:Header> <s:Body> <request> <currency>hkd</currency> </request> </s:Body> </s:Envelope> Reply message #1 ============================== <?xml version="1.0" encoding="UTF-8"?> <s:Envelope xmlns:s="http://schemas.xmlsoap.org/soap/envelope/"> <s:Header> <wsse:Security s:mustUnderstand="1" xmlns:wsse="http://schemas.xmlsoap.org/ws/2002/04/secext/"> <ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#"> <ds:SignedInfo> <ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10 :X509Certificate>MIIDmTCCA0OgAwIBAgIQN7Dt8b73agsj5f5CW8v+jDANBgkqhkiG9w0BAQQFADCBmTERMA8G ... RzuboyCGHqCUMKrFTHr9NdWNxqYigSDIjBvoJeyA1sVXR4tbitco4Z57+mqUSak53HBOK1iW UR9EDaR70A==</ds:X509Certificate> </ds:X509Data> </ds:KeyInfo> </ds:Signature> </wsse:Security> </s:Header> <s:Body> <request> <currency>hkd</currency> </request> </s:Body> </s:Envelope> Reply message #1 ============================== <?xml version="1.0" encoding="UTF-8"?> <s:Envelope xmlns:s="http://schemas.xmlsoap.org/soap/envelope/"> <s:Header> <wsse:Security s:mustUnderstand="1" xmlns:wsse="http://schemas.xmlsoap.org/ws/2002/04/secext/"> <ds:Signature xmlns:ds="http://www.w3.org/2000/09/xmldsig#"> <ds:SignedInfo> <ds:CanonicalizationMethod Algorithm="http://www.w3.org/2001/10  /xml-exc-c14n#"/> <ds:SignatureMethod Algorithm="http://www.w3.org/2000/09 /xml-exc-c14n#"/> <ds:SignatureMethod Algorithm="http://www.w3.org/2000/09  /xmldsig#rsa-sha1"/> <ds:Reference URI="#xpointer(/s:Envelope/s:Body)"> <ds:Transforms> <ds:Transform Algorithm="http://www.w3.org/2001/10 /xmldsig#rsa-sha1"/> <ds:Reference URI="#xpointer(/s:Envelope/s:Body)"> <ds:Transforms> <ds:Transform Algorithm="http://www.w3.org/2001/10  /xml-exc-c14n#"/> </ds:Transforms> <ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/> <ds:DigestValue>NoJLjBHXQG5U3aBBhGYqvOleAf4=</ds:DigestValue> </ds:Reference> </ds:SignedInfo> <ds:SignatureValue>UThG2f96M7ban5M /xml-exc-c14n#"/> </ds:Transforms> <ds:DigestMethod Algorithm="http://www.w3.org/2000/09/xmldsig#sha1"/> <ds:DigestValue>NoJLjBHXQG5U3aBBhGYqvOleAf4=</ds:DigestValue> </ds:Reference> </ds:SignedInfo> <ds:SignatureValue>UThG2f96M7ban5M  TeeBgVkg8bSG482+pH2CImMdKs9saTNpJGDsBBKayhixs1jt+RUvsMlpT eHTL2RipdT3bVNaBi2UZYxuJcGFHFwuW7BDQcPrEI/F6T4qTkzZSNoaAb27XeGbWbHd5BUTo 5YEXBxOfY3WGBn/gBYh9qpSFM8E=</ds:SignatureValue> <ds:KeyInfo> <ds:KeyName>Public key of certificate</ds:KeyName> <ds:KeyValue> <ds:RSAKeyValue> <ds:Modulus>ovig7pVPyrVlhp3BS/TsO TeeBgVkg8bSG482+pH2CImMdKs9saTNpJGDsBBKayhixs1jt+RUvsMlpT eHTL2RipdT3bVNaBi2UZYxuJcGFHFwuW7BDQcPrEI/F6T4qTkzZSNoaAb27XeGbWbHd5BUTo 5YEXBxOfY3WGBn/gBYh9qpSFM8E=</ds:SignatureValue> <ds:KeyInfo> <ds:KeyName>Public key of certificate</ds:KeyName> <ds:KeyValue> <ds:RSAKeyValue> <ds:Modulus>ovig7pVPyrVlhp3BS/TsO  /+Fvoa3I8mtzr0aPXVJEglBrMuP8HUF+1F41EerIwTkoJS7cJX9 KqrzYokmLS/NA09Y/Jw3LNwO74tzQRNQ71V7Ifi7DBQWKuJKGBPRvSSIgYBA9KA5xRLBhXPr 92YrjgUcJKZ2dM6TNxBzE7JGj0U=</ds:Modulus> <ds:Exponent>AQAB</ds:Exponent> </ds:RSAKeyValue> </ds:KeyValue> <ds:X509Data> <ds:X509Certificate>MIICITCCAcsCEDCzpHpOuizSJRp /+Fvoa3I8mtzr0aPXVJEglBrMuP8HUF+1F41EerIwTkoJS7cJX9 KqrzYokmLS/NA09Y/Jw3LNwO74tzQRNQ71V7Ifi7DBQWKuJKGBPRvSSIgYBA9KA5xRLBhXPr 92YrjgUcJKZ2dM6TNxBzE7JGj0U=</ds:Modulus> <ds:Exponent>AQAB</ds:Exponent> </ds:RSAKeyValue> </ds:KeyValue> <ds:X509Data> <ds:X509Certificate>MIICITCCAcsCEDCzpHpOuizSJRp  /MNyjeNkwDQYJKoZIhvcNAQEEBQAwXzELMAkGA1UEBhMC ... GHLCmXN5kBU8</ds:X509Certificate> </ds:X509Data> </ds:KeyInfo> </ds:Signature> </wsse:Security> </s:Header> <s:Body> <YourRequestWasAccepted> <request> <currency> hkd </currency> </request> <profile> Hong Kong dollar </profile> </YourRequestWasAccepted> </s:Body> </s:Envelope> /MNyjeNkwDQYJKoZIhvcNAQEEBQAwXzELMAkGA1UEBhMC ... GHLCmXN5kBU8</ds:X509Certificate> </ds:X509Data> </ds:KeyInfo> </ds:Signature> </wsse:Security> </s:Header> <s:Body> <YourRequestWasAccepted> <request> <currency> hkd </currency> </request> <profile> Hong Kong dollar </profile> </YourRequestWasAccepted> </s:Body> </s:Envelope> The Figure 7-35 SOAP message is created by the program ProfileServlet.java (refer to Figure 7-36), which is used by the case study as a secure messaging provider class using WS-Security. The SOAP request message contains a request to look up the currency code "HKD" for the full description. The SOAP reply message returns with the description "Hong Kong Dollars." This program (refer to Figure 7-36) signs the SOAP messages with a preassigned digital certificate (but it does not encrypt the message in the demo) before sending the contents to the recipient. It is intended to be the underlying JAXM message provider class for other programs. Figure 7-36 Program Excerpt Showing JAXM Secure Message Provider Class [View full width] public class ProfileServlet extends HttpServlet { private static final String DEFAULT_KEYSTORE_FILE = "/opt/myFX/requester  /sample_soap_keystore"; private static final String DEFAULT_KEYSTORE_PASSWORD = "changeit"; private static final String DEFAULT_SERVICE_ALIAS = "service"; private static final String DEFAULT_CLIENT_ALIAS = "client"; private PrivateKey serviceKey; private X509Certificate serviceCert; private X509Certificate clientCert; private SimpleTrustVerifier trustVerifier; private Key encryptingKey; private static XMLResource xml; ... public void doPost(HttpServletRequest req, HttpServletResponse res) throws ServletException, IOException { try { // Generate the data encrypting key // //encryptingKey = createTripleDESKey(); // parse the xml request Document doc = parseRequest(req); // reject if not a SOAP message if (!SOAPMessage.isSOAPMessage(doc)) { publishFault(null, "s:Client", "This service only accepts SOAP messages", res); return; } // interpret request as a SOAP message SOAPMessage msg = new SOAPMessage(doc); // verify request signature; the trust verifier will check that the // signing cert is the client's cert (a cert that we trust) try { msg.verify(trustVerifier); } catch (Throwable e) { publishFault(e, "wsse:FailedCheck", "Unable to verify signature or signing key is untrusted", res); return; } // decrypt body of request try { msg.decrypt(serviceKey); } catch (Throwable e) { publishFault(e, "wsse:FailedCheck", "Unable to decrypt body of request", res); return; } // create the response body from the request body doc = makeResponse(msg.extractBody()); // create SOAP message from response body msg = new SOAPMessage(doc); // encrypt the response body // msg.encrypt(encryptingKey, null, //clientCert.getPublicKey(), null, null); // sign the response msg.sign(serviceKey, serviceCert); // write the