Hardening Wireless LAN Connections
All the hardening steps you have undertaken to secure your WAP and define who can connect to it are pointless exercises if you do not also harden the wireless connections themselves . The four main wireless connection methods you need to be aware of and know how to configure are as follows :
-
Wired Equivalent Privacy (WEP)
-
WiFi Protected Access (WPA) using pre-shared keys
-
WPA using RADIUS
-
Virtual private networks
| |
A fifth type of wireless connection is the wide- open connection. This connection uses no form of authentication or encryption. Anyone with a wireless card can connect to the WAP and get access to the network. This type of connection is typically used for providing WiFi hotspots. By default, most WAPs ship configured in this manner. The recommendations that follow detail the methods you can use to harden the default configuration.
| |
Hardening Wired Equivalent Privacy (WEP)
As the name implies, WEP was designed to provide privacy to wireless connections on par with a wired connection. WEP was part of the original 802.11 standard and is used by all three wireless standards. WEP was designed to prevent eavesdropping and data tampering and to prevent unauthorized access to the wireless network. WEP functions by utilizing the RC4 cipher stream and combining a 40-bit or a 104-bit WEP key with a 24-bit random number known as the initialization vector (IV) . This results in either a 64-bit or 128-bit encryption key. Because the IV changes with every message, a new encryption key is generated for each message. WEP functions by combining the encrypted data packet (known as the ciphertext ) with the clear-text IV before transmitting. The IV is sent in clear text due to the destination needing to know the IV used to generate the encryption key. The receiver then uses the WEP key and attached IV to decrypt the packet.
Unfortunately, for all this effort, WEP has some significant security flaws that make it a very ineffective protocol. Although WEP is better than nothing, a hacker can crack WEP in 15 minutes or less, depending on the amount of traffic they can sniff. This is attributed to the following flaws:
-
WEP key recovery WEP uses the same WEP key and a different IV to encrypt data. The IV has a limited range of values (from 0 to 16777215) to choose from and eventually it uses the same IV over and over. By sniffing the wireless network and picking the same IVs out of the datastream, a hacker can gain enough information to figure out what the WEP key is.
| |
RSA Security has developed a solution that addresses the weak WEP key methods. It is called the Fast Packet Keying Solution and utilizes a hashing mechanism to dynamically generate unique WEP keys for each packet, thus preventing a hacker from being able to determine the WEP key. You can find more information about this at http://www.rsasecurity.com/newsletter/wireless/2002_winter/feature.html and http://www.rsasecurity.com/rsalabs/technotes/wep-fix.html.
| |
-
Unauthorized data decryption Once the WEP key is known, a hacker can transform the ciphertext into its original form and gain access to the original unencrypted data.
-
Violation of data integrity Once the original data has been decrypted, a hacker could potentially use the hacked WEP key to change the ciphertext and forward the changed message to the destination.
-
Poor key management WEP keys are typically static keys that, once configured on a device, remain the same from that point forward. The problem is exacerbated when an employee leaves the company because the WEP key really needs to be changed to ensure security. Unfortunately, this is not a practical solution if your company has hundreds or thousands of wireless devices because they will all need to be configured with the new WEP key.
| |
Some vendors address the key-management issue through the use of proprietary dynamic WEP mechanisms. This causes the systems to dynamically generate WEP keys that devices will use in conjunction with 802.1x authentication. Essentially, a new secret key is generated for each client that is authenticated. Although this can increase the security of WEP, because these are proprietary implementations , they are only practical if you use wireless devices that support the mechanism.
| |
-
No access point authentication WEP functions by allowing the wireless clients to authenticate the WAP; however, the WAP has no means of authenticating the client. Consequently, a hacker can reroute the data to access points through an alternate and unauthorized path .
Although these flaws may seem to imply that one should not use WEP, this is not correct. If you have the ability to use a better protection mechanism, such as WPA or 802.11i, do so. If you can t, though, WEP is still better than nothing ”even with the flaws.
