Risk Mitigation
|
|
The complete elimination of risks is usually an impossible task or one that is so impractical that it is not attempted. For this reason, risk mitigation is used to combat the impact of risks. Risk mitigation is the process of reducing risk to an acceptable level through controls and safeguards, which are implemented to protect against specific threats. Cost-effective approaches are used to apply appropriate methods of regulating the risk and decreasing its impact to an appropriate level. In other words, you deal with the risk in the best way possible with the least amount of cost.
How a potential threat is dealt with is largely dependent on the choices that are made after identifying the risk. As shown in Figure 5.2, there are a number of options for risk mitigation. The choices available are:
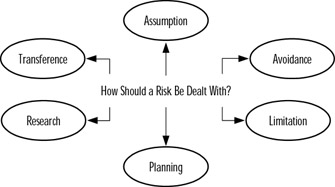
Figure 5.2: Risk Mitigation Options
-
Assumption The risk is accepted and a decision is made to continuing operating or lower the likelihood and consequences of risks by implementing controls.
-
Avoidance The risk is avoided by removing the cause or consequences of the risk.
-
Limitation The risk is limited by applying safeguards to minimize its impact.
-
Planning A plan is developed to prioritize, implement, and maintain safeguards.
-
Transference The risk is transferred to another source, so that any loss can be compensated or the problem becomes that of another party.
-
Research The vulnerability is acknowledged, but further research into controls to correct the vulnerability and lower the risk of loss is needed.
It is important to realize that risks should be mitigated in order of priority, with those that can cause the greatest harm dealt with first. It is important not to waste time dealing with risks that will barely impact a project or company, while others exist that could cripple the business.
Risk assumption is a mitigation option in which the risk is accepted. In accepting the risk, the organization may choose to do nothing about the potential threat, or make efforts to reduce the likelihood the risk and its consequences will occur. For example, the operating system of a server may have vulnerabilities that could be exploited. Bugs in the software could cause problems, or even allow hackers to take advantage of the bug and gain access to the system. If the network was not connected to an external network, they may simply accept the risk as being minimal and do nothing about it. In other situations, the risk would be part of regular maintenance, and they would decide to fix these problems as best they could. They would check the manufacturer's Web site, and apply service packs when they become available. By assuming the risk, the organization accepts the possibility that the risk will occur, and acknowledges that the benefit of an asset or endeavor outweighs the potential losses.
By avoiding a risk, there is no chance that the risk will pose a potential threat to the company. Risk avoidance involves removing the cause or consequences of a risk, so that any possibility of loss is also removed. However, removing risks is not always possible, and to do so means that a company may also lose any potential benefits associated with an asset or risky endeavor. For example, a company could remove the risk of viruses by cutting off Internet access, and removing everyone's ability to add data to the network. While there is now no way for a virus to get on the system, people are unable to do any work and the business is unable to function. Because risks are often an inherent part of normal business practices, the potential benefits of an activity must be weighed against any potential losses before a decision is made.
Risks may have a number of consequences, so limiting the consequences associated with a risk is a legitimate method of mitigation. Risk limitation involves applying safeguards to minimize the impact of a risk. For example, a company may acknowledge that there is a risk of power outages occurring, and purchase Uninterruptible Power Supplies (UPSs) to allow servers to safely shut down if a power failure is detected. While no one is able to use the server, the data on the server is less likely to be corrupted. In doing so, they have limited the consequences of the risk by implementing safeguards to deal with potential problems.
Risk planning is a comprehensive process in which a risk mitigation plan is developed to prioritize, implement, and maintain safeguards. If this option is used, an organization must analyze the risk and determine how to deal with it effectively. As will be discussed later in this chapter, risk planning involves looking at which assets may be affected by a particular risk, determining the likelihood and impact a potential threat may have, and deciding which safeguards should be implemented to minimize the risk.
Risk transference is an option in which the risk is transferred to another source. With this method, an agreement is made with another party to take responsibility for the risk, thereby shifting the consequences of the risk to the other party. For example, generally, the most cost-effective way to deal with the threat of natural disasters damaging a building is to purchase an insurance policy. Because the insurer must pay for any damages resulting from floods, fires, or other events, the risk of loss is passed from the organization to the insurance company. Risk transference is often used with other methods that are geared toward controlling the risk, and used as a fail-safe in case the control fails.