response publishResponse(doc, res); } catch (IOException e) { throw e; } catch (Exception e) { throw new ServletException(e); } } /sample_soap_keystore"; private static final String DEFAULT_KEYSTORE_PASSWORD = "changeit"; private static final String DEFAULT_SERVICE_ALIAS = "service"; private static final String DEFAULT_CLIENT_ALIAS = "client"; private PrivateKey serviceKey; private X509Certificate serviceCert; private X509Certificate clientCert; private SimpleTrustVerifier trustVerifier; private Key encryptingKey; private static XMLResource xml; ... public void doPost(HttpServletRequest req, HttpServletResponse res) throws ServletException, IOException { try { // Generate the data encrypting key // //encryptingKey = createTripleDESKey(); // parse the xml request Document doc = parseRequest(req); // reject if not a SOAP message if (!SOAPMessage.isSOAPMessage(doc)) { publishFault(null, "s:Client", "This service only accepts SOAP messages", res); return; } // interpret request as a SOAP message SOAPMessage msg = new SOAPMessage(doc); // verify request signature; the trust verifier will check that the // signing cert is the client's cert (a cert that we trust) try { msg.verify(trustVerifier); } catch (Throwable e) { publishFault(e, "wsse:FailedCheck", "Unable to verify signature or signing key is untrusted", res); return; } // decrypt body of request try { msg.decrypt(serviceKey); } catch (Throwable e) { publishFault(e, "wsse:FailedCheck", "Unable to decrypt body of request", res); return; } // create the response body from the request body doc = makeResponse(msg.extractBody()); // create SOAP message from response body msg = new SOAPMessage(doc); // encrypt the response body // msg.encrypt(encryptingKey, null, //clientCert.getPublicKey(), null, null); // sign the response msg.sign(serviceKey, serviceCert); // write the response publishResponse(doc, res); } catch (IOException e) { throw e; } catch (Exception e) { throw new ServletException(e); } } The technical design details of digital signatures and WS-Security can be referenced in the relevant sections previously in this chapter, as well as in Chapter 8, Web Services in Action: Case Study. 7.8.3 References -
General Web Services Security Web Services Security. http://www.xwss.org/index.jsp Andrew Yang. " XML Web Services Security Issues. " http://www.xwss.org/articlesThread.jsp?forum=34&thread=648 -
XKMS Brett Mandel. " XKMS Headlines XML Security, Takes a Hard Line on Complexity. " March 19, 2002. http://dcb.sun.com/practices/ webservices /overviews/overview_xkms.jsp -
SAML Baltimore Technologies. " Building Online Partnerships with SAML ”A SelectAccess Technical White Paper. " 2002. http://www.baltimore.com/resources/whitepapers.asp Chris McLaren, ed. " Security and Privacy Considerations for the OASIS Security Assertion Markup Language. " OASIS. April 19, 2002. http://www.oasis- open .org/ committees /security/docs Mark Glaser. " SAML Looks to Allay XML Security Concerns. " February 8, 2002. http://dcb.sun.com/practices/webservices/overviews/overview_saml.jsp Prateek Mishra, ed. " Bindings and Profiles for the OASIS Security Assertion Markup Language. " OASIS. April 19, 2002. http://www.oasis-open.org/committees/security/docs Zdenek Svoboda. " Securing Web Services with Single Sign-on. " http://www.theserverside.com/resources/article.jsp?l=Systinet- web-services -part-6 -
