DIGITAL CERTIFICATES
Digital certificates (also referred to as “authentication certificates,” “SSL server certificates,” and “digital IDs”) are the key to providing customer transaction security. A digital certificate is a message sent by one party to another at the beginning of a secure Internet session. The certificate verifies the sender’s identity and vouches for that person’s/organization’s integrity. Just as a driving license is used to validate a motor vehicle driver, a digital certificate establishs the identity of someone in cyberspace. These digital IDs hold a mapping between a user and an encryption key. This key is private to the user and only he or she can use it. Digital certificates also contain the information necessary to allow users to exchange data securely and to transact business over the Internet.
You obtain your digital certificate from an organization called a “Certificate Authority” (CA). The certificate is virtually impossible to forge because the final requirement of secure communications is non-repudiation: a message’s source must be able to be proven beyond a reasonable doubt upon demand.
Technically, a Digital Certificate is a small piece of unique data used by encryption and authentication software. This digital ID establishes a user’s credentials when doing business or other transactions on the Web. It does this by attaching a small file to the data transaction. That file contains: the certificate owner’s name, a serial number, expiration date, a copy of the certificate owner’s public key (used for encrypting messages and digital signatures), and the digital signature of the certificate-issuing authority, allowing the recipient to verify that the certificate is genuine.
Once an Internet client (i.e. your customer’s web browser) requests a secure session, your web server sends the client/browser its digital certificate information, which contains the following:
- The public key.
- The certificate’s serial number.
- The certificate’s validity period.
- The web server’s official domain name.
- The domain name of the CA that issued the certificate.
This information is encrypted using the private key of the CA that issued the certificate. Upon receiving your digital certificate information, the customer’s web browser validates it by checking the following criteria:
- Validity — is it valid for the current date?
- Ownership — does it belong to the server that sent it?
- Certificate Authority — is the CA that issued the digital certificate known and trusted? (To do this, the client/browser checks the CA’s own certificate, which is signed by the CA itself.)
- Public key — can the CA’s digital signature be decrypted using the CA’s public key. (Most web browsers contain a list of the public keys of the best-known CAs, so they do not need to search the Internet for them.)
If the certificate fails any of these tests, the client/browser issues a warning to the customer. The customer may then choose either to continue with the session or to discontinue the session.
Digital certificates can be issued in chains. For example, a large CA might issue a certificate to a smaller CA, which issues a certificate to a still smaller CA, which issues end-entity certificates to e-commerce websites. This type of procedure helps to distribute the task of administering digital certificates. When a customer’s browser/client receives a certificate from a chain, it checks the certificate of every CA in the chain as described above, until it reaches the self-signed certificate of a top-level CA.
Perhaps this scenario will help the reader better to understand how a digital certificate is used in e-commerce. (Also see Fig. 8.) Let’s assume a customer fills in his or her credit card details on a form at a website and then clicks the buy / send / submit order button, which causes that customer’s credit card information to be sent as little bits of electronic data from the customer’s PC to another computer, via the Internet (which is made up of a network of computers, wires, cables and other connections). If not careful, the customer’s data can be intercepted by malicious third parties (this is why transaction security is vital in e-commerce). Such security is provided by specially-configured servers and encryption technology, which ensure that the data transferred between the customer’s PC, the website, and any other destination (such as the computer responsible for processing the credit card) has been turned into a special encrypted code that is difficult to unencrypt, and thus unusable if intercepted.