In some cases, an organization may not know how to properly deal with a risk, and further research is required into the potential problem. Risk research acknowledges this lack of understanding, and involves studying the issues further. Members of the organization may be required to analyze threats, research safeguards, or consult with outside parties. Once a better understanding of the situation has been acquired, the risk is again discussed by decision makers and another mitigation option is selected.
Even after mitigation options have been chosen and safeguards have been implemented, certain risks resulting from the initial threat may develop. A residual risk is one that occurs despite controls that are applied. For example, the hacking of an e-commerce site might be a risk for which safeguards are implemented. If the site was hacked however, and it was reported to the public that the culprit stole customer credit card numbers, numerous customers might stop buying products from that site. Publicity from the incident could also devalue stocks, making the company's worth drop significantly. As you can see from these examples, cause and effect can result in multiple risks involved in a single incident. To offset the residual risk associated with a threat, additional methods like insurance or public relations may be used to minimize the impact.
| Test Day Tip | To help you remember information, try to arrange the first letter of each word into a new word. For the exam, you will want to remember the six options available for risk mitigation, so just remember the word LAP RAT. Each letter in this word represents an option: Limitation, Assumption, Planning, Research, Avoidance, and Transference. Another way to remember information is to take the first letter of each word and make a sentence. For example, Larry And Pat Ran Around Tokyo. Just as with the word association, each of the first letters in the sentence is the same as the first letters for each of the options. Using such tricks can help to tweak your memory and remember important bits of information, and can be very helpful in stressful moments like exams. |
Identifying the Risks that Need Mitigating
Risk identification is the process of ascertaining what threats pose risk to your company, so that you can deal with them accordingly. As seen earlier, there are a wide variety of risks that may affect different aspects of an organization. Because there are so many potential threats that an organization may face, the administrator needs to identify which risks need mitigating and prioritize them accordingly. This allows them to determine which threats should be dealt with first in an incident, and where policies and procedures need to be created. Determining which risks need mitigating and their priority may be based on:
-
Greatest loss expectancy
-
Regulatory compliance
-
Contractual compliance
As discussed in the next section, every asset in a company has a certain value attached to it. It follows suit that some assets are of greater value than others. For example, the data residing on a server may be considered more valuable than the server itself. When determining whether a risk needs mitigating, and the order in which risks will be dealt with, those with the greatest potential for loss should be of primary concern. Safeguards should be implemented to protect the most vital areas of a company before addressing risks that are of minimal impact.
Some organizations may also need to protect assets to be compliant with certain regulations. State or federal laws may require an organization (such as a hospital or banking institution) to protect client information. In other cases, the company may have a type of certification (such as ISO 9000) that they want or need to be compliant with and that establishes how the company operates. To adhere to policy or legislation and remain in business, these regulations may order that certain risks are mitigated, and may provide standards on how to do so. For example, regulations may state that firewalls must be installed and configured a certain way to protect hacking of the internal network from the Internet. To ensure the risk is managed effectively, third-party validation may be required after the work is done.
In some cases, risks may need to be mitigated and prioritized based on the need to comply with a contract. If an agreement has been made with clients or other parties, the company may be legally obligated to deal with specific types of risk. For example, an Internet Service Provider (ISP) may have a contract with clients guaranteeing a limited amount of downtime. If clients are unable to connect to the Internet for a certain amount of time (such as 24 hours), then the company agrees to reimburse clients for the inconvenience. In other cases, contracts may impose large fines or hold the company in breach of contract. To protect the agreement between an organization and other parties, risks must be mitigated and prioritized effectively.
Asset Identification
To identify risks and prioritize them, it is important to first determine which assets need to be protected. Assets are the property and resources belonging to a company, and can include any number of different properties or personnel. Assets identified within an organization could include:
-
Computers
-
Software
-
Data
-
Network connectivity equipment
-
Other properties owned by the business (supplies, furniture, and so on)
It is almost impossible to identify risks, their likelihood, and impact without asset identification and valuation. After all, if you do not know that a company owns a server, you cannot identify its risk of being effected by viruses, power failures, and other risks. In the same light, if a company's network were not connected to the Internet, then you would not identify the risk of hackers gaining entry in this way. The assets possessed by a company are the focal points on which risks are identified.