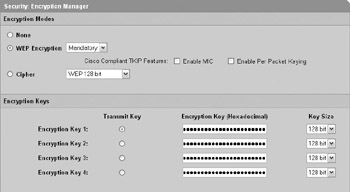
For your Cisco Aironet 1200, you can configure WEP at the Security Encryption Manager screen, shown next . Select WEP Encryption and choose Mandatory from the drop-down list. Enter the four 128-bit encryption keys and click Apply when you re finished.
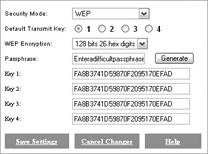
For your Linksys WAP54G, the first step of configuring WEP is to enable wireless security at the Setup Basic Setup screen. Next, you should click Edit Security Settings. This will present you with the Security Settings screen, shown next. Select WEP for the security mode. Select 128 bits 26 hex digits for the WEP Encryption. Enter a passphrase that meets the requirements of your password security policy and click Generate. This will generate the WEP keys you will need to enter on your wireless clients. When you have finished, click Save Settings to close the Security Settings screen.
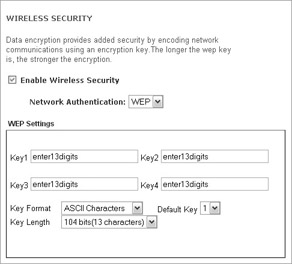
You can enable WEP on your Dell TrueMobile 2300 at the Basic Settings Wireless Security screen. Once you check Enable Wireless Security and select WEP from the Network Authentication drop-down list, you will be presented with the WEP Settings section, shown next. Select 104 bits(13 characters ) for Key Length and enter a 13-character key value for all four keys that conforms to your password security policy. When you have finished, click Save & Apply. When prompted, click Save & Restart.
Hardening WiFi Protected Access (WPA)
WPA is a subset of the 802.11i standard and was created to address the vulnerabilities of WEP.
| |
802.11i is an emerging technology that is designed to address all the security flaws related to WEP and is the direction that wireless security is heading. 802.11i incorporates all the aspects of WPA, including 802.1x authentication, Temporal Key Integrity Protocol (TKIP), and Michael Message Integrity Check (MMIC). In addition, 802.11i addresses a number of issues that WPA does not. 802.11i uses stronger encryption than WPA through the implementation of Advanced Encryption Standard (AES). This presents one of the biggest hindrances to 802.11i, however, because the processing overhead of AES is significant enough to require hardware upgrades to support it in many cases. 802.11i will also support roaming, which allows users to move between WAPs without losing their connection when they switch from the old WAP to the new WAP.
If you do not need wireless now, I recommend that you wait for 802.11i to be finalized and for 802.11i products to come out.
| |
In fact, the hardening procedure for WEP is simply to use WPA instead. WPA is actually a combination of a few different techniques that mitigate the problems that WEP exposes. The first is the use of 802.1x authentication to address authentication issues. The second is the use of Temporal Key Integrity Protocol (TKIP) to address encryption issues. The final is a Michael Message Integrity Check (MMIC) to address message integrity. WPA is forward compatible with 802.11i.
802.1x Authentication
The 802.1x specification was originally defined for wired networks and provides a mechanism for allowing a client (known as a supplicant) to be authenticated by a network device such as a WAP (known as an authenticator) through the use of a RADIUS server (known as an authentication server) . It is important to understand that the WAP does not perform the authentication; rather, it acts as a middleman by passing the client s credentials to the RADIUS server and letting it handle the actual authentication of the client.
802.1x uses a combination of the Extensible Authentication Protocol (EAP) and RADIUS for authenticating clients and distributing keys. RADIUS is used primarily for carrying the authentication and configuration information between the authenticator and the RADIUS server. RADIUS does not have a mechanism for using anything other than password-based authentication. To address this, EAP is used to provide the means to support authentication, such as public key “based authentication (that is, shared secret). Essentially, the WAP uses EAP to communicate with the client and RADIUS to communicate with the RADIUS server, encapsulating the data as required. EAP utilizes three common authentication means: EAP-MD5, EAP-TLS, and EAP-TTLS. In addition, Cisco has a proprietary implementation known as Lightweight EAP (LEAP). However, LEAP uses a weaker authentication algorithm. This, combined with its proprietary nature, makes LEAP not a recommended solution. Finally, Microsoft has implemented Protected EAP (PEAP), which was designed to overcome some of the limitations and vulnerabilities of the other EAP methods. PEAP can use MS-CHAP-v2 authentication within the EAP-TTLS tunnel to actually authenticate the user based on Active Directory. Many vendors support PEAP, so much so that it is currently undergoing evaluation to become a standard.