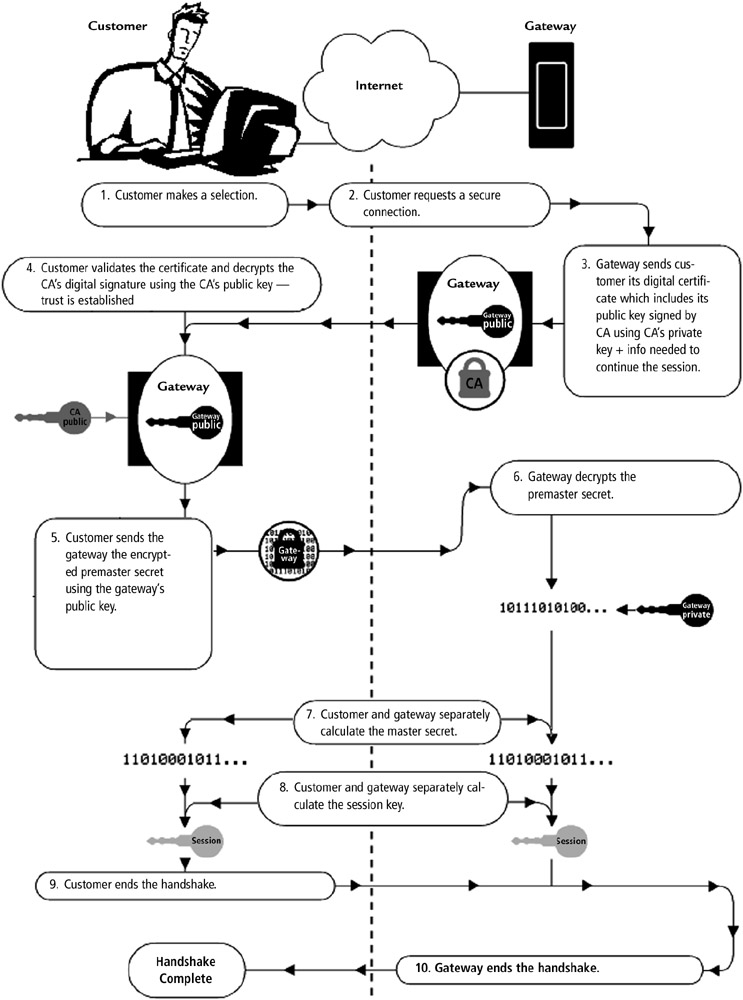
Figure 7: A typical e-commerce related digital certificate scenario. Digital certificates are one of the primary keys to effective e-commerce security because they provide the means for verifying identity.
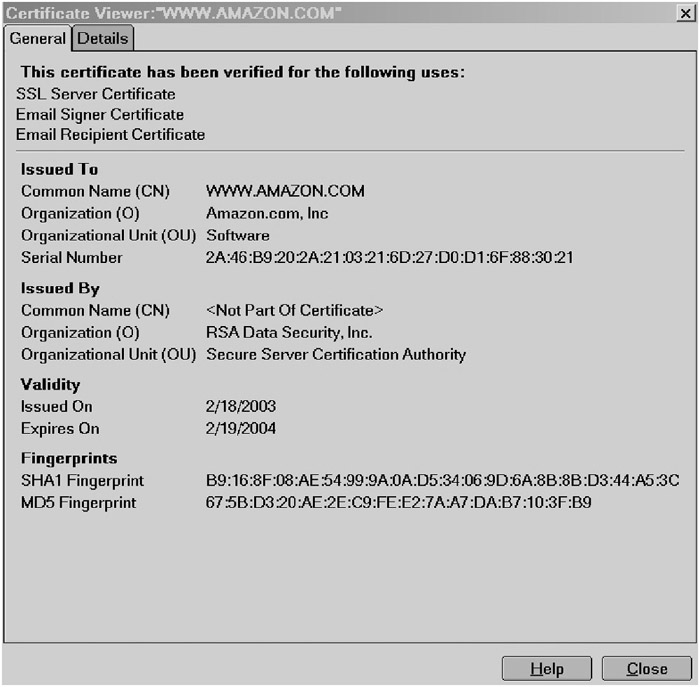
Figure 8: To see what your customer might see when accessing your website via a Netscape browser, we will use Amazon.com’s secure server feature. When a customer signs onto Amazon.com using the site’s “sign in using secure server option,” Amazon’s digital certificate is invoked. To view the digital certificate information, the customer just right clicks any place on the page. That action will bring up a menu and at the bottom of that menu is the selection “View Page Info,” click it. That will bring up a “Page Info” window with several tabs at the top, choose the tab entitled “Security.” Next will be a window that begins “Web Site identify verified” and in the middle of that window is a “view” button, click on that button to bring up the “Certificate Viewer.” There the customer can see the details of the Amazon.com digital certificate as shown in this graphic.
SSL
Central to the digital certificate process is the secure socket layer (SSL) standard, which standardizes the way web browsers and web servers communicate with each other using encrypted data. All but legacy web browsers are set up to conduct secure exchanges of electronic information using the SSL standard. However, a secure exchange can’t take place unless there is a digital certificate installed on the web server in question. The visitor’s web browser uses the digital certificate to authenticate the server and to initiate the encryption process. The browser uses the certificate not only as a stamp of approval, but also to access the information needed to activate the SSL process. If there is no certificate, then the browser (and thus your potential customer) can’t be sure that the server is a reliable partner with which it can exchange data.