Tagging and inventorying assets allows the administrator to identify what assets are at risk, so they can develop plans to protect, recover, and replace them. Tagging assets involves putting a numbered sticker or barcode on each asset. The tags should have a number that is then documented in an asset log. The log should describe the asset and provide such information as the tag number, description of the asset, serial number, and other information relevant to the equipment. Not only can this inventory be used to identify risks, but can also be used to make insurance claims and replace equipment in case of a disaster.
When identifying assets, its value must also be determined. Value refers to the impact the asset will have on a company if it is lost. Determining the value and importance is essential, as it will be used to determine which assets require added protection from risks. To determine the value of an asset, the following factors should be considered:
-
The market value of the asset
-
The cost to support the asset
-
The importance of the asset to the organization
Market value is the price that a buyer would expect to pay or a seller would expect to get for an item for sale on the open market. To determine the fair market value, administrators must look at the current depreciated value of assets. Equipment and certain other assets may drop in value each year they are in service, because they are less valuable the longer they are used., such as when purchasing a car. When the car is driven off the lot, it becomes a used vehicle and is less valuable. As the years go by, wear and tear on the car depreciate it further. This same principle not only applies to vehicles but other assets owned by a company.
The cost of replacing the item can also be used to determine the value of an asset. When considering critical systems that have been in service for a number of years, the depreciated value may have decreased to the point that it has no value under this calculation. For example, an e-commerce business may have been using the same server for the past six years, and the value was depreciated by 25 percent per year. Does this mean that the Web server has no value to the organization and should not be considered in determining objects at risk? Because the server is vital to business operations, it would need to be replaced immediately if it was damaged or destroyed. To determine the value of the asset, the system administrator could determine the cost of this replacement, and use that in their calculations.
The value of an item can also be affected on the cost of supporting it. Many companies have the additional cost of paying support fees to third parties to assist with problems. An example of this would be support costs paid to Novell or Microsoft to provide assistance with issues relating to their operating systems. If a server was not functioning properly, an organization could call a special support line and get assistance with solving the problem. In other cases, fees may be paid to third parties to provide on-site support, where a technician would visit a site and fix the problem.
With some assets, the market value of the item may not be applicable. The asset might have no value to other companies but may still be of vital importance and account for a major loss if anything happened to it. Data is one such asset that may be difficult to assess, as it may have no current or quantifiable monetary value. For example, an unpublished novel may have no value at present, but may be worth millions (or worthless) upon publication. While its value could be determined based on the cost of reentering the data, this may not provide an accurate assessment of its worth. There is no real way to foresee the value of such data, but its importance is relevant to the company or individual who owns it.
| Note | The importance of data not only applies to properties, but also to people. Personnel are as much of an asset to a company as any of the items used to run the business. For example, if a network administrator were the only one with knowledge of the system, the impact of losing this person would be great. Because of the importance of people within an organization, it is important to identify vital members of the organization, and provide methods of continuing business activities if they are unavailable. |
Determining the importance of an asset is often speculative, and will vary from company to company. What is incredibly important for one business to function may be of little worth to others; so acquiring a list from other companies often is not possible. Determining the importance of an asset generally involves assigning a numeric value (called a metric or weight) to each asset. The weight of importance an asset has is based upon the impact its loss will have on the company. For example, while a network router may have little monetary value, the loss of the router could bring down parts of the network, preventing people from doing their work. This makes the weight of importance higher. When creating the inventory of assets, a column should be included on the sheet where a value can be assigned based upon the importance of that equipment. This value is on a scale of 1 to 10, with 10 having the highest importance. As seen in the next section, determining this importance or value is vital in other aspects of the risk mitigation process.
| Exam Warning | Assets and risks may come not only in the form of objects, but also in the form of people. Humans are also a resource, and may provide distinctive skill sets. They can also be the cause of major problems, such as theft or malicious damage to equipment and data. When answering questions dealing with risks and assets, do not forget that people are an important component of both topics. |
Risk Mitigation Analysis
After gathering all of the data discussed up to this point, the administrator will need to analyze this information to determine the probability of a risk occurring, what is affected, and the costs involved with each risk. Assets will have different risks associated with them, and they will need to correlate different risks with each of the assets inventoried in the company. Some risks will impact all of the assets of a company, such as the risk of a massive fire destroying a building and everything in it, while in other cases, groups of assets will be affected by specific risks.
