Threats and Countermeasures
Most Web application attacks require that malicious input is passed within HTTP requests . The general goal is either to coerce the application into performing unauthorized operations or to disrupt its normal operation. This is why thorough input validation is an essential countermeasure to many attacks and should be made a top priority when you develop ASP.NET Web pages and controls. Top threats include:
-
Code injection
-
Session hijacking
-
Identity spoofing
-
Parameter manipulation
-
Network eavesdropping
-
Information disclosure
Figure 10.1 highlights the most common threats to Web applications.
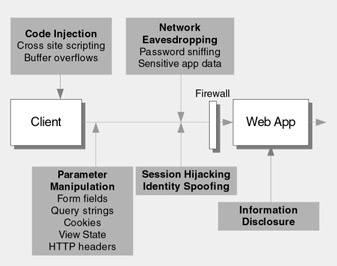
Figure 10.1: Common threats to ASP.NET Web pages and controls
Code Injection
Code injection occurs when an attacker causes arbitrary code to run using your application's security context. The risk increases if your application runs using a privileged account.
Attacks
There are various types of code injection attacks. These include:
-
Cross-site scripting . Malicious script is sent to a Web application as input. It is echoed back to a user 's browser, where it is executed.
-
Buffer overflows . The type safe verification of managed code reduces the risk significantly, but your application is still vulnerable, especially where it calls unmanaged code. Buffer overflows can allow an attacker to execute arbitrary code inside your Web application process, using its security context.
-
SQL injection . This attack targets vulnerable data access code. The attacker sends SQL input that alters the intended query or executes completely new queries in the database. Forms authentication logon pages are common targets because the username and password are used to query the user store.
Vulnerabilities
Vulnerabilities that can lead to successful code injection attacks include:
-
Weak or missing input validation or reliance on client-side input validation
-
Including unvalidated input in HTML output
-
Dynamically constructing SQL statements that do not use typed parameters
-
Use of over-privileged process accounts and database logins
Countermeasures
The following countermeasures can be used to prevent code injection:
-
Validate input so that an attacker cannot inject script code or cause buffer overflows.
-
Encode all output that includes input. This prevents potentially malicious script tags from being interpreted as code by the client's browser.
-
Use stored procedures that accept parameters to prevent malicious SQL input from being treated as executable statements by the database.
-
Use least privileged process and impersonation accounts. This mitigates risk and reduces the damage that can be done if an attacker manages to execute code using the application's security context.
Session Hijacking
Session hijacking occurs when the attacker captures an authentication token and takes control of another user's session. Authentication tokens are often stored in cookies or in URLs. If the attacker captures the authentication token, he can transmit it to the application along with a request. The application associates the request with the legitimate user's session, which allows the attacker to gain access to the restricted areas of the application that require authenticated access. The attacker then assumes the identity and privileges of the legitimate user.
Vulnerabilities
Common vulnerabilities that make your Web pages and controls susceptible to session hijacking include:
-
Unprotected session identifiers in URLs
-
Mixing personalization cookies with authentication cookies
-
Authentication cookies passed over unencrypted links
Attacks
Session hijacking attacks include:
-
Cookie replay . The attacker captures the authentication cookie either by using network monitoring software or by some other means, for example, by exploiting an XSS scripting vulnerability.
-
Query string manipulation . A malicious user changes the session identifier that is clearly visible in the URL query string.
Countermeasures
You can employ the following countermeasures to prevent session hijacking:
-
Separate personalization and authentication cookies.
-
Only transmit authentication cookies over HTTPS connections.
-
Do not pass session identifiers that represent authenticated users in query strings.
-
Re-authenticate the user before critical operations, such as order placement, money transfers, and so on, are performed.
Identity Spoofing
Identity spoofing occurs when a malicious user assumes the identity of a legitimate user so that he can access the application.