Here’s an illustration. A potential customer finds your website, and selects products that he or she wants to purchase. When that customer initiates the credit card transaction, one of the first items of business is for his or her web browser to authenticate your web server by examining its digital certificate. The examination ensures that the certificate has not passed its “best before date” (i.e. it is still valid) and the organization that issued the certificate is on its list of approved certifiers. The browser may also check that the domain name of the website/server it’s communicating with matches the one listed on the digital certificate. Once the browser determines that your server is approved for the secure exchange of data, it will continue with the secure transaction. Since the browser also has a record of that organization’s public key, it will use this key to decrypt and to validate the certifier’s coded digital signature carried on the certificate.
If the browser can’t authenticate the certificate then it will issue an appropriate warning to your customer so that he or she can make the decision whether or not to continue with the transaction.
NOTE
Some readers may wonder how a browser knows if the CA is trustworthy. Web browsers come with their own pre-approved list of CAs. One of the checks that a browser makes before committing to a secure connection is to compare the CA listed on a server’s digital certificate with its own list of approved CAs. To see what I mean, go to your Microsoft IE browser and click on the “Tools” menu, then check on “Internet Options,” followed by the “Contents” tab, and then “Certificates.” This will allow you to see a list of pre-approved CAs. If the CA is not on this approved list, then the web browser will invite its user to decide whether or not to trust the certificate.
This entire digital certification process follows a standard known as SSL — a process that virtually all browsers and web servers can use to send each other encrypted data.
Obtaining Your Digital Certificate
As you should understand, the secure exchange of data through SSL takes place only when the web server has a digital certificate installed. If this license to conduct secure transactions is not present, then SSL is not activated, meaning it isn’t possible to provide a secure transmission of information for your customers.
There are two ways to obtain a digital certificate: Your hosting service owns a digital certificate that you might be able to use for a fee or you can purchase your own certificate.
The best option is to submit the proper paperwork and setup fee to a “certification authority,” which is charged with reviewing a website’s credentials (actually the credentials of the business or person operating the website). Only after the authority is satisfied that the applicant is a legitimate business operation and the genuine owner of the website in question will a digital certificate be issued.
NOTE
Certification authority licensing is a mish mash. In the U.S., the various States have licensing authority, which may be exercised by, for example, the Secretary of State in one instance and the Department of Commerce in another. In other countries, a governmental agency generally issues and oversees certification authority licensing. As an example, in Malaysia it’s the Malaysian Communications and Multimedia Commission.
A certification authority (also known as a “certificate signer,” or a “signer authority”) will award you a digital certificate (after performing a background check) in return for a fee. There are numerous certification authorities eager to provide e-commerce sites with a digital certificate for your server. Once the certificate (which is in the form of a data file) is obtained, it must be installed on your server to activate the server’s SSL features.
If a website wants to be able to conduct secure transactions but doesn’t have a digital certificate, it can use someone else’s server and certificate. The least expensive method is to use a hosting company’s certificate. But this option has a drawback — you will need to use one of your hosting service’s domain names in any secure URL. Thus, when a customer clicks a button to send his or her credit card information the customer’s web browser will indicate a different URL, e.g. https://www.xyzhostingservice.com/www.yourcompany.com/order.htmlname/oderform.htm instead of your URL, e.g. https://www.yourcompany.com/orderform.html.
This may cause confusion on the customer’s end, and that confusion could prevent the customer from completing the transaction.
NOTE
Most web-hosting services require that an e-commerce website have a digital certificate before they will allow the website to use their services. This is a good thing — digital certificates not only allow a website to accept credit card orders securely, but also it helps to keep hackers at bay.
Two of the largest certification authorities are VeriSign and Thawte (which is owned by VeriSign), but there are also other reliable certification authorities including Entrust, Equifax, Globalsign, and RSA Security, to name a few.
For those readers residing in the EU, the European Certification Authority Forum (ECAF) maintains a list of European Supervisory Authorities (www.eema.org/sa_matrix.asp), which may be useful when searching for a Certification Authority.
To wrap up, digital certificates are widely used by e-commerce websites, especially to provide security for credit card transactions online. If a website has a digital certificate, a customer can verify that the website displayed on their computer screen actually is what it appears to be, e.g. your website, not some imposter masquerading as your website in order to intercept your web visitors’ communications.
NOTE
For more information on digital certificates, download the free SSL Guide, which can be found on Verisign’s website (www.verisign.com) and the technical introduction to digital certificates offered by Microsoft (it can be found at http://www.microsoft.com/technet/treeview/default.asp?url=/technet/security/prodtech/cyrpto/Certs.asp).
EAN: N/A
Pages: 159