Assets of a company will generally have multiple risks associated with them. Equipment failure, theft, or misuse can affect hardware, while software may be affected by viruses, upgrade problems, or bugs in the code. By looking at the weight of importance associated with each asset, the administrator should then prioritize which assets will be analyzed first, and determine what risks are associated with each.
There are different methods in which risks can be analyzed to determine which of the risk mitigation options are appropriate. A qualitative analysis will build various scenarios that look at the circumstances relating to possible incidents, and then rank threats and risks associated with them. Quantitative analysis looks at values and equations to analyze risks and their impact on the company. While both methods can be useful for deciding how particular risks will dealt with, they are quite different in how the risk is analyzed.
The primary component of qualitative analysis is the creation of scenarios, which are outlines or models built from anticipated or hypothetical events. The scenario begins with a focal point, such as a particular decision, and then tries to predict what could occur from that point. For example, at the end of the twentieth century, many IT departments created Y2K scenarios that addressed possible issues relating to systems failing to switch over to the year 2000. Scenarios included probabilities like data being invalid because date fields could not enter 2000 as the year, and unpredictable events like computers shutting down, power failures, and so on. By creating these scenarios, IT staff could then review the scenarios and rank the likelihood and loss associated with each risk.
As with asset valuation, ranking scenarios can be done on scales. A scenario may be rated on a scale of 1 to 10, with 10 having the highest probability of occurring. Another method is by rating the likelihood of a scenario based upon a margin of being high, medium, or low. If a scenario is ranked as high, it has been determined to cause a great amount of loss, or has a threat that is very possible of occurring. In such a rating, controls that have been implemented to prevent a particular vulnerability from being exercised are either ineffective or non-existent. If a scenario is ranked as medium, it may have an intermediate amount of loss associated with it, or has a threat that can be impeded by existing controls. If a scenario is ranked as low, then the amount of loss is marginal, or the threat either cannot occur or can be considerably impeded by existing controls. By ranking the scenarios in these ways, decisions can then be made as to what risk mitigation should be used to deal with the situation.
Quantitative analysis uses a more formulated approach to analyzing risks. Equations are used with this method of analysis to calculate how the risk will impact the company, inclusive to providing estimates on the total cost of a risk, how often the risk may occur, and how much it will cost the company on an annual basis. Acquiring this information in the analysis phase of risk management provides an understanding of how and why each risk must be dealt with.
After determining what assets may be affected in a company, and estimating or establishing their value, the administrator then needs to determine the probability of a risk occurring. While there may be numerous threats that could affect a company, not all of them are probable. For example, a tornado is highly probable for a business located in Oklahoma City, but not highly probable in New York City. For this reason, a realistic assessment of the risks must be performed.
Historical data can provide information on how likely it is that a risk will become reality within a specific period of time. Research must be performed to determine the likelihood of risks within a locality or with certain resources. By determining the likelihood of a risk occurring within a year, you can determine what is known as the Annualized Rate of Occurrence (ARO).
Information for risk assessment can be acquired through a variety of sources. Police departments can provide crime statistics on the area certain facilities are located, allowing a company to determine the probability of vandalism, break-ins, or dangers potentially encountered by personnel. Insurance companies can provide information on risks faced by other companies and the amounts paid out when these risks became reality. Other sources may include news agencies, computer incident monitoring organizations, and online resources.