Vulnerabilities
Common vulnerabilities that make your Web pages and controls susceptible to an identity spoofing attack include:
-
Authentication credentials that are passed over unencrypted links
-
Authentication cookies that are passed over unencrypted links
-
Weak passwords and policies
-
Weak credential storage in the user store
Attacks
Identity spoofing attacks include:
-
Cookie replay . The attacker steals the authentication cookie either by using network monitoring software or by using an XSS attack. The attacker then sends the cookie to the application to gain spoofed access.
-
Brute force password attacks . The attacker repeatedly tries username and password combinations.
-
Dictionary attacks . In this automated form of a brute force password attack, every word in a dictionary is tried as a password.
Countermeasures
You can employ the following countermeasures to prevent identity spoofing:
-
Only transmit authentication credentials and cookies over HTTPS connections.
-
Enforce strong passwords. Regular expressions can be used to ensure that user-supplied passwords meet suitable complexity requirements.
-
Store password verifiers in the database. Store non-reversible password hashes combined with a random salt value to mitigate the risk of dictionary attacks.
For more information about storing password hashes and other secrets in the database, see Chapter 14, "Building Secure Data Access."
Parameter Manipulation
Parameters are the items of data that are passed from the client to the server over the network. They include form fields, query strings, view state, cookies, and HTTP headers. If sensitive data or data that is used to make security decisions on the server are passed using unprotected parameters, your application is potentially vulnerable to information disclosure or unauthorized access.
Vulnerabilities
Vulnerabilities that can lead to parameter manipulation include:
-
Using hidden form fields or query strings that contain sensitive data
-
Passing cookies that contain security-sensitive data over unencrypted connections
Attacks
Parameter manipulation attacks include:
-
Cookie replay attacks . The attacker captures and alters a cookie and then replays it to the application. This can easily lead to identity spoofing and elevation or privileges if the cookie contains data that is used for authentication or authorization on the server.
-
Manipulation of hidden form fields . These fields contain data used for security decisions on the server.
-
Manipulation of query string parameters .
Countermeasures
You can employ the following countermeasures to prevent parameter manipulation:
-
Do not rely on client-side state management options. Avoid using any of the client-side state management options such as view state, cookies, query strings or hidden form fields to store sensitive data.
-
Store sensitive data on the server. Use a session token to associate the user's session with sensitive data items that are maintained on the server.
-
Use a message authentication code (MAC) to protect the session token. Pair this with authentication, authorization, and business logic on the server to ensure that the token is not being replayed.
Network Eavesdropping
Network eavesdropping involves using network monitoring software to trace packets of data sent between browser and Web server. This can lead to the disclosure of application-specific confidential data, the retrieval of logon credentials, or the capture of authentication cookies.
Vulnerabilities
Vulnerabilities that can lead to successful network eavesdropping include:
-
Lack of encryption when sending sensitive data
-
Sending authentication cookies over unencrypted channels
Attacks
Network eavesdropping attacks are performed by using packet sniffing tools that are placed on the network to capture traffic.
Countermeasures
To counter network eavesdropping, use Secure Sockets Layer (SSL) to provide an encrypted communication channel between browser and Web server. It is imperative that SSL is used whenever credentials, authentication tickets, or sensitive application data are sent over the network.
Information Disclosure
Information disclosure occurs when an attacker probes your Web pages looking for ways to cause exception conditions. This can be a fruitful exercise for the attacker because exception details, which often are returned as HTML and displayed in the browser, can divulge extremely useful information, such as stack traces that contain database connection strings, database names , database schema information, SQL statements, and operating system and platform versions.
Vulnerabilities
Vulnerabilities that lead to information disclosure include:
-
Weak exception handling
-
Letting raw exception details propagate to the client
Attacks
There are many attacks that can result in information disclosure. These include:
-
Buffer overflows.
-
Sending deliberately malformed input.
Countermeasures
To prevent information disclosure:
-
Use structured exception handling.
-
Return generic error pages to the client.
-
Use default redirect pages that contain generic and harmless error messages.
EAN: 2147483647
Pages: 613