System Policy
The system policies operate in the same manner as firewall rules. These 30 predefined rules define how traffic flows between the ISA Server computer itself and other networks. To view the system policy rules, follow these steps:
-
Open the ISA Server Management console, expand the ISA server name, then click to the Firewall Policy node.
-
In the task pane, click the Tasks tab. Under System Policy Tasks, click Show System Policy Rules. The system policies will appear in the details pane.
Table 8-1 shows all the system policies. The Default/Recommendation column shows the default settings, and provides recommendations for configuring policies in certain usage scenarios.
| Name | Recommendation | Default State | Order | Action | Protocols | From/Listener | To | Condition |
|---|---|---|---|---|---|---|---|---|
| Allow access to directory services for authentication purposes | If your ISA server isn't installed in a domain, disable this rule. | Enabled | 1 | Allow | LDAP LDAP (UDP) LDAP GC (global catalog) LDAPS LDAPS GC (global catalog) | Local Host | Internal | All Users |
| Allow remote management from selected computers using Microsoft Management Console (MMC) | If you will not use the ISA Server Management console from remote machines, disable this rule | Enabled | 2 | Allow | Microsoft Firewall Control NetBIOS datagram NetBIOS Name Service NetBIOS Session RPC (all interfaces) | Remote Management Computers | Local Host | All Users |
| Allow remote management from selected computers using Terminal Server | If you don’t want to allow Terminal Service/Remote Desktop access to the ISA server, disable this system policy. | Enabled | 3 | Allow | RDP (Terminal Services) | Remote Management Computers | Local Host | All Users |
| Allow remote logging to trusted servers using NetBIOS | If you wish to allow the ISA server to log on to trusted machines (say to a central SQL Server database), then enable this rule. | Disabled | 4 | Allow | NetBIOS Datagram NetBIOS Name Service NetBIOS Session | Local Host | Internal | All Users |
| Allow RADIUS authentication from ISA Server to trusted RADIUS servers | If you will not use RADIUS authentication, disable this rule. | Enabled | 5 | Allow | RADIUS RADIUS Accounting | Local Host | Internal | All Users |
| Allow Kerberos authentication from ISA Server to trusted servers | If you do not wish to support Kerberos authentication, then disable this rule. | Enabled | 6 | Allow | Kerberos-Sec (TCP) Kerberos-Sec (UDP) | Local Host | Internal | All Users |
| Allow DNS from ISA Server to selected servers | ISA Server requires domain name system (DNS) for name resolution. Do not disable this rule. You can create computer sets to restrict access to the DNS servers, however. | Enabled | 7 | Allow | DNS | Local Host | All Networks (and Local Host) | All Users |
| Allow DHCP requests from ISA Server to all networks | If your ISA server will not use DHCP to obtain Internet Protocol (IP) addresses, disable this rule. Recommended to always use static address for internal network adapter. If you do require Dynamic Host Configuration Protocol (DHCP), limit traffic by setting the networks that require it on the To tab. | Enabled | 8 | Allow | DHCP (request) | Local Host | Anywhere | All Users |
| Allow DHCP replies from DHCP servers to ISA Server | See Rule 8. | Enabled | 9 | Allow | DHCP (reply) | Internal | Local Host | All Users |
| Allow ICMP (Ping) requests from selected computers to ISA Server | If you do not wish to allow Remote Management Computers to ping the ISA Server, then disable this rule. | Enabled | 10 | Allow | Ping | Remote Management Computers | Local Host | All Users |
| Allow ICMP requests from ISA Server to selected servers | Leave this rule enabled to allow ISA Server to determine connectivity with other computers. | Enabled | 11 | Allow | ICMP Information Request ICMP Timestamp Ping | Local Host | All Networks (and Local Host Network) | All Users |
| All virtual private network (VPN) client traffic to ISA Server | Unless you enable an ISA Server client VPN (which automatically enables this rule), leave this rule disabled. | Disabled | 12 | Allow | PPTP | External | Local Host | All Users |