Once the ARO has been calculated for a risk, it can be compared to the monetary loss associated with an asset. This is the dollar value that represents how much money would be lost if the risk occurred. This can be calculated by looking at the cost of fixing or replacing the asset. For example, if a router failed on a network, a new router would need to be purchased, and the company would have to pay to have it installed. In addition to this, the company would also have to pay for employees who are not able to perform their jobs because they cannot access the network. This means that the monetary loss would include the price of new equipment, the hourly wage of the person replacing the equipment, and the cost of employees unable to perform their work. When the dollar value of the loss is calculated, this provides total cost of the risk, or the Single Loss Expectancy (SLE).
To plan for the probable risk, a budget would be needed for the possibility that the risk will happen. To do this, the ARO and the SLE are used to find the Annual Loss Expectancy (ALE). To illustrate how this works, say that the probability of a Web server failing is 30 percent. This would be the ARO of the risk. If the e-commerce site hosted on this server generates $10,000 an hour and the site would be estimated to be down two hours while the system is repaired, then the cost of this risk is $20,000. In addition to this, there would also be the cost of replacing the server itself. If the server cost $6,000, this would increase the cost to $26,000. This would be the SLE of the risk. Multiplying the ARO and the SLE, determines how much money would need to be budgeted to deal with this risk. This formula provides the ALE:
ARO x SLE = ALE
When looking at the example of the failed server hosting an e-commerce site, this means the ALE would be:
0.3 x $26,000 = $7,800
To deal with the risk, how much needs to be budgeted to deal with the probability of the event occurring needs to be assessed. The ALE provides this information, leaving a company in a better position to recover from the incident when it occurs. It is also important to determine what the ALE would be after safeguards have been implemented, to see whether the benefits of a particular control outweigh the cost.
Safeguard analysis involves reviewing the various vulnerabilities that may be targeted, and finding controls that are appropriate to deal with specific threats. By looking at the areas of a project where a company may experience risk, and where weaknesses exist, the administrator can then begin investigating how to deal with them. For example, a company may have a Web server that provides information to the public. To deal with the potential threat of hackers, the administrator may decide that an appropriate safeguard would be to get rid of the Web server and pay an ISP a fee to host the Web site on one of their servers. In doing so, they will be responsible for dealing with any risks relating to hackers. If the site is hacked, all they will need to do is upload any content after the problem has been identified and fixed. By analyzing the risk and identifying where vulnerabilities exist helps determine an appropriate method of controlling the risk.
When analyzing safeguards, it is important to look at multiple controls, so that there are a number of options to choose from. To use the previous example, simply selecting to transfer the risk is not always the best option. It may be decided that adding a firewall to protect the internal network from hacking attempts through the Web server, and installing bug fixes and service packs may be a more appropriate method of dealing with the threat.
Safeguards can be identified through a variety of sources. Since some vulnerabilities can be identified in multiple companies, an administrator can investigate how others choose to control the risk. Interviewing other companies and acquiring their input will not only provide information on how they dealt with a potential problem, but will also give input to their opinions on how the control worked. The information on controls can also be viewed through manufacturer's specifications, advertising, or reviews of various safeguards. The more methods used to investigate a particular safeguard, the more insight they will have into its effectiveness.
Since any project works on a limited budget, safeguard costing is another important part of the risk mitigation process. Safeguard costing requires a company to look at the prices of various controls and determine which will be the most cost-effective method of dealing with a threat. When identifying safeguards available for a particular vulnerability, lists should be compiled on the cost of purchasing a safeguard from various sources, as not every vendor will generally have the same prices. In some cases, such as applying service packs to a server to control software vulnerabilities, there may be no associated costs. In other situations, such as installing a new server, the costs would be comparatively high.
Support costs should also be determined when establishing the cost of implementing a safeguard. Installing certain controls will require additional costs over the initial cost of purchasing it. For example, installing a firewall would require occasional software and server upgrades, and would have the added cost of personnel having to maintain the server and review logs. Such costs should be incorporated into the overall cost of implementing the control. By determining the annual and total costs associated with different safeguards, a company will be better able to decide on which ones provide the security needed, at an affordable price.
A cost/benefit analysis should be conducted by a firm before a decision is made on which safeguard will be implemented. This type of analysis compares the costs of a particular control to its expected benefits. As with everything involved with management, if the costs are greater than the benefits, another method of dealing with the problem should be found.
