Chapter 4 -- Internet Explorer Security Overview
In the previous chapter, we looked at the foundation for building secure Web services, Microsoft Windows 2000. In this and the following three chapters, we'll discuss the security capabilities of Microsoft Internet Explorer, Internet Information Services (IIS), Microsoft SQL Server, and COM+.
Internet Explorer 5 is the Web-browsing technology incorporated into Windows 2000. It's used to access Web data and FTP data, as well as Windows networking information. Most people think of Internet Explorer as the process called Iexplore.exe; however, you must consider that the Internet Explorer Web-browsing technology is deeply integrated with many aspects of the Windows 2000 graphical shell. This is because the technology is highly componentized. It's possible, for example, to include links to your favorite Web sites in Microsoft Management Console (MMC). One of the authors has a standard set of tools he uses all the time in an MMC console, one of which is a link to the Microsoft security pages at www.microsoft.com/security, as shown in Figure 4-1.
The following sections regarding Internet Explorer security include
- Privacy
- Code safety and malicious content
- Security zones
- SSL/TLS and certificates
- Cookie security
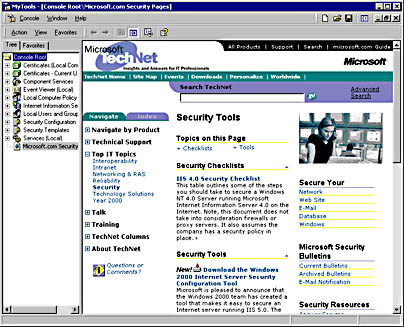
Figure 4-1. A set of standard tools in MMC, including a link to the Microsoft security pages.
EAN: N/A
Pages: 138
- Chapter I e-Search: A Conceptual Framework of Online Consumer Behavior
- Chapter XI User Satisfaction with Web Portals: An Empirical Study
- Chapter XII Web Design and E-Commerce
- Chapter XIII Shopping Agent Web Sites: A Comparative Shopping Environment
- Chapter XVI Turning Web Surfers into Loyal Customers: Cognitive Lock-In Through Interface Design and Web Site Usability