Temporal Key Integrity Protocol
Although 802.1x addresses authentication problems with WEP, it does not address the security problems related to the weak encryption keys used by WEP and the ability for a hacker to determine what the WEP key is. TKIP fixes this. TKIP uses 256-bit long encryption keys that are generated through a more sophisticated procedure to provide a much stronger encryption key. TKIP functions by adding the client MAC address and a 48-bit IV to a 128-bit temporal key (which is shared among clients) to guarantee that the encryption key is unique. The temporal key is changed every 10,000 packets to further ensure that hackers cannot begin decoding all packets if they are able to ascertain the encryption key, thus strengthening the security of the network.
Message Integrity Check
WPA also uses a MIC that is known as Michael to verify message integrity. A 64-bit message is calculated using the Michael algorithm, which can be used to detect potential tampering of the message or data.
Hardening WPA Using Pre-shared Keys
WPA using pre-shared keys (WPA-PSK) is a very common method of configuring wireless connections. This is due to the fact that using pre-shared keys does not require an investment in any AAA mechanisms such as RADIUS. The drawback is the same as any other use of pre-shared keys ”it does not scale as well in large environments as RADIUS does. Also, because the keys are human generated, they are more susceptible to cracking.
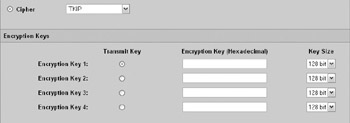
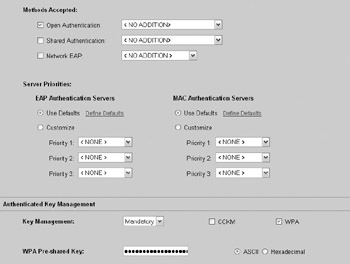
Configuring the Cisco Aironet 1200 for WPA-PSK is a multistep process. The first step is to configure TKIP as the cipher and to clear all encryption keys at the Security Encryption Manager screen, as shown next. When you are finished, click Apply.
The next step is to configure the WPA-PSK settings for the SSID at the Security SSID Manager screen. First, select the SSID you want to configure. Next, scroll down to the Authenticated Key Management section (shown next), select Mandatory, and check WPA for Key Management. Enter the WPA Pre-shared Key value. When you are finished, click Apply.
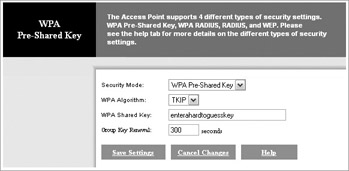
For the Linksys WAP54G, you configure the WPA settings at the Security Settings screen (shown next), just like the WEP configuration. Simply select WPA Pre-shared Key from the Security Mode drop-down box. For the WPA Algorithm setting, select TKIP or AES. AES is more secure, but it can have a negative impact on performance and is not supported by all wireless NICs. Next, enter the WPA shared key that should be used. The shared key should conform to your password security policy. Finally, enter the group key renewal time (default 300 seconds) and click Save Settings when you are finished.
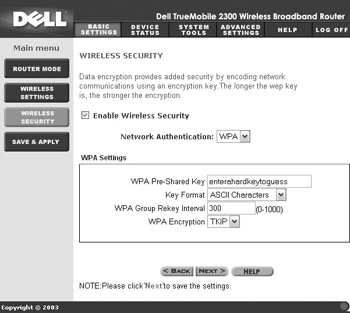
You can configure WPA using pre-shared keys on the Dell TrueMobile 2300 at the Basic Settings Wireless Security screen, shown next. Simply check to enable wireless security and select WPA for the network authentication method. Enter the appropriate WPA pre-shared key and select the proper key format and WPA group rekey interval (default 300). Finally, specify whether to use TKIP or AES (Dell has the same limitations as Linksys). When you are finished, click Save & Apply and then click Save & Restart when prompted.
