Scope of This Guide
Web application security must be addressed across the tiers and at multiple layers . A weakness in any tier or layer makes your application vulnerable to attack.
Securing the Network, Host, and Application
Figure 1 shows the scope of the guide and the three-layered approach that it uses: securing the network, securing the host, and securing the application. It also shows the process called threat modeling , which provides a structure and rationale for the security process and allows you to evaluate security threats and identify appropriate countermeasures. If you do not know your threats, how can you secure your system?
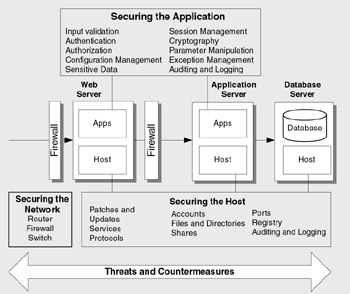
Figure 1: The scope of Improving Web Application Security: Threats and Countermeasures
The guide addresses security across the three physical tiers shown in Figure 1. It covers the Web server, remote application server, and database server. At each tier, security is addressed at the network layer, host layer, and application layer. Figure 1 also shows the configuration categories that the guide uses to organize the various security configuration settings that apply to the host and network, and the application vulnerability categories used to structure application security considerations.
Technologies in Scope
While much of the information in this guide is technology agnostic , the guide focuses on Web applications built with the .NET Framework and deployed on the Windows 2000 Server family of operating systems. The guide also pays special attention to .NET Framework code access security, particularly in relation to the use of code access security with ASP.NET. Where appropriate, new features provided by Windows Server 2003 are highlighted. Table 1 shows the products and technologies that this guidance is based on.
| Area | Product/Technology |
|---|---|
| Platforms | .NET Framework 1.1 Windows 2000 Server family Windows Server 2003 security features are also highlighted. |
| Web Server | IIS 5.0 (included with Windows 2000 Server) |
| Application Server | Windows 2000 Server with .NET Framework 1.1 |
| Database Server | SQL Server 2000 |
| Middleware Technologies | ASP.NET, Enterprise Services, XML Web Services, .NET Remoting |
| Data Access | ADO.NET |
EAN: 2147483647
Pages: 613