| Allow VPN site-to-site traffic to ISA Server | Unless you enable an ISA Server Site-To-Site VPN (which automatically enables this rule), leave this rule disabled. | Disabled | 13 | Allow | None | External IPSec Remote Gateways | Local Host | All Users |
| Allow VPN site-to-site traffic from ISA Server | See Rule 13 | Disabled | 14 | Allow | None | Local Host | External IPSec Remote Gateways | All Users |
| Allow Microsoft CIFS from ISA Server to trusted servers | If you are using authentication with Active Directory directory service, and/or need to access file shares on the internal network, leave this rule enabled. You can also limit exposure by creating a computer set with the domain controllers (DCs) and replace the internal network with your DC Computer Set. | Enabled | 15 | Allow | Microsoft CIFS (TCP, port 445) Microsoft CIFS (UDP, port 445) | Local Host | Internal | All Users |
| Allow remote SQL logging from ISA Server to selected servers | If you want to allow logging to SQL Server computers on other machines, enable this rule. | Disabled | 16 | Allow | Microsoft SQL (TCP) Microsoft SQL (UDP) | Local Host | Internal | All Users |
| Allow HTTP/HTTPS requests from ISA Server to specified sites | This allows access to Microsoft.com sites (defined in the System Policy Allowed Sites Domain Name Set). If you do not want the ISA server to contact the Windows Update or Microsoft.com diagnostic sites directly, disable this rule. This allows access to sites defined in the System Policy Allowed Sites Domain Name set, which by default includes certain Microsoft defined sites (such as Microsoft.com and Windowsupdate.com) | Enabled | 17 | Allow | HTTP HTTPS | Local Host | System Policy Allowed Sites | All Users |
| Allow HTTP/HTTPS requests from ISA Server to selected servers for connectivity verifiers | If you create a connectivity verifier (in the Monitoring node on the Connectivity tab) for Web sites, a prompt allows you to enable this rule. Take caution enabling this rule as it might affect the functionality of new connectivity verifiers. | Disabled | 18 | Allow | HTTP HTTPS | Local Host | All Networks (and Local Host Network) | All Users |
| Allow access from trusted computers to the Firewall Client installation share on ISA Server | If you install the Firewall Client Share on the ISA server, this rule becomes enabled. | Disabled | 19 | Allow | Microsoft CIFS (TCP) Microsoft CIFS (UDP) NetBIOS Datagram NetBIOS Name Service NetBIOS Session | Internal | Local Host | All Users |
| Allow remote performance monitoring of ISA Server from trusted servers | If you will conduct performance monitoring of the ISA server, enable this rule and ensure that the computer performing the monitoring is in the Remote Management Computer Set. | Disabled | 20 | Allow | NetBIOS Datagram NetBIOS Name Service NetBIOS Session | Remote Management Computers | Local Host | All Users |
| Allow NetBIOS from ISA Server to trusted servers | If you do not need to connect to file shares on the internal network, disable this rule. | Enabled | 21 | Allow | NetBIOS Datagram NetBIOS Name Service NetBIOS Session | Local Host | Internal | All Users |
| Allow RPC from ISA Server to trusted servers | Enabled | 22 | Allow | RPC (all interfaces) | Local Host | Internal | All Users | |
| Allow HTTP/HTTPS from ISA Server to specified Microsoft error reporting sites | This rule allows the ISA firewall to send error reports to Microsoft. | Enabled | 23 | Allow | HTTP HTTPS | Local Host | Microsoft Error Reporting sites | All Users |
| Allow SecurID authentication from ISA Server to trusted servers | This rule should be enabled only if SecurID authentication is enabled, otherwise it should remain disabled. | Disabled | 24 | Allow | SecurID | Local Host | Internal | All Users |
| Allow remote monitoring from ISA Server to trusted servers, using Microsoft Operations Manager Agent | Enable this rule if you use Microsoft Operations Manager to monitor the ISA firewall. | Disabled | 25 | Allow | Microsoft Operations Manager Agent | Local Host | Internal | All Users |
| Allow all HTTP traffic from ISA Server to all networks (for CRL downloads) | This rule should be enabled if you want the ISA firewall to access certificate revocation lists (CRLs), required if the ISA server terminates any SSL connections. | Disabled | 26 | Allow | HTTP | Local Host | All Networks (and Local Host) | All Users |