The monetary benefit of a safeguard can be seen by estimating how much will be saved or lost after it has been implemented. To determine an estimate of this value, the following equation needs to be used as part of the cost benefit analysis:
ALE (before) - ALE (after) - Annual Cost = Value of Safeguard
Earlier in this section we discussed how to calculate the ALE. In this formula, you take the ALE before a safeguard is applied, subtract the ALE after the safeguard is applied, and then subtract the annual cost of implementing and supporting the safeguard. Once a safeguard is applied, the threat should occur less frequently or losses should be less significant, so the ALE after the safeguard should also be less but may have an added cost of support. For example, say a safeguard has an annual cost of $1,000. If the ALE before a safeguard was applied was $7,800, but was $5,000 after applying the safeguard, then we could calculate the value of the safeguard as follows:
$7,800 - $5,000 - $1,000 = $1,800
In this example, the monetary value of the safeguard would be calculated as being $1,800, making it worth implementing for the company. If the calculation had equated to a negative value, then it may not have been worth implementing.
While monetary value is an important motive for deciding whether a safeguard is worth implementing, it should not be the only factor. Some safeguards may be easier to use than others, such as when firewall software makes it easier to create rules for different users that control their ability to access resources from the Internet. Other controls may also provide better audit features, allowing the administrator to view what users are accessing or problems relating to the system itself. In other situations, they may find that the reputation of a particular vendor suits their needs better. While one company provides the same product for a cheaper price, they may have had problems with this vendor and do not wish to deal with them again. While formulas give an understanding of the benefits and costs associated with a particular safeguard, you should never underestimate the value of less calculated reasoning.
Exercise 5.03: Determining the Annual Loss Expected to Occur from Risks
A widget manufacturer has installed new network servers, changing its network from a peer-to-peer network to a client/server-based network. The network consists of 200 users who make an average of $20 an hour, working on 100 workstations. Previously, none of the workstations involved in the network had antivirus software installed on the machines. This was because there was no connection to the Internet, and the workstations did not have floppy disk drives or Internet connectivity, so the risk of viruses was deemed minimal. One of the new servers provides a broadband connection to the Internet, which employees can now use to send and receive e-mail, and surf the Internet. One of the managers read in a trade magazine that other widget companies have reported an 80 percent chance of viruses infecting their network after installing T1 lines and other methods of Internet connectivity, and that it may take upwards of three hours to restore data that has been damaged or destroyed. A vendor will sell licensed copies of antivirus software for all servers and the 100 workstations at a cost of $4,700 per year. The company has asked the administrator to determine the annual loss that can be expected from viruses, and determine if it is beneficial in terms of cost to purchase licensed copies of antivirus software.
-
What is the ARO for this risk?
-
Calculate the SLE for this risk.
-
Using the formula ARO × SLE = ALE, calculate the ALE.
-
Determine whether it is beneficial in terms of monetary value to purchase the antivirus software by calculating how much money would be saved or lost by purchasing the software.
Answers to Exercise Questions
-
The ARO is the likelihood of a risk occurring within a year. The scenario states that trade magazines calculate an 80 percent risk of virus infection after connecting to the Internet, so the ARO is 80 percent or 0.8.
-
The SLE is the dollar value of the loss that equals the total cost of the risk. In the case of this scenario, there are 200 users who make an average of $20 per hour. Multiplying the number of employees who are unable to work due to the system being down by their hourly income, this means that the company is losing $4,000 an hour (200 × $20 = $4,000). Because it may take up to three hours to repair damage from a virus, this amount must be multiplied by three because employees will be unable to perform duties for approximately three hours. This makes the SLE $12,000 ($4,000 × 3 = $12,000).
-
The ALE is calculated by multiplying the ARO by the SLE (ARO × SLE = ALE). In this case, you would multiply $12,000 by 80 percent to give you $9,600 (0.8 × $12,000 = $9,600). Therefore, the ALE is $9,600.
-
Because the ALE is $9,600, and the cost of the software that will minimize this risk is $4,700 per year, this means that the company would save $4,900 per year by purchasing the software ($9,600 - $4,700 = $4,900).
|
|
EAN: 2147483647
Pages: 135