XACML OASIS eXtensible Access Control Markup Language Technical Committee. http://www.oasis-open.org/committees/xacml/docs/docs.shtml#link Satoshi Hada and Michiharu Kudo. " XML Access Control Language: Provisional Authorization for XML Documents. " http://www.trl.ibm.com/projects/xml/xacl/xacl-spec.html Satoshi Hada and Michiharu Kudo. " XML Access Control. " http://www.trl.ibm.com/projects/xml/xacl/xmlac-proposal.html -
Project Liberty Public Liberty version 1.1 specifications. http://www.projectliberty.org/ specs /liberty-specifications-v1.1.zip Liberty Alliance. " Liberty Architecture Overview. " Version 1.1. Liberty Alliance Project (January 15, 2003). http://www.projectliberty.org/specs/liberty-architecture-overview-v1.1.pdf Liberty Alliance. " Liberty Protocols and Schema Specification. " Version 1.1. Liberty Alliance Project (January 15, 2003). http://www.projectliberty.org/specs/liberty-architecture-protocols-schema-v1.1.pdf Liberty Alliance. " Liberty Bindings and Profiles Specification. " Version 1.1. Liberty Alliance Project (January 15, 2003). http://www.projectliberty.org/specs/liberty-architecture-bindings-profiles-v1.1.pdf Liberty Alliance. " Liberty Authentication Context Specification. " Version 1.1. Liberty Alliance Project (January 15, 2003). http://www.projectliberty.org/specs/liberty-architecture-authentication-context-v1.1.pdf Liberty Alliance. " Liberty Architecture Implementation Guidelines. " Version 1.1. Liberty Alliance Project (January 15, 2003). http://www.projectliberty.org/specs/liberty-architecture-implementation-guidelines-v1.1.pdf -
Security Threats Denis Piliptchouk and Vince Dovydaitis. " Securing .NET and Java: Side by Side. " RSA Conference 2002. http://www.rsaconference.net/RSApresentations/ pdfs /devwed1115_piliptchouk.pdf Saumil Shah and Shreeraj Shah. " Architectural Threats and Countermeasures for Java Application Servers. " RSA Conference 2002. http://www.rsaconference.net/RSApresentations/pdfs/devthu1015_shah.pdf -
Security Tools Titan. http://www.fish.com/titan/ NMAP. http://www. insecure .org/nmap/nmap_download.html. -
WS-Security Roadmap Web Services Security (WS-Security) 1.0 specification (April 5, 2002). http://www-106.ibm.com/developerworks/webservices/library/ws-secure/ Web Services Security 1.0 Addendum (August 18, 2002). http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-security-addendum.asp Web Services Security Profile for XML-based Tokens (August 28, 2002). http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-security-xml-tokens.asp Web Services Security Policy Language ( WS-SecurityPolicy , or previously WS-Policy) version 1.0 specification (December 18, 2002). http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-securitypolicy.asp Web Services Secure Conversation Language ( WS-SecureConversation ) version 1.0 specification (December 18, 2002). http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-secureconversation.asp Web Services Trust Language ( WS-Trust ) version 1.0
http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-trust.asp
http://msdn.microsoft.com/webservices/default.aspx?pull=/library/en-us/dnglobspec/html/ws-trust.asp |