Configuring WPA Using RADIUS/802.1x
| Note | The Dell TrueMobile 2300 wireless access router does not support WPA and RADIUS/802.1x. |
Using WPA with RADIUS/802.1x allows you to take full advantage of the benefits of the increased security that WPA provides while gaining the scalability that WPA with pre-shared keys does not provide. Before you can configure the WAP to use RADIUS, you need to make sure you have configured your RADIUS server to accept client connections from the WAP and have configured a shared secret. We will look at how to add and configure RADIUS clients in more detail in Chapter 9.
| Note | The Cisco Aironet 1200 WAP does not support WPA and RADIUS/802.1x without the use of a third-party supplicant such as the Funk Odyssey Client (http://www.funk.com) or the Meetinghouse Data Communications AEGIS client (http://www.meetinghousedata.com/). Refer to these vendors for the client-side configuration to support WPA and RADIUS/802.1x. |
Configuring the Cisco Aironet 1200 to support WPA and RADIUS/802.1x is a multistep process. First, you need to make sure you have installed and configured Cisco Secure ACS on your network. We will cover installing and configuring the Cisco Secure ACS in detail in Chapter 9. Second, you will need to install a third-party supplicant on the wireless client. This is extremely important because Cisco devotes only one sentence to this ”and it s buried deep in a technical note. If you don t do this, you will likely find yourself spending a couple hours thinking, I ve done everything that should make it work.
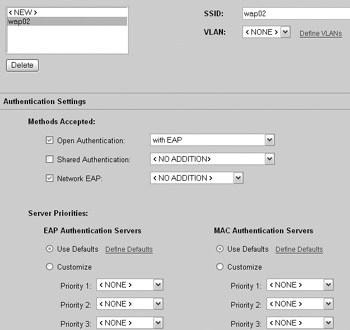
The actual WAP configuration is relatively straightforward. You need to configure the encryption cipher just like you did for the WPA-PSK configuration. The difference is at the Security SSID Manager screen. Select the SSID you want to configure and scroll down to the Authentication Settings section. Select the Open Authentication check box and choose With EAP from the drop-down list. Next, select the Network EAP check box with <No Addition> in the drop-down list, as shown here. When you are finished, click Apply.
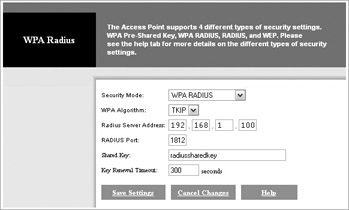
To configure WPA with RADIUS on the Linksys WAP54G, you will need to return to the Security Settings screen, shown here. Select WPA RADIUS for the security mode and specify the WPA algorithm. Enter the IP address and port number for the RADIUS server. Enter the shared key that is required to allow the WAP to authenticate with the RADIUS server and then specify the key renewal timeout. When you have finished, click Save Settings.
Hardening WLANS with Virtual Private Networks
Virtual private networks (VPNs) are not strictly wireless security protocols; however, they offer an excellent security mechanism for wireless networks right now. Because VPNs were designed to secure data in an inherently insecure environment (the Internet) and because WLANs are inherently insecure, VPNs make an excellent workaround to address WLAN security issues. Essentially, implementing a VPN over your wireless network requires your wireless clients to be running the appropriate VPN client software and the implementation of a VPN concentrator (for example, a Nortel Contivity Extranet Switch) that the WLAN connects to. The resources that the wireless clients need access to would reside on the other side of the VPN concentrator. Once the wireless client has connected to the WLAN, it simply uses the VPN client to connect to the VPN concentrator, and all the subsequent data is sent through the VPN tunnel. Implementing a VPN for all your wireless connections is as close to a bulletproof solution as you can implement. We will cover how to design a VPN for your WLANs in Chapters 11 and 12.
EAN: N/A
Pages: 125