| Allow NTP from ISA Server to trusted NTP servers | You should change this rule by allowing contact with a trusted Network Time Protocol (NTP) server in your organization. The Internal entry allows it to contact any server within the Internal network. | Enabled | 27 | Allow | NTP (UDP) | Local Host | Internal | All Users |
| Allow SMTP from ISA Server to trusted servers | If you don't plan on using Simple Mail Transfer Protocol (SMTP) to send alerts, you should disable this rule. If you do plan on sending SMTP alerts, then you should replace the Internal Destination with a specific computer that will accept the SMTP messages from the ISA Server firewall. | Enabled | 28 | Allow | SMPT | Local Host | Internal | All Users |
| Allow HTTP from ISA Server to selected computers for Content Download Jobs | This rule is automatically enabled when Content Download Jobs are enabled. | Enabled | 29 | Allow | HTTP | Local Host | All Networks (and Local Host) | System and Network Service |
| Allow Microsoft Firewall Control communication to selected computers | Unless you plan on using the remote MMC, you should disable this rule. | Enabled | 30 | Allow | All outbound traffic | Local Host | Remote ManagementComputers | All Users |
Editing the System Policy
System policy rules can be edited using the System Policy Editor. By default, system policy rules are not shown in the details pane along with the firewall policy rules. To access the System Policy Editor and edit the system policy, follow these steps:
-
Open the ISA Server Management console.
-
In the console tree, expand the server name, and click Firewall Policy.
-
In the task pane, under System Policy Tasks, click Edit System Policy.
-
The System Policy Editor, shown in Figure 8-2, allows you to modify the configuration groups, enable or disable the configuration groups or individual services, and control how the traffic flows between the networks.
-
For example, to disable the DNS service, in the Network Services configuration group select DNS. On the General tab, select the Enable check box to disable the communication between ISA Server and trusted DNS servers.
-
To modify the networks to which traffic can be routed, click the To tab illustrated in Figure 8-3. Click Add, Edit, or Remove to change the network entities. Click OK after completing your changes.
-
In the details pane, click Apply to save the changes and update the configuration.
-
Click OK to complete the change.
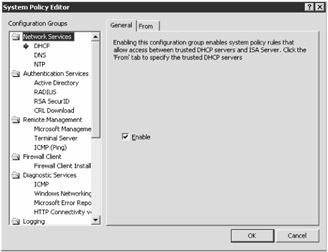
Figure 8-2: The System Policy Editor in ISA Server 2004.
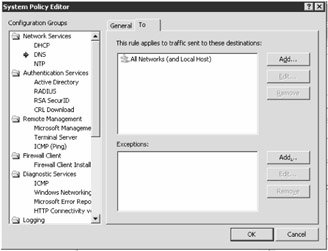
Figure 8-3: Each policy has a General tab that illustrates the properties, and either a From or To tab that controls the source or destination to which the policy applies.
Exporting and Importing System Policy
Exporting and importing functions in ISA Server 2004 gives you the ability to save your ISA configuration to an XML file. This is useful if you need to back up your configuration at a later date, or would like to apply your configuration of one ISA server to another ISA server. Although exporting the firewall policy rules will be more commonplace, you can also export and import the system policy rules.
To export the system policy, follow these steps:
-
In the console tree, expand the server name, and click Firewall Policy.
-
In the task pane, click the Tasks tab. Under System Policy Tasks, click Export System Policy.
-
On the Export Configuration dialog box, browse to the location to where you would like to save the export file, type a filename to be given to the export file in the File Name text box, and then click Export.
-
In the Exporting System Policy Rules dialog box, click OK.
To import the system policy, follow these steps:
-
In the console tree, expand the server name, and click Firewall Policy.
-
In the task pane, click the Tasks tab. Under System Policy Tasks, click Import System Policy.
-
In the Import Configuration dialog box, browse to the location on the disk where you saved the export XML file, select the export file to insert it into the File Name text box, and click Import.
-
In the Importing System Policy Rules dialog box, click OK.
-
In the details pane, click Apply to save the changes, and then click OK.
EAN: 2147483647
Pages: 173